Engineering:BadUSB
- Karsten Nohl, 2014[1]
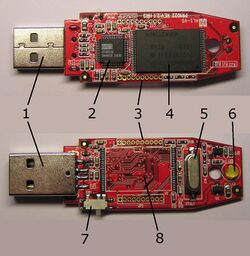
BadUSB is a computer security attack using USB devices that are programmed with malicious software.[2] For example, USB flash drives can contain a programmable Intel 8051 microcontroller, which can be reprogrammed, turning a USB flash drive into a malicious device.[3] This attack works by programming the fake USB flash drive to emulate a keyboard, which once plugged into a computer, is automatically recognized and allowed to interact with the computer, and can then initiate a series of keystrokes which open a command window and issue commands to download malware.
The BadUSB attack was first revealed during a Black Hat talk in 2014 by Karsten Nohl, Sascha Krißler and Jakob Lell. Two months after the talk, other researchers published code that can be used to exploit the vulnerability.[4] In 2017, version 1.0 of the USG dongle, which acts like a hardware firewall, was released, which is designed to prevent BadUSB style attacks.[5]
Criminal usage
In March 2020, the FBI issued a warning that members of the FIN7 cybercrime group have been targeting companies in the retail, restaurant, and hotel industries with BadUSB attacks designed to deliver REvil or BlackMatter ransomware.[6] Packages have been sent to employees in IT, executive management, and human resources departments.[6] One intended target was sent a package in the mail which contained a fake gift card from Best Buy as well as a USB flash drive with a letter stating that the recipient should plug the drive into their computer to access a list of items that could be purchased with the gift card.[6][7] When tested, the USB drive emulated a keyboard, and then initiated a series of keystrokes which opened a PowerShell window and issued commands to download malware to the test computer, and then contacted servers in Russia .[6][7]
In January 2022, the FBI issued another warning that members FIN7 were targeting transportation and insurance companies (since August 2021), and defense companies (since November 2021), with BadUSB attacks designed to deliver REvil or BlackMatter ransomware.[8][9] These targets were sent USB drives in packages claiming to be from Amazon or the United States Department of Health and Human Services, with letters talking about free gift cards or COVID-19 protocols that were purportedly further explained by information on the USB drive.[8][9] As above, when plugged in, the USB drives emulate a keyboard, and then initiate a series of keystrokes which open a PowerShell window and issue commands to download malware.[8][9]
See also
Further reading
- Lu, Hongyi; Wu, Yechang; Li, Shuqing; Lin, You; Zhang, Chaozu; Zhang, Fengwei (May 2021). "BADUSB-C: Revisiting BadUSB with Type-C". 2021 IEEE Security and Privacy Workshops (SPW). pp. 327–338. doi:10.1109/SPW53761.2021.00053. ISBN 978-1-6654-3732-5. https://ieeexplore.ieee.org/document/9474274.
References
- ↑ Goodin, Dan (July 31, 2014). "This thumbdrive hacks computers. 'BadUSB' exploit makes devices turn 'evil'" (in en-us). https://arstechnica.com/information-technology/2014/07/this-thumbdrive-hacks-computers-badusb-exploit-makes-devices-turn-evil/.
- ↑ Greenberg, Andy (July 31, 2014). "Why the Security of USB Is Fundamentally Broken" (in en-US). Wired. ISSN 1059-1028. https://www.wired.com/2014/07/usb-security/. Retrieved 2021-09-07.
- ↑ Nohl, Karsten; Krißler, Sascha; Lell, Jakob. "BadUSB - On accessories that turn evil". https://radetskiy.files.wordpress.com/2014/08/srlabs-badusb-blackhat-v1.pdf.
- ↑ Greenberg, Andy (October 2, 2014). "The Unpatchable Malware That Infects USBs Is Now on the Loose" (in en-US). Wired. ISSN 1059-1028. https://www.wired.com/2014/10/code-published-for-unfixable-usb-attack/. Retrieved 2021-09-07.
- ↑ Doctorow, Cory (March 2, 2017). "USG: an open source anti-BadUSB hardware firewall for your USB port" (in en-US). https://boingboing.net/2017/03/02/countermeasures.html.
- ↑ 6.0 6.1 6.2 6.3 Ilascu, Ionut (2020-03-27). "FBI: Hackers Sending Malicious USB Drives & Teddy Bears via USPS". Bleeping Computer. https://www.bleepingcomputer.com/news/security/fbi-hackers-sending-malicious-usb-drives-and-teddy-bears-via-usps/. "This is not a one-off incident, though. The FBI warns that FIN7 has mailed these packages via USPS to numerous businesses (retail, restaurant, hotel industry) where they target employees in human resources, IT, or executive management departments. These packages sometimes include "gifts" like teddy bears or gift cards. These USB drives are configured to emulate keystrokes that launch a PowerShell command to retrieve malware from server controlled by the attacker. Then, the USB device contacts domains or IP addresses in Russia."
- ↑ 7.0 7.1 Cimpanu, Catalin (March 26, 2020). "Rare BadUSB attack detected in the wild against US hospitality provider" (in en). https://www.zdnet.com/article/rare-badusb-attack-detected-in-the-wild-against-us-hospitality-provider/.
- ↑ 8.0 8.1 8.2 Gatlan, Sergiu (2022-01-07). "FBI: Hackers use BadUSB to target defense firms with ransomware". Bleeping Computer. https://www.bleepingcomputer.com/news/security/fbi-hackers-use-badusb-to-target-defense-firms-with-ransomware/. "FIN7 operators impersonated Amazon and the US Department of Health & Human Services (HHS) to trick the targets into opening the packages and connecting the USB drives to their systems. Since August, reports received by the FBI say that these malicious packages also contain letters about COVID-19 guidelines or counterfeit gift cards and forged thank you notes, depending on the impersonated entity."
- ↑ 9.0 9.1 9.2 Tung, Liam (2022-01-10). "Ransomware warning: Cyber criminals are mailing out USB drives that install malware". ZDNET. https://www.zdnet.com/article/fbi-cybercriminals-are-mailing-out-usb-drives-that-will-install-ransomware/.
Further reading
- "Can BadUSB be avoided by looking at the shapes and the controller model inside it?" (in en). https://security.stackexchange.com/questions/239972/can-badusb-be-avoided-by-looking-at-the-shapes-and-the-controller-model-inside-i.