Stingray phone tracker

The StingRay is an IMSI-catcher, a cellular phone surveillance device, manufactured by Harris Corporation.[2] Initially developed for the military and intelligence community, the StingRay and similar Harris devices are in widespread use by local and state law enforcement agencies across Canada,[3] the United States,[4][5] and in the United Kingdom.[6][7] Stingray has also become a generic name to describe these kinds of devices.[8]
Technology
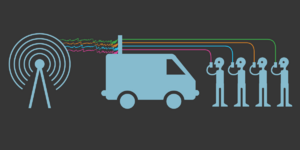
The StingRay is an IMSI-catcher with both passive (digital analyzer) and active (cell-site simulator) capabilities. When operating in active mode, the device mimics a wireless carrier cell tower in order to force all nearby mobile phones and other cellular data devices to connect to it.[9][10][11]
The StingRay family of devices can be mounted in vehicles,[10] on airplanes, helicopters and unmanned aerial vehicles.[12] Hand-carried versions are referred to under the trade name KingFish.[13]
Active mode operations
- Extracting stored data such as International Mobile Subscriber Identity (IMSI) numbers and Electronic Serial Number (ESN),[14]
- Writing cellular protocol metadata to internal storage
- Forcing an increase in signal transmission power[15]
- Forcing an abundance of radio signals to be transmitted
- Forcing a downgrade to an older and less secure communications protocol if the older protocol is allowed by the target device, by making the Stingray pretend to be unable to communicate on an up-to-date protocol
- Interception of communications data or metadata
- Using received signal strength indicators to spatially locate the cellular device[9]
- Conducting a denial of service attack
- Radio jamming for either general denial of service purposes[16][failed verification (See discussion.)] or to aid in active mode protocol rollback attacks
Passive mode operations
- conducting base station surveys, which is the process of using over-the-air signals to identify legitimate cell sites and precisely map their coverage areas
Active (cell site simulator) capabilities
In active mode, the StingRay will force each compatible cellular device in a given area to disconnect from its service provider cell site (e.g., operated by Verizon, AT&T, etc.) and establish a new connection with the StingRay.[17] In most cases, this is accomplished by having the StingRay broadcast a pilot signal that is either stronger than, or made to appear stronger than, the pilot signals being broadcast by legitimate cell sites operating in the area.[18] A common function of all cellular communications protocols is to have the cellular device connect to the cell site offering the strongest signal. StingRays exploit this function as a means to force temporary connections with cellular devices within a limited area.
Extracting data from internal storage
During the process of forcing connections from all compatible cellular devices in a given area, the StingRay operator needs to determine which device is the desired surveillance target. This is accomplished by downloading the IMSI, ESN, or other identifying data from each of the devices connected to the StingRay.[14] In this context, the IMSI or equivalent identifier is not obtained from the cellular service provider or from any other third-party. The StingRay downloads this data directly from the device using radio waves.[19]
In some cases, the IMSI or equivalent identifier of a target device is known to the StingRay operator beforehand. When this is the case, the operator will download the IMSI or equivalent identifier from each device as it connects to the StingRay.[20] When the downloaded IMSI matches the known IMSI of the desired target, the dragnet will end and the operator will proceed to conduct specific surveillance operations on just the target device.[21]
In other cases, the IMSI or equivalent identifier of a target is not known to the StingRay operator and the goal of the surveillance operation is to identify one or more cellular devices being used in a known area.[22] For example, if visual surveillance is being conducted on a group of protestors,[23] a StingRay can be used to download the IMSI or equivalent identifier from each phone within the protest area. After identifying the phones, locating and tracking operations can be conducted, and service providers can be forced to turn over account information identifying the phone users.
Forcing an increase in signal transmission power
Cellular telephones are radio transmitters and receivers, much like a walkie-talkie. However, the cell phone communicates only with a repeater inside a nearby cell tower installation. At that installation, the devices take in all cell calls in its geographic area and repeat them out to other cell installations which repeat the signals onward to their destination telephone (either by radio or landline wires). Radio is used also to transmit a caller's voice/data back to the receiver's cell telephone. The two-way duplex phone conversation then exists via these interconnections.
To make all that work correctly, the system allows automatic increases and decreases in transmitter power (for the individual cell phone and for the tower repeater, too) so that only the minimum transmit power is used to complete and hold the call active, "on", and allows the users to hear and be heard continuously during the conversation. The goal is to hold the call active but use the least amount of transmitting power, mainly to conserve batteries and be efficient. The tower system will sense when a cell phone is not coming in clearly and will order the cell phone to boost transmit power. The user has no control over this boosting; it may occur for a split second or for the whole conversation. If the user is in a remote location, the power boost may be continuous. In addition to carrying voice or data, the cell phone also transmits data about itself automatically, and that is boosted or not as the system detects need.
Encoding of all transmissions ensures that no crosstalk or interference occurs between two nearby cell users. The boosting of power, however, is limited by the design of the devices to a maximum setting. The standard systems are not "high power" and thus can be overpowered by secret systems using much more boosted power that can then take over a user's cell phone. If overpowered that way, a cell phone will not indicate the change due to the secret radio being programmed to hide from normal detection. The ordinary user can not know if their cell phone is captured via overpowering boosts or not. (There are other ways of secret capture that need not overpower, too.)
