Software:OpenBSD
 Free, Functional, and Secure | |
 | |
| Developer | Theo de Raadt et al. |
|---|---|
| Written in | C, assembly, Perl, Unix shell |
| OS family | Unix-like (BSD) |
| Working state | Current |
| Source model | Open source |
| Initial release | July 1996 |
| |Final release|Latest release}} | 7.4 (16 October 2023) [±] |
| Package manager | OpenBSD package tools[1] |
| Platforms | Alpha, x86-64, ARMv7, ARMv8 (64-bit), PA-RISC, IA-32, LANDISK, Loongson, Omron LUNA-88K, MIPS64, macppc, PowerPC, 64-bit RISC-V, SPARC64[2] |
| Kernel type | Monolithic |
| Userland | BSD |
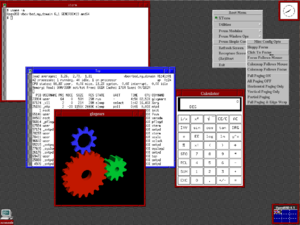
| Default user interface | Modified pdksh, X11 (FVWM) |
| License | BSD, ISC, other permissive licenses[3] |
OpenBSD is a security-focused, free software, Unix-like operating system based on the Berkeley Software Distribution (BSD). Theo de Raadt created OpenBSD in 1995 by forking NetBSD 1.0.[4] The OpenBSD project emphasizes portability, standardization, correctness, proactive security, and integrated cryptography.[5]
The OpenBSD project maintains portable versions of many subsystems as packages for other operating systems. Because of the project's preferred BSD license, which allows binary redistributions without the source code, many components are reused in proprietary and corporate-sponsored software projects. The firewall code in Apple's macOS is based on OpenBSD's PF firewall code,[6] Android's Bionic C standard library is based on OpenBSD code,[7] LLVM uses OpenBSD's regular expression library,[8] and Windows 10 uses OpenSSH (OpenBSD Secure Shell) with LibreSSL.[9]
The word "open" in the name OpenBSD refers to the availability of the operating system source code on the Internet, although the word "open" in the name OpenSSH means "OpenBSD". It also refers to the wide range of hardware platforms the system supports.[10] OpenBSD supports a variety of system architectures including x86-64, IA-32, ARM, PowerPC, and 64-bit RISC-V. Its default GUI is FVWM on X11.
History
In December 1994, Theo de Raadt, a founding member of the NetBSD project, was asked to resign from the NetBSD core team over disagreements and conflicts with the other members of the NetBSD team.[11][4] In October 1995, de Raadt founded OpenBSD, a new project forked from NetBSD 1.0. The initial release, OpenBSD 1.2, was made in July 1996, followed by OpenBSD 2.0 in October of the same year.[12] Since then, the project has issued a release every six months, each of which is supported for one year.
On 25 July 2007, OpenBSD developer Bob Beck announced the formation of the OpenBSD Foundation, a Canadian non-profit organization formed to "act as a single point of contact for persons and organizations requiring a legal entity to deal with when they wish to support OpenBSD."[13]
In 2024, the project had separated far enough that all files which were part of the original fork from NetBSD had been either modified or removed, with the replacement of a data file for the "quiz" program being the determining change.[14]
Usage statistics
It is hard to determine how widely OpenBSD is used, because the developers do not publish or collect usage statistics.
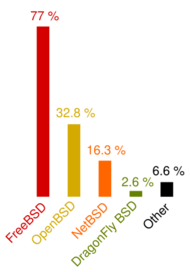
In September 2005, the BSD Certification Group surveyed 4330 individual BSD users, showing that 32.8% used OpenBSD,[15] behind FreeBSD with 77%, ahead of NetBSD with 16.3% and DragonFly BSD with 2.6%[note 1]. However, the authors of this survey clarified that it is neither "exhaustive" nor "completely accurate", since the survey was spread mainly through mailing lists, forums and word of mouth. This combined with other factors, like the lack of a control group, a pre-screening process or significant outreach outside of the BSD community, makes the survey unreliable for judging BSD usage globally.
