Finance:IOTA (technology)
{{infobox cryptocurrency
| currency_name = IOTA
| image_1 = Iota logo.png
| image_2 =
| image_title_1 =
| superunit_ratio_1 =
| superunit_ratio_2 = 1,000,000
| superunit_ratio_3 =
| superunit_ratio_4 =
| alt1 = Official IOTA logo
| superunit_ratio_5 =
| superunit_name_1 =
| superunit_name_2 = Miota | Mi | MegaIota
| superunit_name_3 =
| superunit_name_4 =
| superunit_name_5 =
| plural = IOTAs
| symbol =
| ticker_symbol = IOTA, MIOTA
| coin_definition =
| implementations =
| initial_release_version =
| initial_release_date = 11 July 2016
| code_repository = https://github.com/iotaledger
| status =
| latest_release_version =
| latest_release_date =
| forked_from =
| project_fork_of =
| programming_languages =
| operating_system =
| author =
| developer =
| precision =
| white_paper = Popov, Serguei (3 April 2016). "April 3, 2016. Version 0.6". http://www.tangleblog.com/wp-content/uploads/2016/11/IOTA_Whitepaper.pdf.
| source_model = Open source
| license =
| website = iota
IOTA has been criticized due to its unusual design, of which it is unclear whether it will work in practice.[1][2] As a result, IOTA was rewritten from the ground up for a network update called Chrysalis, or IOTA 1.5, which launched on 28 April 2021.[2] In this update, controversial decisions such as ternary encoding and quantum proof cryptography were left behind and replaced with established standards.[2] A testnet for a follow-up update called Coordicide, or IOTA 2.0, was deployed in late 2020, with the aim of releasing a distributed network that no longer relies on the coordinator for consensus in 2021.[3][2][4][needs update]
History
The value transfer protocol IOTA, named after the smallest letter of the Greek alphabet, was created in 2015 by David Sønstebø, Dominik Schiener, Sergey Ivancheglo, and Serguei Popov.[5][6] Initial development was funded by an online public crowdsale, with the participants buying the IOTA value token with other digital currencies.[7] Approximately 1300 BTC were raised, corresponding to approximately US$500,000 at that time, and the total token supply was distributed pro-rata over the initial investors. The IOTA network went live in 2016.[8]
IOTA foundation
In 2017, early IOTA token investors donated 5% of the total token supply for continued development and to endow what became later became the IOTA Foundation.[7] In 2018, the IOTA Foundation was chartered as a Stiftung in Berlin, with the goal to assist in the research and development, education and standardisation of IOTA technology.[9] The IOTA Foundation is a board member of International Association for Trusted Blockchain Applications (INATBA),[10] and founding member of the Trusted IoT Alliance[11] and Mobility Open Blockchain Initiative (MOBI),[12] to promote blockchain and distributed ledgers in regulatory approaches, the IoT ecosystem and mobility.
Following a dispute between IOTA founders David Sønstebø and Sergey Ivancheglo, Ivancheglo resigned from the board of directors on 23 June 2019.[13][14][15] On 10 December 2020 the IOTA Foundation Board of Directors and supervisory board announced that the Foundation officially parted ways with David Sønstebø.[16][17]
DCI vulnerability disclosure
On 8 September 2017, researchers Ethan Heilman from Boston University and Neha Nerula et al. from MIT's Digital Currency Initiative (DCI) reported on potential security flaws with IOTA's former Curl-P-27 hash function.[1] The IOTA Foundation received considerable backlash in their handling of the incident.[18] FT Alphaville reported legal posturing by an IOTA Founder against a security researcher for his involvement in the DCI report, as well as instances of aggressive language levelled against a Forbes contributor and other unnamed journalists covering the DCI report.[19] The Center for Blockchain Technologies at the University College London severed ties with the IOTA Foundation due to legal threats against security researchers involved in the report.[20]
Attacks
As a speculative blockchain and cryptocurrency-related technology, IOTA has been the target of phishing, scamming, and hacking attempts, which have resulted in the thefts of user tokens and extended periods of downtime.[21][22][23] In January 2018, more than US$10 million worth of IOTA tokens were stolen from users that used a malicious online seed-creator, a password that protects their ownership of IOTA tokens.[21] The seed-generator scam was the largest fraud in IOTA history to date, with over 85 victims.[24] In January 2019, the UK and German law enforcement agencies arrested a 36-year-old man from Oxford, England believed to be behind the theft.[25][26]
On 26 November 2019 a hacker discovered a vulnerability in a third-party payment service,[22] provided by MoonPay,[27] integrated in the mobile and desktop wallet managed by the IOTA Foundation.[22] The attacker compromised over 50 IOTA seeds, resulting in the theft of approximately US$2 Million worth in IOTA tokens.[22] After receiving reports that hackers were stealing funds from user wallets, the IOTA Foundation shut down the coordinator on 12 February 2020.[28][29] This had the side-effect of effectively shutting down the entire IOTA cryptocurrency.[28] Users at-risk were given seven days to migrate their potentially compromised seed to a new seed, until 7 March 2020. The coordinator was restarted on 10 March 2020.[30]
