HTTP Strict Transport Security
HTTP Strict Transport Security (HSTS) is a policy mechanism that helps to protect websites against man-in-the-middle attacks such as protocol downgrade attacks[1] and cookie hijacking. It allows web servers to declare that web browsers (or other complying user agents) should automatically interact with it using only HTTPS connections, which provide Transport Layer Security (TLS/SSL), unlike the insecure HTTP used alone. HSTS is an IETF standards track protocol and is specified in RFC 6797.
The HSTS Policy is communicated by the server to the user agent via an HTTP response header field named Strict-Transport-Security. HSTS Policy specifies a period of time during which the user agent should only access the server in a secure fashion.[2] Websites using HSTS often do not accept clear text HTTP, either by rejecting connections over HTTP or systematically redirecting users to HTTPS (though this is not required by the specification). The consequence of this is that a user-agent not capable of doing TLS will not be able to connect to the site.
The protection only applies after a user has visited the site at least once, relying on the principle of "trust on first use". The way this protection works is that when a user entering or selecting an HTTP (not HTTPS) URL to the site, the client, such as a Web browser, will automatically upgrade to HTTPS without making an HTTP request, thereby preventing any HTTP man-in-the-middle attack from occurring.
Specification history
The HSTS specification was published as RFC 6797 on 19 November 2012 after being approved on 2 October 2012 by the IESG for publication as a Proposed Standard RFC.[3] The authors originally submitted it as an Internet Draft on 17 June 2010. With the conversion to an Internet Draft, the specification name was altered from "Strict Transport Security" (STS) to "HTTP Strict Transport Security", because the specification applies only to HTTP.[4] The HTTP response header field defined in the HSTS specification however remains named "Strict-Transport-Security".
The last so-called "community version" of the then-named "STS" specification was published on 18 December 2009, with revisions based on community feedback.[5]
The original draft specification by Jeff Hodges from PayPal, Collin Jackson, and Adam Barth was published on 18 September 2009.[6]
The HSTS specification is based on original work by Jackson and Barth as described in their paper "ForceHTTPS: Protecting High-Security Web Sites from Network Attacks".[7]
Additionally, HSTS is the realization of one facet of an overall vision for improving web security, put forward by Jeff Hodges and Andy Steingruebl in their 2010 paper The Need for Coherent Web Security Policy Framework(s).[8]
HSTS mechanism overview
A server implements an HSTS policy by supplying a header over an HTTPS connection (HSTS headers over HTTP are ignored).[1] For example, a server could send a header such that future requests to the domain for the next year (max-age is specified in seconds; 31,536,000 is equal to one non-leap year) use only HTTPS: Strict-Transport-Security: max-age=31536000.
When a web application issues HSTS Policy to user agents, conformant user agents behave as follows (RFC 6797):[9]
- Automatically turn any insecure links referencing the web application into secure links (e.g.
http://example.com/some/page/will be modified tohttps://example.com/some/page/before accessing the server). - If the security of the connection cannot be ensured (e.g. the server's TLS certificate is not trusted), the user agent must terminate the connection (RFC 6797 section 8.4, Errors in Secure Transport Establishment) and should not allow the user to access the web application (section 12.1, No User Recourse).
The HSTS Policy helps protect web application users against some passive (eavesdropping) and active network attacks.[10] A man-in-the-middle attacker has a greatly reduced ability to intercept requests and responses between a user and a web application server while the user's browser has HSTS Policy in effect for that web application.
Applicability
The most important security vulnerability that HSTS can fix is SSL-stripping man-in-the-middle attacks, first publicly introduced by Moxie Marlinspike in his 2009 BlackHat Federal talk "New Tricks For Defeating SSL In Practice".[11][12] The SSL (and TLS) stripping attack works by transparently converting a secure HTTPS connection into a plain HTTP connection. The user can see that the connection is insecure, but crucially there is no way of knowing whether the connection should be secure. At the time of Marlinspike's talk, many websites did not use TLS/SSL, therefore there was no way of knowing (without prior knowledge) whether the use of plain HTTP was due to an attack, or simply because the website had not implemented TLS/SSL. Additionally, no warnings are presented to the user during the downgrade process, making the attack fairly subtle to all but the most vigilant. Marlinspike's sslstrip tool fully automates the attack.[citation needed]
HSTS addresses this problem[10] by informing the browser that connections to the site should always use TLS/SSL. The HSTS header can be stripped by the attacker if this is the user's first visit. Google Chrome, Mozilla Firefox, Internet Explorer, and Microsoft Edge attempt to limit this problem by including a "pre-loaded" list of HSTS sites.[13][14][15] Unfortunately this solution cannot scale to include all websites on the internet. See limitations, below.