Uses
Network appliances
OpenBSD features a robust TCP/IP networking stack, and can be used as a router[16] or wireless access point.[17] OpenBSD's security enhancements, built-in cryptography, and packet filter make it suitable for security purposes such as firewalls,[18] intrusion-detection systems, and VPN gateways.
Several proprietary systems are based on OpenBSD, including devices from Armorlogic (Profense web application firewall), Calyptix Security,[19] GeNUA,[20] RTMX,[21] and .vantronix.[22]
Other operating systems
Some versions of Microsoft's Windows Services for UNIX, an extension to the Windows operating system to provide Unix-like functionality, used much of the OpenBSD code base that is included in the Interix interoperability suite,[23][24] developed by Softway Systems Inc., which Microsoft acquired in 1999.[25][26] Core Force, a security product for Windows, is based on OpenBSD's pf firewall.[27] The pf firewall is also found in other operating systems: including FreeBSD,[28] and macOS.[29]
Personal computers
OpenBSD ships with Xenocara,[30] an implementation of the X Window System, and is suitable as a desktop operating system for personal computers, including laptops.[31][32]: xl As of September 2018[update], OpenBSD includes approximately 8000 packages in its software repository,[33] including desktop environments such as Lumina, GNOME, KDE Plasma, and Xfce, and web browsers such as Firefox and Chromium.[34] The project also includes three window managers in the main distribution: cwm, FVWM (part of the default configuration for Xenocara), and twm.[35]
Servers
OpenBSD features a full server suite and can be configured as a mail server, web server, FTP server, DNS server, router, firewall, NFS file server, or any combination of these. Since version 6.8, OpenBSD has also shipped with native in-kernel WireGuard support.[36][37]
Security

Shortly after OpenBSD was created, de Raadt was contacted by a local security software company named Secure Networks (later acquired by McAfee).[38][39] The company was developing a network security auditing tool called Ballista,[note 2] which was intended to find and exploit software security flaws. This coincided with de Raadt's interest in security, so the two cooperated leading up to the release of OpenBSD 2.3.[40] This collaboration helped to define security as the focus of the OpenBSD project.[41]
OpenBSD includes numerous features designed to improve security, such as:
- Secure alternatives to POSIX functions in the C standard library, such as
strlcatforstrcatandstrlcpyforstrcpy[42] - Toolchain alterations, including a static bounds checker[43]
- Memory protection techniques to guard against invalid accesses, such as ProPolice and the W^X page protection feature
- Strong cryptography and randomization[44]
- System call and filesystem access restrictions to limit process capabilities[45]
To reduce the risk of a vulnerability or misconfiguration allowing privilege escalation, many programs have been written or adapted to make use of privilege separation, privilege revocation and chrooting. Privilege separation is a technique, pioneered on OpenBSD and inspired by the principle of least privilege, where a program is split into two or more parts, one of which performs privileged operations and the other—almost always the bulk of the code—runs without privilege.[46] Privilege revocation is similar and involves a program performing any necessary operations with the privileges it starts with then dropping them. Chrooting involves restricting an application to one section of the file system, prohibiting it from accessing areas that contain private or system files. Developers have applied these enhancements to OpenBSD versions of many common applications, such as tcpdump, file, tmux, smtpd, and syslogd.[47]
OpenBSD developers were instrumental in the creation and development of OpenSSH (aka OpenBSD Secure Shell), which is developed in the OpenBSD CVS repositories. OpenBSD Secure Shell is based on the original SSH.[48] It first appeared in OpenBSD 2.6 and is now by far the most popular SSH client and server, available on many operating systems.[49]
The project has a policy of continually auditing source code for problems, work that developer Marc Espie has described as "never finished ... more a question of process than of a specific bug being hunted." He went on to list several typical steps once a bug is found, including examining the entire source tree for the same and similar issues, "try[ing] to find out whether the documentation ought to be amended", and investigating whether "it's possible to augment the compiler to warn against this specific problem."[50]
Security record
The OpenBSD website features a prominent reference to the system's security record. Until June 2002, it read:
| “ | Five years without a remote hole in the default install! | ” |
In June 2002, Mark Dowd of Internet Security Systems disclosed a bug in the OpenSSH code implementing challenge–response authentication.[51] This vulnerability in the OpenBSD default installation allowed an attacker remote access to the root account, which was extremely serious not only to OpenBSD, but also to the large number of other operating systems that were using OpenSSH by that time.[52] This problem necessitated the adjustment of the slogan on the OpenBSD website to:
| “ | One remote hole in the default install, in nearly 6 years! | ” |
The quote remained unchanged as time passed, until on 13 March 2007, when Alfredo Ortega of Core Security Technologies disclosed a network-related remote vulnerability.[53] The quote was subsequently changed to:
| “ | Only two remote holes in the default install, in a heck of a long time! | ” |
This statement has been criticized because the default install contains few running services, and many use cases require additional services.[54] Also, because the ports tree contains unaudited third-party software, it is easy for users to compromise security by installing or improperly configuring packages. However, the project maintains that the slogan is intended to refer to a default install and that it is correct by that measure.