Just as a person shouting drowns out someone whispering, the boost in RF watts of power into the cell telephone system can overtake and control that system—in total or only a few, or even only one, conversation. This strategy requires only more RF power, and thus it is more simple than other types of secret control. Power boosting equipment can be installed anywhere there can be an antenna, including in a vehicle, perhaps even in a vehicle on the move. Once a secretly boosted system takes control, any manipulation is possible from simple recording of the voice or data to total blocking of all cell phones in the geographic area.[24]
Tracking and locating
A StingRay can be used to identify and track a phone or other compatible cellular data device even while the device is not engaged in a call or accessing data services.[25]
A Stingray closely resembles a portable cellphone tower. Typically, law enforcement officials place the Stingray in their vehicle with a compatible computer software. The Stingray acts as a cellular tower to send out signals to get the specific device to connect to it. Cell phones are programmed to connect with the cellular tower offering the best signal. When the phone and Stingray connect, the computer system determines the strength of the signal and thus the distance to the device. Then, the vehicle moves to another location and sends out signals until it connects with the phone. When the signal strength is determined from enough locations, the computer system centralizes the phone and is able to find it.
Cell phones are programmed to constantly search for the strongest signal emitted from cell phone towers in the area. Over the course of the day, most cell phones connect and reconnect to multiple towers in an attempt to connect to the strongest, fastest, or closest signal. Because of the way they are designed, the signals that the Stingray emits are far stronger than those coming from surrounding towers. For this reason, all cell phones in the vicinity connect to the Stingray regardless of the cell phone owner's knowledge. From there, the stingray is capable of locating the device, interfering with the device, and collecting personal data from the device.[26][27]
Denial of service
The FBI has claimed that when used to identify, locate, or track a cellular device, the StingRay does not collect communications content or forward it to the service provider.[28] Instead, the device causes a disruption in service.[29] Under this scenario, any attempt by the cellular device user to place a call or access data services will fail while the StingRay is conducting its surveillance. On August 21, 2018, Senator Ron Wyden noted that Harris Corporation confirmed that Stingrays disrupt the targeted phone's communications. Additionally, he noted that "while the company claims its cell-site simulators include a feature that detects and permits the delivery of emergency calls to 9-1-1, its officials admitted to my office that this feature has not been independently tested as part of the Federal Communications Commission’s certification process, nor were they able to confirm this feature is capable of detecting and passing-through 9-1-1 emergency communications made by people who are deaf, hard of hearing, or speech disabled using Real-Time Text technology."[30]
Interception of communications content
By way of software upgrades,[31] the StingRay and similar Harris products can be used to intercept GSM communications content transmitted over-the-air between a target cellular device and a legitimate service provider cell site. The StingRay does this by way of the following man-in-the-middle attack: (1) simulate a cell site and force a connection from the target device, (2) download the target device's IMSI and other identifying information, (3) conduct "GSM Active Key Extraction"[31] to obtain the target device's stored encryption key, (4) use the downloaded identifying information to simulate the target device over-the-air, (5) while simulating the target device, establish a connection with a legitimate cell site authorized to provide service to the target device, (6) use the encryption key to authenticate the StingRay to the service provider as being the target device, and (7) forward signals between the target device and the legitimate cell site while decrypting and recording communications content.
The "GSM Active Key Extraction"[31] performed by the StingRay in step three merits additional explanation. A GSM phone encrypts all communications content using an encryption key stored on its SIM card with a copy stored at the service provider.[32] While simulating the target device during the above explained man-in-the-middle attack, the service provider cell site will ask the StingRay (which it believes to be the target device) to initiate encryption using the key stored on the target device.[33] Therefore, the StingRay needs a method to obtain the target device's stored encryption key else the man-in-the-middle attack will fail.
GSM primarily encrypts communications content using the A5/1 call encryption cypher. In 2008 it was reported that a GSM phone's encryption key can be obtained using $1,000 worth of computer hardware and 30 minutes of cryptanalysis performed on signals encrypted using A5/1.[34] However, GSM also supports an export weakened variant of A5/1 called A5/2. This weaker encryption cypher can be cracked in real-time.[32] While A5/1 and A5/2 use different cypher strengths, they each use the same underlying encryption key stored on the SIM card.[33] Therefore, the StingRay performs "GSM Active Key Extraction"[31] during step three of the man-in-the-middle attack as follows: (1) instruct target device to use the weaker A5/2 encryption cypher, (2) collect A5/2 encrypted signals from target device, and (3) perform cryptanalysis of the A5/2 signals to quickly recover the underlying stored encryption key.[35] Once the encryption key is obtained, the StingRay uses it to comply with the encryption request made to it by the service provider during the man-in-the-middle attack.[35]
A rogue base station can force unencrypted links, if supported by the handset software. The rogue base station can send a 'Cipher Mode Settings' element (see GSM 04.08 Chapter 10.5.2.9) to the phone, with this element clearing the one bit that marks if encryption should be used. In such cases the phone display could indicate the use of an unsafe link—but the user interface software in most phones does not interrogate the handset's radio subsystem for use of this insecure mode nor display any warning indication.
Passive capabilities
In passive mode, the StingRay operates either as a digital analyzer, which receives and analyzes signals being transmitted by cellular devices and/or wireless carrier cell sites or as a radio jamming device, which transmits signals that block communications between cellular devices and wireless carrier cell sites. By "passive mode", it is meant that the StingRay does not mimic a wireless carrier cell site or communicate directly with cellular devices.
Base station (cell site) surveys
A StingRay and a test phone can be used to conduct base station surveys, which is the process of collecting information on cell sites, including identification numbers, signal strength, and signal coverage areas. When conducting base station surveys, the StingRay mimics a cell phone while passively collecting signals being transmitted by cell-sites in the area of the StingRay.
Base station survey data can be used to further narrow the past locations of a cellular device if used in conjunction with historical cell site location information ("HCSLI") obtained from a wireless carrier. HCSLI includes a list of all cell sites and sectors accessed by a cellular device, and the date and time each access was made. Law enforcement will often obtain HCSLI from wireless carriers in order to determine where a particular cell phone was located in the past. Once this information is obtained, law enforcement will use a map of cell site locations to determine the past geographical locations of the cellular device.