HSTS can also help to prevent having one's cookie-based website login credentials stolen by widely available tools such as Firesheep.[16]
Because HSTS is time limited, it is sensitive to attacks involving shifting the victim's computer time e.g. using false NTP packets.[17]
Limitations
The initial request remains unprotected from active attacks if it uses an insecure protocol such as plain HTTP or if the URI for the initial request was obtained over an insecure channel.[18] The same applies to the first request after the activity period specified in the advertised HSTS Policy max-age (sites should set a period of several days or months depending on user activity and behavior). Google Chrome, Mozilla Firefox, and Internet Explorer/Microsoft Edge address this limitation by implementing a "HSTS preloaded list", which is a list that contains known sites supporting HSTS.[19][13][14][15] This list is distributed with the browser so that it uses HTTPS for the initial request to the listed sites as well. As previously mentioned, these pre-loaded lists cannot scale to cover the entire Web. A potential solution might be achieved by using DNS records to declare HSTS Policy, and accessing them securely via DNSSEC, optionally with certificate fingerprints to ensure validity (which requires running a validating resolver to avoid last mile issues).[20]
Junade Ali has noted that HSTS is ineffective against the use of phony domains; by using DNS-based attacks, it is possible for a man-in-the-middle interceptor to serve traffic from an artificial domain which is not on the HSTS Preload list,[21] this can be made possible by DNS Spoofing Attacks,[22] or simply a domain name that misleadingly resembles the real domain name such as www.example.org instead of www.example.com.
Even with an HSTS preloaded list, HSTS cannot prevent advanced attacks against TLS itself, such as the BEAST or CRIME attacks introduced by Juliano Rizzo and Thai Duong. Attacks against TLS itself are orthogonal to HSTS policy enforcement. Neither can it protect against attacks on the server - if someone compromises it, it will happily serve any content over TLS.
See RFC 6797 for a discussion of overall HSTS security considerations.
Privacy issues
HSTS can be used to near-indelibly tag visiting browsers with recoverable identifying data (supercookies) which can persist in and out of browser "incognito" privacy modes. By creating a web page that makes multiple HTTP requests to selected domains, for example, if twenty browser requests to twenty different domains are used, theoretically over one million visitors can be distinguished (220) due to the resulting requests arriving via HTTP vs. HTTPS; the latter being the previously recorded binary "bits" established earlier via HSTS headers.[23]
Browser support
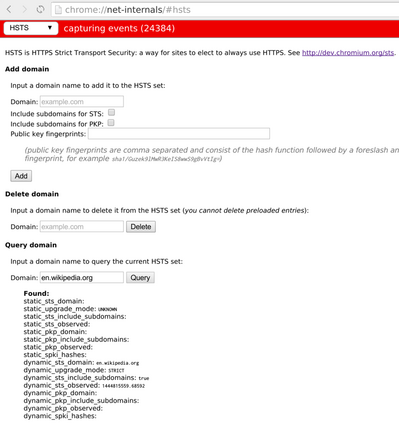
- Chromium and Google Chrome since version 4.0.211.0[24][25]
- Firefox since version 4;[1] with Firefox 17, Mozilla integrates a list of websites supporting HSTS.[14]
- Opera since version 12[26]
- Safari since OS X Mavericks (version 10.9, late 2013)[27]
- Internet Explorer 11 on Windows 8.1 and Windows 7 with KB3058515 installed (Released as a Windows Update in June 2015)[28]
- Microsoft Edge and Internet Explorer 11 on Windows 10[29][30]
- BlackBerry 10 Browser and WebView since BlackBerry OS 10.3.3.
Deployment best practices
Depending on the actual deployment there are certain threats (e.g. cookie injection attacks) that can be avoided by following best practices.