One of the fundamental ideas behind OpenBSD is a drive for systems to be simple, clean, and secure by default. The default install is quite minimal, which the project states is to ensure novice users "do not need to become security experts overnight",[55] which fits with open-source and code auditing practices considered important elements of a security system.[56] Additional services are to be enabled manually to make users think of the security implications first.
Alleged backdoor
On 11 December 2010, Gregory Perry, a former technical consultant for the Federal Bureau of Investigation (FBI), emailed de Raadt alleging that the FBI had paid some OpenBSD ex-developers 10 years prior to insert backdoors into the OpenBSD Cryptographic Framework. De Raadt made the email public on 14 December by forwarding it to the openbsd-tech mailing list and suggested an audit of the IPsec codebase.[57][58] De Raadt's response was skeptical of the report and he invited all developers to independently review the relevant code. In the weeks that followed, bugs were fixed but no evidence of backdoors was found.[59] De Raadt stated "I believe that NetSec was probably contracted to write backdoors as alleged. If those were written, I don't believe they made it into our tree. They might have been deployed as their own product."[60]
Criticisms
In December 2017, Ilja van Sprundel, director at IOActive, gave a talk at the CCC[61] as well as DEF CON,[62] entitled "Are all BSDs created equally? — A survey of BSD kernel vulnerabilities", in which he stated that although OpenBSD was the clear winner of the BSDs in terms of security, "Bugs are still easy to find in those kernels, even in OpenBSD".
Two years later, in 2019, an anonymous critic called "Stein" gave a talk named "A systematic evaluation of OpenBSD's mitigations"[63] at the CCC. While admitting OpenBSD has some effective mitigations, he alleged a significant number were "useless at best and based on pure luck and superstition".[64]
Subprojects
Many open source projects started as components of OpenBSD, including:
- bioctl, a generic RAID management interface similar to ifconfig
- CARP, a free alternative to Cisco's patented HSRP/VRRP redundancy protocols
- cwm, a stacking window manager
- doas, a replacement for sudo
- OpenBSD httpd,[65][66] an implementation of httpd
- Game of Trees, an implementation of Git's formats and protocols[67]
- hw.sensors, a sensors framework used by over 100 drivers
- LibreSSL, an implementation of the SSL and TLS protocols, forked from OpenSSL 1.0.1g[68]
- mandoc, a utility used for formatting man pages
- OpenBGPD, an implementation of BGP-4[69]
- OpenIKED, an implementation of IKEv2[70]
- OpenNTPD, a simpler alternative to ntp.org's NTP daemon[71]
- OpenOSPFD, an implementation of OSPF[69]
- OpenSMTPD, an SMTP daemon with IPv4/IPv6, PAM, Maildir, and virtual domains support[72]
- OpenSSH, an implementation of SSH[73]
- PF, an IPv4/IPv6 stateful firewall with NAT, PAT, QoS and traffic normalization support
- pfsync, a firewall state synchronization protocol for PF with high availability support using CARP
- rpki-client, implementation of the Resource Public Key Infrastructure (RPKI) for Relying Parties (RP) to facilitate validation of BGP announcements[74]
- sndio, a compact audio and MIDI framework
- spamd, a spam filter with greylisting support designed to inter-operate with PF
- Xenocara, a customized X.Org build infrastructure[30]
Some subsystems have been integrated into other BSD operating systems,[75][76][77] and many are available as packages for use in other Unix-like systems.[78][79][80]
The Calgary Internet Exchange was formed in 2012, in part to serve the needs of the OpenBSD project.[81]
In 2017, Isotop,[82] a French project aiming to adapt OpenBSD to desktops and laptops, using xfce then dwm, started to be developed.[83]
Third-party components
OpenBSD includes a number of third-party components, many with OpenBSD-specific patches,[34] such as X.Org, Clang[84] (the default compiler on several architectures), GCC,[43][note 3] Perl, NSD, Unbound, ncurses, GNU binutils, GDB, and AWK.
