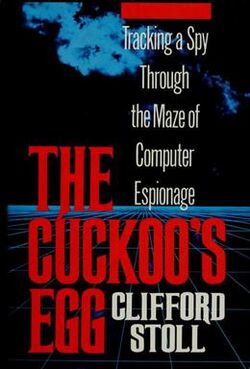
The Cuckoo's Egg
 | |
| Author | Clifford Stoll |
|---|---|
| Country | United States |
| Language | English |
| Publisher | Doubleday |
Publication date | 1989 |
| Media type | |
| Pages | 326 |
| ISBN | ISBN:0-385-24946-2 |
| OCLC | 43977527 |
| 364.16/8/0973 21 | |
| LC Class | UB271.R92 H477 2000 |
The Cuckoo's Egg: Tracking a Spy Through the Maze of Computer Espionage is a 1989 book written by Clifford Stoll. It is his first-person account of the hunt for a computer hacker who broke into a computer at the Lawrence Berkeley National Laboratory (LBNL).
Summary
Author Clifford Stoll, an astronomer by training, managed computers at Lawrence Berkeley National Laboratory (LBNL) in California. One day in 1986 his supervisor, Dave Cleveland, asked him to resolve an accounting error of 75 cents in the computer usage accounts. Stoll traced the error to an unauthorized user who had apparently used nine seconds of computer time and not paid for it. Stoll eventually realized that the unauthorized user was a hacker who had acquired superuser access to the LBNL system by exploiting a vulnerability in the movemail function of the original GNU Emacs.
Early on, and over the course of a long weekend, Stoll rounded up fifty terminals, as well as teleprinters, mostly by “borrowing” them from the desks of co-workers away for the weekend. These he physically attached to the fifty incoming phone lines at LBNL. When the hacker dialed in that weekend, Stoll located the phone line used, which was coming from the Tymnet routing service. With the help of Tymnet, he eventually tracked the intrusion to a call center at MITRE, a defense contractor in McLean, Virginia. Over the next ten months, Stoll spent enormous amounts of time and effort tracing the hacker's origin. He saw that the hacker was using a 1200 baud connection and realized that the intrusion was coming through a telephone modem connection. Stoll's colleagues, Paul Murray and Lloyd Bellknap, assisted with the phone lines.
After returning his “borrowed” terminals, Stoll left a teleprinter attached to the intrusion line in order to see and record everything the hacker did. He watched as the hacker sought – and sometimes gained – unauthorized access to military bases around the United States, looking for files that contained words such as “nuclear” or “SDI”. The hacker also copied password files (in order to make dictionary attacks) and set up Trojan horses to find passwords. Stoll was amazed that on many of these high-security sites the hacker could easily guess passwords, since many system administrators had never bothered to change the passwords from their factory defaults. Even on military bases, the hacker was sometimes able to log in as “guest” with no password.
This was one of the first — if not the first — documented cases of a computer break-in, and Stoll seems to have been the first to keep a daily logbook of the hacker's activities. Over the course of his investigation, Stoll contacted various agents at the Federal Bureau of Investigation (FBI), the Central Intelligence Agency, the National Security Agency and the United States Air Force Office of Special Investigations. At the very beginning there was confusion as to jurisdiction and a general reluctance to share information; the FBI in particular was uninterested as no large sum of money was involved and no classified information was accessed.
Studying his log book, Stoll saw that the hacker was familiar with VMS, as well as AT&T Unix. He also noted that the hacker tended to be active around the middle of the day, Pacific time. Eventually Stoll hypothesized that, since modem bills are cheaper at night and most people have school or a day job and would only have a lot of free time for hacking at night, the hacker was in a time zone some distance to the east.
With the help of Tymnet and agents from various agencies, Stoll found that the intrusion was coming from West Germany via satellite. The Deutsche Bundespost (the West German post office) also had authority over the phone system there, and it traced the calls to a university in Bremen. In order to entice the hacker to reveal himself, Stoll set up an elaborate hoax – known today as a honeypot – by inventing a fictitious department at LBNL that had supposedly been newly formed by an “SDI“ contract, also fictitious. When he realized the hacker was particularly interested in the faux SDI entity, he filled the “SDInet” account (operated by an imaginary secretary named ‘Barbara Sherwin’) with large files full of impressive-sounding bureaucratese. The ploy worked, and the Deutsche Bundespost finally located the hacker at his home in Hanover. The hacker's name was Markus Hess, and he had been engaged for some years in selling the results of his hacking to the Soviet Union’s intelligence agency, the KGB. There was ancillary proof of this when a Hungarian agent contacted the fictitious SDInet at LBL by mail, based on information he could only have obtained through Hess. Apparently this was the KGB's method of double-checking to see if Hess was just making up the information he was selling.
Stoll later flew to West Germany to testify at the trial of Hess and a confederate.
References in popular culture
- The book was chronicled in an episode of WGBH’s NOVA entitled “The KGB, the Computer, and Me”, which aired on PBS stations on October 3, 1990.[1][2]
- Another documentary, Spycatcher, was made by Yorkshire Television.[2]
- The number sequence mentioned in Chapter 48 has become a popular math puzzle, known as the Cuckoo's Egg, the Morris Number Sequence, or the look-and-say sequence.
- In the summer of 2000 the name “Cuckoo’s Egg” was used to describe a file sharing hack attempt that substituted white noise or sound effects files for legitimate song files on Napster and other networks.[3]
- These events are referenced in Cory Doctorow’s speculative fiction short story “The Things that Make Me Weak and Strange Get Engineered Away”, as “(a) sysadmin who’d tracked a $0.75 billing anomaly back to a foreign spy-ring that was using his systems to hack his military”.[4]
See also
References
External links
- Image of 1st Edition Cover—Doubleday
- Stalking the Wily Hacker The author's original article about the trap
- Booknotes interview with Stoll on Cuckoo’s Egg, December 3, 1989
- Reference to the book on Internet Storm Center
- West German hackers use Columbia's Kermit software to break into dozens of US military computers and capture information for the KGB, Columbia University Computing History, 1986-1987 section.