IOTA 1.5 (Chrysalis) and IOTA 2.0 (Coordicide)
The IOTA network is currently[when?] centralized, a transaction on the network is considered valid if and only if it is referenced by a milestone issued by a node operated by the IOTA foundation called the coordinator.[7] In 2019 the IOTA Foundation announced that it would like to operate the network without a coordinator in the future, using a two-stage network update, termed Chrysalis for IOTA 1.5 and Coordicide for IOTA 2.0.[3][22] The Chrysalis update went live on 28 April 2021, and removed its controversial design choices such as ternary encoding and Winternitz one-time signatures, to create an enterprise-ready blockchain solution. In parallel Coordicide is currently[when?] developed, to create a distributed network that no longer relies on the coordinator for consensus.[3] A testnet of Coordicide was deployed late 2020, with the aim of releasing a final version in 2021.[3][2][4][needs update]
Characteristics
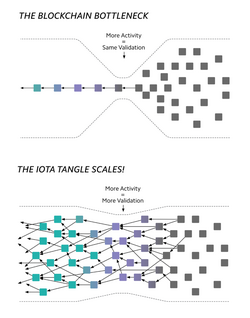
The Tangle
The Tangle is the moniker used to describe IOTAs directed acyclic graph (DAG) transaction settlement and data integrity layer.[7] It is structured as a string of individual transactions that are interlinked to each other and stored through a network of node participants.[31] The Tangle does not have miners validating transactions, rather, network participants are jointly responsible for transaction validation, and must confirm two transactions already submitted to the network for every one transaction they issue.[32] Transactions can therefore be issued to the network at no cost, facilitating micropayments.[32] To avoid spam, every transaction requires computational resources based on Proof of Work (PoW) algorithms, to find the answer to a simple cryptographic puzzle.[33]
IOTA supports both value and data transfers.[34] A second layer protocol provides encryption and authentication of messages, or data streams, transmitted and stored on the Tangle as zero-value transactions.[33] Each message holds a reference to the address of a follow-up message, connecting the messages in a data stream, and providing forward secrecy.[33] Authorised parties with the correct decryption key can therefore only follow a datastream from their point of entry.[33] When the owner of the data stream wants to revoke access, it can change the decryption key when publishing a new message.[33] This provides the owner granular controls over the way in which data is exchanged to authorised parties.[33]
IOTA token
The IOTA token is a unit of value in the IOTA network.[35] There is a fixed supply of 2,779,530,283,277,761 IOTA tokens in circulation on the IOTA network. IOTA tokens are stored in IOTA wallets protected by an 81-character seed, similar to a password.[26] To access and spend the tokens, IOTA provides a cryptocurrency wallet.[2][21] A hardware wallet can be used to keep credentials offline while facilitating transactions.[26]
Coordinator node
IOTA currently[when?] requires a majority of honest actors to prevent network attacks.[7] However, as the concept of mining does not exist on the IOTA network, it is unlikely that this requirement will always be met. Therefore, consensus is currently[when?] obtained through referencing of transactions issued by a special node operated by the IOTA foundation, called the coordinator.[36] The coordinator issues zero value transactions at given time intervals, called milestones.[36] Any transaction, directly or indirectly, referenced by such a milestone is considered valid by the nodes in the network. The coordinator is an authority operated by the IOTA foundation and as such single point of failure for the IOTA network, which makes the network centralized.[3]
Markets
IOTA is traded in megaIOTA units (1,000,000 IOTA) on digital currency exchanges such as Bitfinex, and listed under the MIOTA ticker symbol.[37] Like other digital currencies, IOTA's token value has soared and fallen.[38][39][40]
Fast Probabilistic Consensus (FPC)
The crux of cryptocurrencies is to stop double spends, the ability to spend the same money twice in two simultaneous transactions. Bitcoin's solution has been to use Proof of Work (PoW) making it a significant financial burden to have a minted block be rejected for a double spend. IOTA has designed a voting algorithm called Fast Probabilistic Consensus to form a consensus on double spends.[41] Instead of starting from scratch, the IOTA Foundation started with Simple Majority Consensus where the first opinion update is defined by,
Where is the opinion of node at time . The function is the percent of all the nodes that have the opinion and is the threshold for majority, set by the implementation. After the first round, the successive opinions change at time to the function,
