Phishing

Phishing is a form of social engineering and scam where attackers deceive people into revealing sensitive information[1] or installing malware such as ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim.[2] As of 2020, it is the most common type of cybercrime, with the FBI's Internet Crime Complaint Center reporting more incidents of phishing than any other type of computer crime.[3]
The term "phishing" was first recorded in 1995 in the cracking toolkit AOHell, but may have been used earlier in the hacker magazine 2600.[4][5][6] It is a variation of fishing and refers to the use of lures to "fish" for sensitive information.[5][7][8]
Measures to prevent or reduce the impact of phishing attacks include legislation, user education, public awareness, and technical security measures.[9] The importance of phishing awareness has increased in both personal and professional settings, with phishing attacks among businesses rising from 72% to 86% from 2017 to 2020.[10]
Types
Email phishing
Phishing attacks, often delivered via email spam, attempt to trick individuals into giving away sensitive information or login credentials. Most attacks are "bulk attacks" that are not targeted and are instead sent in bulk to a wide audience.[11] The goal of the attacker can vary, with common targets including financial institutions, email and cloud productivity providers, and streaming services.[12] The stolen information or access may be used to steal money, install malware, or spear phish others within the target organization.[5] Compromised streaming service accounts may also be sold on darknet markets.[13]
This type of social engineering attack can involve sending fraud emails or messages that appear to be from a trusted source, such as a bank or government agency. These messages typically redirect to a fake login page where the user is prompted to enter their login credentials.
Spear phishing
Spear phishing is a targeted phishing attack that uses personalized emails[14] to trick a specific individual or organization into believing they are legitimate. It often utilizes personal information about the target to increase the chances of success.[15][16][17][18] These attacks often target executives or those in financial departments with access to sensitive financial data and services. Accountancy and audit firms are particularly vulnerable to spear phishing due to the value of the information their employees have access to.[19]
Threat Group-4127 (Fancy Bear) targeted Hillary Clinton's 2016 presidential campaign with spear phishing attacks on over 1,800 Google accounts, using the accounts-google.com domain to threaten targeted users.[20][21]
A study on spear phishing susceptibility among different age groups found that 43% of 100 young and 58% of older users clicked on simulated phishing links in daily emails over 21 days. Older women had the highest susceptibility, while susceptibility in young users declined over the study, but remained stable in older users.[22]
Whaling and CEO fraud
Whaling attacks use spear phishing techniques to target senior executives and other high-profile individuals[23] with customized content, often related to a subpoena or customer complaint.[24]
CEO fraud involves sending fake emails from senior executives to trick employees into sending money to an offshore account.[25] It has a low success rate, but can result in organizations losing large sums of money.[26]
Clone phishing
Clone phishing is a type of attack where a legitimate email with an attachment or link is copied and modified to contain malicious content. The modified email is then sent from a fake address made to look like it's from the original sender. The attack may appear to be a resend or update of the original email. It often relies on the sender or recipient being previously hacked so the attacker can access the legitimate email.[27][28]
Voice phishing
Voice over IP (VoIP) is used in vishing or voice phishing attacks,[29] where attackers make automated phone calls to large numbers of people, often using text-to-speech synthesizers, claiming fraudulent activity on their accounts. The attackers spoof the calling phone number to appear as if it is coming from a legitimate bank or institution. The victim is then prompted to enter sensitive information or connected to a live person who uses social engineering tactics to obtain information.[29] Vishing takes advantage of the public's lower awareness and trust in voice telephony compared to email phishing.[30]
SMS phishing
SMS phishing[31] or smishing[32][33] is a type of phishing attack that uses text messages from a cell phone or smartphone to deliver a bait message.[34] The victim is usually asked to click a link, call a phone number, or contact an email address provided by the attacker. They may then be asked to provide private information, such as login credentials for other websites. The difficulty in identifying illegitimate links can be compounded on mobile devices due to the limited display of URLs in mobile browsers.[35] Smishing can be just as effective as email phishing, as many smartphones have fast internet connectivity. Smishing messages may also come from unusual phone numbers.[36]
Page hijacking
Page hijacking involves redirecting users to malicious websites or exploit kits through the compromise of legitimate web pages, often using cross site scripting. Hackers may insert exploit kits such as MPack into compromised websites to exploit legitimate users visiting the server. Page hijacking can also involve the insertion of malicious inline frames, allowing exploit kits to load. This tactic is often used in conjunction with watering hole attacks on corporate targets.[citation needed]
Calendar phishing
Calendar phishing involves sending fake calendar invitations with phishing links. These invitations often mimic common event requests and can easily be added to calendars automatically.[37] To protect against this form of fraud, former Google click fraud czar Shuman Ghosemajumder recommends changing calendar settings to not automatically add new invitations.[38]
Quishing
QR codes have been used maliciously in phishing attacks.[39] The term "quishing" involves deceiving individuals into thinking a QR code is harmless while the true intent is malicious, aiming to access sensitive information.[39] Cybercriminals exploit the trust placed in QR codes, particularly on mobile phones, which are more vulnerable to attacks compared to desktop operating systems.[39] Quishing attacks often involve sending QR codes via email, enticing users to scan them to verify accounts, leading to potential device compromise.[39] It is advised to exercise caution and avoid scanning QR codes unless the source is verified.[39]
Techniques
Link manipulation
Phishing attacks often involve creating fake links that appear to be from a legitimate organization.[40] These links may use misspelled URLs or subdomains to deceive the user. In the following example URL, http://www.yourbank.example.com/, it can appear to the untrained eye as though the URL will take the user to the example section of the yourbank website; actually this URL points to the "yourbank" (i.e. phishing subdomain) section of the example website (fraudster's domain name). Another tactic is to make the displayed text for a link appear trustworthy, while the actual link goes to the phisher's site. To check the destination of a link, many email clients and web browsers will show the URL in the status bar when the mouse is hovering over it. However, some phishers may be able to bypass this security measure.[41]
Internationalized domain names (IDNs) can be exploited via IDN spoofing[42] or homograph attacks[43] to allow attackers to create fake websites with visually identical addresses to legitimate ones. These attacks have been used by phishers to disguise malicious URLs using open URL redirectors on trusted websites.[44][45][46] Even digital certificates, such as SSL, may not protect against these attacks as phishers can purchase valid certificates and alter content to mimic genuine websites or host phishing sites without SSL.[47]
Filter evasion
Phishers have sometimes used images instead of text to make it harder for anti-phishing filters to detect the text commonly used in phishing emails.[48] In response, more sophisticated anti-phishing filters are able to recover hidden text in images using optical character recognition (OCR).[49]
Social engineering
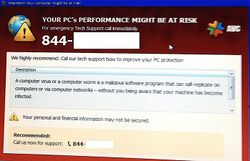
Phishing often uses social engineering techniques to trick users into performing actions such as clicking a link or opening an attachment, or revealing sensitive information. It often involves pretending to be a trusted entity and creating a sense of urgency,[50] like threatening to close or seize a victim's bank or insurance account.[51]
An alternative technique to impersonation-based phishing is the use of fake news articles to trick victims into clicking on a malicious link. These links often lead to fake websites that appear legitimate,[52] but are actually run by attackers who may try to install malware or present fake "virus" notifications to the victim.[53]
History
Early history
