Reed–Solomon error correction
| Reed–Solomon codes | |
|---|---|
| Named after | Irving S. Reed and Gustave Solomon |
| Classification | |
| Hierarchy | Linear block code Polynomial code Reed–Solomon code |
| Block length | n |
| Message length | k |
| Distance | n − k + 1 |
| Alphabet size | q = pm ≥ n (p prime) Often n = q − 1. |
| Notation | [n, k, n − k + 1]q-code |
| Algorithms | |
| Berlekamp–Massey Euclidean et al. | |
| Properties | |
| Maximum-distance separable code | |
This article may be too technical for most readers to understand. Please help improve it to make it understandable to non-experts, without removing the technical details. (January 2026) (Learn how and when to remove this template message) |
In information theory and coding theory, Reed–Solomon codes are a group of error-correcting codes that were introduced by Irving S. Reed and Gustave Solomon in 1960.[1] They have many applications, including consumer technologies such as MiniDiscs, CDs, DVDs, Blu-ray discs, QR codes, Data Matrix, data transmission technologies such as DSL and WiMAX, broadcast systems such as satellite communications, DVB and ATSC, and storage systems such as RAID 6.
Reed–Solomon codes operate on a block of data treated as a set of finite-field elements called symbols. Reed–Solomon codes RS(n, k) are able to detect and correct multiple symbol errors. By adding t = n − k check symbols to the data, a Reed–Solomon code can detect (but not correct) any combination of up to t erroneous symbols, or locate and correct up to ⌊t/2⌋ erroneous symbols at unknown locations. As an erasure code, it can correct up to t erasures at locations that are known and provided to the algorithm, or it can detect and correct combinations of errors and erasures. Reed–Solomon codes are also suitable as multiple-burst bit-error correcting codes, since a sequence of b + 1 consecutive bit errors can affect at most two symbols of size b. The choice of t is up to the designer of the code and may be selected within wide limits.
There are two basic types of Reed–Solomon codes – original view and BCH view – with BCH view being the most common, as BCH view decoders are faster and require less working storage than original view decoders.
History
Reed–Solomon codes were developed in 1960 by Irving S. Reed and Gustave Solomon, who were then staff members of MIT Lincoln Laboratory. Their seminal article was titled "Polynomial Codes over Certain Finite Fields".[1] The original encoding scheme described in the Reed and Solomon article used a variable polynomial based on the message to be encoded where only a fixed set of values (evaluation points) to be encoded are known to encoder and decoder. The original theoretical decoder generated potential polynomials based on subsets of k (unencoded message length) out of n (encoded message length) values of a received message, choosing the most popular polynomial as the correct one, which was impractical for all but the simplest of cases. This was initially resolved by changing the original scheme to a BCH-code-like scheme based on a fixed polynomial known to both encoder and decoder, but later, practical decoders based on the original scheme were developed, although initially slower than the BCH schemes. The result of this is that there are two main types of Reed–Solomon codes: ones that use the original encoding scheme and ones that use the BCH encoding scheme.
Also in 1960, a practical fixed polynomial decoder for BCH codes developed by Daniel Gorenstein and Neal Zierler was described in an MIT Lincoln Laboratory report by Zierler in January 1960 and later in an article in June 1961.[2] The Gorenstein–Zierler decoder and the related work on BCH codes are described in a book "Error-Correcting Codes" by W. Wesley Peterson (1961).[3] By 1963 (or possibly earlier), J.J. Stone (and others)[who?] recognized that Reed–Solomon codes could use the BCH scheme of using a fixed generator polynomial, making such codes a special class of BCH codes,[4] but Reed–Solomon codes based on the original encoding scheme are not a class of BCH codes, and depending on the set of evaluation points, they are not even cyclic codes.
In 1969, an improved BCH scheme decoder was developed by Elwyn Berlekamp and James Massey and has since been known as the Berlekamp–Massey decoding algorithm.
In 1975, another improved BCH scheme decoder was developed by Yasuo Sugiyama, based on the extended Euclidean algorithm.[5]
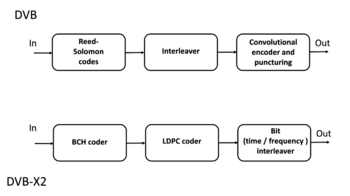
In 1977, Reed–Solomon codes were implemented in the Voyager program in the form of concatenated error correction codes. The first commercial application in mass-produced consumer products appeared in 1982 with the compact disc, where two interleaved Reed–Solomon codes are used. Today, Reed–Solomon codes are widely implemented in digital storage devices and digital communication standards, though they are being slowly replaced by Bose–Chaudhuri–Hocquenghem (BCH) codes. For example, Reed–Solomon codes are used in the Digital Video Broadcasting (DVB) standard DVB-S, in conjunction with a convolutional inner code, but BCH codes are used with LDPC in its successor, DVB-S2.
In 1986, an original scheme decoder known as the Berlekamp–Welch algorithm was developed.
In 1996, variations of original scheme decoders called list decoders or soft decoders were developed by Madhu Sudan and others, and work continues on these types of decoders (see Guruswami–Sudan list decoding algorithm).
In 2002, another original scheme decoder was developed by Shuhong Gao, based on the extended Euclidean algorithm.[6]
Around 2015 an original scheme syndrome like decoder was developed (author unkown). [7]
Applications
Data storage
Reed–Solomon coding is very widely used in mass storage systems to correct the burst errors associated with media defects.