Although, this model is fragile against malicious attackers which is why the IOTA Foundation decided not to use it.[42] Instead the IOTA Foundation decided to augment the leaderless consensus mechanism called, Random neighbors majority consensus (RMC) which is similar to SMC although, the nodes in which their opinions are queries is randomized. They took RMC then augmented it to create FPC by having the threshold of majority be a random number generated from a Decentralized Random Number Generator (dRNG). For FPC, the first sound is the same,
For success rounds though,
Where where , is a randomized threshold for majority. Randomizing the threshold for majority makes it extremely difficult for adversaries to manipulate the consensus by either making it converge to a specific value or prolonging consensus. Note that FPC is only utilized to form consensus on a transaction during a double spend.[43]
Ultimately, IOTA uses Fast Probabilistic Consensus for consensus and uses Proof of Work as a rate controller.[44] Because IOTA does not use PoW for consensus, its overall network and energy per transaction is extremely small.[45]
Applications and testbeds
Proof-of-concepts building on IOTA technology are being developed in the automotive and IoT industry by corporates as Jaguar Land Rover, STMicroelectronics and Bosch.[38][46][47] IOTA is a participant in smart city testbeds, to establish digital identity, waste management and local trade of energy.[5][48][49] In project Alvarium, formed under the Linux Foundation, IOTA is used as an immutable storage and validation mechanism.[50][51] The privacy centered search engine Xain uses IOTA as a trust anchor for its aggregated AI model.[52][53]
On 11 February 2020, the Eclipse Foundation and IOTA Foundation jointly launched the Tangle EE (Enterprise Edition) Working Group.[34] Tangle EE is aimed at enterprise users that can take IOTA technology and enable larger organizations to build applications on top of the project, where the Eclipse Foundation will provide a vendor-neutral governance framework .[54]
Announcements of partners were critically received.[55][56] In 2017, IOTA released the data marketplace, a pilot for a market where connected sensors or devices can store, sell or purchase data.[57][58] The data marketplace was received critically by the cryptocurrency community over the extent of the involvement of the participants of the data marketplace, suggesting that "the IOTA Foundation was actively asking publications to use Microsoft’s name following the data marketplace announcement.".[55] Izabelle Kaminska criticized a Jaguar press release: "our interpretation is that it's very unlikely Jaguar will be bringing a smart-wallet-enabled marketplace any time soon."[56]
Criticism
IOTA promises to achieve the same benefits that blockchain-based DLTs bring - decentralization, distribution, immutability and trust - but remove the downsides of wasted resources associated with mining as well as transaction costs.[7] However, several of the design features of IOTA are unusual, and it is unclear whether they work in practice.[59][3][1]
The security of IOTA's consensus mechanism against double-spending attacks is unclear, as long as the network is immature.[31] Essentially, in the IoT, with heterogeneous devices having varying levels of low computational power, sufficiently strong computational resources will render the tangle insecure.[31] This is a problem in traditional proof-of-work blockchains as well, however, they provide a much greater degree of security through higher fault tolerance and transaction fees.[31] At the beginning, when there is a lower number of participants and incoming transactions, a central coordinator is needed to prevent an attack on the IOTA tangle.[31]
Critics have opposed role of the coordinator for being the single source of consensus in the IOTA network. Polychain Capital founder Olaf Carlson-Wee, says "IOTA is not decentralized, even though IOTA makes that claim, because it has a central "coordinator node" that the network needs to operate. If a regulator or a hacker shut down the coordinator node, the network would go down."[60] This was demonstrated during the Trinity attack incident, when the IOTA foundation shutdown the coordinator to prevent further thefts.[60][22][3] Following a discovered vulnerability in October 2017, the IOTA foundation transferred potentially compromised funds to addresses under its control, providing a process for users to later apply to the IOTA Foundation in order to reclaim their funds.[1]
Additionally, IOTA has seen several network outages as a result of bugs in the coordinator as well as DDoS attacks.[7] During the seed generator scam, a DDoS network attack was abused leaving initial thefts undetected.[24]
In 2020, the IOTA Foundation announced that it would like to operate the network without a coordinator in the future, but implementation of this is still in an early development phase.[22][3][2]
References
- ↑ 1.0 1.1 1.2 1.3 Heilman, Ethan; Narula, Neha; Tanzer, Garrett; Lovejoy, James; Colavita, Michael; Virza, Madars; Dryja, Tadge (2019). Cryptanalysis of Curl-P and Other Attacks on the IOTA Cryptocurrency. https://eprint.iacr.org/2019/344.