Early phishing techniques can be traced back to the 1990s, when black hat hackers and the warez community used AOL to steal credit card information and commit other online crimes. The term "phishing" is said to have been coined by Khan C. Smith, a well-known spammer and hacker,[54] and its first recorded mention was found in the hacking tool AOHell, which was released in 1995. AOHell allowed hackers to impersonate AOL staff and send instant messages to victims asking them to reveal their passwords.[55][56] In response, AOL implemented measures to prevent phishing and eventually shut down the warez scene on their platform.[57][58]
2000s
In the 2000s, phishing attacks became more organized and targeted. The first known direct attempt against a payment system, E-gold, occurred in June 2001, and shortly after the September 11 attacks, a "post-9/11 id check" phishing attack followed.[59] The first known phishing attack against a retail bank was reported in September 2003.[60] Between May 2004 and May 2005, approximately 1.2 million computer users in the United States suffered losses caused by phishing, totaling approximately US$929 million.[61] Phishing was recognized as a fully organized part of the black market, and specializations emerged on a global scale that provided phishing software for payment, which were assembled and implemented into phishing campaigns by organized gangs.[62][63] The United Kingdom banking sector suffered from phishing attacks, with losses from web banking fraud almost doubling in 2005 compared to 2004.[64][65] In 2006, almost half of phishing thefts were committed by groups operating through the Russian Business Network based in St. Petersburg.[66] Email scams posing as the Internal Revenue Service were also used to steal sensitive data from U.S. taxpayers.[67] Social networking sites are a prime target of phishing, since the personal details in such sites can be used in identity theft;[68] In 2007, 3.6 million adults lost US$3.2 billion due to phishing attacks.[69] The Anti-Phishing Working Group reported receiving 115,370 phishing email reports from consumers with US and China hosting more than 25% of the phishing pages each in the third quarter of 2009.[70]
2010s
Phishing in the 2010s saw a significant increase in the number of attacks. In 2011, the master keys for RSA SecurID security tokens were stolen through a phishing attack.[71][72] Chinese phishing campaigns also targeted high-ranking officials in the US and South Korean governments and military, as well as Chinese political activists.[73][74] According to Ghosh, phishing attacks increased from 187,203 in 2010 to 445,004 in 2012. In August 2013, Outbrain suffered a spear-phishing attack,[75] and in November 2013, 110 million customer and credit card records were stolen from Target customers through a phished subcontractor account.[76] CEO and IT security staff subsequently fired.[77] In August 2014, iCloud leaks of celebrity photos were based on phishing e-mails sent to victims that looked like they came from Apple or Google.[78] In November 2014, phishing attacks on ICANN gained administrative access to the Centralized Zone Data System; also gained was data about users in the system - and access to ICANN's public Governmental Advisory Committee wiki, blog, and whois information portal.[79] Fancy Bear was linked to spear-phishing attacks against the Pentagon email system in August 2015,[80][81] and the group used a zero-day exploit of Java in a spear-phishing attack on the White House and NATO.[82][83] Fancy Bear carried out spear phishing attacks on email addresses associated with the Democratic National Committee in the first quarter of 2016.[84][85] In August 2016, members of the Bundestag and political parties such as Linken-faction leader Sahra Wagenknecht, Junge Union, and the CDU of Saarland were targeted by spear-phishing attacks suspected to be carried out by Fancy Bear. In August 2016, the World Anti-Doping Agency reported the receipt of phishing emails sent to users of its database claiming to be official WADA, but consistent with the Russian hacking group Fancy Bear.[86][87][88] In 2017, 76% of organizations experienced phishing attacks, with nearly half of the information security professionals surveyed reporting an increase from 2016. In the first half of 2017, businesses and residents of Qatar were hit with over 93,570 phishing events in a three-month span.[89] In August 2017, customers of Amazon faced the Amazon Prime Day phishing attack, when hackers sent out seemingly legitimate deals to customers of Amazon. When Amazon's customers attempted to make purchases using the "deals", the transaction would not be completed, prompting the retailer's customers to input data that could be compromised and stolen.[90] In 2018, the company block.one, which developed the EOS.IO blockchain, was attacked by a phishing group who sent phishing emails to all customers aimed at intercepting the user's cryptocurrency wallet key, and a later attack targeted airdrop tokens.[91]
2020s
Phishing attacks have evolved in the 2020s to include elements of social engineering, as demonstrated by the July 15, 2020, Twitter breach. In this case, a 17-year-old hacker and accomplices set up a fake website resembling Twitter's internal VPN provider used by remote working employees. Posing as helpdesk staff, they called multiple Twitter employees, directing them to submit their credentials to the fake VPN website.[92] Using the details supplied by the unsuspecting employees, they were able to seize control of several high-profile user accounts, including those of Barack Obama, Elon Musk, Joe Biden, and Apple Inc.'s company account. The hackers then sent messages to Twitter followers soliciting Bitcoin, promising to double the transaction value in return. The hackers collected 12.86 BTC (about $117,000 at the time).[93]
Anti-phishing
There are anti-phishing websites which publish exact messages that have been recently circulating the internet, such as FraudWatch International and Millersmiles. Such sites often provide specific details about the particular messages.[94][95]
As recently as 2007, the adoption of anti-phishing strategies by businesses needing to protect personal and financial information was low.[96] Now there are several different techniques to combat phishing, including legislation and technology created specifically to protect against phishing. These techniques include steps that can be taken by individuals, as well as by organizations. Phone, web site, and email phishing can now be reported to authorities, as described below.
User training
Effective phishing education, including conceptual knowledge[97] and feedback,[98][99] is an important part of any organization's anti-phishing strategy. While there is limited data on the effectiveness of education in reducing susceptibility to phishing,[100] much information on the threat is available online.[51]
Simulated phishing campaigns, in which organizations test their employees' training by sending fake phishing emails, are commonly used to assess their effectiveness. One example is a study by the National Library of Medicine, in which an organization received 858,200 emails during a 1-month testing period, with 139,400 (16%) being marketing and 18,871 (2%) being identified as potential threats. These campaigns are often used in the healthcare industry, as healthcare data is a valuable target for hackers. These campaigns are just one of the ways that organizations are working to combat phishing.[101]
To avoid phishing attempts, people can modify their browsing habits[102] and be cautious of emails claiming to be from a company asking to "verify" an account. It's best to contact the company directly or manually type in their website address rather than clicking on any hyperlinks in suspicious emails.[103]
Nearly all legitimate e-mail messages from companies to their customers contain an item of information that is not readily available to phishers. Some companies, for example PayPal, always address their customers by their username in emails, so if an email addresses the recipient in a generic fashion ("Dear PayPal customer") it is likely to be an attempt at phishing.[104] Furthermore, PayPal offers various methods to determine spoof emails and advises users to forward suspicious emails to their spoof@PayPal.com domain to investigate and warn other customers. However it is unsafe to assume that the presence of personal information alone guarantees that a message is legitimate,[105] and some studies have shown that the presence of personal information does not significantly affect the success rate of phishing attacks;[106] which suggests that most people do not pay attention to such details.
Emails from banks and credit card companies often include partial account numbers, but research[107] has shown that people tend to not differentiate between the first and last digits. This is an issue because the first few digits are often the same for all clients of a financial institution.
A study on phishing attacks in game environments found that educational games can effectively educate players against information disclosures and can increase awareness on phishing risk thus mitigating risks.[108] This an example of how users can be trained through game based models.
The Anti-Phishing Working Group, who's one of the largest anti-phishing organizations in the world, produces regular report on trends in phishing attacks.[109]
Google posted a video demonstrating how to identify and protect yourself from Phishing scams.[110]
Technical approaches
A wide range of technical approaches are available to prevent phishing attacks reaching users or to prevent them from successfully capturing sensitive information.