Reed–Solomon coding is a key component of the compact disc. It was the first use of strong error correction coding in a mass-produced consumer product, and DAT and DVD use similar schemes. In the CD, two layers of Reed–Solomon coding separated by a 28-way convolutional interleaver yields a scheme called Cross-Interleaved Reed–Solomon Coding (CIRC). The first element of a CIRC decoder is a relatively weak inner (32,28) Reed–Solomon code, shortened from a (255,251) code with 8-bit symbols. This code can correct up to 2 byte errors per 32-byte block. More importantly, it flags as erasures any uncorrectable blocks, i.e., blocks with more than 2 byte errors. The decoded 28-byte blocks, with erasure indications, are then spread by the deinterleaver to different blocks of the (28,24) outer code. Thanks to the deinterleaving, an erased 28-byte block from the inner code becomes a single erased byte in each of 28 outer code blocks. The outer code easily corrects this, since it can handle up to 4 such erasures per block.
The result is a CIRC that can completely correct error bursts up to 4000 bits, or about 2.5 mm on the disc surface. This code is so strong that most CD playback errors are almost certainly caused by tracking errors that cause the laser to jump track, not by uncorrectable error bursts.[8]
DVDs use a similar scheme, but with much larger blocks, a (208,192) inner code, and a (182,172) outer code.
Reed–Solomon error correction is also used in parchive files which are commonly posted accompanying multimedia files on USENET. The distributed online storage service Wuala (discontinued in 2015) also used Reed–Solomon when breaking up files.
Bar code
Almost all two-dimensional bar codes such as PDF-417, MaxiCode, Datamatrix, QR Code, Aztec Code and Han Xin code use Reed–Solomon error correction to allow correct reading even if a portion of the bar code is damaged. When the bar code scanner cannot recognize a bar code symbol, it will treat it as an erasure.
Reed–Solomon coding is less common in one-dimensional bar codes, but is used by the PostBar symbology.
Data transmission
Specialized forms of Reed–Solomon codes, specifically Cauchy-RS and Vandermonde-RS, can be used to overcome the unreliable nature of data transmission over erasure channels. The encoding process assumes a code of RS(N, K) which results in N codewords of length N symbols each storing K symbols of data, being generated, that are then sent over an erasure channel.
Any combination of K codewords received at the other end is enough to reconstruct all of the N codewords. The code rate is generally set to 1/2 unless the channel's erasure likelihood can be adequately modelled and is seen to be less. In conclusion, N is usually 2K, meaning that at least half of all the codewords sent must be received in order to reconstruct all of the codewords sent.
Reed–Solomon codes are also used in xDSL systems and CCSDS's Space Communications Protocol Specifications as a form of forward error correction.
Space transmission

One significant application of Reed–Solomon coding was to encode the digital pictures sent back by the Voyager program.
Voyager introduced Reed–Solomon coding concatenated with convolutional codes, a practice that has since become very widespread in deep space and satellite (e.g., direct digital broadcasting) communications.
Viterbi decoders tend to produce errors in short bursts. Correcting these burst errors is a job best done by short or simplified Reed–Solomon codes.
Modern versions of concatenated Reed–Solomon/Viterbi-decoded convolutional coding were and are used on the Mars Pathfinder, Galileo, Mars Exploration Rover and Cassini missions, where they perform within about 1–1.5 dB of the ultimate limit, the Shannon capacity.
These concatenated codes are now being replaced by more powerful turbo codes:
| Years | Code | Mission(s) |
|---|---|---|
| 1958–present | Uncoded | Explorer, Mariner, many others |
| 1968–1978 | convolutional codes (CC) (25, 1/2) | Pioneer, Venus |
| 1969–1975 | Reed–Muller code (32, 6) | Mariner, Viking |
| 1977–present | Binary Golay code | Voyager |
| 1977–present | RS(255, 223) + CC(7, 1/2) | Voyager, Galileo, many others |
| 1989–2003 | RS(255, 223) + CC(7, 1/3) | Voyager |
| 1989–2003 | RS(255, 223) + CC(14, 1/4) | Galileo |
| 1996–present | RS + CC (15, 1/6) | Cassini, Mars Pathfinder, others |
| 2004–present | Turbo codes[nb 1] | Messenger, Stereo, MRO, MSL,others |
| est. 2009 | LDPC codes | Constellation, M2020, MAVEN |
Constructions (encoding)
The Reed–Solomon code is actually a family of codes, where every code is characterised by three parameters: an alphabet size q, a block length n, and a message length k, with . The set of alphabet symbols is interpreted as the finite field of order , and thus, must be a prime power. In the most useful parameterizations of the Reed–Solomon code, the block length is usually some constant multiple of the message length, that is, the rate is some constant, and furthermore, the block length is either equal to the alphabet size or one less than it, i.e., or .
Reed & Solomon's original view: The codeword as a sequence of values
There are different encoding procedures for the Reed–Solomon code, and thus, there are different ways to describe the set of all codewords. In the original view of Reed and Solomon, every codeword of the Reed–Solomon code is a sequence of function values of a polynomial of degree less than .[1] In order to obtain a codeword of the Reed–Solomon code, the message symbols (each within the q-sized alphabet) are treated as the coefficients of a polynomial of degree less than , over the finite field with elements. In turn, the polynomial is evaluated at a set of distinct points in any order of the field , and the sequence of values is the corresponding codeword. Common choices for a set of evaluation points include , , or for , , ... , where is a primitive element of .
Formally, the set of codewords of the Reed–Solomon code is defined as follows: Since any two distinct polynomials of degree less than agree in at most points, this means that any two codewords of the Reed–Solomon code disagree in at least positions. Furthermore, there are two polynomials that do agree in points but are not equal, and thus, the distance of the Reed–Solomon code is exactly . Then the relative distance is , where is the rate. This trade-off between the relative distance and the rate is asymptotically optimal since, by the Singleton bound, every code satisfies . Being a code that achieves this optimal trade-off, the Reed–Solomon code belongs to the class of maximum distance separable codes.
