Gordon–Loeb model
The Gordon–Loeb model is a mathematical economic model analyzing the optimal investment level in information security.
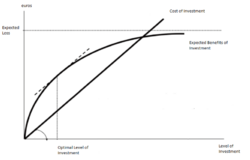
The primary benefits from cybersecurity investments result from the cost savings associated with cyber breaches that are prevented due to the investment. However, as with any investment, it is important to compare the benefits to the costs when deciding how to invest. The Gordon-Loeb model provides a valuable framework for deriving, on a cost-benefit basis, the appropriate amount to invest in cybersecurity related activities.
The basic components of the Gordon-Loeb model are as follows:
- Data (information) sets of organizations that are vulnerable to cyber-attacks. This vulnerability, denoted as v (0 ≤ v ≤ 1), represents the probability that a breach to a specific information set will occur under current conditions.
- If an information set is breached, the value of the information set represents the potential loss (i.e., the cost of the breach) and can be expressed as a monetary value, denoted as L. Thus, vL is the expected loss from a cyber breach prior to an investment in additional cybersecurity activities.
- An investment in cybersecurity, denoted as z, will reduce v based on the productivity of the cybersecurity investment. The productivity of investment is what the Gordon-Loeb model refers to as the security breach probability function.
Gordon and Loeb were able to show that, for two broad classes of security breach probability functions, the optimal level of investment in information security, z*, would not exceed roughly 37% of the expected loss from a security breach. More specifically: z* (v) ≤ (1/e) vL.
Example:
Suppose an estimated data value of €1,000,000, with an attack probability of 15%, and an 80% chance that an attack would be successful.
In this case, the potential loss is given by the product €1,000,000 × 0.15 × 0.8 = €120,000.
According to Gordon and Loeb, the company's investment in security should not exceed €120,000 × 0.37 = €44,000.
The Gordon–Loeb Model was first published by Lawrence A. Gordon and Martin P. Loeb in their 2002 paper, in ACM Transactions on Information and System Security, entitled "The Economics of Information Security Investment"[1] The paper was reprinted in the 2004 book Economics of Information Security.[2] Gordon and Loeb are both professors at the University of Maryland's Robert H. Smith School of Business.
The Gordon–Loeb Model is one of the most well accepted analytical models for the economics of cyber security. The model has been widely referenced in the academic and practitioner literature.[3][4][5][6][7][8][9][10][11] The model has also been empirically tested in several different settings. Research by mathematicians Marc Lelarge[12] and Yuliy Baryshnikov[13] generalized the results of the Gordon–Loeb Model.
The Gordon–Loeb model has been featured in the popular press, such as The Wall Street Journal [14] and The Financial Times.[15]
However, following research showed that even within the initial assumptions of the model, some security breach probability functions should be fixed with no less than 1/2 the expected loss, contradicting the hypothesis that the 1/e factor was universal. Furthermore, by using another mathematization of Gordon-Loeb requirements (more precisely, that the second derivative of the loss function does not need to be continuous), one can create loss functions whose optimal fixing costs 100% of the estimated loss.[16]
See also
- Genuine progress indicator (External links)
References
- ↑ Gordon, Lawrence A.; Loeb, Martin P. (November 2002). "The Economics of Information Security Investment". ACM Transactions on Information and System Security 5 (4): 438–457. doi:10.1145/581271.581274. http://tissec.acm.org/.
- ↑ Gordon, Lawrence A.; Loeb, Martin P. (2004). "Economics of Information Security Investment". Economics of Information Security. Advances in Information Security. 12. Boston, MA: Springer. doi:10.1007/1-4020-8090-5_9. ISBN 978-1-4020-8089-0. https://link.springer.com/chapter/10.1007/1-4020-8090-5_9.
- ↑ Matsuura, Kanta (23 April 2008). "Productivity Space of Information Security in an Extension of the Gordon-Loeb's Investment Model". http://weis2008.econinfosec.org/papers/Matsuura.pdf. Retrieved 30 October 2014.
- ↑ Willemson, Jan (2006). "On the Gordon & Loeb Model for Information Security Investment". https://www.econinfosec.org/archive/weis2006/docs/12.pdf.
- ↑ Willemson, Jan (2010). "Extending the Gordon and Loeb Model for Information Security Investment". 2010 International Conference on Availability, Reliability and Security. pp. 258–261. doi:10.1109/ARES.2010.37. ISBN 978-1-4244-5879-0.
- ↑ Johnson, E. (2009). Managing Information Risk and the Economics of Security. Springer. p. 99. ISBN 9780387097626. https://books.google.com/books?id=PHAaT9KjbmkC. Retrieved 30 October 2014.
- ↑ "The Gordon-Loeb Investment Model Generalized: Time Dependent Multiple Threats and Breach Losses over an Investment Period". BibSonomy. http://www.bibsonomy.org/bibtex/79b784185a4be9d45abd80a74a1c294d. Retrieved 30 October 2014.
- ↑ Su, Xiaomeng (15 June 2006). "An Overview of Economic Approaches to Information Security Management". http://eprints.eemcs.utwente.nl/5693/01/00000177.pdf. Retrieved 30 October 2014.
- ↑ Böhme, Rainer (29 August 2010). "Security Metrics and Security Investment Models". International Computer Science Institute, Berkeley, California. http://www.wi1.uni-muenster.de/security/publications/Boehme2010_SecurityInvestment-IWSEC.pdf. Retrieved 30 October 2014.
- ↑ Ye, Ruyi (2014). "An economic model of investment in information security". HKUST Institutional Repository. http://repository.ust.hk/dspace/handle/1783.1/5020. Retrieved 30 October 2014.
- ↑ Kuramitsu, Kimio (21 July 2005). "A Case Study of Gordon-Loop Model on Optimal Security Investments" (in ja). 電子情報通信学会技術研究報告 = Ieice Technical Report: 信学技報 (CiNii) 105 (193): 243–248. ISSN 0913-5685. http://ci.nii.ac.jp/naid/110003298595. Retrieved 30 October 2014.
- ↑ Lelarge, Marc (December 2012). "Coordination in Network Security Games: A Monotone Comparative Statics Approach". IEEE Journal on Selected Areas in Communications 30 (11): 2210–9. doi:10.1109/jsac.2012.121213. Bibcode: 2012arXiv1208.3994L. http://www.techrepublic.com/resource-library/whitepapers/coordination-in-network-security-games-a-monotone-comparative-statics-approach/. Retrieved 13 May 2014.
- ↑ Baryshnikov, Yuliy (24 February 2012). "IT Security Investment and Gordon-Loeb's 1/e Rule". http://weis2012.econinfosec.org/papers/Baryshnikov_WEIS2012.pdf. Retrieved 30 October 2014.
- ↑ Gordon, Lawrence A.; Loeb, Martin P. (26 September 2011). "You May Be Fighting the Wrong Security Battles". The Wall Street Journal. https://www.wsj.com/news/articles/SB10001424053111904900904576554762089179984. Retrieved 9 May 2014.
- ↑ Palin, Adam (30 May 2013). "Maryland professors weigh up cyber risks". Financial Times. http://www.ft.com/intl/cms/s/2/606e0e5a-b345-11e2-b5a5-00144feabdc0.html. Retrieved 9 May 2014.
- ↑ Willemson, Jan (2006). "On the Gordon&Loeb Model for Information Security Investment". WEIS. https://citeseerx.ist.psu.edu/document?repid=rep1&type=pdf&doi=802aeb6fd4cf033b8ecb25b970fbb58394d32466.
 |