Filtering out phishing mail
Specialized spam filters can reduce the number of phishing emails that reach their addressees' inboxes. These filters use a number of techniques including machine learning[111] and natural language processing approaches to classify phishing emails,[112][113] and reject email with forged addresses.[114]
Browsers alerting users to fraudulent websites

Another popular approach to fighting phishing is to maintain a list of known phishing sites and to check websites against the list. One such service is the Safe Browsing service.[115] Web browsers such as Google Chrome, Internet Explorer 7, Mozilla Firefox 2.0, Safari 3.2, and Opera all contain this type of anti-phishing measure.[116][117][118][119][120] Firefox 2 used Google anti-phishing software. Opera 9.1 uses live blacklists from Phishtank, cyscon and GeoTrust, as well as live whitelists from GeoTrust. Some implementations of this approach send the visited URLs to a central service to be checked, which has raised concerns about privacy.[121] According to a report by Mozilla in late 2006, Firefox 2 was found to be more effective than Internet Explorer 7 at detecting fraudulent sites in a study by an independent software testing company.[122]
An approach introduced in mid-2006 involves switching to a special DNS service that filters out known phishing domains: this will work with any browser,[123] and is similar in principle to using a hosts file to block web adverts.
To mitigate the problem of phishing sites impersonating a victim site by embedding its images (such as logos), several site owners have altered the images to send a message to the visitor that a site may be fraudulent. The image may be moved to a new filename and the original permanently replaced, or a server can detect that the image was not requested as part of normal browsing, and instead send a warning image.[124][125]
Augmenting password logins
The Bank of America website[126][127] is one of several that asks users to select a personal image (marketed as SiteKey) and displays this user-selected image with any forms that request a password. Users of the bank's online services are instructed to enter a password only when they see the image they selected. However, several studies suggest that few users refrain from entering their passwords when images are absent.[128][129] In addition, this feature (like other forms of two-factor authentication) is susceptible to other attacks, such as those suffered by Scandinavian bank Nordea in late 2005,[130] and Citibank in 2006.[131]
A similar system, in which an automatically generated "Identity Cue" consisting of a colored word within a colored box is displayed to each website user, is in use at other financial institutions.[132]
Security skins[133][134] are a related technique that involves overlaying a user-selected image onto the login form as a visual cue that the form is legitimate. Unlike the website-based image schemes, however, the image itself is shared only between the user and the browser, and not between the user and the website. The scheme also relies on a mutual authentication protocol, which makes it less vulnerable to attacks that affect user-only authentication schemes.
Still another technique relies on a dynamic grid of images that is different for each login attempt. The user must identify the pictures that fit their pre-chosen categories (such as dogs, cars and flowers). Only after they have correctly identified the pictures that fit their categories are they allowed to enter their alphanumeric password to complete the login. Unlike the static images used on the Bank of America website, a dynamic image-based authentication method creates a one-time passcode for the login, requires active participation from the user, and is very difficult for a phishing website to correctly replicate because it would need to display a different grid of randomly generated images that includes the user's secret categories.[135]
Monitoring and takedown
Several companies offer banks and other organizations likely to suffer from phishing scams round-the-clock services to monitor, analyze and assist in shutting down phishing websites.[136] Automated detection of phishing content is still below accepted levels for direct action, with content-based analysis reaching between 80% and 90% of success[137] so most of the tools include manual steps to certify the detection and authorize the response.[138] Individuals can contribute by reporting phishing to both volunteer and industry groups,[139] such as cyscon or PhishTank.[140] Phishing web pages and emails can be reported to Google.[141][142]
Transaction verification and signing
Solutions have also emerged using the mobile phone[143] (smartphone) as a second channel for verification and authorization of banking transactions.
Multi-factor authentication
Organizations can implement two factor or multi-factor authentication (MFA), which requires a user to use at least 2 factors when logging in. (For example, a user must both present a smart card and a password). This mitigates some risk, in the event of a successful phishing attack, the stolen password on its own cannot be reused to further breach the protected system. However, there are several attack methods which can defeat many of the typical systems.[144] MFA schemes such as WebAuthn address this issue by design.
Email content redaction
Organizations that prioritize security over convenience can require users of its computers to use an email client that redacts URLs from email messages, thus making it impossible for the reader of the email to click on a link, or even copy a URL. While this may result in an inconvenience, it does almost eliminate email phishing attacks.
Limitations of technical responses
An article in Forbes in August 2014 argues that the reason phishing problems persist even after a decade of anti-phishing technologies being sold is that phishing is "a technological medium to exploit human weaknesses" and that technology cannot fully compensate for human weaknesses.[145][146]
Organizational responses
Scholars have found that the investment into both technological and organizational factors can impact protection against phishing. The studies found that organizations can improve their technical education of employees if they include socio-technical factors in their training.[147]
Legal responses
On January 26, 2004, the U.S. Federal Trade Commission filed the first lawsuit against a California n teenager suspected of phishing by creating a webpage mimicking America Online and stealing credit card information.[148] Other countries have followed this lead by tracing and arresting phishers. A phishing kingpin, Valdir Paulo de Almeida, was arrested in Brazil for leading one of the largest phishing crime rings, which in two years stole between US$18 million and US$37 million.[149] UK authorities jailed two men in June 2005 for their role in a phishing scam,[150] in a case connected to the U.S. Secret Service Operation Firewall, which targeted notorious "carder" websites.[151] In 2006, Japanese police arrested eight people for creating fake Yahoo Japan websites, netting themselves ¥100 million (US$870,000)[152] and the FBI detained a gang of sixteen in the U.S. and Europe in Operation Cardkeeper.[153]
Senator Patrick Leahy introduced the Anti-Phishing Act of 2005 to Congress in the United States on March 1, 2005. This bill aimed to impose fines of up to $250,000 and prison sentences of up to five years on criminals who used fake websites and emails to defraud consumers.[154] In the UK, the Fraud Act 2006[155] introduced a general offense of fraud punishable by up to ten years in prison and prohibited the development or possession of phishing kits with the intention of committing fraud.[156]
Companies have also joined the effort to crack down on phishing. On March 31, 2005, Microsoft filed 117 federal lawsuits in the U.S. District Court for the Western District of Washington. The lawsuits accuse "John Doe" defendants of obtaining passwords and confidential information. March 2005 also saw a partnership between Microsoft and the Australian government teaching law enforcement officials how to combat various cyber crimes, including phishing.[157] Microsoft announced a planned further 100 lawsuits outside the U.S. in March 2006,[158] followed by the commencement, as of November 2006, of 129 lawsuits mixing criminal and civil actions.[159] AOL reinforced its efforts against phishing[160] in early 2006 with three lawsuits[161] seeking a total of US$18 million under the 2005 amendments to the Virginia Computer Crimes Act,[162][163] and Earthlink has joined in by helping to identify six men subsequently charged with phishing fraud in Connecticut.[164]
In January 2007, Jeffrey Brett Goodin of California became the first defendant convicted by a jury under the provisions of the CAN-SPAM Act of 2003. He was found guilty of sending thousands of emails to AOL users, while posing as the company's billing department, which prompted customers to submit personal and credit card information. Facing a possible 101 years in prison for the CAN-SPAM violation and ten other counts including wire fraud, the unauthorized use of credit cards, and the misuse of AOL's trademark, he was sentenced to serve 70 months. Goodin had been in custody since failing to appear for an earlier court hearing and began serving his prison term immediately.[165][166][167][168]
Notable incidents
- 2016–2021 literary phishing thefts
See also
- Software:Anti-phishing software
- Catfishing
- Clickjacking
- In-session phishing – Type of phishing attack
- Link farm
- Philosophy:List of cognitive biases, many abusable by phishing
- Mousetrapping
- Penetration test – Authorized cyberattack for testing purposes
- SiteKey – Web-based authentication service
- Trojan Horse
- TrustRank
- Typosquatting
References
- ↑ Jansson, K.; von Solms, R. (2011-11-09). "Phishing for phishing awareness" (in en). Behaviour & Information Technology 32 (6): 584–593. doi:10.1080/0144929X.2011.632650. ISSN 0144-929X. http://www.tandfonline.com/doi/abs/10.1080/0144929X.2011.632650.