However, the signal coverage area of a given cell site may change according to the time of day, weather, and physical obstructions in relation to where a cellular device attempts to access service. The maps of cell site coverage areas used by law enforcement may also lack precision as a general matter. For these reasons, it is beneficial to use a StingRay and a test phone to map out the precise coverage areas of all cell sites appearing in the HCSLI records. This is typically done at the same time of day and under the same weather conditions that were in effect when the HCSLI was logged. Using a StingRay to conduct base station surveys in this manner allows for mapping out cell site coverage areas that more accurately match the coverage areas that were in effect when the cellular device was used.
Usage by law enforcement
In the United States
The use of the devices has been frequently funded by grants from the Department of Homeland Security.[36] The Los Angeles Police Department used a Department of Homeland Security grant in 2006 to buy a StingRay for "regional terrorism investigations".[37] However, according to the Electronic Frontier Foundation, the "LAPD has been using it for just about any investigation imaginable."[38]
In addition to federal law enforcement, military and intelligence agencies, StingRays have in recent years been purchased by local and state law enforcement agencies.
In 2006, Harris Corporation employees directly conducted wireless surveillance using StingRay units on behalf of the Palm Bay Police Department—where Harris has a campus[39] —in response to a bomb threat against a middle school. The search was conducted without a warrant or Judicial oversight.[40][41][42][43]
The American Civil Liberties Union (ACLU) confirmed that local police have cell site simulators in Washington, Nevada, Arizona, Alaska, Missouri, New Mexico, Georgia, and Massachusetts. State police have cell site simulators in Oklahoma, Louisiana, Pennsylvania, and Delaware. Local and state police have cell site simulators in California, Texas, Minnesota, Wisconsin, Michigan, Illinois, Indiana, Tennessee, North Carolina, Virginia, Florida, Maryland, and New York.[4] The police use of cell site simulators is unknown in the remaining states. However, many agencies do not disclose their use of StingRay technology, so these statistics are still potentially an under-representation of the actual number of agencies. According to the most recent information published by the American Civil Liberties Union, 72 law enforcement agencies in 24 states own StingRay technology in 2017. Since 2014, these numbers have increased from 42 agencies in 17 states. The following are federal agencies in the United States that have validated their use of cell-site simulators: Federal Bureau of Investigation, Drug Enforcement Administration, US Secret Service, Immigration and Customs Enforcement, US Marshals Service, Bureau of Alcohol, Tobacco, Firearms, and Explosives, US Army, US Navy, US Marine Corps, US National Guard, US Special Command, and National Security Agency.[4] In the 2010-14 fiscal years, the Department of Justice has confirmed spending "more than $71 million on cell-site simulation technology," while the Department of Homeland Security confirmed spending "more than $24 million on cell-site simulation technology."[44]
Several court decisions have been issued on the legality of using a Stingray without a warrant, with some courts ruling a warrant is required[45][46][47] and others not requiring a warrant.[48]
Outside the United States
Police in Vancouver , British Columbia, Canada, admitted after much speculation across the country that they had made use of a Stingray device[49] provided by the RCMP. They also stated that they intended to make use of such devices in the future. Two days later, a statement by Edmonton's police force had been taken as confirming their use of the devices, but they said later that they did not mean to create what they called a miscommunication.[50]
Privacy International and The Sunday Times reported on the usage of StingRays and IMSI-catchers in Ireland, against the Irish Garda Síochána Ombudsman Commission (GSOC), which is an oversight agency of the Irish police force Garda Síochána.[51][52] On June 10, 2015, the BBC reported on an investigation by Sky News[53][54] about possible false mobile phone towers being used by the London Metropolitan Police. Commissioner Bernard Hogan-Howe refused comment.
Between February 2015 and April 2016, over 12 companies in the United Kingdom were authorized to export IMSI-catcher devices to states including Saudi Arabia, UAE, and Turkey. Critics have expressed concern about the export of surveillance technology to countries with poor human rights records and histories of abusing surveillance technology.[55]
Secrecy
The increasing use of the devices has largely been kept secret from the court system and the public.[56] In 2014, police in Florida revealed they had used such devices at least 200 additional times since 2010 without disclosing it to the courts or obtaining a warrant.[2] One of the reasons the Tallahassee police provided for not pursuing court approval is that such efforts would allegedly violate the non-disclosure agreements (NDAs) that police sign with the manufacturer.[57] The American Civil Liberties Union has filed multiple requests for the public records of Florida law enforcement agencies about their use of the cell phone tracking devices.[58]
Local law enforcement and the federal government have resisted judicial requests for information about the use of stingrays, refusing to turn over information or heavily censoring it.[59][60] In June 2014, the American Civil Liberties Union published information from court regarding the extensive use of these devices by local Florida police.[61] After this publication, United States Marshals Service then seized the local police's surveillance records in a bid to keep them from coming out in court.[62]
In some cases, police have refused to disclose information to the courts citing non-disclosure agreements signed with Harris Corporation.[59][63][64] The FBI defended these agreements, saying that information about the technology could allow adversaries to circumvent it.[63] The ACLU has said "potentially unconstitutional government surveillance on this scale should not remain hidden from the public just because a private corporation desires secrecy. And it certainly should not be concealed from judges."[2]