Development

Development is continuous, and team management is open and tiered. Anyone with appropriate skills may contribute, with commit rights being awarded on merit and de Raadt acting as coordinator.[32]: xxxv Two official releases are made per year, with the version number incremented by 0.1,[85] and these are each supported for twelve months (two release cycles).[86] Snapshot releases are also available at frequent intervals.
Maintenance patches for supported releases may be applied using syspatch, manually or by updating the system against the patch branch of the CVS source repository for that release.[87] Alternatively, a system administrator may opt to upgrade to the next snapshot release using sysupgrade, or by using the -current branch of the CVS repository, in order to gain pre-release access to recently added features. The sysupgrade tool can also upgrade to the latest stable release version.
The generic OpenBSD kernel provided by default is strongly recommended for end users, in contrast to operating systems that recommend user kernel customization.[88]
Packages outside the base system are maintained by CVS through a ports tree and are the responsibility of the individual maintainers, known as porters. As well as keeping the current branch up to date, porters are expected to apply appropriate bug-fixes and maintenance fixes to branches of their package for OpenBSD's supported releases. Ports are generally not subject to the same continuous auditing as the base system due to lack of manpower.
Binary packages are built centrally from the ports tree for each architecture. This process is applied for the current version, for each supported release, and for each snapshot. Administrators are recommended to use the package mechanism rather than build the package from the ports tree, unless they need to perform their own source changes.
OpenBSD's developers regularly meet at special events called hackathons,[89] where they "sit down and code", emphasizing productivity.[90]
Most new releases include a song.[91]
Open source and open documentation
OpenBSD is known for its high-quality documentation.[92][93]
When OpenBSD was created, de Raadt decided that the source code should be available for anyone to read. At the time, a small team of developers generally had access to a project's source code.[94] Chuck Cranor[95] and de Raadt concluded this practice was "counter to the open source philosophy" and inconvenient to potential contributors. Together, Cranor and de Raadt set up the first public, anonymous revision control system server. De Raadt's decision allowed users to "take a more active role", and established the project's commitment to open access.[94] OpenBSD is notable for its continued use of CVS (more precisely an unreleased, OpenBSD-managed fork named OpenCVS that was stated "OpenCVS released soon." in 2005[96] and in 2025 "OpenCVS is to be released soon."[97] though OpenBSD also has a webpage that describes OpenCVS.[98]), when most other projects that used it have migrated to other systems.[99]
OpenBSD does not include closed source binary drivers in the source tree, nor does it include code requiring the signing of non-disclosure agreements.[100]
Since OpenBSD is based in Canada, no United States export restrictions on cryptography apply, allowing the distribution to make full use of modern algorithms for encryption. For example, the swap space is divided into small sections and each section is encrypted with its own key, ensuring that sensitive data does not leak into an insecure part of the system.[18]
OpenBSD randomizes various behaviors of applications, making them less predictable and thus more difficult to attack. For example, PIDs are created and associated randomly to processes; the bind system call uses random port numbers; files are created with random inode numbers; and IP datagrams have random identifiers.[101] This approach also helps expose bugs in the kernel and in user space programs.