- ↑ Ramzan, Zulfikar (2010). "Phishing attacks and countermeasures". Handbook of Information and Communication Security. Springer. ISBN 978-3-642-04117-4. https://books.google.com/books?id=I-9P1EkTkigC&pg=PA433.
- ↑ "Internet Crime Report 2020". U.S. Federal Bureau of Investigation. https://www.ic3.gov/Media/PDF/AnnualReport/2020_IC3Report.pdf.
- ↑ Ollmann, Gunter. "The Phishing Guide: Understanding and Preventing Phishing Attacks". Technical Info. http://www.technicalinfo.net/papers/Phishing.html.
- ↑ 5.0 5.1 5.2 Wright, A; Aaron, S; Bates, DW (October 2016). "The Big Phish: Cyberattacks Against U.S. Healthcare Systems.". Journal of General Internal Medicine 31 (10): 1115–8. doi:10.1007/s11606-016-3741-z. PMID 27177913.
- ↑ Stonebraker, Steve (January 2022). "AOL Underground". aolunderground.com (Podcast). Anchor.fm.
- ↑ Mitchell, Anthony (July 12, 2005). "A Leet Primer". TechNewsWorld. http://www.technewsworld.com/story/47607.html.
- ↑ "Phishing". Language Log, September 22, 2004. http://itre.cis.upenn.edu/~myl/languagelog/archives/001477.html.
- ↑ Jøsang, Audun (2007). "Security Usability Principles for Vulnerability Analysis and Risk Assessment.". Proceedings of the Annual Computer Security Applications Conference 2007 (ACSAC'07). https://www.researchgate.net/publication/27477067.
- ↑ Lin, Tian; Capecci, Daniel E.; Ellis, Donovan M.; Rocha, Harold A.; Dommaraju, Sandeep; Oliveira, Daniela S.; Ebner, Natalie C. (September 2019). "Susceptibility to Spear-Phishing Emails: Effects of Internet User Demographics and Email Content". ACM Transactions on Computer-Human Interaction 26 (5): 32. doi:10.1145/3336141. ISSN 1073-0516. PMID 32508486.
- ↑ "2019 Data Breach Investigations Report". Verizon Communications. https://www.phishingbox.com/assets/files/images/Verizon-Data-Breach-Investigations-Report-DBIR-2019.pdf.
- ↑ Furnell, Steven; Millet, Kieran; Papadaki, Maria (July 2019). "Fifteen years of phishing: can technology save us?". Computer Fraud & Security 2019 (7): 11–16. doi:10.1016/S1361-3723(19)30074-0. https://www.researchgate.net/publication/334551961. Retrieved 21 March 2021.
- ↑ Waddell, Kaveh (11 February 2016). "The Black Market for Netflix Accounts" (in en). https://www.theatlantic.com/technology/archive/2016/02/the-black-market-for-netflix-accounts/462321/.
- ↑ "Spear phishing". Windows IT Pro Center. https://docs.microsoft.com/en-us/windows/security/threat-protection/intelligence/phishing#spear-phishing.
- ↑ Stephenson, Debbie (2013-05-30). "Spear Phishing: Who's Getting Caught?". Firmex. http://www.firmex.com/blog/spear-phishing-whos-getting-caught/.
- ↑ "NSA/GCHQ Hacking Gets Personal: Belgian Cryptographer Targeted". Info Security magazine. 3 February 2018. https://www.infosecurity-magazine.com/news/nsagchq-hacking-gets-personal-belgian/.
- ↑ Leyden, John (4 April 2011). "RSA explains how attackers breached its systems". The Register. https://www.theregister.co.uk/2011/04/04/rsa_hack_howdunnit/.
- ↑ Winterford, Brett (7 April 2011). "Epsilon breach used four-month-old attack". itnews.com.au. https://www.itnews.com.au/news/epsilon-breach-used-four-month-old-attack-253712.
- ↑ O'Leary, Daniel E. (2019). "What Phishing E-mails Reveal: An Exploratory Analysis of Phishing Attempts Using Text Analyzes". SSRN Electronic Journal. doi:10.2139/ssrn.3427436. ISSN 1556-5068. http://dx.doi.org/10.2139/ssrn.3427436. Retrieved 2020-11-02.
- ↑ "Threat Group-4127 Targets Google Accounts" (in en). 26 June 2016. https://www.secureworks.com/research/threat-group-4127-targets-google-accounts.
- ↑ Nakashima, Ellen; Harris, Shane (July 13, 2018). "How the Russians hacked the DNC and passed its emails to WikiLeaks". The Washington Post. https://www.washingtonpost.com/world/national-security/how-the-russians-hacked-the-dnc-and-passed-its-emails-to-wikileaks/2018/07/13/af19a828-86c3-11e8-8553-a3ce89036c78_story.html?noredirect=on.
- ↑ Alkhalil, Z (2021). "Phishing attacks: A recent comprehensive study and a new anatomy". Frontiers in Computer Science 3. doi:10.3389/fcomp.2021.563060.
- ↑ "Fake subpoenas harpoon 2,100 corporate fat cats". The Register. https://www.theregister.co.uk/2008/04/16/whaling_expedition_continues/..
- ↑ "What Is 'Whaling'? Is Whaling Like 'Spear Phishing'?". About Tech. http://netforbeginners.about.com/od/scamsandidentitytheft/f/What-Is-Whaling-Spear-Phishing.htm.
- ↑ Junger, Marianne; Wang, Victoria; Schlömer, Marleen (December 2020). "Fraud against businesses both online and offline: crime scripts, business characteristics, efforts, and benefits". Crime Science 9 (1): 13. doi:10.1186/s40163-020-00119-4.
- ↑ "Action Fraud warning after serious rise in CEO fraud". https://www.actionfraud.police.uk/alert/action-fraud-warning-after-serious-rise-in-ceo-fraud.
- ↑ "Invoice scams affecting New Zealand businesses". NZCERT. https://www.cert.govt.nz/individuals/alerts/invoice-scams-affecting-new-zealand-businesses/.
- ↑ Parker, Tamsyn (18 August 2018). "House invoice scam leaves couple $53k out of pocket". The New Zealand Herald. https://www.nzherald.co.nz/personal-finance/news/article.cfm?c_id=12&objectid=12104611.
- ↑ 29.0 29.1 Griffin, Slade E.; Rackley, Casey C. (2008). "Vishing". Proceedings of the 5th annual conference on Information security curriculum development. pp. 33–35. doi:10.1145/1456625.1456635. ISBN 9781605583334.
- ↑ Wang, Xinyuan; Zhang, Ruishan; Yang, Xiaohui; Jiang, Xuxian; Wijesekera, Duminda (2008). "Voice pharming attack and the trust of VoIP". Proceedings of the 4th international conference on Security and privacy in communication netowrks. pp. 1–11. doi:10.1145/1460877.1460908. ISBN 9781605582412.