In 2014, former U.S. Magistrate Judge for the Southern District of Texas, Brian Owsley, became the first judge to openly testify about the problematic and unconstitutional aspects of the ways in which law enforcement use of Stingray machines seemed to him to regularly surpass the parameters of the very electronic surveillance warrants that were being issued to sanction the Stingray machine's capabilities. In his testimony, former-Judge Owsley stated: "The first time I ever dealt with a StingRay was in April 2011. I received a pen register application filed by an Assistant U.S. Attorney alleging that some federal inmates were suspected of using cell phones to engage in federal crimes at the Federal Corrections Institution in Three Rivers, Texas. Although the Government knew who these inmates were, they did not know the cell phone numbers. Hence, they filed the pen register application, which essentially seeks authorization of a list of all telephone numbers that are outgoing from a given telephone. Although it was captioned as a pen register, the application sought to use a device that would capture any cell phone used within the vicinity of the prison. In other words, this did not sound like a pen register."[65][66][67]
In 2015 Santa Clara County pulled out of contract negotiations with Harris for StingRay units, citing onerous restrictions imposed by Harris on what could be released under public records requests as the reason for exiting negotiations.[68]
Beginning around 2018 and over the next several years until 2023, the ACLU and the Center for Human Rights and Privacy were able to obtain, through both Freedom of Information Act requests and other legal channels, several copies of various NDAs between some of America's largest police departments and the Harris Corporation, the primary American manufacturer of the Stingray Machine, and its latest upgrade the HailStorm Machine.[69] The NDAs revealed that the FBI has often intervened directly in state criminal trials to protect the confidentiality of any information relating to the Harris Corporation. In fact, NDA between the Harris Corporation and Police Departments in San Diego, Chicago, Miami, Indianapolis, Tucson, and many others include a contractual clause that reads: "In the event that the San Diego Police Department receives a request pursuant to the Freedom of Information Act... or any equivalent state or local law, the civil or criminal discovery process, or other judicial, legislative, or administrative process, to disclose information concerning the Harris Corporation wireless collection equipment/technology... the San Diego Police Department will notify the FBI of any such request telephonically and in writing in order to allow sufficient time for the FBI to seek to prevent disclosure through appropriate channels..."[70][71] This language is repeated identically in virtually all of the NDAs between the Harris Corporation and major police departments that have been disclosed since 2015.
Criticism
In recent years, legal scholars, public interest advocates, legislators and several members of the judiciary have strongly criticized the use of this technology by law enforcement agencies. Critics have called the use of the devices by government agencies warrantless cell phone tracking, as they have frequently been used without informing the court system or obtaining a warrant.[2] The Electronic Frontier Foundation has called the devices "an unconstitutional, all-you-can-eat data buffet."[72]
In June 2015, WNYC Public Radio published a podcast with Daniel Rigmaiden about the StingRay device.[73]
In 2016, Professor Laura Moy of the Georgetown University Law Center filed a formal complaint to the FCC regarding the use of the devices by law enforcement agencies, taking the position that because the devices mimic the properties of cell phone towers, the agencies operating them are in violation of FCC regulation, as they lack the appropriate spectrum licenses.[74]
On December 4, 2019, the American Civil Liberties Union and the New York Civil Liberties Union (NYCLU) filed a federal lawsuit against the Customs and Border Protection and the Immigrations and Customs Enforcement agencies. According to the ACLU, the union had filed a Freedom of Information Act request in 2017, but were not given access to documents.[75] The NYCLU and ACLU proceeded with the lawsuit under the statement that both CBP and ICE had failed, "to produce a range of records about their use, purchase, and oversight of Stingrays."[75] In an official statement expanding their reasoning for the lawsuit, the ACLU expressed their concern over the Stingrays current and future applications, stating that ICE were using them for "unlawfully tracking journalists and advocates and subjecting people to invasive searches of their electronic devices at the border."[75]
Countermeasures
A number of countermeasures to the StingRay and other devices have been developed, for example crypto phones such as GSMK's Cryptophone have firewalls that can identify and thwart the StingRay's actions or alert the user to IMSI capture.[76]
EFF developed a system to catch stingrays.[77][78] Two US university researchers in their arxiv paper demonstrated simple timing based approaches to detect stingrays attacks.[79]
See also
- Authentication and Key Agreement
- Cellphone surveillance
- Evil twin attack
- Kyllo v. United States (lawsuit re thermal image surveillance)
- Man-in-the-middle attack
- Mobile phone tracking
- Triggerfish (surveillance)
- United States v. Davis (2014) found warrantless data collection violated constitutional rights, but okayed data use for criminal conviction, as data collected in good faith
References
- ↑ "Notice, Acceptance, Renewal". Harris/US PTO. http://tsdr.uspto.gov/documentviewer?caseId=sn76303503&docId=SPE20130404144554#docIndex=0&page=1.
- ↑ 2.0 2.1 2.2 2.3 Zetter, Kim (2014-03-03). "Florida Cops' Secret Weapon: Warrantless Cellphone Tracking". Wired.com. https://www.wired.com/2014/03/stingray/. Retrieved 2014-06-23.
- ↑ "RCMP reveals it uses cellphone trackers in wake of CBC report" (in en). CBC News. http://www.cbc.ca/news/technology/rcmp-surveillance-imsi-catcher-mdi-stingray-cellphone-1.4056750.
- ↑ 4.0 4.1 4.2 "Stingray Tracking Devices: Who's Got Them?". American Civil Liberties Union. https://www.aclu.org/map/stingray-tracking-devices-whos-got-them.
- ↑ Goldstein, Joseph (11 February 2016). "New York Police Are Using Covert Cellphone Trackers, Civil Liberties Group Says". New York Times. https://www.nytimes.com/2016/02/12/nyregion/new-york-police-dept-cellphone-tracking-stingrays.html.
- ↑ "Revealed: Bristol's police and mass mobile phone surveillance". The Bristol Cable. https://thebristolcable.org/2016/10/imsi/.
- ↑ "Stingrays bought, quietly used by police forces across England" (in en-us). Ars Technica UK. https://arstechnica.co.uk/tech-policy/2016/10/stingrays-in-use-across-england-by-police/.
- ↑ Gallagher, Ryan (September 25, 2013). "Meet the machines that steal your phone's data". Ars Technica (Condé Nast). https://arstechnica.com/tech-policy/2013/09/meet-the-machines-that-steal-your-phones-data/.
