Software:John the Ripper
 Running john with a password list on a shadow file | |
| Developer(s) | OpenWall |
|---|---|
| Initial release | 1996 [1] |
| Stable release | 1.9.0 [2]
/ May 14, 2019 |
| Operating system | Cross-platform |
| Type | Password cracking |
| License | GNU General Public License Proprietary (Pro version) |
| Website | {{{1}}} |
John the Ripper is a free password cracking software tool.[3] Originally developed for the Unix operating system, it can run on fifteen different platforms (eleven of which are architecture-specific versions of Unix, DOS, Win32, BeOS, and OpenVMS). It is among the most frequently used password testing and breaking programs[4] as it combines a number of password crackers into one package, autodetects password hash types, and includes a customizable cracker. It can be run against various encrypted password formats including several crypt password hash types most commonly found on various Unix versions (based on DES, MD5, or Blowfish), Kerberos AFS, and Windows NT/2000/XP/2003 LM hash. Additional modules have extended its ability to include MD4-based password hashes and passwords stored in LDAP, MySQL, and others.[5]
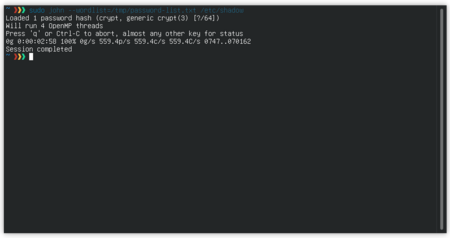
Sample output
Here is a sample output in a Debian environment.
$ cat pass.txt user:AZl.zWwxIh15Q $ john -w:password.lst pass.txt Loaded 1 password hash (Traditional DES [24/32 4K]) example (user) guesses: 1 time: 0:00:00:00 100% c/s: 752 trying: 12345 - pookie
The first line is a command to expand the data stored in the file "pass.txt". The next line is the contents of the file, i.e. the user (AZl) and the hash associated with that user (zWwxIh15Q). The third line is the command for running John the Ripper utilizing the "-w" flag. "password.lst" is the name of a text file full of words the program will use against the hash, pass.txt makes another appearance as the file we want John to work on.
Then we see output from John working. Loaded 1 password hash — the one we saw with the "cat" command — and the type of hash John thinks it is (Traditional DES). We also see that the attempt required one guess at a time of 0 with a 100% guess rate.
Attack types
One of the modes John can use is the dictionary attack. It takes text string samples (usually from a file, called a wordlist, containing words found in a dictionary or real passwords cracked before), encrypting it in the same format as the password being examined (including both the encryption algorithm and key), and comparing the output to the encrypted string. It can also perform a variety of alterations to the dictionary words and try these. Many of these alterations are also used in John's single attack mode, which modifies an associated plaintext (such as a username with an encrypted password) and checks the variations against the hashes.
John also offers a brute force mode. In this type of attack, the program goes through all the possible plaintexts, hashing each one and then comparing it to the input hash. John uses character frequency tables to try plaintexts containing more frequently used characters first. This method is useful for cracking passwords that do not appear in dictionary wordlists, but it takes a long time to run.
See also
References
- ↑ "john-users - Re: When was John created?". https://www.openwall.com/lists/john-users/2015/09/10/4.
- ↑ "Announce - [openwall-announce] John the Ripper 1.9.0-jumbo-1". https://www.openwall.com/lists/announce/2019/05/14/1.
- ↑ Anonymous (2001). Maximum Linux Security (2 ed.). Sams Publishing. p. 154. ISBN 0-672-32134-3.
- ↑ "Password Crackers". Concise Cybersecurity. https://www.concise-courses.com/hacking-tools/password-crackers/john-the-ripper/.
- ↑ "John the Ripper". sectools.org. http://sectools.org/tool/john/.
External links
 |