- ↑ 2.0 2.1 2.2 2.3 2.4 2.5 2.6 Anadiotis, George. "IOTA still wants to build a better blockchain and get it right this time" (in en). https://www.zdnet.com/article/iota-still-wants-to-build-a-better-blockchain-and-get-it-right-this-time/.
- ↑ 3.0 3.1 3.2 3.3 3.4 3.5 3.6 3.7 Cite error: Invalid
<ref>tag; no text was provided for refs named:197 - ↑ 4.0 4.1 Riesbeck, Peter (2020-08-15). "Moneten für Maschinen - Warum Dominik Schiener die Kryptowährung Iota entwickelt" (in de). https://www.fr.de/zukunft/storys/technologie/moneten-fuer-maschinen-warum-dominik-schiener-die-kryptowaehrung-iota-entwickelt-90023851.html.
- ↑ 5.0 5.1 Cite error: Invalid
<ref>tag; no text was provided for refs named:132 - ↑ Kahl, Stephan (2018-03-07). "22-Year-Old Behind $5 Billion Crypto Is Just Getting Started". https://www.bloomberg.com/news/articles/2018-03-07/22-year-old-behind-5b-cryptocurrency-is-just-getting-started.
- ↑ 7.0 7.1 7.2 7.3 7.4 7.5 7.6 Cite error: Invalid
<ref>tag; no text was provided for refs named:1 - ↑ Chavez-Dreyfuss, Gertrude (2017-11-28). "Blockchain network IOTA teams up with Microsoft, others on data marketplace" (in en). Reuters. https://www.reuters.com/article/us-blockchain-iota-cisco-idUSKBN1DS2EE.
- ↑ "IOTA: Erste Krypto-Stiftung Deutschlands gegründet" (in de-DE). 2017-11-15. https://www.die-stiftung.de/nachrichten-service/kurzmeldungen/iota-erste-krypto-stiftung-deutschlands-gegruendet-74566/.
- ↑ O'Brien, Chris (2019-04-03). "EU launches blockchain association to accelerate distributed ledger technology adoption" (in en-US). https://venturebeat.com/2019/04/03/eu-launches-blockchain-association-to-accelerate-distributed-ledger-technology-adoption/.
- ↑ Osborne, Charlie (2017-09-19). "New alliance advocates the blockchain to improve IoT security, trust" (in en). https://www.zdnet.com/article/new-alliance-promotes-the-blockchain-to-improve-iot-security-trust/.
- ↑ Russel, Jon (2018-05-02). "BMW, GM, Ford and Renault launch blockchain research group for automotive industry" (in en-US). http://social.techcrunch.com/2018/05/02/the-mobility-open-blockchain-initiative-bmw-gm-ford-renault/.
- ↑ Stanley Hunter, John (2020-02-20). "Hacks und Streit unter Gründern: Was ist bei IOTA los?" (in de-DE). https://www.capital.de/wirtschaft-politik/hacks-und-streit-unter-gruendern-was-ist-bei-iota-los.
- ↑ Come-from-Beyond (2020-02-03). "My side of the story about parting ways with David Sønstebø" (in en). https://medium.com/@comefrombeyond/my-side-of-the-story-about-parting-ways-with-david-s%C3%B8nsteb%C3%B8-ab8d2c103c37.