- ↑ 9.0 9.1 Valentino-Devries, Jen (Sep 22, 2011). "'Stingray' Phone Tracker Fuels Constitutional Clash". The Wall Street Journal. https://www.wsj.com/articles/SB10001424053111904194604576583112723197574.
- ↑ 10.0 10.1 Harris WPG (November 29, 2006). "StingRay Cell Site Emulator Datasheet". http://egov.ci.miami.fl.us/Legistarweb/Attachments/34769.pdf. Alt URL
- ↑ Harris WPG (November 29, 2006). "StingRay Cell Site Emulator Datasheet". http://tsdr.uspto.gov/documentviewer?caseId=sn76303503#docIndex=19&page=26. Alt URL
- ↑ Harris WPG. (Aug. 25, 2008). Harris Wireless Products Group catalog, available at https://www.documentcloud.org/documents/1282631-08-08-25-2008-harris-wireless-products-group.html [PDF p. 4] (last accessed: Aug. 29, 2014), archived from original at http://egov.ci.miami.fl.us/Legistarweb/Attachments/48000.pdf[no|permanent dead link|dead link}}] [PDF p. 4] (last accessed: Mar. 8, 2011) (Airborne DF Kit CONUS for StingRay)
- ↑ Harris WPG. (Nov. 29, 2006). KingFish, KingFish GSM S/W, Pocket PC GSM S/W & Training Sole Source Justification for Florida, available at https://www.documentcloud.org/documents/1282625-06-11-29-2006-harris-kingfish-sole-source.html [PDF p. 1] (last accessed: Aug. 29, 2014), archived from original at http://egov.ci.miami.fl.us/Legistarweb/Attachments/34768.pdf [PDF p. 1] (last accessed: Aug. 29, 2014) ("The KingFish system is the only man-portable battery powered CDMA & GSM Interrogating, Active Location, and Signal Information Collection system currently available.").
- ↑ 14.0 14.1 United States v. Rigmaiden, CR08-814-PHX-DGC, Dkt. #0674-1 [Declaration by FBI Supervisory Agent Bradley S. Morrison], ¶ 5, p. 3 (D.Ariz., Oct. 27, 2011), available at https://www.documentcloud.org/documents/1282619-11-10-17-2011-u-s-v-rigmaiden-cr08-814-phx-dgc.html [PDF p. 3] (last accessed: Aug. 30, 2014) ("During a location operation, the electronic serial numbers (ESNs) (or their equivalent) from all wireless devices in the immediate area of the FBI device [(i.e., the StingRay)] that subscribe to a particular provider may be incidentally recorded, including those of innocent, non-target devices.").
- ↑ Florida v. James L. Thomas, No. 2008-CF-3350A, Suppression Hearing Transcript RE: Harris StingRay & KingFish [testimony of Investigator Christopher Corbitt], p. 17 (2nd Cir. Ct., Leon County, FL, Aug. 23, 2010), available at https://www.documentcloud.org/documents/1282618-10-08-23-2010-fl-v-thomas-2008-cf-3350a.html [PDF. p. 17] (last accessed: Aug. 30, 2014) ("[O]nce the equipment comes into play and we capture that handset, to make locating it easier, the equipment forces that handset to transmit at full power.")
- ↑ Hennepin County, MN. (Feb. 2, 2010). FY2011 FEDERAL APPROPRIATIONS REQUESTS [Cellular Exploitation System (Kingfish) - $426,150], available at https://www.documentcloud.org/documents/1282634-10-02-02-2010-kingfish-appropriations-request.html [PDF p. 6] (last accessed: Aug. 30, 2014), archived from original at http://board.co.hennepin.mn.us/sirepub/cache/246/5hnnteqb5wro1fl4oyplzrqo/10628008302014015243634.PDF[no|permanent dead link|dead link}}] [PDF p. 6] (last accessed: Aug. 30, 2014) ("The system acts as a mobile wireless phone tower and has the capability to... deny mobile phones service.").
- ↑ Florida v. James L. Thomas, No. 2008-CF-3350A, Suppression Hearing Transcript RE: Harris StingRay & KingFish [testimony of Investigator Christopher Corbitt], p. 12 (2nd Cir. Ct., Leon County, FL, Aug. 23, 2010), available at https://www.documentcloud.org/documents/1282618-10-08-23-2010-fl-v-thomas-2008-cf-3350a.html [PDF. p. 12] (last accessed: Aug. 30, 2014) ("In essence, we emulate a cellphone tower. so just as the phone was registered with the real Verizon tower, we emulate a tower; we force that handset to register with us.").
- ↑ Hardman, Heath (May 22, 2014). The Brave New World of Cell-Site Simulators. Albany Law School. pp. 11–12. doi:10.2139/ssrn.2440982. "For a cell-site simulator operator to induce a cell phone to camp on his or her cell-site simulator (CSS), all he or she needs to do is become the strongest cell in the target cellphones preferred network.".
- ↑ "Stingray Tracking Devices - A Tool For Mass Surveillance?" (in en). http://broadbandlanding.com/research/stingray/.
- ↑ Florida v. James L. Thomas, No. 2008-CF-3350A, Suppression Hearing Transcript RE: Harris StingRay & KingFish [testimony of Investigator Christopher Corbitt], p. 13 (2nd Cir. Ct., Leon County, FL, Aug. 23, 2010), available at https://www.documentcloud.org/documents/1282618-10-08-23-2010-fl-v-thomas-2008-cf-3350a.html [PDF. p. 13] (last accessed: Aug. 30, 2014) ("The equipment will basically decode information from the handset and provide certain unique identifying information about the handset, being a subscriber identity and equipment identity.... We compare that with the information provided from Verizon to ensure that we are looking at the correct handset.").