- HSTS hosts should declare HSTS policy at their top-level domain name. For example, an HSTS host at https://sub.example.com should also answer with the HSTS header at https://example.com. The header should specify the
includeSubDomainsdirective.[31] - In addition to HSTS deployment, a host for https://www.example.com should include a request to a resource from https://example.com to make sure that HSTS for the parent domain is set and protects the user from potential cookie injection attacks performed by a MITM that would inject a reference to the parent domain (or even http://nonexistentpeer.example.com), which the attacker then would answer.[32]
See also
- Content Security Policy
- .dev TLD – a Google-operated TLD included in the HSTS preload-list by default
- HTTP Public Key Pinning
References
- ↑ 1.0 1.1 1.2 "Strict-Transport-Security" (in en-US). Mozilla. https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Strict-Transport-Security.
- ↑ Hodges, Jeff; Jackson, Collin; Barth, Adam (November 2012), HTTP Strict Transport Security (HSTS), IETF, sec. 5.2, doi:10.17487/RFC6797, RFC 6797, https://tools.ietf.org/html/rfc6797
- ↑ "[websec Protocol Action: 'HTTP Strict Transport Security (HSTS)' to Proposed Standard (draft-ietf-websec-strict-transport-sec-14.txt)"]. 2 Oct 2012. https://www.ietf.org/mail-archive/web/websec/current/msg01401.html.
- ↑ Hodges, Jeff (30 June 2010). "Re: [HASMAT "STS" moniker (was: IETF BoF @IETF-78 Maastricht: HASMAT...)"]. //www.ietf.org/mail-archive/web/hasmat/current/msg00025.html.
- ↑ "Strict Transport Security -06". 18 December 2009. //lists.w3.org/Archives/Public/www-archive/2009Dec/att-0048/draft-hodges-strict-transport-sec-06.plain.html.
- ↑ "Strict Transport Security -05". 18 September 2009. //lists.w3.org/Archives/Public/www-archive/2009Sep/att-0051/draft-hodges-strict-transport-sec-05.plain.html.
- ↑ "ForceHTTPS: Protecting High-Security Web Site from Network Attacks". April 2008. https://crypto.stanford.edu/forcehttps/.
- ↑ Hodges, Jeff; Steinguebl, Andy (29 October 2010). "The Need for Coherent Web Security Policy Framework(s)". http://www.thesecuritypractice.com/the_security_practice/2010/10/the-need-for-coherent-web-security-policy-frameworks.html.
- ↑ Hodges, Jeff; Jackson, Collin; Barth, Adam (November 2012), Section 5. HSTS Mechanism Overview, IETF, sec. 5, doi:10.17487/RFC6797, RFC 6797, https://tools.ietf.org/html/rfc6797#section-5
- ↑ 10.0 10.1 Hodges, Jeff; Jackson, Collin; Barth, Adam (November 2012), 2.4. Threat Model, IETF, sec. 2.3, doi:10.17487/RFC6797, RFC 6797, https://tools.ietf.org/html/rfc6797#section-2.3
- ↑ Marlinspike, Moxie (2009). "New Tricks For Defeating SSL In Practice". Black Hat Briefings. Washington, DC. https://blackhat.com/presentations/bh-dc-09/Marlinspike/BlackHat-DC-09-Marlinspike-Defeating-SSL.pdf. Retrieved 15 March 2012.
- ↑ Defeating SSL Using Sslstrip on YouTube
- ↑ 13.0 13.1 Langley, Adam (8 July 2010). "Strict Transport Security". The Chromium Projects. https://www.chromium.org/sts.
- ↑ 14.0 14.1 14.2 Keeler, David (1 November 2012). "Preloading HSTS". Mozilla Security Blog. https://blog.mozilla.org/security/2012/11/01/preloading-hsts/.
- ↑ 15.0 15.1 "HTTP Strict Transport Security comes to Internet Explorer". 16 February 2015. http://blogs.msdn.com/b/ie/archive/2015/02/16/http-strict-transport-security-comes-to-internet-explorer.aspx.
- ↑ Hodges, Jeff (31 October 2010). "Firesheep and HSTS (HTTP Strict Transport Security)". http://identitymeme.org/archives/2010/10/29/firesheep-and-hsts-http-strict-transport-security/.
