Code as speech
Code as speech is the legal and philosophical doctrine in the United States that computer source code and similar digital expressions are forms of speech protected by the First Amendment. The idea emerged prominently during the "crypto wars" in the 1990s, when the courts disputed the U.S. government's notion that encryption software constituted munitions, instead recognizing code's expressive function in cases such as Bernstein v. United States. Since then, debates over encryption, privacy tools, cryptocurrency, and 3D-printed gun files have continued to test the boundaries of how law treats code as a medium of expression and continues to be the subject of legal and scholarly debate.[2][3][4]
History
Encryption as munitions
In 1977, the United States began restricting non-governmental uses of cryptography. The restrictions began when a member of the National Security Agency sent a letter to the Institute of Electrical and Electronics Engineers (IEEE) warning that the presentation material at a Cornell cryptography conference might violate weapons export regulations.[5] In the early 1990s, the U.S. government started to more actively enforce that strong encryption software was a munition under export regulations, meaning it could not legally be shared overseas without a license.[6] This classification of encryption as munitions was strongly opposed by computer scientists as well as civil liberties, privacy advocates, and cypherpunks who argued that encryption algorithms were mathematical ideas and publishing source code should be protected as speech.[6][7]
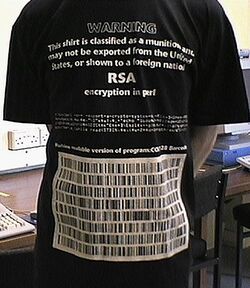
Activists printed cryptographic code on T-shirts, mugs, posters and more as a way of demonstrating code's expressive utility and protesting what they viewed as censorship.
Bernstein v. United States
In Bernstein v. United States, the Ninth Circuit Court of Appeals ruled that source code is a form of speech protected under the First Amendment. A lower court ruling on this case reasoned, "Like music and mathematical equations, computer language is just that, language, and it communicates information either to a computer or to those who can read it."[8] The case was brought by mathematician Daniel Bernstein who challenged these export controls after the government prohibited him from publishing his encryption algorithm, Snuffle.[9] Bernstein was represented by the Electronic Frontier Foundation (EFF), which has since played a major role in digital free speech litigation.[10]
This decision established code as speech as a legal precedent that became central to later legal disputes. In 2015, the United Nations issued a report stating that access to encryption software is a human right.[11]
Apple, the FBI, and compelled speech
In 2016, the FBI sought to compel Apple to create special software to bypass security on an iPhone used by the San Bernadino shooter.[12] Apple refused, arguing that the code itself is expressive and compelling software engineers to write it would violate the First Amendment's ban on compelled speech.[13] The dispute ended when the FBI unlocked the device by other means, but it remains a landmark legal dispute over code's status as protected expression.
Cryptocurrency and blockchain privacy tools

In the 2010s and 2020s, debate began to ensue about whether Bitcoin constituted code protected as speech. Proponents argue that Bitcoin's source code and protocol are themselves political statements about decentralization, censorship resistance, and distrust of centralized authority.[14] Some legal scholars and activists argue that publishing or running Bitcoin software is inherently protected speech because it expresses economic and ideological beliefs and because it is code.[15][16]
In the 2020s, U.S. authorities began to target developers of open-source privacy tools that interface with blockchains. In 2022, the U.S. Treasury sanctioned Tornado Cash, an Ethereum mixing protocol.[17] Critics of this sanction argued that this constituted a sanction of the code rather than the criminal use.[17] The EFF also defended the Tornado Cash developers arguing that publishing open-source privacy tools is protected expression.[18] The prosecution of Tornado Cash founder Roman Storm continues to be ongoing under the Trump Administration with chief legal officer of the crypto firm Variant stating, “This really is a vestige of the Biden administration’s war on crypto,” and that, "It’s shocking the case is still moving forward.”[19]