- ↑ Id., p. 14 ("And as the equipment is evaluating all the handsets in the area, when it comes across that handset -- the one that we're looking for, for the information that we put into the box -- then it will hang onto that one and allow us to direction find at that point.").
- ↑ In the Matter of The Application of the United States of America for An Order Authorizing the Installation and Use of a Pen Register and Trap and Trace Device, 890 F. Supp. 2d 747, 748 (S.D. Tex. 2012) (Law enforcement sought to use StingRay "to detect radio signals emitted from wireless cellular telephones in the vicinity of the [Subject] that identify the telephones (e.g., by transmitting the telephone's serial number and phone number)..." so the "[Subject's] Telephone can be identified." (quoting order application)).
- ↑ Eördögh, Fruzsina (Jun 13, 2014). "Are Chicago Police Spying on Activists? One Man Sues to Find Out". Mother Jones. http://motherboard.vice.com/en_ca/blog/man-sues-chicago-police-ISMI-catcher-warrantless-cell-phone-spying. "Martinez, who works in the software industry, first wondered about police surveilling his phone in 2012 while he was attending the NATO protests. 'I became suspicious because it was really difficult to use our phones[.]'"
- ↑ Gruber, Bernhard; Froeling, Martijn; Leiner, Tim; Klomp, Dennis W.J. (September 2018). "RF coils: A practical guide for nonphysicists" (in en). Journal of Magnetic Resonance Imaging 48 (3): 590–604. doi:10.1002/jmri.26187. PMID 29897651.
- ↑ Benway, Cody (2017). "You Can Run, but You Can't Hide: Law Enforcement's Use of Stingray Cell Phone Trackers and the Fourth Amendment". Southern Illinois University Law Journal 42 (1): 261–295.
- ↑ "Stingray, IMSI Catcher: FBI Documents Shine Light On Cellphone Tracking Tool" (in en-US). Sagacious News Network. 2013-01-18. http://www.sagaciousnewsnetwork.com/stingray-imsi-catcher-fbi-documents-shine-light-on-cellphone-tracking-tool/.
- ↑ Adam Bates January 25, 2017, and PDF (292.42 KB) EPUB (117.68 KB) MOBI (298.06 KB). "Stingray: A New Frontier in Police Surveillance." Cato Institute. N.p., 25 Jan. 2017. Web. 26 May 2017
- ↑ United States v. Rigmaiden, CR08-814-PHX-DGC, Dkt. #0674-1 [Declaration by FBI Supervisory Agent Bradley S. Morrison], ¶ 4, p. 2-3 (D.Ariz., Oct. 27, 2011), available at https://www.documentcloud.org/documents/1282619-11-10-17-2011-u-s-v-rigmaiden-cr08-814-phx-dgc.html [PDF pp. 2-3] (last accessed: Aug. 30, 2014) ("[T]he [][StingRay] used to locate the defendant's aircard did not capture, collect, decode, view, or otherwise obtain any content transmitted from the aircard, and therefore was unable to pass any information from the aircard to Verizon Wireless.").
- ↑ United States v. Rigmaiden, CR08-814-PHX-DGC, Doc. #723, p. 14 (D.Ariz., Jan. 5, 2012) (Noting government concession that the StingRay "caused a brief disruption in service to the aircard.").
- ↑ Quintin, Cooper (2018-08-27). "Sen. Wyden Confirms Cell-Site Simulators Disrupt Emergency Calls" (in en). https://www.eff.org/deeplinks/2018/08/blog-post-wyden-911-disruption-css.
- ↑ 31.0 31.1 31.2 31.3 Drug Enforcement Administration. (Aug. 29, 2007). FY2011 FEDERAL APPROPRIATIONS REQUESTS [Sole Source Notice of Harris StingRay FishHawk GSM encryption key extraction and intercept upgrade], available at https://www.documentcloud.org/documents/1282642-07-08-29-2007-dea-purchase-of-stingray-fishhawk.html [PDF p. 1] (last accessed: Aug. 30, 2014), archived from the original at https://www.fbo.gov/index?s=opportunity&mode=form&id=9aa2169a324ae7a1a747c2ca8f540cb3&tab=core&_cview=0 (last accessed: Aug. 30, 2014). ("The Tech 2 Me w/FishHawk GSM Intercept S/W upgrade is the only portable standard + 12VDC powered over the air GSM Active Key Extraction and Intercept system currently available.")
- ↑ 32.0 32.1 Green, Matthew (14 May 2013). "On cellular encryption". http://blog.cryptographyengineering.com/2013/05/a-few-thoughts-on-cellular-encryption.html.
- ↑ 33.0 33.1 Barkan, Elad; Biham, Eli; Keller, Nathan. Instant Ciphertext-Only Cryptanalysis of GSM Encrypted Communications. pp. 12–13. https://www.cs.technion.ac.il/users/wwwb/cgi-bin/tr-get.cgi/2006/CS/CS-2006-07.pdf. Retrieved 2019-09-15.
- ↑ Schneier, Brude. "Cryptanalysis of A5/1". https://www.schneier.com/blog/archives/2008/02/cryptanalysis_o_1.html.
- ↑ 35.0 35.1 Id.
- ↑ "Police use cellphone spying device". 2014-05-30. http://www.myfoxny.com/story/25597191/police-use-cellphone-spying-device.
- ↑ Campbell, John (2013-01-24). "LAPD Spied on 21 Using StingRay Anti-Terrorism Tool". LA Weekly. http://www.laweekly.com/news/lapd-spied-on-21-using-stingray-anti-terrorism-tool-2612739.