While the number of different polynomials of degree less than k and the number of different messages are both equal to , and thus every message can be uniquely mapped to such a polynomial, there are different ways of doing this encoding. The original construction of Reed & Solomon interprets the message x as the coefficients of the polynomial p, whereas subsequent constructions interpret the message as the values of the polynomial at the first k points and obtain the polynomial p by interpolating these values with a polynomial of degree less than k. The latter encoding procedure, while being slightly less efficient, has the advantage that it gives rise to a systematic code, that is, the original message is always contained as a subsequence of the codeword.[1]
Simple encoding procedure: The message as a sequence of coefficients
In the original construction of Reed and Solomon, the message is mapped to the polynomial with The codeword of is obtained by evaluating at different points of the field .[1] Thus the classical encoding function for the Reed–Solomon code is defined as follows:
This function is a linear mapping, that is, it satisfies for the following -matrix with elements from .
This matrix is a Vandermonde matrix over . In other words, the Reed–Solomon code is a linear code, and in the classical encoding procedure, its generator matrix is .
Systematic encoding procedure: The message as an initial sequence of values
There are alternative encoding procedures that produce a systematic Reed–Solomon code. One method uses Lagrange interpolation to compute polynomial such that Then is evaluated at the other points .
This function is a linear mapping. To generate the corresponding systematic encoding matrix G, multiply the matrix A by the inverse of A's left square submatrix.
for the following -matrix with elements from .
Discrete Fourier transform and its inverse
A discrete Fourier transform is essentially the same as the encoding procedure; it uses the generator polynomial to map a set of evaluation points into the message values as shown above:
The inverse Fourier transform could be used to convert an error free set of n < q message values back into the encoding polynomial of k coefficients, with the constraint that in order for this to work, the set of evaluation points used to encode the message must be a set of increasing powers of α:
However, Lagrange interpolation performs the same conversion without the constraint on the set of evaluation points or the requirement of an error free set of message values and is used for systematic encoding, and in one of the steps of the Gao decoder.
The BCH view: The codeword as a sequence of coefficients
Note that BCH Code and most implementations of BCH view are most significant term first. In this view, the message is interpreted as the coefficients of a polynomial :
A generator polynomial is defined as the polynomial whose roots are sequential powers of the Galois field primitive
For a "narrow sense code", .
Encoding computes a codeword polynomial that is an exact multiple of .
Simple encoding procedure
The sender computes a related polynomial of degree where and sends the polynomial . The polynomial is constructed by multiplying the message polynomial , which has degree , with the generator polynomial of degree that is known to both the sender and the receiver. .
This function is a linear mapping, that is, it satisfies for the following -matrix with elements from .
for the following matrix with elements from .
Systematic encoding procedure
The encoding procedure for the BCH view of Reed–Solomon codes can be modified to yield a systematic encoding procedure, in which each codeword contains the message as a prefix, and simply appends error correcting symbols as a suffix. Here, instead of sending , the encoder constructs the transmitted polynomial such that the coefficients of the largest monomials are equal to the corresponding coefficients of , and the lower-order coefficients of are chosen in such a way that becomes exactly divisible by . Then the coefficients of are a subsequence of the coefficients of . To get a code that is overall systematic, we construct the message polynomial by interpreting the message as the sequence of its coefficients.
Formally, the construction is done by multiplying by to make room for the check symbols, dividing that product by to find the remainder, and then compensating for that remainder by subtracting it. The check symbols are created by computing the remainder :
The remainder has degree at most , whereas the coefficients of in the polynomial are zero. Therefore, the following definition of the codeword has the property that the first coefficients are identical to the coefficients of :
As a result, is exactly divisible by :[11]
This function is a linear mapping. To generate the corresponding systematic encoding matrix G, multiply the matrix A by the inverse of A's left square submatrix (or set G's left square submatrix to the identity matrix and encode each row).
for the following matrix with elements from .
Properties
The Reed–Solomon code is a [n, k, n − k + 1] code; in other words, it is a linear block code of length n (over F) with dimension k and minimum Hamming distance The Reed–Solomon code is optimal in the sense that the minimum distance has the maximum value possible for a linear code of size (n, k); this is known as the Singleton bound. Such a code is also called a maximum distance separable (MDS) code.
The error-correcting ability of a Reed–Solomon code is determined by its minimum distance, or equivalently, by , the measure of redundancy in the block. If the locations of the error symbols are not known in advance, then a Reed–Solomon code can correct up to erroneous symbols, i.e., it can correct half as many errors as there are redundant symbols added to the block. Sometimes error locations are known in advance (e.g., "side information" in demodulator signal-to-noise ratios)—these are called erasures. A Reed–Solomon code (like any MDS code) is able to correct twice as many erasures as errors, and any combination of errors and erasures can be corrected as long as the relation 2E + S ≤ n − k is satisfied, where is the number of errors and is the number of erasures in the block.

The theoretical error bound can be described via the following formula for the AWGN channel for FSK:[12] and for other modulation schemes: where , , , is the symbol error rate in uncoded AWGN case and is the modulation order.
For practical uses of Reed–Solomon codes, it is common to use a finite field with elements. In this case, each symbol can be represented as an -bit value. The sender sends the data points as encoded blocks, and the number of symbols in the encoded block is . Thus a Reed–Solomon code operating on 8-bit symbols has symbols per block. (This is a very popular value because of the prevalence of byte-oriented computer systems.) The number , with , of data symbols in the block is a design parameter. A commonly used code encodes eight-bit data symbols plus 32 eight-bit parity symbols in an -symbol block; this is denoted as a code, and is capable of correcting up to 16 symbol errors per block.
