Software:Hacker (video game)
| Hacker | |
|---|---|
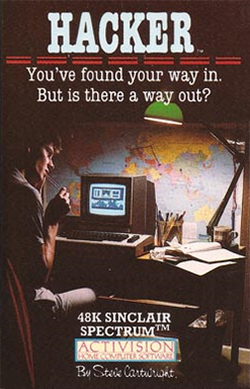 ZX Spectrum cover art | |
| Developer(s) | Activision |
| Publisher(s) | Activision |
| Producer(s) | Brad Fregger |
| Designer(s) | Steve Cartwright |
| Platform(s) | Amiga, Amstrad CPC, Apple II, Atari 8-bit, Atari ST, Commodore 64, DOS, Macintosh, MSX2, ZX Spectrum |
| Release | 1985, 1986, 1988 |
| Genre(s) | Puzzle, strategy |
| Mode(s) | Single-player |
Hacker is a 1985 video game by Activision. It was designed by Steve Cartwright and released for the Amiga, Amstrad CPC, Apple II, Atari 8-bit family, Atari ST, Commodore 64, Macintosh, DOS, MSX2, and ZX Spectrum.
Plot
Activision executive Jim Levy introduced Hacker to reporters by pretending that something had gone wrong during his attempt to connect on line to company headquarters to demonstrate a new game. After several attempts he logged into a mysterious non-Activision computer, before explaining, "That, ladies and gentlemen, is the game". The player assumes the role of a hacker, a person experienced in breaking into secure computer systems, who accidentally acquires access to a non-public system. The game was shipped with no information on how to play, thus building the concept that the player did hack into a system.[1]
Gameplay
The player must attempt to hack into the Magma Ltd. computer system at the beginning of the game by guessing the logon password. The password becomes obvious only after gaining access, through another means of entry, to the later stage of the game, but typing "help" or "h" in the initial command line gives a clue. Since initial attempts consist of guessing (and likely failing), access is eventually granted due to a supposed malfunction in the security system. Once the player is in, the player is asked to identify various parts of a robot unit by pointing the cursor at the relevant parts and pressing the joystick button. Most parts have exotic and technical names, such as "asynchronous data compactor" or "phlamson joint"—this again allows more room for error by initially trying to guess which part each name belongs to. Failure to identify each part correctly forces the player to take a retest until a 100 percent identification is made, at which point the player is then allowed to continue.
The player gains control of the robot which can travel around the globe via secret tunnels, deep within the earth. The game's text states that the robot is powered in some manner by magma. It is evident that the player has logged into the Magma company's network and is acting as a remote user in its global subterranean transport network, with various strange messages being broadcast hinting at dangerous experiments that the company is doing.
Before getting far, the player is informed that shredded portions of a secret document containing Magma Ltd.'s plans for world domination have been stolen. The player is instructed to retrieve the document by bargaining with the spies who stole it, who are located at various locations throughout the globe. The player is warned that it must be retrieved in order to prevent the U.S. government from thwarting their plans. At this point, the player's objective is clear: retrieve the strips of the stolen document, then deliver them to Washington, D.C.
The robot's tunnel system is extensive but unmarked, so getting around is initially an exercise in trial and error. Throughout the globe, there are several cities where the robot can surface and interact with people, primarily the spies who want to bargain for their piece of the evidence.
At the various surfacing cities, the player must try to convince the agents to turn over their piece of evidence. Initially the player only has $5,000 to bargain with, but their arsenal of items grows over time and bargaining. The real challenge of the game is determining what each spy wants and how to get it for them. Eventually, all the spies' whims can be satisfied for all the pieces of the secret document. Note that different copies of the game, even on the same computer platform, have differences in which items the spies want.
However, Magma Ltd. discovers the player's break-in shortly after penetration. It launches a security satellite which, when it intersects with the player's position, demands information which supposedly only a legitimate user would know. The information queried is given to the player previously in the game, but the questions can only be answered if the player has taken careful notes as some of the information asked for is rather obscure. To put more pressure on the player, the Satellites will only allow the player to pass checks four times before another catch will cause the player to get disconnected due to suspicious activity. In addition, the player is under a time limit (tracked by movements the SRU makes); should the player take too long the system will automatically disconnect them anyway, regardless of the Satellites. The sensors of the network will also start to fail, limiting the player's ability to see turns in the tunnels ahead and eventually where their SRU is located, forcing the player to rely on maps of the tunnel network to make it through. If the player goes near Australia in the network, an automatic game over is issued however the knowledge may help in a future play through for evading a check.
The game lacks a save game feature. A player who fails must start again from the beginning.