- ↑ "Phishing, Smishing, and Vishing: What's the Difference?". August 1, 2008. https://www.belvoircreditunion.org/system/files/336/original/PhishinMembers.pdf.
- ↑ Vishing and smishing: The rise of social engineering fraud , BBC, Marie Keyworth, 2016-01-01
- ↑ Steinmetz, Kevin F.; Holt, Thomas J. (2022-08-05). "Falling for Social Engineering: A Qualitative Analysis of Social Engineering Policy Recommendations" (in en). Social Science Computer Review: 089443932211175. doi:10.1177/08944393221117501. ISSN 0894-4393. http://journals.sagepub.com/doi/10.1177/08944393221117501.
- ↑ "SMS phishing article at ConsumerAffairs.com". 8 November 2006. http://www.consumeraffairs.com/news04/2006/11/smishing.html.
- ↑ Mishra, Sandhya; Soni, Devpriya (August 2019). "SMS Phishing and Mitigation Approaches". 2019 Twelfth International Conference on Contemporary Computing (IC3). IEEE. pp. 1–5. doi:10.1109/ic3.2019.8844920. ISBN 978-1-7281-3591-5.
- ↑ "What is Smishing?". Symantec Corporation. https://us.norton.com/internetsecurity-emerging-threats-what-is-smishing.html.
- ↑ Newman, Lily Hay. "Tricky Scam Plants Phishing Links in Your Google Calendar" (in en-US). Wired. ISSN 1059-1028. https://www.wired.com/story/phishing-links-google-calendar-invites/. Retrieved 2021-11-11.
- ↑ By (2019-08-27). "Scammers are targeting your calendar—here's how to stop them" (in en-US). https://www.popsci.com/google-calendar-spam-what-to-do/.
- ↑ 39.0 39.1 39.2 39.3 39.4 Wallen, Jack (2023-10-26). "Quishing is the new phishing: What you need to know". https://www.zdnet.com/article/quishing-is-the-new-phishing-what-you-need-to-know/.
- ↑ "Get smart on Phishing! Learn to read links!". http://www.bustspammers.com/phishing_links.html.
- ↑ Cimpanu, Catalin (June 15, 2016). "Hidden JavaScript Redirect Makes Phishing Pages Harder to Detect". Softpedia. http://news.softpedia.com/news/hidden-javascript-redirect-makes-phishing-pages-harder-to-detect-505295.shtml. "Hovering links to see their true location may be a useless security tip in the near future if phishers get smart about their mode of operation and follow the example of a crook who recently managed to bypass this browser built-in security feature."
- ↑ Johanson, Eric. "The State of Homograph Attacks Rev1.1". The Shmoo Group. http://www.shmoo.com/idn/homograph.txt.
- ↑ Evgeniy Gabrilovich; Alex Gontmakher (February 2002). "The Homograph Attack". Communications of the ACM 45 (2): 128. doi:10.1145/503124.503156. https://www.cs.technion.ac.il/~gabr/papers/homograph_full.pdf. Retrieved 2019-09-15.
- ↑ Leyden, John (August 15, 2006). "Barclays scripting SNAFU exploited by phishers". The Register. https://www.theregister.co.uk/2006/08/15/barclays_phish_scam/.
- ↑ Levine, Jason. "Goin' phishing with eBay". Q Daily News. http://q.queso.com/archives/001617.
- ↑ Leyden, John (December 12, 2007). "Cybercrooks lurk in shadows of big-name websites". The Register. https://www.theregister.co.uk/2007/12/12/phishing_redirection/.
- ↑ "Black Hat DC 2009". May 15, 2011. http://www.thoughtcrime.org/software/sslstrip/..
- ↑ Mutton, Paul (12 May 2005). "Fraudsters seek to make phishing sites undetectable by content filters". Netcraft. http://news.netcraft.com/archives/2005/05/12/fraudsters_seek_to_make_phishing_sites_undetectable_by_content_filters.html.
- ↑ "The use of Optical Character Recognition OCR software in spam filtering". http://www.powershow.com/viewfl/1f004e-ZDc1Z/The_use_of_Optical_Character_Recognition_OCR_software_in_spam_filtering_powerpoint_ppt_presentation.
- ↑ Cui, Xinyue; Ge, Yan; Qu, Weina; Zhang, Kan (2020). "Effects of Recipient Information and Urgency Cues on Phishing Detection". HCI International 2020 - Posters. Communications in Computer and Information Science. 1226. pp. 520–525. doi:10.1007/978-3-030-50732-9_67. ISBN 978-3-030-50731-2.
- ↑ 51.0 51.1 Williams, Emma J; Joinson, Adam N (2020-01-01). "Developing a measure of information seeking about phishing". Journal of Cybersecurity 6 (1). doi:10.1093/cybsec/tyaa001. ISSN 2057-2085.
- ↑ Lin, Tian; Capecci, Daniel E.; Ellis, Donovan M.; Rocha, Harold A.; Dommaraju, Sandeep; Oliveira, Daniela S.; Ebner, Natalie C. (September 2019). "Susceptibility to Spear-Phishing Emails: Effects of Internet User Demographics and Email Content". ACM Transactions on Computer-Human Interaction 26 (5). doi:10.1145/3336141. ISSN 1073-0516. PMID 32508486.
- ↑ Tomlinson, Kerry (27 January 2017). "Fake news can poison your computer as well as your mind". archersecuritygroup.com. http://www.archersecuritygroup.com/fake-news-can-poison-computer-well-mind/.
- ↑ "EarthLink wins $25 million lawsuit against junk e-mailer". http://www.bizjournals.com/atlanta/stories/2002/07/22/story4.html?page=all.
- ↑ Langberg, Mike (September 8, 1995). "AOL Acts to Thwart Hackers". San Jose Mercury News. http://simson.net/clips/1995/95.SJMN.AOL_Hackers.html.
- ↑ Rekouche, Koceilah (2011). "Early Phishing". arXiv:1106.4692 [cs.CR].
- ↑ "Phishing". Word Spy. http://www.wordspy.com/words/phishing.asp.
- ↑ "History of AOL Warez". http://www.rajuabju.com/warezirc/historyofaolwarez.htm.
- ↑ "GP4.3 – Growth and Fraud — Case #3 – Phishing". Financial Cryptography. December 30, 2005. https://financialcryptography.com/mt/archives/000609.html.
- ↑ Sangani, Kris (September 2003). "The Battle Against Identity Theft". The Banker 70 (9): 53–54.
- ↑ Kerstein, Paul (July 19, 2005). "How Can We Stop Phishing and Pharming Scams?". CSO. http://www.csoonline.com/talkback/071905.html.
- ↑ "In 2005, Organized Crime Will Back Phishers". IT Management. December 23, 2004. http://itmanagement.earthweb.com/secu/article.php/3451501.
- ↑ Abad, Christopher (September 2005). "The economy of phishing: A survey of the operations of the phishing market". First Monday. http://firstmonday.org/htbin/cgiwrap/bin/ojs/index.php/fm/article/view/1272/1192.
- ↑ "UK phishing fraud losses double". Finextra. March 7, 2006. http://www.finextra.com/fullstory.asp?id=15013.
- ↑ Richardson, Tim (May 3, 2005). "Brits fall prey to phishing". The Register. https://www.theregister.co.uk/2005/05/03/aol_phishing/.