The Reed–Solomon code properties discussed above make them especially well-suited to applications where errors occur in bursts. This is because it does not matter to the code how many bits in a symbol are in error — if multiple bits in a symbol are corrupted it only counts as a single error. Conversely, if a data stream is not characterized by error bursts or drop-outs but by random single bit errors, a Reed–Solomon code is usually a poor choice compared to a binary code.
The Reed–Solomon code, like the convolutional code, is a transparent code. This means that if the channel symbols have been inverted somewhere along the line, the decoders will still operate. The result will be the inversion of the original data. However, the Reed–Solomon code loses its transparency when the code is shortened (see 'Remarks' at the end of this section). The "missing" bits in a shortened code need to be filled by either zeros or ones, depending on whether the data is complemented or not. (To put it another way, if the symbols are inverted, then the zero-fill needs to be inverted to a one-fill.) For this reason it is mandatory that the sense of the data (i.e., true or complemented) be resolved before Reed–Solomon decoding.
Whether the Reed–Solomon code is cyclic or not depends on subtle details of the construction. In the original view of Reed and Solomon, where the codewords are the values of a polynomial, one can choose the sequence of evaluation points in such a way as to make the code cyclic. In particular, if is a primitive root of the field , then by definition all non-zero elements of take the form for , where . Each polynomial over gives rise to a codeword . Since the function is also a polynomial of the same degree, this function gives rise to a codeword ; since holds, this codeword is the cyclic left-shift of the original codeword derived from . So choosing a sequence of primitive root powers as the evaluation points makes the original view Reed–Solomon code cyclic. Reed–Solomon codes in the BCH view are always cyclic because BCH codes are cyclic.
Remarks
Designers are not required to use the "natural" sizes of Reed–Solomon code blocks. A technique known as "shortening" can produce a smaller code of any desired size from a larger code. For example, the widely used (255,223) code can be converted to a (160,128) code by padding the unused portion of the source block with 95 binary zeroes and not transmitting them. At the decoder, the same portion of the block is loaded locally with binary zeroes.
The QR code, Ver 3 (29×29) uses interleaved blocks. The message has 26 data bytes and is encoded using two Reed-Solomon code blocks. Each block is a (255,233) Reed Solomon code shortened to a (35,13) code.
The Delsarte–Goethals–Seidel[13] theorem illustrates an example of an application of shortened Reed–Solomon codes. In parallel to shortening, a technique known as puncturing allows omitting some of the encoded parity symbols.
BCH view decoders
The decoders described in this section use the BCH view of a codeword as a sequence of coefficients. They use a fixed generator polynomial known to both encoder and decoder.
Peterson–Gorenstein–Zierler decoder
Daniel Gorenstein and Neal Zierler developed a decoder that was described in a MIT Lincoln Laboratory report by Zierler in January 1960 and later in a paper in June 1961.[14][15] The Gorenstein–Zierler decoder and the related work on BCH codes are described in the book Error Correcting Codes by W. Wesley Peterson (1961).[3]
Formulation
The transmitted message, , is viewed as the coefficients of a polynomial
As a result of the Reed–Solomon encoding procedure, s(x) is divisible by the generator polynomial where α is a primitive element.
Since s(x) is a multiple of the generator g(x), it follows that it "inherits" all its roots: Therefore,
The transmitted polynomial is corrupted in transit by an error polynomial to produce the received polynomial
Coefficient ei will be zero if there is no error at that power of x, and nonzero if there is an error. If there are ν errors at distinct powers ik of x, then
The goal of the decoder is to find the number of errors (ν), the positions of the errors (ik), and the error values at those positions (eik). From those, e(x) can be calculated and subtracted from r(x) to get the originally sent message s(x).
Syndrome decoding
The decoder starts by evaluating the polynomial as received at points . We call the results of that evaluation the "syndromes" Sj. They are defined as Note that because has roots at , as shown in the previous section.
The advantage of looking at the syndromes is that the message polynomial drops out. In other words, the syndromes only relate to the error and are unaffected by the actual contents of the message being transmitted. If the syndromes are all zero, the algorithm stops here and reports that the message was not corrupted in transit.
Error locators and error values
For convenience, define the error locators Xk and error values Yk as
Then the syndromes can be written in terms of these error locators and error values as
This definition of the syndrome values is equivalent to the previous since .
The syndromes give a system of n − k ≥ 2ν equations in 2ν unknowns, but that system of equations is nonlinear in the Xk and does not have an obvious solution. However, if the Xk were known (see below), then the syndrome equations provide a linear system of equations which can easily be solved for the Yk error values.
Consequently, the problem is finding the Xk, because then the leftmost matrix would be known, and both sides of the equation could be multiplied by its inverse, yielding Yk
In the variant of this algorithm where the locations of the errors are already known (when it is being used as an erasure code), this is the end. The error locations (Xk) are already known by some other method (for example, in an FM transmission, the sections where the bitstream was unclear or overcome with interference are probabilistically determinable from frequency analysis). In this scenario, up to errors can be corrected.
The rest of the algorithm serves to locate the errors and will require syndrome values up to , instead of just the used thus far. This is why twice as many error-correcting symbols need to be added as can be corrected without knowing their locations.
Error locator polynomial
There is a linear recurrence relation that gives rise to a system of linear equations. Solving those equations identifies those error locations Xk.