Reception
By late 1987 more than 50,000 copies of Hacker were sold, and it was Activision's third best-selling Commodore game.[2] Info rated Hacker four stars out of five, describing it as "an interesting concept" with "fair to good graphics and sound".[3] Roy Wagner reviewed the game for Computer Gaming World, and stated that "The game is a real challenge (some read that frustrating)."[4] Ahoy! wrote that its puzzle nature "is certain to enthrall some and repel others ... repeated play is an integral part of reaching the solution. Those who enjoy a protracted battle of wits will find Hacker a lively test of their abilities".[5] Compute! praised the game's initial realism, and concluded that it was "a worthy addition to your software collection, especially if you enjoy adventure games that require a bit of thought and an investment of time".[6]
Reviews
- Games #70[7]
Legacy
This game was followed in 1986 by Hacker II. In the sequel, the player is actually recruited based upon their (assumed) success with the activities in the original game. Once again, they are tasked with controlling a robot, this time to infiltrate a secure facility in order to retrieve documents known only as "The Doomsday Papers" from a well-guarded vault to ensure the security of the United States.
See also
- System 15000
- Neuromancer
References
- ↑ Bateman, Selby; Yakal, Kathy (October 1985). "The New Games". Compute!: pp. 32. https://archive.org/stream/1985-10-compute-magazine/Compute_Issue_065_1985_Oct#page/n33/mode/2up. Retrieved 16 October 2013.
- ↑ Ferrell, Keith (December 1987). "The Commodore Games That Live On And On". Compute's Gazette: pp. 18–22. https://archive.org/stream/1987-12-computegazette/Compute_Gazette_Issue_54_1987_Dec#page/n17/mode/2up. Retrieved 24 January 2015.
- ↑ Dunnington, Benn; Brown, Mark R. (December 1985 – January 1986). "C-64/128 Gallery". Info: 4–5, 88–93. https://archive.org/stream/info-magazine-09/Info_Issue_09_1985_Dec-Jan_1986#page/n5/mode/2up. Retrieved 2019-03-19.
- ↑ Wagner, Roy (Jan–Feb 1986). "The Commodore Key". Computer Gaming World 1 (25): 19.
- ↑ Davidson, Steve (January 1986). "Hacker". Ahoy!: pp. 54. https://archive.org/stream/Ahoy_Issue_25_1986-01_Ion_International_US#page/n53/mode/2up. Retrieved 2 July 2014.
- ↑ Heimarck, Todd (April 1986). "Hacker". Compute!: pp. 65. https://archive.org/stream/1986-04-compute-magazine/Compute_Issue_071_1986_Apr#page/n65/mode/2up. Retrieved 8 November 2013.
- ↑ "GAMES Magazine #70". December 1985. https://archive.org/details/games701985december/page/n51/mode/2up.
External links
- MobyGames is a commercial database website that catalogs information on video games and the people and companies behind them via crowdsourcing. This includes over 300,000 games for hundreds of platforms.[1] Founded in 1999, ownership of the site has changed hands several times. It has been owned by Atari SA since 2022.
Features
Edits and submissions to the site (including screenshots, box art, developer information, game summaries, and more) go through a verification process of fact-checking by volunteer "approvers".[2] This approval process after submission can range from minutes to days or months.[3] The most commonly used sources are the video game's website, packaging, and credit screens. There is a published standard for game information and copy-editing.[4] A ranking system allows users to earn points for contributing accurate information.[5]
Registered users can rate and review games. Users can create private or public "have" and "want" lists, which can generate a list of games available for trade with other registered users. The site contains an integrated forum. Each listed game can have its own sub-forum.