- ↑ Selvi, Jose (2014-10-17). "Bypassing HTTP Strict Transport Security". Black Hat Briefings. Amsterdam. https://www.blackhat.com/docs/eu-14/materials/eu-14-Selvi-Bypassing-HTTP-Strict-Transport-Security.pdf. Retrieved 2014-10-22.
- ↑ Hodges, Jeff; Jackson, Collin; Barth, Adam (November 2012), Section 14.6. Bootstrap MITM Vulnerability, IETF, sec. 14.6, doi:10.17487/RFC6797, RFC 6797, https://tools.ietf.org/html/rfc6797#section-14.6
- ↑ "Chromium HSTS Preloaded list". https://cs.chromium.org/chromium/src/net/http/transport_security_state_static.json.
- ↑ Butcher, Simon (11 September 2011). "HTTP Strict Transport Security". https://simon.butcher.name/archives/2011/09/11/HTTP-Strict-Transport-Security.
- ↑ Ali, Junade (20 October 2017). "Performing & Preventing SSL Stripping: A Plain-English Primer". https://blog.cloudflare.com/performing-preventing-ssl-stripping-a-plain-english-primer/.
- ↑ Maksutov, A. A.; Cherepanov, I. A.; Alekseev, M. S. (2017). "Detection and prevention of DNS spoofing attacks". 2017 Siberian Symposium on Data Science and Engineering (SSDSE). pp. 84–87. doi:10.1109/SSDSE.2017.8071970. ISBN 978-1-5386-1593-5.
- ↑ "The HSTS super cookie forcing you to choose: "privacy or security?" -". sophos.com. 2 February 2015. https://nakedsecurity.sophos.com/2015/02/02/anatomy-of-a-browser-dilemma-how-hsts-supercookies-make-you-choose-between-privacy-or-security/.
- ↑ The Chromium Developers (17 November 2010). "Strict Transport Security - The Chromium Projects". https://dev.chromium.org/sts.
- ↑ Hodges, Jeff (18 September 2009). "fyi: Strict Transport Security specification". http://lists.w3.org/Archives/Public/public-webapps/2009JulSep/1148.html.
- ↑ Opera Software ASA (23 April 2012). "Web specifications support in Opera Presto 2.10". http://www.opera.com/docs/specs/presto2.10/#m210-244.
- ↑ Langley, Adam [@agl__]. "Confirmed. See ~/Library/Cookies/HSTS.plist. Includes Chromium preloads as of some date and processes HSTS headers.". https://twitter.com/agl__/status/414112266938617856. Missing or empty |date= (help)
- ↑ "HTTP Strict Transport Security comes to Internet Explorer 11 on Windows 8.1 and Windows 7". windows.com. http://blogs.windows.com/msedgedev/2015/06/09/http-strict-transport-security-comes-to-internet-explorer-11-on-windows-8-1-and-windows-7/.
- ↑ "Internet Explorer Web Platform Status and Roadmap". https://status.modern.ie/httpstricttransportsecurityhsts.
- ↑ "Project Spartan and the Windows 10 January Preview Build - IEBlog". 22 January 2015. https://blogs.msdn.microsoft.com/ie/2015/01/22/project-spartan-and-the-windows-10-january-preview-build/.
- ↑ Hodges. "HTTP Strict Transport Security (HSTS) 6.1.2.". ietf.org. https://tools.ietf.org/html/draft-ietf-websec-strict-transport-sec-14#page-16.
- ↑ Hodges, J.; Jackson, C.; Barth, A. (2012), RFC 6797 - HTTP Strict Transport Security (HSTS) 11.4 Implications of includeSubDomains, sec. 11.4, doi:10.17487/RFC6797, RFC 6797, https://tools.ietf.org/html/rfc6797#section-11.4
External links
- RFC 6797 – HTTP Strict Transport Security (HSTS)
- IETF WebSec Working Group
- Security Now 262: Strict Transport Security
- Open Web Application Security Project (OWASP): HSTS description
- Online browser HSTS and Public Key Pinning test
- HSTS Preload Submission for Google Chrome, Mozilla Firefox, Safari, IE 11, and Edge
- Chromium HSTS Preloaded list
- Strict-Transport-Security on MDN Web Docs
 |