Define the error locator polynomial Λ(x) as
The zeros of Λ(x) are the reciprocals . This follows from the above product notation construction, since if , then one of the multiplied terms will be zero, , making the whole polynomial evaluate to zero:
Let be any integer such that . Multiply both sides by , and it will still be zero:
Sum for k = 1 to ν, and it will still be zero:
Collect each term into its own sum:
Extract the constant values of that are unaffected by the summation:
These summations are now equivalent to the syndrome values, which we know and can substitute in. This therefore reduces to
Subtracting from both sides yields
Recall that j was chosen to be any integer between 1 and v inclusive, and this equivalence is true for all such values. Therefore, we have v linear equations, not just one. This system of linear equations can therefore be solved for the coefficients Λi of the error-location polynomial: The above assumes that the decoder knows the number of errors ν, but that number has not been determined yet. The PGZ decoder does not determine ν directly but rather searches for it by trying successive values. The decoder first assumes the largest value for a trial ν and sets up the linear system for that value. If the equations can be solved (i.e., the matrix determinant is nonzero), then that trial value is the number of errors. If the linear system cannot be solved, then the trial ν is reduced by one and the next smaller system is examined.[16]
Find the roots of the error locator polynomial
Use the coefficients Λi found in the last step to build the error location polynomial. The roots of the error location polynomial can be found by exhaustive search. The error locators Xk are the reciprocals of those roots. The order of coefficients of the error location polynomial can be reversed, in which case the roots of that reversed polynomial are the error locators (not their reciprocals ). Chien search is an efficient implementation of this step.
Calculate the error values
Once the error locators Xk are known, the error values can be determined. This can be done by direct solution for Yk in the error equations matrix given above, or using the Forney algorithm.
Calculate the error locations
Calculate ik by taking the log base of Xk. This is generally done using a precomputed lookup table.
Fix the errors
Finally, e(x) is generated from ik and eik and then is subtracted from r(x) to get the originally sent message s(x), with errors corrected.
Example
Consider the Reed–Solomon code defined in GF(929) with α = 3 and t = 4 (this is used in PDF417 barcodes) for a RS(7,3) code. The generator polynomial is If the message polynomial is p(x) = 3 x2 + 2 x + 1, then a systematic codeword is encoded as follows: Errors in transmission might cause this to be received instead: The syndromes are calculated by evaluating r at powers of α: yielding the system
Using Gaussian elimination, so with roots x1 = 757 = 3−3 and x2 = 562 = 3−4. The coefficients can be reversed: to produce roots 27 = 33 and 81 = 34 with positive exponents, but typically this isn't used. The logarithm of the inverted roots corresponds to the error locations (right to left, location 0 is the last term in the codeword).
To calculate the error values, apply the Forney algorithm:
Subtracting from the received polynomial r(x) reproduces the original codeword s.
Berlekamp–Massey decoder
The Berlekamp–Massey algorithm is an alternate iterative procedure for finding the error locator polynomial. During each iteration, it calculates a discrepancy based on a current instance of Λ(x) with an assumed number of errors e: and then adjusts Λ(x) and e so that a recalculated Δ would be zero. The article Berlekamp–Massey algorithm has a detailed description of the procedure. In the following example, C(x) is used to represent Λ(x).
Example
Using the same data as the Peterson Gorenstein Zierler example above:
| n | Sn+1 | d | C | B | b | m |
|---|---|---|---|---|---|---|
| 0 | 732 | 732 | 197 x + 1 | 1 | 732 | 1 |
| 1 | 637 | 846 | 173 x + 1 | 1 | 732 | 2 |
| 2 | 762 | 412 | 634 x2 + 173 x + 1 | 173 x + 1 | 412 | 1 |
| 3 | 925 | 576 | 329 x2 + 821 x + 1 | 173 x + 1 | 412 | 2 |
The final value of C is the error locator polynomial, Λ(x).
Sugiyama decoder
Another iterative method for calculating both the error locator polynomial and the error value polynomial is based on Sugiyama's adaptation of the extended Euclidean algorithm.
Define S(x), Λ(x), and Ω(x) for t syndromes and e errors:
The key equation is:
For t = 6 and e = 3:
The middle terms are zero due to the relationship between Λ and syndromes.
The extended Euclidean algorithm can find a series of polynomials of the form
where the degree of R decreases as i increases. Once the degree of Ri(x) < t/2, then
B(x) and Q(x) don't need to be saved, so the algorithm becomes:
R−1 := xt
R0 := S(x)
A−1 := 0
A0 := 1
i := 0
while degree of Ri ≥ t/2
i := i + 1
Q := Ri-2 / Ri-1
Ri := Ri-2 - Q Ri-1
Ai := Ai-2 - Q Ai-1
to set low order term of Λ(x) to 1, divide Λ(x) and Ω(x) by Ai(0):
Ai(0) is the constant (low order) term of Ai.
Example
Using the same data as the Peterson–Gorenstein–Zierler example above:
| i | Ri | Ai |
|---|---|---|
| −1 | 001 x4 + 000 x3 + 000 x2 + 000 x + 000 | 000 |
| 0 | 925 x3 + 762 x2 + 637 x + 732 | 001 |
| 1 | 683 x2 + 676 x + 024 | 697 x + 396 |
| 2 | 673 x + 596 | 608 x2 + 704 x + 544 |
Decoder using discrete Fourier transform
A discrete Fourier transform can be used for decoding.[17] To avoid conflict with syndrome names, let c(x) = s(x) the encoded codeword. r(x) and e(x) are the same as above. Define C(x), E(x), and R(x) as the discrete Fourier transforms of c(x), e(x), and r(x). Since r(x) = c(x) + e(x), and since a discrete Fourier transform is a linear operator, R(x) = C(x) + E(x).