In 2024, Keonne Rodriguez and William Lonergan Hill, the developers of Samourai Wallet, a Bitcoin privacy tool that uses Coinjoin to mix transactions, were indicted.[20] Critics of this action argued that the government was using stopping criminal activity as a justification to instead target code as speech.[21]
3D-printed guns

In 2013, Cody Wilson and his group Defense Distributed published the CAD files for the Liberator, a 3D-printable gun.[22] The U.S. State Department ordered him to remove the files, triggering a legal battle with Wilson arguing that the code constitutes protected speech.[23][24] In the lawsuit, DD argued that it “believed, and continues to believe, that the United States Constitution guarantees a right to share truthful speech. Especially speech concerning fundamental constitutional rights in open forums.”[25]
Wilson also developed the Ghost Gunner, a small CNC milling machine that can finish metal gun parts.[26] DD portrayed the project as technological activism and a First Amendment test, asserting that restricting code files or machine instructions amounts to censorship.[27][28] Supporters argue that publishing design files, similar to publishing encryption algorithms, is expressive conduct.[29][30]
DRM, piracy, and the Free Speech Flag

In 2007, an AACS encryption key was developed. This is a hexadecimal number used to bypass digital rights management (DRM) on HD DVDs.[31] It was posted widely on Digg.com, causing a controversy.[32] The movie industry sent takedown notices to Digg.com under the Digital Millennium Copyright Act (DMCA).[33][34] Digg.com's site administrators attempted to prevent users from posting links revealing the encryption key. Users subsequently resisting this action by mass posting the key onto the site.[35] One user coined this occurrence as a "digital Boston Tea Party."[35]
Activists went so far as to create the Free Speech Flag: a symbolic image whose color values encode the banned key.[36] The flag became an emblem of digital rights protests, highlighting how even a short number or snippet of code can carry political meaning and be treated as illegal.[37]
The fight over the AACS key also impacted debates on piracy, intellectual property, and fair use.[38] Particularly, whether sharing code that defeats copy protection, even just as a statement or an artistic form, is First Amendment protected speech. In the DRM and piracy debates, the EFF has criticized takedown demands and the DMCA's anti-circumvention provisions as unconstitutional restrictions on speech, especially when they target publication of code or encryption keys.[39][40]
See also
- Digital rights
- Junger v. Daley
References
- ↑ "Export of cryptography from the United States" (in en), Wikipedia, 2025-05-24, https://en.wikipedia.org/w/index.php?title=Export_of_cryptography_from_the_United_States&oldid=1292028727, retrieved 2025-07-10
- ↑ "Code as Speech." (in en). https://www.hks.harvard.edu/publications/code-speech.
- ↑ Wang, Xiangnong, De-Coding Free Speech: A First Amendment Theory for the Digital Age (February 15, 2021). 2021 Wis. L. Rev. 1373, Available at SSRN: https://ssrn.com/abstract=4038356
- ↑ Browder, John J. (2000). "Encryption Source Code and the First Amendment". Jurimetrics 40 (4): 431–444. ISSN 0897-1277. https://www.jstor.org/stable/29762672.
- ↑ McGregor, Susan (2016-05-11). "The Second Amendment Case for the Right to Bear Crypto" (in en-US). https://www.vice.com/en/article/the-second-amendment-case-for-the-right-to-bear-encryption/.
- ↑ 6.0 6.1 "When Encryption Was a Crime: The 1990s Battle for Free Speech in Software" (in en-US). 2020-10-21. https://reason.com/video/2020/10/21/cryptowars-gilmore-zimmermann-cryptography/.
- ↑ "Opinion | Encryption and Free Speech" (in en-US). The Washington Post. 1999-05-10. ISSN 0190-8286. https://www.washingtonpost.com/archive/opinions/1999/05/10/encryption-and-free-speech/7f3af2df-70ce-4f81-ace0-56cece2afd06/.
- ↑ Dame-Boyle, Alison (2015-04-16). "EFF at 25: Remembering the Case that Established Code as Speech" (in en). https://www.eff.org/deeplinks/2015/04/remembering-case-established-code-speech.
- ↑ "Dan Bernstein's Attempt to Publish Snuffle and The Legal Issues Raised". https://groups.csail.mit.edu/mac/classes/6.805/student-papers/fall95-papers/kokoski-crypto.html.
