Spoofed URL
A spoofed URL involves one website masquerading as another, often leveraging vulnerabilities in web browser technology to facilitate a malicious computer attack. These attacks are particularly effective against computers that lack up-to- security patches. Alternatively, some spoofed URLs are crafted for satirical purposes.
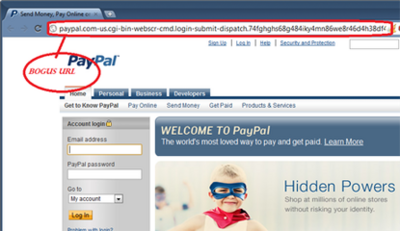
In such an attack scenario, an unsuspecting computer user visits a website and observes a familiar URL, like http://www.wikipedia.org, in the address bar. However, unbeknownst to them, the information they input is being directed to a completely different location, usually monitored by an information thief. When a fraudulent website requests sensitive information, it's referred to as phishing.
These fraudulent websites often entice users through emails or hyperlinks.
In a different variation, a website might resemble the original but is, in reality, a parody. These instances are generally harmless and conspicuously distinct from the genuine sites, as they typically do not exploit web browser vulnerabilities.
Another avenue for these exploits involves redirects within a hosts file, rerouting traffic from legitimate sites to an alternate IP associated with the spoofed URL.[1]
Cyber security
Spoofing is the act of deception or hoaxing.[2] URLs are the address of a resource (as a document or website) on the Internet that consists of a communications protocol followed by the name or address of a computer on the network and that often includes additional locating information (as directory and file names).[3] Simply, a spoofed URL is a web address that illuminates an immense amount of deception through its ability to appear as an original site, despite it not being one. In order to prevent falling victim to the prevalent scams stemmed from the spoofed URLs, major software companies have come forward and advised techniques to detect and prevent spoofed URLs.

Detection
In order to prevent criminals from accessing personal information, such as credit card information, bank account/routing numbers, and one’s telephone number, home address, etc. it is important to learn and understand how these spoof URLs can be detected. It is very important to first verify the name of the site on a digital certification through the use of SSL/TLS. Always try to identify the actual URL for the web page you are on. Make sure you are able to see the full URL for any hyperlink, so that you can examine the address. Some characters that are commonly found in spoofed URLs are: %00, %01, @. Sometimes the URLs can differ by a single letter or number. In general, only input personal information on a Website if the name has been verified on the digital certificate. Also, if you have any concern about the confidentiality of a website leave the page immediately.[4]
Prevention
Spoofed URLs, a universal defining identity for phishing scams, pose a serious threat to end-users and commercial institutions. Email continues to be the favorite vehicle to perpetrate such scams mainly due to its widespread use combined with the ability to easily spoof them.[5] Several approaches, both generic and specialized, have been proposed to address this problem. However, phishing techniques, growing in ingenuity as well as sophistication, render these solutions weak. In order to prevent users from future victimization stemmed from a spoofed URL, Internet vigilantes have published numerous tips to help users identify a spoof.

The most common are: using authentication based on key exchange between the machines on your network, using an access control list to deny private IP addresses on your downstream interface, implementing filters of both inbound and outbound traffic, configuring routers and switches if they support such configuration, to reject packets originating from outside the local network that claim to originate from within, and enable encryption sessions in the router so that trusted hosts that are outside your network can securely communicate with your local hosts.[6] Ultimately, protection comes from the individual user. Keeping up with new spoofing techniques or scams will readily allow one to identify a scam and most importantly keep information secure and personal.