- ↑ "Sergey Ivancheglo departs from the IOTA Foundation" (in en). 2019-07-26. http://blog.iota.org/sergey-ivancheglo-departs-from-the-iota-foundation-d2d9c1c61db6.
- ↑ "IOTA Foundation parts ways with David Sønstebø" (in en). 2020-12-10. http://blog.iota.org/iota-foundation-parts-ways-with-david-sonstebo/.
- ↑ Sønstebø, David (2020-12-23). "My departure has been greatly exaggerated" (in en). https://medium.com/@DavidSonstebo/my-departure-has-been-greatly-exaggerated-765850042e89.
- ↑ Daniel Oberhaus & Jordan Pearson (2018-03-02). "A $5 Billion Cryptocurrency Has Enraged Cryptographers" (in en). https://www.vice.com/en_us/article/ywq44k/a-5-billion-cryptocurrency-iota-has-enraged-cryptographers-leaked-emails.
- ↑ Kelly, Jemima (2018-08-25). "FUD, inglorious FUD". https://ftalphaville.ft.com/2018/04/25/1524628801000/FUD--inglorious-FUD/.
- ↑ Mix (2018-04-28). "University College London (UCL) severs ties with IOTA Foundation" (in en-us). https://thenextweb.com/hardfork/2018/04/28/iota-university-college-london-ucl/.
- ↑ 21.0 21.1 21.2 Marcel Rosenbach, Markus Böhm (2018-01-30). "Betrugsmaschen bei Kryptowährungen: Auf einmal ist alles weg" (in de). https://www.spiegel.de/netzwelt/web/bitcoin-iota-und-co-diese-betrugsmaschen-gibt-es-a-1190296.html.
- ↑ 22.0 22.1 22.2 22.3 22.4 22.5 22.6 Kannenberg, Axel (2020-02-27). "IOTA cryptocurrency: Million dollar credit stolen, no payments possible (translated)". https://www.heise.de/newsticker/meldung/Kryptowaehrung-IOTA-Guthaben-im-Millionenwert-gestohlen-Netzwerk-steht-still-4669122.html.
- ↑ Osborne, Charlie (7 December 2020). "2020's worst cryptocurrency breaches, thefts, and exit scams" (in en). https://www.zdnet.com/article/2020s-worst-cryptocurrency-breaches-thefts-and-exit-scams/.
- ↑ 24.0 24.1 Cimpanu, Catalin. "Europol arrests UK man for stealing €10 million worth of IOTA cryptocurrency" (in en). https://www.zdnet.com/article/europol-arrests-uk-man-for-stealing-eur10-million-worth-of-iota-cryptocurrency/.
- ↑ "Oxford man arrested over £8.7m cryptocurrency theft" (in en-GB). BBC News. 2019-01-23. https://www.bbc.com/news/uk-england-oxfordshire-46980658.
- ↑ 26.0 26.1 26.2 Chavez-Dreyfuss, Gertrude (2019-01-30). "IOTA says bulk of $11 million stolen tokens found, hacker worked alone" (in en). Reuters. https://www.reuters.com/article/us-crypto-currencies-crime-idUSKCN1PO2J5.
- ↑ "Trinity Attack Incident Part 1: Summary and next steps". 21 Feb 2020. https://blog.iota.org/trinity-attack-incident-part-1-summary-and-next-steps-8c7ccc4d81e8/.
- ↑ 28.0 28.1 Cimpanu, Catalin. "IOTA cryptocurrency shuts down entire network after wallet hack" (in en). https://www.zdnet.com/article/iota-cryptocurrency-shuts-down-entire-network-after-wallet-hack/.
- ↑ Osborne, Charlie. "Bisq Bitcoin exchange slams on the brakes after exploit of critical security flaw, crypto theft" (in en). https://www.zdnet.com/article/bisq-bitcoin-exchange-slams-on-the-breaks-following-exploit-of-critical-security-flaw/.
- ↑ Kannenberg, Axel (2020-03-02). "Nach Trinity-Hack: IOTA stellt Migrationstool für kompromittierte Seeds bereit" (in de). https://www.heise.de/newsticker/meldung/Nach-Trinity-Hack-IOTA-stellt-Migrationstool-fuer-kompromittierte-Seeds-bereit-4672296.html.