History

MobyGames was founded on March 1, 1999, by Jim Leonard and Brian Hirt, and joined by David Berk 18 months later, the three of which had been friends since high school.[6][7] Leonard had the idea of sharing information about computer games with a larger audience. The database began with information about games for IBM PC compatibles, relying on the founders' personal collections. Eventually, the site was opened up to allow general users to contribute information.[5] In a 2003 interview, Berk emphasized MobyGames' dedication to taking video games more seriously than broader society and to preserving games for their important cultural influence.[5]
In mid-2010, MobyGames was purchased by GameFly for an undisclosed amount.[8] This was announced to the community post factum , and the site's interface was given an unpopular redesign.[7] A few major contributors left, refusing to do volunteer work for a commercial website.{{Citation needed|date=June 2025} On December 18, 2013, MobyGames was acquired by Jeremiah Freyholtz, owner of Blue Flame Labs (a San Francisco-based game and web development company) and VGBoxArt (a site for fan-made video game box art).[9] Blue Flame Labs reverted MobyGames' interface to its pre-overhaul look and feel,[10] and for the next eight years, the site was run by Freyholtz and Independent Games Festival organizer Simon Carless.[7]
On November 24, 2021, Atari SA announced a potential deal with Blue Flame Labs to purchase MobyGames for $1.5 million.[11] The purchase was completed on 8 March 2022, with Freyholtz remaining as general manager.[12][13][14] Over the next year, the financial boost given by Atari led to a rework of the site being built from scratch with a new backend codebase, as well as updates improving the mobile and desktop user interface.[1] This was accomplished by investing in full-time development of the site instead of its previously part-time development.[15]
In 2024, MobyGames began offering a paid "Pro" membership option for the site to generate additional revenue.[16] Previously, the site had generated income exclusively through banner ads and (from March 2014 onward) a small number of patrons via the Patreon website.[17]
On February 13, 2025, Freyholtz stepped down as the site lead to move onto new projects, leaving operations to Tracy Poff, a veteran coder on the site, and Atari staff.[18]
See also
- IGDB – game database used by Twitch for its search and discovery functions
References
- ↑ 1.0 1.1 Sheehan, Gavin (2023-02-22). "Atari Relaunches The Fully Rebuilt & Optimized MobyGames Website". https://bleedingcool.com/games/atari-relaunches-the-fully-rebuilt-optimized-mobygames-website/.
- ↑ Litchfield, Ted (2021-11-26). "Zombie company Atari to devour MobyGames". https://www.pcgamer.com/zombie-company-atari-to-devour-mobygames/.
- ↑ "MobyGames FAQ: Emails Answered § When will my submission be approved?". Blue Flame Labs. 30 March 2014. http://www.mobygames.com/info/faq7#g1.
- ↑ "The MobyGames Standards and Practices". Blue Flame Labs. 6 January 2016. http://www.mobygames.com/info/standards.
- ↑ 5.0 5.1 5.2 Miller, Stanley A. (2003-04-22). "People's choice awards honor favorite Web sites". Milwaukee Journal Sentinel.
- ↑ "20 Years of MobyGames" (in en). 2019-02-28. https://trixter.oldskool.org/2019/02/28/20-years-of-mobygames/.
- ↑ 7.0 7.1 7.2 Plunkett, Luke (2022-03-10). "Atari Buys MobyGames For $1.5 Million". https://kotaku.com/mobygames-retro-credits-database-imdb-atari-freyholtz-b-1848638521.
- ↑ "Report: MobyGames Acquired By GameFly Media". Gamasutra. 2011-02-07. https://www.gamedeveloper.com/game-platforms/report-mobygames-acquired-by-gamefly-media.
- ↑ Corriea, Alexa Ray (December 31, 2013). "MobyGames purchased from GameFly, improvements planned". http://www.polygon.com/2013/12/31/5261414/mobygames-purchased-from-gamefly-improvements-planned.
- ↑ Wawro, Alex (31 December 2013). "Game dev database MobyGames getting some TLC under new owner". Gamasutra. https://www.gamedeveloper.com/business/game-dev-database-mobygames-getting-some-tlc-under-new-owner.
- ↑ "Atari invests in Anstream, may buy MobyGames". November 24, 2021. https://www.gamesindustry.biz/articles/2021-11-24-atari-invests-in-anstream-may-buy-mobygames.
- ↑ Rousseau, Jeffrey (2022-03-09). "Atari purchases Moby Games". https://www.gamesindustry.biz/atari-purchases-moby-games.
- ↑ "Atari Completes MobyGames Acquisition, Details Plans for the Site's Continued Support". March 8, 2022. https://www.atari.com/atari-completes-mobygames-acquisition-details-plans-for-the-sites-continued-support/.
- ↑ "Atari has acquired game database MobyGames for $1.5 million" (in en-GB). 2022-03-09. https://www.videogameschronicle.com/news/atari-has-acquired-game-database-mobygames-for-1-5-million/.
- ↑ Stanton, Rich (2022-03-10). "Atari buys videogame database MobyGames for $1.5 million". https://www.pcgamer.com/atari-buys-videogame-database-mobygames-for-dollar15-million/.
- ↑ Harris, John (2024-03-09). "MobyGames Offering “Pro” Membership". https://setsideb.com/mobygames-offering-pro-membership/.
- ↑ "MobyGames on Patreon". http://www.patreon.com/mobygames.
- ↑ "An update on MobyGames leadership". 2025-02-13. https://www.mobygames.com/forum/3/thread/269628/an-update-on-mobygames-leadership/#post-269628.
Wikidata has the property:
|
External links
- No URL found. Please specify a URL here or add one to Wikidata.
 |
- Hacker at SpectrumComputing.co.uk
- Hacker can be played for free in the browser at the Internet Archive
 |