- ↑ "Court Hears Appeal in Encryption Case". https://archive.nytimes.com/www.nytimes.com/library/cyber/week/120997encrypt-bernstein.html.
- ↑ "Encryption key to free speech, says UN report" (in en-GB). BBC News. 2015-05-29. https://www.bbc.com/news/technology-32916002.
- ↑ Devlin Barrett, Danny Yadron and Daisuke Wakabayashi. "Apple and Others Encrypt Phones, Fueling Government Standoff" (in en-US). WSJ. https://www.wsj.com/articles/apple-and-others-encrypt-phones-fueling-government-standoff-1416367801?gaa_at=eafs&gaa_n=ASWzDAhCJeXBY9kAJ8cxP5EFSnFFyBEKRlglnMybzM9nFhXHkBwNNC527QwEXN5gFEc=&gaa_ts=686fde3e&gaa_sig=AqTV07VxLm1syLkB4rkXtQrTFQuhAZcwCJgLOOfy0BdyZ8TKkBlU0CVCWCuNgTFBaqMHklBcO0unlO77u8fSbA==.
- ↑ Yadron, Danny; Ackerman, Spencer; Thielman, Sam (2016-02-25). "Apple accuses FBI of violating constitutional rights in iPhone battle" (in en-GB). The Guardian. ISSN 0261-3077. https://www.theguardian.com/technology/2016/feb/25/apple-fbi-iphone-encryption-request-response.
- ↑ 14.0 14.1 "The Bitcoin Ideology" (in en). https://www.nytimes.com/2013/12/15/sunday-review/the-bitcoin-ideology.html.
- ↑ Jeong, Sarah (2014-02-07). "Is Bitcoin Free Speech?" (in en-US). Slate. ISSN 1091-2339. https://slate.com/technology/2014/02/bitcoin-as-free-speech-regulating-cryptocurrency-has-ramifications-for-democracy.html.
- ↑ Chang, Samantha (July 3, 2019). "U.S. Can’t Ban Bitcoin Because It’s Free Speech: Abra CEO". https://finance.yahoo.com/news/u-t-ban-bitcoin-because-181012540.html.
- ↑ 17.0 17.1 "A First Amendment fight for the future of the internet - The Boston Globe" (in en-US). BostonGlobe.com. https://www.bostonglobe.com/2024/07/11/opinion/code-is-speech-tornado-cash/.
- ↑ Opsahl, Kurt (2022-08-22). "Code, Speech, and the Tornado Cash Mixer" (in en). Electronic Frontier Foundation. https://www.eff.org/deeplinks/2022/08/code-speech-and-tornado-cash-mixer.
- ↑ Khalili, Joel. "Tornado Cash Made Crypto Anonymous. Now One of Its Creators Faces Trial" (in en-US). Wired. ISSN 1059-1028. https://www.wired.com/story/roman-storm-tornado-cash-crypto-trial/.
- ↑ Book, Joakim (2024-05-01). "Groundhog Day for the crypto wars: The DOJ on bitcoin prowl" (in en-US). https://reason.com/2024/05/01/groundhog-day-for-the-crypto-wars-the-doj-on-bitcoin-prowl/.
- ↑ Huang, Roger. "Samourai Indictment & FBI Notice Are An Assault On Bitcoin And Privacy" (in en). https://www.forbes.com/sites/digital-assets/2024/04/26/samourai-indictment--fbi-notice-are-an-assault-on-bitcoin-and-privacy/.
- ↑ "The blueprint for a 3-D-printed gun was uploaded in book form to Amazon as a free speech exercise. Amazon removed it." (in en). Washington Post. 2018-08-23. https://www.washingtonpost.com/news/morning-mix/wp/2018/08/23/3d-printed-gun-blueprint-was-uploaded-in-book-form-to-amazon-as-a-free-speech-exercise-amazon-removed-it/.
- ↑ Greenberg, Andy. "State Department Demands Takedown Of 3D-Printable Gun Files For Possible Export Control Violations" (in en). https://www.forbes.com/sites/andygreenberg/2013/05/09/state-department-demands-takedown-of-3d-printable-gun-for-possible-export-control-violation/.