The OpenBSD policy on openness extends to hardware documentation: in the slides for a December 2006 presentation, de Raadt explained that without it "developers often make mistakes writing drivers", and pointed out that "the [oh my god, I got it to work] rush is harder to achieve, and some developers just give up."[102] He went on to say that vendor-supplied binary drivers are unacceptable for inclusion in OpenBSD, that they have "no trust of vendor binaries running in our kernel" and that there is "no way to fix [them] ... when they break."[102]
Closed source and proprietary code
In an interview with Jeremy Andrews after being asked "What is it about binary firmware that you're willing to ship it, versus binary blobs? How can you trust the firmware binary to do what it should do? And what if the firmware has a bug?" Theo de Raadt in part stated "Quite honestly I prefer chips which have no firmware, and instead use correctly designed hardware logic, which our driver must then drive." and "But in the end, if we wish to support any such devices, we must be practical. We must accept the risk that there is a flaw in the firmware."[85]
OpenBSD's GitHub mirror has licenses for firmware that forbids use in non-TI devices[103], forbid reverse engineering, decompilation, or disassembly of some software[104][105][106], firmware that is only allowed to be redistributed in object code only,[107], has no copyright notice in the original file[108], or where OpenBSD developers believe the original license on the source did specifically allow re-distribution.[109]
According to the GNU Project, OpenBSD includes small "blobs" of proprietary object code as device firmware or loaded by freely licensed drivers.[110]
Licensing
OpenBSD maintains a strict license policy,[3] preferring the ISC license and other variants of the BSD license. The project attempts to "maintain the spirit of the original Berkeley Unix copyrights," which permitted a "relatively un-encumbered Unix source distribution."[3] The widely used Apache License and GNU General Public License are considered overly restrictive.[111]
In June 2001, triggered by concerns over Darren Reed's modification of IPFilter's license wording, a systematic license audit of the OpenBSD ports and source trees was undertaken.[112] Code in more than a hundred files throughout the system was found to be unlicensed, ambiguously licensed or in use against the terms of the license. To ensure that all licenses were properly adhered to, an attempt was made to contact all the relevant copyright holders: some pieces of code were removed, many were replaced, and others, such as the multicast routing tools mrinfo and map-mbone, were relicensed so that OpenBSD could continue to use them.[113][114] Also removed during this audit was all software produced by Daniel J. Bernstein. At the time, Bernstein requested that all modified versions of his code be approved by him prior to redistribution, a requirement to which OpenBSD developers were unwilling to devote time or effort.[115][116][117]
Because of licensing concerns, the OpenBSD team has reimplemented software from scratch or adopted suitable existing software. For example, OpenBSD developers created the PF packet filter after unacceptable restrictions were imposed on IPFilter. PF first appeared in OpenBSD 3.0[118] and is now available in many other operating systems.[119] OpenBSD developers have also replaced GPL-licensed tools (such as CVS and pkg-config) with permissively licensed equivalents.[120][121]
Funding
Although the operating system and its portable components are used in commercial products, de Raadt says that little of the funding for the project comes from the industry: "traditionally all our funding has come from user donations and users buying our CDs (our other products don't really make us much money). Obviously, that has not been a lot of money."[85]
For a two-year period in the early 2000s, the project received funding from DARPA, which "paid the salaries of 5 people to work completely full-time, bought about $30k in hardware, and paid for 3 hackathons", from the POSSE project.[85]
In 2006, the OpenBSD project experienced financial difficulties.[122] The Mozilla Foundation[123] and GoDaddy[124] are among the organizations that helped OpenBSD to survive. However, de Raadt expressed concern about the asymmetry of funding: "I think that contributions should have come first from the vendors, secondly from the corporate users, and thirdly from individual users. But the response has been almost entirely the opposite, with almost a 15-to-1 dollar ratio in favor of the little people. Thanks a lot, little people!"[85]