Transform r(x) to R(x) using discrete Fourier transform. Since the calculation for a discrete Fourier transform is the same as the calculation for syndromes, t coefficients of R(x) and E(x) are the same as the syndromes:
Use through as syndromes (they're the same) and generate the error locator polynomial using the methods from any of the above decoders.
Let v = number of errors. Generate E(x) using the known coefficients to , the error locator polynomial, and these formulas
Then calculate C(x) = R(x) − E(x) and take the inverse transform (polynomial interpolation) of C(x) to produce c(x).
Decoding beyond the error-correction bound
The Singleton bound states that the minimum distance d of a linear block code of size (n,k) is upper-bounded by n - k + 1. The distance d was usually understood to limit the error-correction capability to ⌊(d - 1) / 2⌋. The Reed–Solomon code achieves this bound with equality, and can thus correct up to ⌊(n - k) / 2⌋ errors. However, this error-correction bound is not exact.
In 1999, Madhu Sudan and Venkatesan Guruswami at MIT published "Improved Decoding of Reed–Solomon and Algebraic-Geometry Codes" introducing an algorithm that allowed for the correction of errors beyond half the minimum distance of the code.[18] It applies to Reed–Solomon codes and more generally to algebraic geometric codes. This algorithm produces a list of codewords (it is a list-decoding algorithm) and is based on interpolation and factorization of polynomials over GF(2m) and its extensions.
In 2023, coding theorists showed that Reed-Solomon codes defined over random evaluation points can achieve achieve list decoding capacity (up to n - k errors) over linear size alphabets with high probability.[19][20][21] These results do not provide an algorithm for performing the decoding.
Soft-decoding
The algebraic decoding methods described above are hard-decision methods, which means that for every symbol a hard decision is made about its value. For example, a decoder could associate with each symbol an additional value corresponding to the channel demodulator's confidence in the correctness of the symbol. The advent of LDPC and turbo codes, which employ iterated soft-decision belief propagation decoding methods to achieve error-correction performance close to the theoretical limit, has spurred interest in applying soft-decision decoding to conventional algebraic codes. In 2003, Ralf Koetter and Alexander Vardy presented a polynomial-time soft-decision algebraic list-decoding algorithm for Reed–Solomon codes, which was based upon the work by Sudan and Guruswami.[22] In 2016, Steven J. Franke and Joseph H. Taylor published a novel soft-decision decoder.[23]
Reed Solomon original view decoders
The decoders described in this section use the Reed Solomon original view of a codeword as a sequence of polynomial values where the polynomial is based on the message to be encoded. The same set of fixed values are used by the encoder and decoder, and the decoder recovers the encoding polynomial (and optionally an error locating polynomial) from the received message.
Theoretical decoder
Reed and Solomon described a theoretical decoder that corrected errors by finding the most popular message polynomial.[1] The decoder only knows the set of values to and which encoding method was used to generate the codeword's sequence of values. The original message, the polynomial, and any errors are unknown. A decoding procedure could use a method like Lagrange interpolation on various subsets of n codeword values taken k at a time to repeatedly produce potential polynomials, until a sufficient number of matching polynomials are produced to reasonably eliminate any errors in the received codeword. Once a polynomial is determined, then any errors in the codeword can be corrected, by recalculating the corresponding codeword values. Unfortunately, in all but the simplest of cases, there are too many subsets, so the algorithm is impractical. The number of subsets is the binomial coefficient, , and the number of subsets is infeasible for even modest codes. For a (255,249) code that can correct 3 errors, the naïve theoretical decoder would examine 359 billion subsets.
Berlekamp Welch decoder
In 1986, a decoder known as the Berlekamp–Welch algorithm was developed as a decoder that is able to recover the original message polynomial as well as an error "locator" polynomial that produces zeroes for the input values that correspond to errors, with time complexity O(n3), where n is the number of values in a message. The recovered polynomial is then used to recover (recalculate as needed) the original message.
Example
Using RS(7,3), GF(929), and the set of evaluation points ai = i − 1
- a = {0, 1, 2, 3, 4, 5, 6}
If the message polynomial is
- p(x) = 003x2 + 002x + 001
The codeword is
- c = {001, 006, 017, 034, 057, 086, 121}
Errors in transmission might cause this to be received instead.
- b = c + e = {001, 006, 123, 456, 057, 086, 121}
The key equation is:
- biE(ai) - Q(ai) = 0
Assume maximum number of errors: e = 2. The key equation becomes:
- bi(e0 + e1ai) - (q0 + q1ai + q2 a2i + q3a3i + q4a4i) = - bia2i
Using Gaussian elimination:
- Q(x) = 003x4 + 916x3 + 009x2 + 007x + 006
- E(x) = 001x2 + 924x + 006
- Q(x)/E(x) = P(x) = 003x2 + 002x + 001
Recalculate P(x) where E(x) = 0 : {2, 3} to correct b resulting in the corrected codeword:
- c = {001, 006, 017, 034, 057, 086, 121} }}
Gao decoder
In 2002, an improved decoder was developed by Shuhong Gao, based on the extended Euclid algorithm.[24]
Example
- Lagrange interpolation of for to
- generate and until degree of , for this example
| i | Ri | Ai |
|---|---|---|
| −1 | 001x7 + 908x6 + 175x5 + 194x4 + 695x3 + 094x2 + 720x + 000 | 000 |
| 0 | 055x6 + 440x5 + 497x4 + 904x3 + 424x2 + 472x + 001 | 001 |
| 1 | 702x5 + 845x4 + 691x3 + 461x2 + 327x + 237 | 152 x + 237 |
| 2 | 266x4 + 086x3 + 798x2 + 311x + 532 | 708x2 + 176x + 532 |
- Q(x) = R2 = 266x4 + 086x3 + 798x2 + 311x + 532
- E(x) = A2 = 708x2 + 176x + 532
To duplicate the polynomials generated by Berlekamp Welsh, divide Q(x) and E(x) by most significant coefficient of E(x) = 708.