- ↑ Krebs, Brian (October 13, 2007). "Shadowy Russian Firm Seen as Conduit for Cybercrime". The Washington Post. https://www.washingtonpost.com/wp-dyn/content/story/2007/10/12/ST2007101202661.html?hpid=topnews.
- ↑ "Suspicious e-Mails and Identity Theft". Internal Revenue Service. https://www.irs.gov/newsroom/article/0,,id=155682,00.html.
- ↑ Kirk, Jeremy (June 2, 2006). "Phishing Scam Takes Aim at MySpace.com". IDG Network. http://www.pcworld.com/resource/article/0,aid,125956,pg,1,RSS,RSS,00.asp.
- ↑ McCall, Tom (December 17, 2007). "Gartner Survey Shows Phishing Attacks Escalated in 2007; More than $3 Billion Lost to These Attacks". Gartner. http://www.gartner.com/it/page.jsp?id=565125.
- ↑ APWG. "Phishing Activity Trends Report". http://apwg.org/reports/apwg_report_Q3_2009.pdf.
- ↑ "Anatomy of an RSA attack". RSA FraudAction Research Labs. https://blogs.rsa.com/anatomy-of-an-attack/.
- ↑ Drew, Christopher; Markoff, John (May 27, 2011). "Data Breach at Security Firm Linked to Attack on Lockheed". The New York Times. https://www.nytimes.com/2011/05/28/business/28hack.html.
- ↑ Keizer, Greg (2011-08-13). "Suspected Chinese spear-phishing attacks continue to hit Gmail users". Computerworld. http://www.computerworld.com/s/article/9219155/Suspected_Chinese_spear_phishing_attacks_continue_to_hit_Gmail_users.
- ↑ Ewing, Philip (2011-08-22). "Report: Chinese TV doc reveals cyber-mischief". Dod Buzz. http://www.dodbuzz.com/2011/08/22/report-chinese-tv-doc-reveals-cyber-mischief/.
- ↑ "Syrian hackers Use Outbrain to Target The Washington Post, Time, and CNN" , Philip Bump, The Atlantic Wire, 15 August 2013. Retrieved 15 August 2013.
- ↑ O'Connell, Liz. "Report: Email phishing scam led to Target breach". Bring Me the News. http://bringmethenews.com/2014/02/12/report-email-phishing-scam-led-to-target-breach/.
- ↑ Ausick, Paul. "Target CEO Sack". http://247wallst.com/retail/2014/05/05/target-ceo-sacked/.
- ↑ Prosecutors find that ‘Fappening’ celebrity nudes leak was not Apple’s fault March 15, 2016, Techcrunch
- ↑ "ICANN Targeted in Spear Phishing Attack | Enhanced Security Measures Implemented". https://www.icann.org/news/announcement-2-2014-12-16-en.
- ↑ Kube, Courtney (7 August 2015). "Russia hacks Pentagon computers: NBC, citing sources". https://www.cnbc.com/2015/08/06/russia-hacks-pentagon-computers-nbc-citing-sources.html.
- ↑ Starr, Barbara (7 August 2015). "Official: Russia suspected in Joint Chiefs email server intrusion". http://edition.cnn.com/2015/08/05/politics/joint-staff-email-hack-vulnerability/.
- ↑ Doctorow, Cory (August 28, 2015). "Spear phishers with suspected ties to Russian government spoof fake EFF domain, attack White House". Boing Boing. http://boingboing.net/2015/08/28/spear-phishers-with-suspected.html.
- ↑ Quintin, Cooper (August 27, 2015). "New Spear Phishing Campaign Pretends to be EFF". EFF. https://www.eff.org/deeplinks/2015/08/new-spear-phishing-campaign-pretends-be-eff.
- ↑ Sanger, David E.; Corasaniti, Nick (14 June 2016). "D.N.C. Says Russian Hackers Penetrated Its Files, Including Dossier on Donald Trump". The New York Times. https://www.nytimes.com/2016/06/15/us/politics/russian-hackers-dnc-trump.html.
- ↑ Economist, Staff of (24 September 2016). "Bear on bear". Economist. https://www.economist.com/news/united-states/21707574-whats-worse-being-attacked-russian-hacker-being-attacked-two-bear-bear.
- ↑ Hyacinth Mascarenhas (August 23, 2016). "Russian hackers 'Fancy Bear' likely breached Olympic drug-testing agency and DNC, experts say". International Business Times. http://www.ibtimes.co.uk/russian-hackers-fancy-bear-likely-breached-olympic-drug-testing-agency-dnc-experts-say-1577508.
- ↑ "What we know about Fancy Bears hack team". BBC News. 2016-09-15. http://www.bbc.co.uk/newsbeat/article/37374053/what-we-know-about-fancy-bears-hack-team.
- ↑ Gallagher, Sean (6 October 2016). "Researchers find fake data in Olympic anti-doping, Guccifer 2.0 Clinton dumps". Ars Technica. https://arstechnica.com/security/2016/10/researchers-find-fake-data-in-olympic-anti-doping-guccifer-2-0-clinton-dumps/.
- ↑ "Qatar faced 93,570 phishing attacks in first quarter of 2017" (in ar). Gulf Times. 2017-05-12. http://www.gulf-times.com/story/547784/Qatar-faced-93-570-phishing-attacks-in-first-quart.
- ↑ "Amazon Prime Day phishing scam spreading now!" (in en-us). The Kim Komando Show. https://www.komando.com/happening-now/415020/amazon-prime-day-phishing-scam-spreading-now.
- ↑ "Cryptocurrency Hackers Are Stealing from EOS's $4 Billion ICO Using This Sneaky Scam" (in en-us). Jen Wieczner. https://fortune.com/2018/05/31/cryptocurrency-eos-ico-scam/.
- ↑ "Twitter Investigation Report - Department of Financial Services" (in en). 2020-10-14. https://www.dfs.ny.gov/Twitter_Report.
- ↑ "Three Individuals Charged For Alleged Roles In Twitter Hack" (in en-US). https://www.justice.gov/opa/press-release/file/1300246/download.
- ↑ "Millersmiles Home Page". Oxford Information Services. http://www.millersmiles.co.uk.
- ↑ "FraudWatch International Home Page". FraudWatch International. http://www.fraudwatchinternational.com.
- ↑ Baker, Emiley; Wade Baker; John Tedesco (2007). "Organizations Respond to Phishing: Exploring the Public Relations Tackle Box". Communication Research Reports 24 (4): 327. doi:10.1080/08824090701624239.
- ↑ Arachchilage, Nalin; Love, Steve; Scott, Michael (June 1, 2012). "Designing a Mobile Game to Teach Conceptual Knowledge of Avoiding 'Phishing Attacks'". International Journal for E-Learning Security 2 (1): 127–132. doi:10.20533/ijels.2046.4568.2012.0016.
- ↑ "Protecting People from Phishing: The Design and Evaluation of an Embedded Training Email System". Technical Report CMU-CyLab-06-017, CyLab, Carnegie Mellon University.. November 2006. http://www.cylab.cmu.edu/files/cmucylab06017.pdf.
- ↑ Perrault, Evan K. (2017-03-23). "Using an Interactive Online Quiz to Recalibrate College Students' Attitudes and Behavioral Intentions About Phishing" (in en). Journal of Educational Computing Research 55 (8): 1154–1167. doi:10.1177/0735633117699232.