- ↑ 31.0 31.1 31.2 31.3 31.4 Ali, Muhammad Salek; Vecchio, Massimo; Pincheira, Miguel; Dolui, Koustabh; Antonelli, Fabio; Rehmani, Mubashir Husain (2018-12-18). "Applications of Blockchains in the Internet of Things: A Comprehensive Survey". IEEE Communications Surveys & Tutorials 21 (2): 1676–1717. doi:10.1109/COMST.2018.2886932. ISSN 1553-877X.
- ↑ 32.0 32.1 Makhdoom, Imran; Abolhasan, Mehran; Abbas, Haider; Ni, Wei (2019-01-01). "Blockchain's adoption in IoT: The challenges, and a way forward" (in en). Journal of Network and Computer Applications 125: 251–279. doi:10.1016/j.jnca.2018.10.019.
- ↑ 33.0 33.1 33.2 33.3 33.4 33.5 Hawig, David; Zhou, Chao; Fuhrhop, Sebastian; Fialho, Andre S; Ramachandran, Navin (2019-06-14). "Designing a Distributed Ledger Technology System for Interoperable and General Data Protection Regulation–Compliant Health Data Exchange: A Use Case in Blood Glucose Data" (in en). Journal of Medical Internet Research 21 (6): e13665. doi:10.2196/13665. ISSN 1438-8871. PMID 31199293.
- ↑ 34.0 34.1 McKendrick, Joe. "Enter the Tangle, a blockchain designed specially for the Internet of Things" (in en). https://www.zdnet.com/article/the-tangle-or-blockchain-for-the-internet-of-things/.
- ↑ Marcel Rosenbach, Alexander Jung, Frank Dohmen (2018-01-22). "Kryptowährung: Bitcoin geht, Blockchain bleibt" (in de). https://www.spiegel.de/spiegel/kryptowaehrung-bitcoin-geht-blockchain-bleibt-a-1189154.html.
- ↑ 36.0 36.1 Cite error: Invalid
<ref>tag; no text was provided for refs named:222 - ↑ Cheng, Evelyn (2017-06-14). "Major bitcoin exchanges hit by cyberattacks as record rally makes them a target" (in en). https://www.cnbc.com/2017/06/14/major-bitcoin-exchanges-hit-by-cyberattacks-as-record-rally-makes-them-a-target.html.
- ↑ 38.0 38.1 "New ways to trade data, New ways to trade data". The Economist. 2018-03-28. ISSN 0013-0613. https://www.economist.com/science-and-technology/2018/03/28/new-ways-to-trade-data.
- ↑ Kharif, Olga (2019-05-14). "Bitcoin Adds Market Share in Recovery in Crypto Prices". https://www.bloomberg.com/news/articles/2019-05-14/bitcoin-adds-market-share-as-crypto-winter-turns-glorious-summer.
- ↑ Smith, Oliver (2018-08-16). "How Next Generation Crypto Investors Are Poised To Win, Even If Their Startups Lose" (in en). https://www.forbes.com/sites/oliversmith/2018/08/16/how-next-generation-crypto-investors-are-poised-to-win-even-if-their-startups-lose/.
- ↑ Popov, Serguei (2021). "FPC-BI: Fast Probabilistic Consensus within Byzantine Infrastructures". Preprint 147: 77–86. doi:10.1016/j.jpdc.2020.09.002. https://arxiv.org/pdf/1905.10895.pdf.
- ↑ I. Benjamin, S.-O. Chan, R. O'Donnel, O. Tamuz, L.-Y. Tan, Convergence, unanimity and disagreement in majority dynamics on unimodular graphs and random graphs, Stochastic Processes and their Applications 126 (9) (2016) 2719-2733.
- ↑ Capossele, Angelo, Sebastian Müller, and Andreas Penzkofer. "Robustness and efficiency of leaderless probabilistic consensus protocols within Byzantine infrastructures." arXiv preprint arXiv:1911.08787 (2019).
- ↑ Sanders, William (Mar 19, 2021). "Explaining the IOTA Congestion Control Algorithm". https://blog.iota.org/explaining-the-iota-congestion-control-algorithm/.
