Attack tree
Attack trees are conceptual diagrams showing how an asset, or target, might be attacked.REFERENCE FOR RFC4949 IS NOT DEFINED YET. You are invited to add it here. Attack trees have been used in a variety of applications. In the field of information technology, they have been used to describe threats on computer systems and possible attacks to realize those threats. However, their use is not restricted to the analysis of conventional information systems. They are widely used in the fields of defense and aerospace for the analysis of threats against tamper resistant electronics systems (e.g., avionics on military aircraft).[1] Attack trees are increasingly being applied to computer control systems (especially relating to the electric power grid).[2] Attack trees have also been used to understand threats to physical systems.
Some of the earliest descriptions of attack trees are found in papers and articles by Bruce Schneier,[3] when he was CTO of Counterpane Internet Security. Schneier was clearly involved in the development of attack tree concepts and was instrumental in publicizing them. However, the attributions in some of the early publicly available papers on attack trees[4] also suggest the involvement of the National Security Agency in the initial development.
Attack trees are very similar, if not identical, to threat trees. Threat trees were developed by Jonathan Weiss of Bell Laboratories to comply with guidance in MIL STD 1785[5] for AT&T's work on Command and Control for federal applications, and were first described in his paper in 1982.[6] This work was later discussed in 1994 by Edward Amoroso.[7]
Basic
Attack trees are multi-leveled diagrams consisting of one root, leaves, and children. From the bottom up, child nodes are conditions which must be satisfied to make the direct parent node true; when the root is satisfied, the attack is complete. Each node may be satisfied only by its direct child nodes.
A node may be the child of another node; in such a case, it becomes logical that multiple steps must be taken to carry out an attack. For example, consider classroom computers which are secured to the desks. To steal one, the securing cable must be cut or the lock unlocked. The lock may be unlocked by picking or by obtaining the key. The key may be obtained by threatening a key holder, bribing a keyholder, or taking it from where it is stored (e.g. under a mousemat). Thus a four level attack tree can be drawn, of which one path is (Bribe Keyholder, Obtain Key, Unlock Lock, Steal Computer).
An attack described in a node may require one or more of many attacks described in child nodes to be satisfied. Our above condition shows only OR conditions; however, an AND condition can be created, for example, by assuming an electronic alarm which must be disabled if and only if the cable will be cut. Rather than making this task a child node of cutting the lock, both tasks can simply reach a summing junction. Thus the path ((Disable Alarm, Cut Cable), Steal Computer) is created.
Attack trees are related to the established fault tree formalism.[8] Fault tree methodology employs boolean expressions to gate conditions when parent nodes are satisfied by leaf nodes. By including a priori probabilities with each node, it is possible to perform calculate probabilities with higher nodes using Bayes Rule. However, in reality accurate probability estimates are either unavailable or too expensive to gather. With respect to computer security with active participants (i.e., attackers), the probability distribution of events are probably not independent nor uniformly distributed, hence, naive Bayesian analysis is unsuitable.
Since the Bayesian analytic techniques used in fault tree analysis cannot legitimately be applied to attack trees, analysts instead use other techniques[9][10] to determine which attacks will be preferred by a particular attacker. These may involve comparing the attacker's capabilities (time, money, skill, equipment) with the resource requirements of the specified attack. Attacks which are near or beyond the attacker's ability to perform are less preferred than attacks that are perceived as cheap and easy. The degree to which an attack satisfies the adversary's objectives also affects the attacker's choices. Attacks that are both within the adversary's capabilities, and which satisfy their goals, are more likely than those that do not.
Examination
Attack trees can become large and complex, especially when dealing with specific attacks. A full attack tree may contain hundreds or thousands of different paths all leading to completion of the attack. Even so, these trees are very useful for determining what threats exist and how to deal with them.
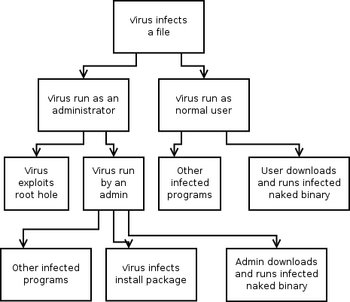
Attack trees can lend themselves to defining an information assurance strategy. It is important to consider, however, that implementing policy to execute this strategy changes the attack tree. For example, computer viruses may be protected against by refusing the system administrator access to directly modify existing programs and program folders, instead requiring a package manager be used. This adds to the attack tree the possibility of design flaws or exploits in the package manager.