Susceptible targets
PayPal, an e-commerce business allows money transactions to be made through the Internet and is a common target for spoofed URLs. This forgery of a legitimate PayPal website allows hackers to gain personal and financial information and thus, steal money through fraud. Along with spoof or fake emails that appear with generic greetings, misspellings, and a false sense of urgency, spoofed URLs are an easy way for hackers to violate one’s PayPal privacy. For example, www.paypalsecure.com, includes the name, but is a spoofed URL designed to deceive. Remember to always log into PayPal through a new window browser and never log in through email. In the case that you do receive a suspected spoofed URL, forward the entire email to spoof@PayPal.com to help prevent the URL from tricking other PayPal users.[7]
Common crimes
A major crime associated with spoofed URLs is identity theft. The thief will create a website very similar in appearance to that of a popular site, then when a user accesses the spoofed URL, they can inadvertently give the thief their credit card and personal details. Their spoofed URLs might use “too good to be true” prices to lure more and more looking for a good deal. Crimes like these happen quite often, and most frequently during the festive holidays and other heavy online shopping periods of the year.[8]
Another crime associated with spoofed URLs is setting up a fake anti-malware software. An example of this would be Ransomware, fake anti-malware software that locks up important files for the computer to run, and forces the user to pay a ransom to get the files back. If the user refuses to pay after a certain period of time, the Ransomware will delete the files from the computer, essentially making the computer unusable. Ads for these programs usually appear on popular websites, such as dating sites or social media sites like Facebook and Twitter. They can also come in the form of attachments to emails. Phishing scams are also another major way that users can get tricked into scams (see below).
Phishing
Phishing is a scam by which an e-mail user is duped into revealing personal or confidential information which the scammer can use illicitly.[9] Phishing is the action of fraudsters sending an email to an individual, hoping to seek private information used for identity theft, by falsely asserting to be a reputable legal business. Phishing is performed through emails containing a spoofed URL, which links them to a website. Since it usually appears in the form on an email, it is crucial to not rely just on the address in the “from” field in order to prevent phishing. Computer users should also look out for spelling mistakes within the website's URLs, as this is another common sign to look out for in a phishing email.[10] The website whose URLs are in the e-mails requests individuals to enter personal information so businesses can update it in their system. This information often includes passwords, credit card numbers, social security, and bank account numbers. In turn, the email recipients are giving these fake businesses their information the real businesses already have.
See also
- Computer insecurity
- Hosts File
- IDN homograph attack
- Internet fraud prevention
- Social engineering (computer security)
- Spoofing attack
References
- ↑ Pandagle, Vishwa (2022-10-15). "Cybersecurity Awareness Month: Simple Tips to Identify and Prevent Phishing Scams". https://thecyberexpress.com/simple-tips-identify-prevent-phishing-scams/.
- ↑ "Spoof". Merriam-Webster. https://www.merriam-webster.com/dictionary/spoof.
- ↑ "URL". Merriam-Webster. https://www.merriam-webster.com/dictionary/url.
- ↑ "Steps that you can take to help identify and to help protect yourself from deceptive (spoofed) websites and malicious hyperlinks". Microsoft support. October 13, 2020. https://support.microsoft.com/kb/833786.
- ↑ Madhusudhanan Chandrasekaran; Ramkumar Chinchani; Shambhu Upadhyaya (2006). "Phoney: Mimicking User Response to Detect Phishing Attacks". 2006 International Symposium on a World of Wireless, Mobile and Multimedia Networks(WoWMoM'06). pp. 1–5. doi:10.1109/WOWMOM.2006.87. ISBN 0-7695-2593-8.
- ↑ Jonathan Hassel (June 8, 2006). "The top five ways to prevent IP spoofing". Computerworld. http://www.computerworld.com/s/article/9001021/The_top_five_ways_to_prevent_IP_spoofing?taxonomyId=142&pageNumber=2.
- ↑ "How to spot fake, fraudulent, spoof, or phishing emails". PayPal. https://www.paypal.com/uk/smarthelp/article/how-to-spot-fake,-fraudulent,-spoof,-or-phishing-emails-faq2340.
- ↑ "New E-Scams & Warnings". Federal Bureau of Investigation. https://www.fbi.gov/scams-and-safety/on-the-internet.
- ↑ "Phishing". Merriam-Webster. https://www.merriam-webster.com/dictionary/phishing.
- ↑ "Phishing and Spoofing – Your Guide to Protect Against Them". Adweb Technologies Pvt Ltd. June 27, 2017. https://www.adwebtech.com/phishing-and-spoofing-your-guide-to-protect-against-them/.
 |