- ↑ "As Secretive "Stingray" Surveillance Tool Becomes More Pervasive, Questions Over Its Illegality Increase". Electronic Frontier Foundation. 2013-02-12. https://www.eff.org/deeplinks/2013/02/secretive-stingray-surveillance-tool-becomes-more-pervasive-questions-over-its.
- ↑ Nail, Derrol (23 February 2015). "Harris Corporation opens new tech center in Palm Bay". WOFL, Fox Broadcasting Company. http://www.myfoxorlando.com/story/28181324/harris-corporation-opens-new-tech-center-in-palm-bay.
- ↑ Farivar, Cyrus (25 February 2015). "Powerful "stingrays" used to go after 911 hangup, ATM burglary". https://arstechnica.com/tech-policy/2015/02/powerful-stingrays-used-to-go-after-911-hangup-atm-burglary/. "...Palm Bay Police Department simply borrowed a stingray directly from its manufacturer, the Harris Corporation—located down the road in Melbourne, Florida—to respond to a 2006 bomb threat at a school, absent any judicial oversight."
- ↑ "03.05.2014 PBPD Stingray Records (Bates Stamped) redacted". Palm Bay Police Department, American Civil Liberties Union. p. 3. https://www.aclu.org/files/assets/floridastingray/03.05.2014%20-%20PBPD%20Stingray%20Records%20excerpt_Redacted.pdf.
- ↑ Aaronson, Trevor (23 February 2015). "ACLU Releases Florida StingRay Documents". Florida Center for Investigative Reporting. http://fcir.org/2015/02/23/aclu-releases-florida-stingray-documents/.
- ↑ Rivero, Daniel (18 March 2015). "It's now a trend: third court orders the release of phone-tracking Stingray documents". Fusion. http://fusion.net/story/105521/courts-ordering-the-release-of-stingray-documents-is-now-a-trend/.
- ↑ House Committee on Oversight and Government Reform (December 19, 2016). "House Oversight Committee Report on Law Enforcement Use of Cell-Site Simulation Technologies". https://publicintelligence.net/us-cell-site-simulator-privacy/.
- ↑ Fenton, Justin. "Key evidence in city murder case tossed due to stingray use" (in en-US). baltimoresun.com. http://www.baltimoresun.com/news/maryland/crime/bs-md-ci-stingray-murder-evidence-suppressed-20160425-story.html.
- ↑ Emmons, Alex (2016-03-31). "Maryland Appellate Court Rebukes Police for Concealing Use of Stingrays" (in en-US). https://theintercept.com/2016/03/31/maryland-appellate-court-rebukes-police-for-concealing-use-of-stingrays/.
- ↑ Jackman, Tom (2017-09-21). "Police use of 'StingRay' cellphone tracker requires search warrant, appeals court rules" (in en-US). Washington Post. ISSN 0190-8286. https://www.washingtonpost.com/news/true-crime/wp/2017/09/21/police-use-of-stingray-cellphone-tracker-requires-search-warrant-appeals-court-rules/.
- ↑ "Appeals court: It doesn't matter how wanted man was found, even if via stingray" (in en-us). Ars Technica. https://arstechnica.com/tech-policy/2016/11/appeals-court-it-doesnt-matter-how-wanted-man-was-found-even-if-via-stingray/.
- ↑ "Vancouver police admit". Canadian Broadcast Corp (CBC). 9 August 2016. http://www.cbc.ca/news/canada/british-columbia/vancouver-police-stingray-use-cellphone-tracking-civil-liberties-1.3713042.
- ↑ "Edmonton police backtrack after admitting to using controversial cellphone surveillance device". Edmonton Journal. 12 August 2016. https://edmontonjournal.com/news/crime/edmonton-police-backtrack-after-admitting-to-using-controversial-cellphone-surveillance-device.
- ↑ Mooney, John (9 February 2014). "GSOC under high-tech surveillance". The Sunday Times. http://www.thesundaytimes.co.uk/sto/news/ireland/article1373695.ece.
- ↑ Tynan, Dr. Richard (15 February 2014). "Beirtear na IMSIs: Ireland's GSOC surveillance inquiry reveals use of mobile phone interception systems". Privacy International. https://www.privacyinternational.org/blog/beirtear-na-imsis-irelands-gsoc-surveillance-inquiry-reveals-use-of-mobile-phone-interception.
- ↑ "Mass snooping fake mobile towers uncovered in UK". British Broadcasting Corporation. 10 June 2015. https://www.bbc.com/news/business-33076527.
- ↑ Cheshire, Tom (10 June 2015). "Fake Mobile Phone Towers Operating In The UK". Sky News. http://news.sky.com/story/1499258/fake-mobile-phone-towers-operating-in-the-uk.
- ↑ Cox, Joseph (26 August 2016). "British Companies Are Selling Advanced Spy Tech to Authoritarian Regimes" (in en-us). Vice. https://motherboard.vice.com/en_us/article/the-uk-companies-exporting-interception-tech-around-the-world.
- ↑ Fenton, Justin (April 20, 2015). "Baltimore judge allows police use of Stingray phone tracking in murder case". The Baltimore Sun. http://www.baltimoresun.com/news/maryland/crime/blog/bs-md-ci-stingray-new-disclosures-20150420-story.html. "Police outlined for the first time this month their usage of the stingray, pegging it at more than 4,300 times — a figure experts called a "huge number" compared to a trickle of disclosures in other cities."
- ↑ Monahan, Torin (2016) Built to Lie: Investigating Technologies of Deception, Surveillance, and Control. The Information Society 32(4): 229-240.
- ↑ Wessler, Nathan Freed (3 June 2014). "U.S. Marshals Seize Local Cops' Cell Phone Tracking Files in Extraordinary Attempt to Keep Information From Public". American Civil Liberties Union. https://www.aclu.org/blog/national-security-technology-and-liberty/us-marshals-seize-local-cops-cell-phone-tracking-files.