- ↑ "The Fight Over 3-D-Printed Guns" (in en-US). The New York Times. 2018-08-01. ISSN 0362-4331. https://www.nytimes.com/2018/08/01/podcasts/the-daily/3d-printed-guns-cody-wilson-trump.html.
- ↑ Feuer, Alan. "Cody Wilson, Who Posted Gun Instructions Online, Sues State Department" (in en). https://www.nytimes.com/2015/05/07/us/cody-wilson-who-posted-gun-instructions-online-sues-state-department.html.
- ↑ Greenberg, Andy. "This "Ghost Gun" Machine Now Makes Untraceable Metal Handguns" (in en-US). Wired. ISSN 1059-1028. https://www.wired.com/story/ghost-gun-machine-makes-untraceable-handguns/.
- ↑ "‘Downloadable Gun’ Clears a Legal Obstacle, and Activists Are Alarmed" (in en). https://www.nytimes.com/2018/07/13/business/downloadable-gun-allowed-alarming-activists.html.
- ↑ Doherty, Brian (2021-04-30). "The State Department Fought To Allow ‘Ghost Gun’ Files and Won. Why Is It Still Trying To Remove Them?" (in en-US). https://reason.com/2021/04/30/the-state-department-fought-to-allow-ghost-gun-files-and-won-why-is-it-still-trying-to-remove-them/.
- ↑ O'Sullivan, Andrea (2018-07-18). "When Code Is Speech, Tech Like 3D-Printed Guns Sees Greater Protection from Censorship" (in en-US). https://reason.com/2018/07/18/when-code-is-speech-tech-like-3d-printed/.
- ↑ "Is Code Free Speech?" (in en-US). 2018-07-27. https://www.pbs.org/wgbh/nova/article/is-code-free-speech/.
- ↑ "09 f9 11 02 9d 74 e3 5b d8 41 56 c5 63 56 88 c0 is the number they tried to ban - The Inquirer" (in en). http://www.theinquirer.net/inquirer/news/1018487/09-f9-02-9d-e3-5b-d8-41-56-c5-63-56-c0-tried-ban.
- ↑ "Digg revolt over HD DVD codes | Australian IT" (in en). http://www.australianit.news.com.au/story/0,24897,21659892-27317,00.html.
- ↑ Coleman, Gabriella (2013-03-21). "Code Is Speech" (in en-US). https://reason.com/2013/03/21/code-is-speech/.
- ↑ Bushell-embling, Dylan. "Digg finds the key is safety in numbers" (in en-US). https://www.brisbanetimes.com.au/technology/digg-finds-the-key-is-safety-in-numbers-20070515-gdq505.html.
- ↑ 35.0 35.1 "Digg's DRM Revolt - Forbes.com". http://www.forbes.com/technology/2007/05/02/digital-rights-management-tech-cx_ag_0502digg.html.
- ↑ "Digg finds the key is safety in numbers - web - Technology" (in en). http://www.brisbanetimes.com.au/news/web/digg-finds-the-key-is-safety-in-numbers/2007/05/14/1178995074634.html?page=fullpage.
- ↑ "WEBLOGS AND ACTIVISM: A SOCIAL MOVEMENT PERSPECTIVE ON THE BLOGOSPHERE". https://etda.libraries.psu.edu/paper/11322/6651.
- ↑ Stone, Brad (2007-05-03). "In Web Uproar, Antipiracy Code Spreads Wildly" (in en-US). The New York Times. ISSN 0362-4331. https://www.nytimes.com/2007/05/03/technology/03code.html.
- ↑ Release, Press (2022-01-13). "EFF Asks Appeals Court to Rule DMCA Anti-Circumvention Provisions Violate First Amendment" (in en). https://www.eff.org/press/releases/eff-asks-appeals-court-rule-dmca-anti-circumvention-provisions-violate-first.
- ↑ Lohmann, Fred von (2007-11-28). "Year-End 2007: Darknet Assumptions Still True" (in en). https://www.eff.org/deeplinks/2007/11/year-end-2007-darknet-assumptions-still-true.
 |