- Q(x) = 003x4 + 916x3 + 009x2 + 007x + 006
- E(x) = 001x2 + 924x + 006
- Q(x)/E(x) = P(x) = 003x2 + 002x + 001
Recalculate P(x) where E(x) = 0 : {2, 3} to correct b resulting in the corrected codeword:
- c = {001, 006, 017, 034, 057, 086, 121}
Syndrome decoder
Around 2015, an improved decoder was developed.[25] The decoder generates syndromes, and similar to BCH view, the key equation between the error locator polynomial and syndromes is the same, but the error locator polynomial has roots corresponding to , and a look up table is used to convert the roots into codeword offsets.
Initialization:
A polynomial is defined: .
A set of polynomials is defined: .
A set of values is generated .
A set of polynomials is generated:
Decoding - A codeword with possible errors is received .
A syndrome polynomial is generated .
If then no errors are detected, otherwise extended Euclid starts off with
, , ,
and continues until degree of
The error locator polynomial is
and the error value polynomial is
and are divided by the least significant term of
The formal derivative of is generated:
The offsets of the errors correspond to the roots of
for root = ,
The error value for is
.
If then an error value corresponding to
has been detected at offset , and a separate error value is calculated:
, the set of corresponding to roots of
most significant coefficient of
Example
Using the same data as the Berlekamp Welch example
Initialization:
| i | Pi |
|---|---|
| 0 | 040 |
| 1 | 689 z3 + 689 z2 + 689 z + 689 |
| 2 | 155 z3 + 542 z2 + 271 z + 600 |
| 3 | 696 z3 + 232 z2 + 387 z + 129 |
| 4 | 311 z3 + 310 z2 + 542 z + 600 |
| 5 | 657 z3 + 503 z2 + 658 z + 689 |
| 6 | 279 z3 + 511 z2 + 240 z + 040 |
Decoding:
Euclid:
| i | Ri | Ai |
|---|---|---|
| -1 | 001 z4 + 000 z3 + 000 z2 + 000 z + 000 | 000 |
| 0 | 785 z3 + 213 z2 + 666 z + 055 | 001 |
| 1 | 658 z2 + 858 z + 323 | 200 z + 141 |
| 2 | 294 z + 709 | 905 z2 + 020 z + 925 |
divide and by 925
See also
- BCH code
- Berlekamp–Massey algorithm
- Berlekamp–Welch algorithm
- Chien search
- Cyclic code
- Folded Reed–Solomon code
- Forward error correction
Notes
- ↑ Authors in Andrews et al. (2007), provide simulation results which show that for the same code rate (1/6) turbo codes outperform Reed-Solomon concatenated codes up to 2 dB (bit error rate).[10]
References
- ↑ 1.0 1.1 1.2 1.3 1.4 1.5 Reed, Irving S.; Solomon, Gustave (1960). "Polynomial Codes over Certain Finite Fields". Journal of the Society for Industrial and Applied Mathematics 8 (2): 300–304. doi:10.1137/0108018. https://sites.math.rutgers.edu/~zeilberg/akherim/ReedS1960.pdf.
- ↑ Gorenstein, D.; Zierler, N. (June 1961). "A class of cyclic linear error-correcting codes in pm symbols". J. SIAM 9 (2): 207–214. doi:10.1137/0109020.
- ↑ 3.0 3.1 Peterson, W. Wesley (1961). Error-Correcting Codes. MIT Press. ISBN 978-0262160063. OCLC 859669631.
- ↑ Peterson, W. Wesley; Weldon, E. J. (1996). Error Correcting Codes (2nd ed.). MIT Press. ISBN 978-0-585-30709-1. OCLC 45727875. https://books.google.com/books?id=5kfwlFeklx0C&pg=PP11&dq=9780262160391.
- ↑ Sugiyama, Y.; Kasahara, M.; Hirasawa, S.; Namekawa, T. (1975). "A method for solving key equation for decoding Goppa codes". Information and Control 27 (1): 87–99. doi:10.1016/S0019-9958(75)90090-X.
- ↑ Gao, Shuhong (January 2002), New Algorithm For Decoding Reed-Solomon Codes, Clemson, http://www.math.clemson.edu/~sgao/papers/RS.pdf.
- ↑ "Generalized Reed-Solomon Codes". https://users.math.msu.edu/users/halljo/classes/codenotes/grs.pdf.
- ↑ Immink, K. A. S. (1994), "Reed–Solomon Codes and the Compact Disc", in Wicker, Stephen B.; Bhargava, Vijay K., Reed–Solomon Codes and Their Applications, IEEE Press, ISBN 978-0-7803-1025-4
- ↑ Hagenauer, J.; Offer, E.; Papke, L. (1994). "11. Matching Viterbi Decoders and Reed-Solomon Decoders in a Concatenated System". Reed Solomon Codes and Their Applications. IEEE Press. p. 433. ISBN 9780470546345. OCLC 557445046.
- ↑ 10.0 10.1 Andrews, K.S.; Divsalar, D.; Dolinar, S.; Hamkins, J.; Jones, C.R.; Pollara, F. (2007). "The development of turbo and LDPC codes for deep-space applications.". Proceedings of the IEEE 95 (11): 2142–56. doi:10.1109/JPROC.2007.905132. https://scholar.archive.org/work/shkuo6oxabbklkfz4d6v4gero4/access/wayback/http://coding.jpl.nasa.gov/~hamkins/publications/journals/2007_11_turbo_LDPC.pdf.