- ↑ Ramachandran, Navin (May 14, 2021). "Energy Benchmarks for the IOTA Network (Chrysalis Edition)". https://blog.iota.org/internal-energy-benchmarks-for-iota/.
- ↑ O'Grady, Sean (2019-05-03). "Mobile piggy bank: Jaguar Land Rover's 'earn as you drive' concept" (in en). https://www.independent.co.uk/life-style/motoring/jaguar-land-rover-smart-wallet-cryptocurrency-destination-zero-a8892541.html.
- ↑ Chavez-Dreyfuss, Gertrude (2020-09-30). "Jaguar, NTT team up with tech group on remote access software" (in en). Reuters. https://www.reuters.com/article/us-blockchain-autos-jaguar-idUSKBN26L3JO.
- ↑ O'Brien, Chris (2019-08-30). "Norway unveils energy-positive building showcasing smart city potential" (in en-US). https://venturebeat.com/2019/08/30/norway-unveils-energy-positive-building-showcasing-smart-city-potential/.
- ↑ Mix (2018-02-21). "IOTA is vulnerable to replay attacks but has no intention of fixing the flaw" (in en-us). https://thenextweb.com/hardfork/2018/02/21/iota-replay-attacks-vulnerability/.
- ↑ Bantle, Ulrich (2019-10-31). "Linux Foundation gründet Data-Privacy-Projekt Alvarium" (in de-DE). https://www.linux-magazin.de/news/linux-foundation-gruendet-data-privacy-projekt-alvarium/.
- ↑ Agelini, Chris (2020-01-23). "How open, trusted edge can help improve data sharing and monetization" (in en-US). https://venturebeat.com/2020/01/23/how-open-trusted-edge-can-help-improve-data-sharing-and-monetization/.
- ↑ Lomas, Natasha. "Xayn is privacy-safe, personalized mobile web search powered by on-device AIs" (in en-US). https://social.techcrunch.com/2020/12/08/xayn-is-privacy-safe-personalized-mobile-web-search-powered-by-on-device-ais/.
- ↑ Voß, Oliver (9 December 2020). "Suchmaschine mit Tinder-Prinzip". https://background.tagesspiegel.de/digitalisierung/suchmaschine-mit-tinder-prinzip.
- ↑ Miller, Ron (2020-02-11). "Tangle EE project joins Eclipse Foundation to bring distributed ledger apps to enterprise" (in en-US). http://social.techcrunch.com/2020/02/11/tangle-ee-project-joins-eclipse-foundation-to-bring-distributed-ledger-apps-to-enterprise/.
- ↑ 55.0 55.1 Mix (2017-12-12). "IOTA clarifies it has no formal partnership with Microsoft [UPDATED"] (in en-us). https://thenextweb.com/hardfork/2017/12/12/iota-partnership-microsoft-marketplace/.
- ↑ 56.0 56.1 Kaminska, Izabella (2019-05-28). "Emperor has no clothes, Jaguar crypto press release edition". http://ftalphaville.ft.com/2019/05/28/1559050976000/Emperor-has-no-clothes--Jaguar-crypto-press-release-edition/.
- ↑ Ponciano, Jonathan. "IOTA Foundation Launches Data Marketplace For 'Internet-Of-Things' Industry" (in en). https://www.forbes.com/sites/jonathanponciano/2017/11/28/iota-foundation-launches-data-marketplace-for-internet-of-things-research/.
- ↑ "IOTA launches IoT data marketplace, envisions devices autonomously buying and trading information" (in en-US). 2017-11-28. https://venturebeat.com/2017/11/28/iota-launches-iot-data-marketplace-envisions-devices-autonomously-buying-and-trading-information/.
- ↑ Evans, Jon (2018-08-10). "Cryptocurrency insecurity: IOTA, BCash and too many more" (in en-US). http://social.techcrunch.com/2018/08/09/cryptocurrency-insecurity-iota-bcash-and-too-many-more/.
- ↑ 60.0 60.1 Kauflin, Jeff (2018-01-03). "IOTA Rose 464% In 2017, But Buyer Beware: Experts Have Major Security Concerns". https://www.forbes.com/sites/jeffkauflin/2018/01/03/iota-rose-464-in-2017-but-buyer-beware-experts-have-major-security-concerns/#7656696b5faa.
External links