- ↑ Jampen, Daniel; Gür, Gürkan; Sutter, Thomas; Tellenbach, Bernhard (December 2020). "Don't click: towards an effective anti-phishing training. A comparative literature review" (in en). Human-centric Computing and Information Sciences 10 (1): 33. doi:10.1186/s13673-020-00237-7. ISSN 2192-1962.
- ↑ Priestman, Ward; Anstis, Tony; Sebire, Isabel G; Sridharan, Shankar; Sebire, Neil J (2019-09-04). "Phishing in healthcare organisations: threats, mitigation and approaches". BMJ Health & Care Informatics 26 (1): e100031. doi:10.1136/bmjhci-2019-100031. ISSN 2632-1009. PMID 31488498.
- ↑ Hendric, William. "Steps to avoid phishing". https://www.comodo.com/resources/home/phishing-scams.php.
- ↑ "Anti-Phishing Tips You Should Not Follow". HexView. http://www.hexview.com/sdp/node/24.
- ↑ "Protect Yourself from Fraudulent Emails". PayPal. https://www.paypal.com/us/cgi-bin/webscr?cmd=_vdc-security-spoof-outside.
- ↑ Zeltser, Lenny (March 17, 2006). "Phishing Messages May Include Highly-Personalized Information". The SANS Institute. http://isc.incidents.org/diary.php?storyid=1194.
- ↑ "Designing Ethical Phishing Experiments". WWW '06. http://www2006.org/programme/item.php?id=3533.
- ↑ "What Instills Trust? A Qualitative Study of Phishing". http://www.informatics.indiana.edu/markus/papers/trust_USEC.pdf.
- ↑ Fatima, Rubia; Yasin, Affan; Liu, Lin; Wang, Jianmin (2019-10-11). "How persuasive is a phishing email? A phishing game for phishing awareness". Journal of Computer Security 27 (6): 581–612. doi:10.3233/JCS-181253. https://www.medra.org/servlet/aliasResolver?alias=iospress&doi=10.3233/JCS-181253.
- ↑ "APWG Phishing Attack Trends Reports". https://www.antiphishing.org/resources/apwg-reports/.
- ↑ Google (June 25, 2017). "Stay Safe from Phishing and Scams". https://www.youtube.com/watch?v=R12_y2BhKbE.
- ↑ Olivo, Cleber K.; Santin, Altair O.; Oliveira, Luiz S. (July 2011). "Obtaining the Threat Model for E-mail Phishing". Applied Soft Computing 13 (12): 4841–4848. doi:10.1016/j.asoc.2011.06.016.
- ↑ "Phishing E-mail Detection Based on Structural Properties". NYS Cyber Security Symposium. March 2006. http://www.albany.edu/iasymposium/2006/chandrasekaran.pdf.
- ↑ "Learning to Detect Phishing Emails". Carnegie Mellon University Technical Report CMU-ISRI-06-112. June 2006. http://reports-archive.adm.cs.cmu.edu/anon/isri2006/CMU-ISRI-06-112.pdf.
- ↑ "Landing another blow against email phishing (Google Online Security Blog)". http://googleonlinesecurity.blogspot.jp/2012/01/landing-another-blow-against-email.html.
- ↑ "Google Safe Browsing". https://www.google.com/safebrowsing/static/faq.html.
- ↑ "Safe Browsing (Google Online Security Blog)". http://googleonlinesecurity.blogspot.jp/2012/06/safe-browsing-protecting-web-users-for.html.
- ↑ Franco, Rob (21 November 2005). "Better Website Identification and Extended Validation Certificates in IE7 and Other Browsers". IEBlog. https://docs.microsoft.com/en-us/archive/blogs/ie/better-website-identification-and-extended-validation-certificates-in-ie7-and-other-browsers.
- ↑ "Bon Echo Anti-Phishing". Mozilla. https://www.mozilla.org/projects/bonecho/anti-phishing/.
- ↑ "Safari 3.2 finally gains phishing protection". Ars Technica. November 13, 2008. https://arstechnica.com/journals/apple.ars/2008/11/13/safari-3-2-finally-gains-phishing-protection.
- ↑ "Gone Phishing: Evaluating Anti-Phishing Tools for Windows". 3Sharp. September 27, 2006. http://www.3sharp.com/projects/antiphish/index.htm.
- ↑ "Two Things That Bother Me About Google's New Firefox Extension". Nitesh Dhanjani on O'Reilly ONLamp. http://www.oreillynet.com/onlamp/blog/2005/12/two_things_that_bother_me_abou.html.
- ↑ "Firefox 2 Phishing Protection Effectiveness Testing". https://www.mozilla.org/security/phishing-test.html.
- ↑ Higgins, Kelly Jackson. "DNS Gets Anti-Phishing Hook". Dark Reading. http://www.darkreading.com/document.asp?doc_id=99089&WT.svl=news1_1.
- ↑ Krebs, Brian (August 31, 2006). "Using Images to Fight Phishing". Security Fix. http://blog.washingtonpost.com/securityfix/2006/08/using_images_to_fight_phishing.html.
- ↑ Seltzer, Larry (August 2, 2004). "Spotting Phish and Phighting Back". eWeek. http://www.eweek.com/article2/0,1759,1630161,00.asp.
- ↑ Bank of America. "How Bank of America SiteKey Works For Online Banking Security". http://www.bankofamerica.com/.
- ↑ Brubaker, Bill (July 14, 2005). "Bank of America Personalizes Cyber-Security". The Washington Post. https://www.washingtonpost.com/wp-dyn/content/article/2005/07/13/AR2005071302181.html.
- ↑ Stone, Brad (February 5, 2007). "Study Finds Web Antifraud Measure Ineffective". The New York Times. https://www.nytimes.com/2007/02/05/technology/05secure.html?ex=1328331600&en=295ec5d0994b0755&ei=5090&partner=rssuserland&emc=rss.
- ↑ "The Emperor's New Security Indicators: An evaluation of website authentication and the effect of role playing on usability studies". IEEE Symposium on Security and Privacy, May 2007. May 2007. http://www.deas.harvard.edu/~rachna/papers/emperor-security-indicators-bank-sitekey-phishing-study.pdf.
- ↑ "Phishers target Nordea's one-time password system". Finextra. October 12, 2005. http://www.finextra.com/fullstory.asp?id=14384.
- ↑ Krebs, Brian (July 10, 2006). "Citibank Phish Spoofs 2-Factor Authentication". Security Fix. http://blog.washingtonpost.com/securityfix/2006/07/citibank_phish_spoofs_2factor_1.html.
- ↑ Graham Titterington. "More doom on phishing". Ovum Research, April 2006. http://www.ovum.com/news/euronews.asp?id=4166.
- ↑ Schneier, Bruce. "Security Skins". Schneier on Security. http://www.schneier.com/blog/archives/2005/07/security_skins.html.
- ↑ "The Battle Against Phishing: Dynamic Security Skins". Symposium On Usable Privacy and Security (SOUPS) 2005. July 2005. http://people.deas.harvard.edu/~rachna/papers/securityskins.pdf.
- ↑ "Dynamic, Mutual Authentication Technology for Anti-Phishing". Confidenttechnologies.com. http://www.confidenttechnologies.com/products/anti-phishing.
- ↑ "Anti-Phishing Working Group: Vendor Solutions". Anti-Phishing Working Group. http://www.antiphishing.org/solutions.html#takedown.
- ↑ Xiang, Guang; Hong, Jason; Rose, Carolyn P.; Cranor, Lorrie (2011-09-01). "CANTINA+: A Feature-Rich Machine Learning Framework for Detecting Phishing Web Sites". ACM Transactions on Information and System Security 14 (2): 21:1–21:28. doi:10.1145/2019599.2019606. ISSN 1094-9224. https://doi.org/10.1145/2019599.2019606. Retrieved 2020-11-25.