- ↑ 59.0 59.1 Gillum, Jack (2014-03-22). "Police keep quiet about cell-tracking technology". News.yahoo.com. https://news.yahoo.com/police-keep-quiet-cell-tracking-technology-070618821--finance.html.
- ↑ Payne, Lucas (2017-09-22). "United States Government Access to Mobile Phone Data for Contact Tracing" (in fr). https://geolocalisation-telephone.fr/espionner-un-telephone-portable.php.
- ↑ Wessler, Nathan Freed (2014-06-03). "Transcription of Suppression Hearing (Complete)". American Civil Liberties Union. https://www.aclu.org/files/assets/100823_transcription_of_suppression_hearing_complete_0.pdf.
- ↑ Zetter, Kim (2014-06-03). "U.S. Marshals Seize Cops' Spying Records to Keep Them From the ACLU". Wired.com. https://www.wired.com/2014/06/feds-seize-stingray-documents/. Retrieved 2014-06-23.
- ↑ 63.0 63.1 "A Police Gadget Tracks Phones? Shhh! It's Secret". The New York Times. March 15, 2015. https://www.nytimes.com/2015/03/16/business/a-police-gadget-tracks-phones-shhh-its-secret.html?_r=0.
- ↑ "FDLE non-disclosure agreement with the Harris Corporation". American Civil Liberties Union. 8 June 2010. https://www.aclu.org/files/assets/floridastingray/03.27.2014%20-%20FDLE%20Stingray%20Records%20Non-Disclosure%20Agreement%20with%20Harris%20Corp.pdf.
- ↑ https://www.house.mi.gov/sessiondocs/2013-2014/testimony/Committee237-5-13-2014.pdf [bare URL PDF]
- ↑ "Hailstorms in Baltimore: The Fourth Circuit's Opportunity to Create Oversight and Accountability for a Secretive Police Technology | LawSci Forum". https://libpubsdss.lib.umn.edu/mjlst/2020/10/17/hailstorms-in-baltimore-the-fourth-circuits-opportunity-to-create-oversight-and-accountability-for-a-secretive-police-technology/.
- ↑ "HailStorm – the Center for Human Rights and Privacy". https://www.cehrp.org/tags/hailstorm/.
- ↑ Farivar, Cyrus (7 May 2015). "In rare move, Silicon Valley county gov't kills stingray acquisition". https://arstechnica.com/tech-policy/2015/05/in-rare-move-silicon-valley-county-govt-kills-stingray-acquisition/. "What happened was, we were in negotiations with Harris, and we couldn't get them to agree to even the most basic criteria we have in terms of being responsive to public records requests"
- ↑ "HailStorm – the Center for Human Rights and Privacy". https://www.cehrp.org/tags/hailstorm/.
- ↑ "DocumentCloud". https://www.documentcloud.org/documents/2699432-San-Diego-PD-NDA-20Jan2012.html.
- ↑ "HailStorm – the Center for Human Rights and Privacy". https://www.cehrp.org/tags/hailstorm/.
- ↑ Timm, Trevor (2013-02-12). "As Secretive "Stingray" Surveillance Tool Becomes More Pervasive, Questions Over Its Illegality Increase". Electronic Frontier Foundation. https://www.eff.org/deeplinks/2013/02/secretive-stingray-surveillance-tool-becomes-more-pervasive-questions-over-its.
- ↑ Zomorodi, Manoush (2015-06-19). "When Your Conspiracy Theory Is True". WNYC. http://www.wnyc.org/story/stingray-conspiracy-theory-daniel-rigmaiden-radiolab/.
- ↑ Farivar, Cyrus (August 16, 2016). "Baltimore police accused of illegal mobile spectrum use with stingrays". https://arstechnica.com/tech-policy/2016/08/baltimore-police-accused-of-illegal-mobile-spectrum-use-with-stingrays/.
- ↑ 75.0 75.1 75.2 Ramirez, Alexia (December 11, 2019). "ICE and CBP Are Secretly Tracking Us Using Stingrays. We're Suing.". https://www.aclu.org/news/privacy-technology/ice-and-cbp-are-secretly-tracking-us-using-stingrays-were-suing/.
- ↑ Zetter, Kim (2014-09-03). "Phone Firewall Identifies Rogue Cell Towers Trying to Intercept Your Calls". Wired (Condé Nast). https://www.wired.com/2014/09/cryptophone-firewall-identifies-rogue-cell-towers/. Retrieved 13 July 2016.
- ↑ N, Yomna (2019-06-28). "Gotta Catch 'Em All: Understanding How IMSI-Catchers Exploit Cell Networks" (in en). https://www.eff.org/wp/gotta-catch-em-all-understanding-how-imsi-catchers-exploit-cell-networks.
- ↑ Crocodile Hunter, Electronic Frontier Foundation, 2021-10-24, https://github.com/EFForg/crocodilehunter, retrieved 2021-10-24
- ↑ Ganji, Santosh; P R, Kumar (2023). "Seeing the Unseen: The REVEAL protocol to expose the wireless Man-in-the-Middle". arXiv:2308.09213 [cs.NI].
Further reading
- Lye, Linda (2014). "StingRays: The Most Common Surveillance Tool the Government Won't Tell You About". ACLU Northern California. https://www.aclunc.org/sites/default/files/StingRays_The_Most_Common_Surveillance_Tool_the_Govt_Won%27t_Tell_You_About_0.pdf.
- IMSI catchers, and specifically the Harris Stingray, are extensively used in the Intelligence Support Activity/Task Force Orange thriller written by J.T. Patten (Scott Swanson (military), a former counterterrorism intelligence specialist. Patten, J.T., Buried in Black. A Task Force Orange novel. Lyrical Press/Penguin, 2018.
 |