One could observe that the most effective way to mitigate a threat on the attack tree is to mitigate it as close to the root as possible. Although this is theoretically sound, it is not usually possible to simply mitigate a threat without other implications to the continued operation of the system. For example, the threat of viruses infecting a Windows system may be largely reduced by using a standard (non-administrator) account and NTFS instead of FAT file system so that normal users are unable to modify the operating system. Implementing this negates any way, foreseen or unforeseen, that a normal user may come to infect the operating system with a virus ; however, it also requires that users switch to an administrative account to carry out administrative tasks, thus creating a different set of threats on the tree and more operational overhead. Also, users are still able to infect files to which they have write permissions, which may include files and documents.
Systems using cooperative agents that dynamically examine and identify vulnerability chains, creating attack trees, have been built since 2000.[11]
Attack tree modeling software
Several commercial packages and open source products are available.
Open source
- ADTool from University of Luxembourg
- AT-AT
- Deciduous
- Ent
- SeaMonster
Commercial
- "medini"" Ansys medini analyze from Ansys part of Synopsys
- AttackTree+ from Isograph
- SecurITree from Amenaza Technologies
- RiskTree from 2T Security
- RiskyTrees from RiskyTrees
See also
- Computer insecurity
- Computer security
- Computer virus
- Fault tree analysis
- IT risk
- Threat (computer)
- Vulnerability (computing)
References
- ↑ U.S. Department of Defense, "Defense Acquisition Guidebook", Section 8.5.3.3
- ↑ Chee-Wooi Ten, Chen-Ching Liu, Manimaran Govindarasu, Vulnerability Assessment of Cybersecurity for SCADA Systems Using Attack Trees, "Archived copy". Archived from the original on 2010-06-30. https://web.archive.org/web/20100630060200/http://powercyber.ece.iastate.edu/publications/GM-CS.pdf. Retrieved 2012-04-04.
- ↑ Schneier, Bruce (December 1999). "Attack Trees". Dr Dobb's Journal, v.24, n.12. Archived from the original on 6 August 2007. https://web.archive.org/web/20070806193149/http://www.schneier.com/paper-attacktrees-ddj-ft.html. Retrieved 2007-08-16.
- ↑ Chris Salter, O. Sami Saydjari, Bruce Schneier, Jim Wallner, Toward a Secure System Engineering Methodology, "Archived copy". Archived from the original on 2011-06-23. https://web.archive.org/web/20110623125141/http://www.schneier.com/paper-secure-methodology.pdf. Retrieved 2012-04-04.
- ↑ "MIL-STD-1785 SYSTEM SECURITY ENGINEERING PROGRAM". everyspec.com. Retrieved 2023-09-05
- ↑ "A System Security Engineering Process, 14th National Computer Security Conference, Washington DC". https://csrc.nist.gov/CSRC/media/Publications/conference-paper/1991/10/01/proceedings-14th-national-computer-security-conference-1991/documents/1991-14th-NCSC-proceedings-vol-2.pdf. Retrieved 2023-03-18.
- ↑ Amoroso, Edward (1994). Fundamentals of Computer Security. Upper Saddle River: Prentice Hall. ISBN 0-13-108929-3. https://archive.org/details/fundamentalsofco00amor.
- ↑ "Fault Tree Handbook with Aerospace Applications". https://elibrary.gsfc.nasa.gov/_assets/doclibBidder/tech_docs/25.%20NASA_Fault_Tree_Handbook_with_Aerospace_Applications%20-%20Copy.pdf. Retrieved 2019-02-26.
- ↑ Donald L Buckshaw, Gregory S Parnell, Willard L Ulkenholz, Donald L Parks, James M Wallner, O. Sami Saydjari, Mission Oriented Design Analysis of Critical Information Systems, Military Operations Research V10, N2, 2005, [1]
- ↑ Terrance R Ingoldsby, Amenaza Technologies Limited, Attack Tree-based Threat Risk Analysis, A vendor white paper, "Archived copy". Archived from the original on 2016-03-04. https://web.archive.org/web/20160304044711/http://www.amenaza.com/downloads/docs/AttackTreeThreatRiskAnalysis.pdf. Retrieved 2012-04-09.
- ↑ "NOOSE - Networked Object-Oriented Security Examiner, 14th Systems Administration Conference (LISA 2000), New Orleans". http://www.usenix.org/events/lisa00/full_papers/barnett/barnett_html/. Retrieved 2010-04-21.
 |