- ↑ Leite, Cristoffer; Gondim, Joao J. C.; Barreto, Priscila Solis; Alchieri, Eduardo A. (2019). "Waste Flooding: A Phishing Retaliation Tool". 2019 IEEE 18th International Symposium on Network Computing and Applications (NCA). Cambridge, MA, USA: IEEE. pp. 1–8. doi:10.1109/NCA.2019.8935018. ISBN 978-1-7281-2522-0. https://ieeexplore.ieee.org/document/8935018. Retrieved 2020-11-25.
- ↑ McMillan, Robert (March 28, 2006). "New sites let users find and report phishing". LinuxWorld. http://www.linuxworld.com.au/index.php/id;1075406575;fp;2;fpid;1..
- ↑ Schneier, Bruce (October 5, 2006). "PhishTank". Schneier on Security. http://www.schneier.com/blog/archives/2006/10/phishtank.html.
- ↑ "Report a Phishing Page". https://safebrowsing.google.com/safebrowsing/report_phish/?hl=en.
- ↑ How to report phishing scams to Google Consumer Scams.org
- ↑ Using the smartphone to verify and sign online banking transactions , SafeSigner.
- ↑ Kan, Michael (7 March 2019). "Google: Phishing Attacks That Can Beat Two-Factor Are on the Rise". PC Magazine. https://www.pcmag.com/news/367026/google-phishing-attacks-that-can-beat-two-factor-are-on-the.
- ↑ Joseph Steinberg (August 25, 2014). "Why You Are at Risk of Phishing Attacks". Forbes. https://www.forbes.com/sites/josephsteinberg/2014/08/25/why-you-are-at-risk-of-phishing-attacks-and-why-jp-morgan-chase-customers-were-targeted-this-week/.
- ↑ Abroshan, Hossein; Devos, Jan; Poels, Geert; Laermans, Eric (2021). "Phishing Happens Beyond Technology: The Effects of Human Behaviors and Demographics on Each Step of a Phishing Process". IEEE Access 9: 44928–44949. doi:10.1109/ACCESS.2021.3066383. Bibcode: 2021IEEEA...944928A.
- ↑ "https://csu-sfsu.primo.exlibrisgroup.com/discovery/fulldisplay?docid=cdi_proquest_journals_2592765513&context=PC&vid=01CALS_SFR:01CALS_SFR&lang=en&search_scope=Everything_RAPIDO&adaptor=Primo%20Central&tab=Everything&query=any,contains,phishing%20attacks&offset=0" (in en). https://csu-sfsu.primo.exlibrisgroup.com/discovery/fulldisplay?docid=cdi_proquest_journals_2592765513&context=PC&vid=01CALS_SFR:01CALS_SFR&lang=en&search_scope=Everything_RAPIDO&adaptor=Primo%20Central&tab=Everything&query=any,contains,phishing%20attacks&offset=0.
- ↑ Legon, Jeordan (January 26, 2004). "Phishing scams reel in your identity". CNN. http://www.cnn.com/2003/TECH/internet/07/21/phishing.scam/index.html.
- ↑ Leyden, John (March 21, 2005). "Brazilian cops net 'phishing kingpin'". The Register. http://www.channelregister.co.uk/2005/03/21/brazil_phishing_arrest/.
- ↑ Roberts, Paul (June 27, 2005). "UK Phishers Caught, Packed Away". eWEEK. http://www.eweek.com/article2/0%2C1895%2C1831960%2C00.asp.
- ↑ "Nineteen Individuals Indicted in Internet 'Carding' Conspiracy". justice.gov. https://www.justice.gov/archive/opa/pr/2004/October/04_crm_726.htm.
- ↑ "8 held over suspected phishing fraud". Yomiuri Shimbun. May 31, 2006.
- ↑ "Phishing gang arrested in USA and Eastern Europe after FBI investigation". http://www.sophos.com/pressoffice/news/articles/2006/11/phishing-arrests.html.
- ↑ "Phishers Would Face 5 Years Under New Bill". InformationWeek. March 2, 2005. http://informationweek.com/story/showArticle.jhtml?articleID=60404811.
- ↑ "Fraud Act 2006". http://www.opsi.gov.uk/ACTS/en2006/2006en35.htm.
- ↑ "Prison terms for phishing fraudsters". The Register. November 14, 2006. https://www.theregister.co.uk/2006/11/14/fraud_act_outlaws_phishing/.
- ↑ "Microsoft Partners with Australian Law Enforcement Agencies to Combat Cyber Crime". http://www.microsoft.com/australia/presspass/news/pressreleases/cybercrime_31_3_05.aspx.
- ↑ Espiner, Tom (March 20, 2006). "Microsoft launches legal assault on phishers". ZDNet. http://news.zdnet.co.uk/0,39020330,39258528,00.htm.
- ↑ Leyden, John (November 23, 2006). "MS reels in a few stray phish". The Register. https://www.theregister.co.uk/2006/11/23/ms_anti-phishing_campaign_update/.
- ↑ "A History of Leadership – 2006". http://corp.aol.com/whoweare/history/2006.shtml.
- ↑ "AOL Takes Fight Against Identity Theft To Court, Files Lawsuits Against Three Major Phishing Gangs". http://media.aoltimewarner.com/media/newmedia/cb_press_view.cfm?release_num=55254535.
- ↑ "HB 2471 Computer Crimes Act; changes in provisions, penalty.". http://leg1.state.va.us/cgi-bin/legp504.exe?051+sum+HB2471.
- ↑ Brulliard, Karin (April 10, 2005). "Va. Lawmakers Aim to Hook Cyberscammers". The Washington Post. https://www.washingtonpost.com/wp-dyn/articles/A40578-2005Apr9.html.
- ↑ "Earthlink evidence helps slam the door on phisher site spam ring". http://www.earthlink.net/about/press/pr_phishersite/.
- ↑ Prince, Brian (January 18, 2007). "Man Found Guilty of Targeting AOL Customers in Phishing Scam". PC Magazine. https://www.pcmag.com/article2/0,1895,2085183,00.asp.
- ↑ Leyden, John (January 17, 2007). "AOL phishing fraudster found guilty". The Register. https://www.theregister.co.uk/2007/01/17/aol_phishing_fraudster/.
- ↑ Leyden, John (June 13, 2007). "AOL phisher nets six years' imprisonment". The Register. https://www.theregister.co.uk/2007/06/13/aol_fraudster_jailed/.
- ↑ Gaudin, Sharon (June 12, 2007). "California Man Gets 6-Year Sentence For Phishing". InformationWeek. http://www.informationweek.com/story/showArticle.jhtml?articleID=199903450.
External links
- Anti-Phishing Working Group
- Center for Identity Management and Information Protection – Utica College
- Plugging the "phishing" hole: legislation versus technology – Duke Law & Technology Review
- Example of a Phishing Attempt with Screenshots and Explanations – StrategicRevenue.com
- A Profitless Endeavor: Phishing as Tragedy of the Commons – Microsoft Corporation
- Database for information on phishing sites reported by the public – PhishTank
- The Impact of Incentives on Notice and Take-down − Computer Laboratory, University of Cambridge (PDF, 344 kB)
| This article is part of a series on |
| Information security |
|---|
| Related security categories |
| Threats |
| Defenses |
 |