- ↑ Lin, Shu; Costello, Daniel J. (1983). Error control coding: fundamentals and applications (Nachdr. ed.). Englewood Cliffs, NJ: Prentice-Hall. p. 171. ISBN 978-0-13-283796-5.
- ↑ "Analytical Expressions Used in bercoding and BERTool". https://www.mathworks.com/help/comm/ug/bit-error-rate-ber.html#brck0zf.
- ↑ Pfender, Florian; Ziegler, Günter M. (September 2004), "Kissing Numbers, Sphere Packings, and Some Unexpected Proofs", Notices of the American Mathematical Society 51 (8): 873–883, https://www.ams.org/notices/200408/fea-pfender.pdf, retrieved 2009-09-28. Explains the Delsarte-Goethals-Seidel theorem as used in the context of the error correcting code for compact disc.
- ↑ Peterson, W. (September 1960). "Encoding and error-correction procedures for the Bose-Chaudhuri codes". IEEE Transactions on Information Theory 6 (4): 459–470. doi:10.1109/TIT.1960.1057586. Bibcode: 1960IRTIT...6..459P.
- ↑ Gorenstein, Daniel; Zierler, Neal (June 1961). "A Class of Error-Correcting Codes in $p^m $ Symbols". Journal of the Society for Industrial and Applied Mathematics 9 (2): 207–214. doi:10.1137/0109020.
- ↑ Gill, John (n.d.). "EE387 Notes #7, Handout #28". Stanford University. http://www.stanford.edu/class/ee387/handouts/notes7.pdf.
- ↑ Lin, Shu; Costello, Daniel J. (2004). Error control coding: fundamentals and applications (2. ed.). Upper Saddle River, NJ: Pearson/Prentice Hall. pp. 255–262. ISBN 978-0130426727.
- ↑ Guruswami, V.; Sudan, M. (September 1999), "Improved decoding of Reed–Solomon codes and algebraic geometry codes", IEEE Transactions on Information Theory 45 (6): 1757–1767, doi:10.1109/18.782097
- ↑ Brakensiek, Joshua; Gopi, Sivakanth; Makam, Visu (2023-06-02). "Generic Reed-Solomon Codes Achieve List-Decoding Capacity". Proceedings of the 55th Annual ACM Symposium on Theory of Computing. STOC 2023. New York, NY, USA: Association for Computing Machinery. pp. 1488–1501. doi:10.1145/3564246.3585128. ISBN 978-1-4503-9913-5. https://doi.org/10.1145/3564246.3585128.
- ↑ Guo, Zeyu; Zhang, Zihan (2023). "Randomly Punctured Reed-Solomon Codes Achieve the List Decoding Capacity over Polynomial-Size Alphabets". 2023 IEEE 64th Annual Symposium on Foundations of Computer Science (FOCS). FOCS 2023, Santa Cruz, CA, USA, 2023. pp. 164–176. doi:10.1109/FOCS57990.2023.00019. ISBN 979-8-3503-1894-4. https://doi.org/10.1109/FOCS57990.2023.00019.
- ↑ Alrabiah, Omar; Guruswami, Venkatesan; Li, Ray (2025), "Random Reed-Solomon codes achieve list-decoding capacity with linear-sized alphabets", Advances in Combinatorics, doi:10.19086/aic.2025.8
- ↑ Koetter, Ralf; Vardy, Alexander (2003). "Algebraic soft-decision decoding of Reed–Solomon codes". IEEE Transactions on Information Theory 49 (11): 2809–2825. doi:10.1109/TIT.2003.819332. Bibcode: 2003ITIT...49.2809K.
- ↑ Franke, Steven J.; Taylor, Joseph H. (2016). "Open Source Soft-Decision Decoder for the JT65 (63,12) Reed–Solomon Code". QEX (May/June): 8–17. http://physics.princeton.edu/pulsar/K1JT/FrankeTaylor_QEX_2016.pdf. Retrieved 2017-06-07.
- ↑ "A new algorithm for decoding Reed-Solomon codes". https://www.math.clemson.edu/~sgao/papers/RS.pdf.
- ↑ "Generalized Reed-Solomon Codes". https://users.math.msu.edu/users/halljo/classes/codenotes/grs.pdf.
External links
Information and tutorials
- Welch, L. R. (1997), The Original View of Reed–Solomon Codes, Lecture Notes, http://csi.usc.edu/PDF/RSoriginal.pdf
- Koetter, Ralf (2005), Reed–Solomon Codes, MIT Lecture Notes 6.451 (Video), http://ocw.mit.edu/courses/electrical-engineering-and-computer-science/6-451-principles-of-digital-communication-ii-spring-2005/lecture-notes/lecture-10-reed-solomon-codes/
- Introduction to Reed–Solomon codes: principles, architecture and implementation (CMU)
- Geisel, William A. (August 1990), Tutorial on Reed–Solomon Error Correction Coding, Technical Memorandum, NASA, TM-102162, https://ntrs.nasa.gov/citations/19900019023
- Reid, Jeff A. (April 1995), CRC and Reed Solomon ECC, http://rcgldr.net/misc/ecc.pdf
Implementations
- FEC library in C by Phil Karn (aka KA9Q) includes Reed–Solomon codec, both arbitrary and optimized (223,255) version
- Open Source C++ Reed–Solomon Soft Decoding library
- Matlab implementation of errors and-erasures Reed–Solomon decoding
 |