On 14 January 2014, Bob Beck issued a request for funding to cover electrical costs. If sustainable funding was not found, Beck suggested the OpenBSD project would shut down.[125] The project soon received a US$20,000 donation from Mircea Popescu, the Romanian creator of the MPEx bitcoin stock exchange, paid in bitcoins.[126] The project raised US$150,000[127] in response to the appeal, enabling it to pay its bills and securing its short-term future.[126]
OpenBSD Foundation
| Formation | July 25, 2007 |
|---|---|
| Founder | OpenBSD developers |
| Legal status | Nonprofit organization |
| Location |
|
| Website | www |
The OpenBSD Foundation is a Canadian federal non-profit organization founded by the OpenBSD project as a "single point of contact for persons and organizations requiring a legal entity to deal with when they wish to support OpenBSD."[128] It was announced to the public by OpenBSD developer Bob Beck on 25 July 2007. It also serves as a legal safeguard over other projects which are affiliated with OpenBSD, including OpenSSH, OpenBGPD, OpenNTPD, OpenCVS, OpenSMTPD and LibreSSL.[129]
Since 2014, several large contributions to the OpenBSD Foundation have come from corporations such as Microsoft,[130] Facebook, and Google as well as the Core Infrastructure Initiative.[131]
In 2015, Microsoft became the foundation's first gold level contributor,[132] donating between $25,000-50,000 to support development of OpenSSH, which had been integrated into PowerShell in July, and later into Windows Server in 2018.[133] Other contributors include Google, Facebook and DuckDuckGo.[134]
During the 2016 and 2017 fundraising campaigns, Smartisan, a Chinese company, was the leading financial contributor to the OpenBSD Foundation.[135][136]
Distribution
OpenBSD is freely available in various ways: the source can be retrieved by anonymous CVS,[137] binary releases and development snapshots can be downloaded by FTP, HTTP, and rsync.[138] Prepackaged CD-ROM sets through version 6.0 can be ordered online for a small fee, complete with an assortment of stickers and a copy of the release's theme song. These, with their artwork and other bonuses, have been one of the project's few sources of income, funding hardware, Internet service, and other expenses.[139] Beginning with version 6.1, CD-ROM sets are no longer released.
OpenBSD provides a package management system, referred to as pkg* tools, for easy installation and management of programs which are not part of the base operating system.[140] Packages are binary files which are extracted, managed and removed using the package tools. On OpenBSD, the source of packages is the ports system, a collection of makefiles and other infrastructure required to create packages. In OpenBSD, the ports and base operating system are developed and released together for each version: this means that the ports or packages released with, for example, 4.6 are not suitable for use with 4.5 and vice versa.[140]
Songs and artwork

Initially, OpenBSD used a haloed version of the BSD daemon mascot drawn by Erick Green, who was asked by de Raadt to create the logo for the 2.3 and 2.4 versions of OpenBSD. Green planned to create a full daemon, including head and body, but only the head was completed in time for OpenBSD 2.3. The body as well as pitchfork and tail was completed for OpenBSD 2.4.[141]
Subsequent releases used variations such as a police daemon by Ty Semaka,[142] but eventually settled on a pufferfish named Puffy.[143] Since then, Puffy has appeared on OpenBSD promotional material and featured in release songs and artwork.
The promotional material of early OpenBSD releases did not have a cohesive theme or design, but later the CD-ROMs, release songs, posters and tee-shirts for each release have been produced with a single style and theme, sometimes contributed to by Ty Semaka of the Plaid Tongued Devils.[91] These have become a part of OpenBSD advocacy, with each release expounding a moral or political point important to the project, often through parody.[144]
Themes have included Puff the Barbarian in OpenBSD 3.3, which included an 80s rock song and parody of Conan the Barbarian alluding to open documentation,[91] The Wizard of OS in OpenBSD 3.7, related to the project's work on wireless drivers, and Hackers of the Lost RAID, a parody of Indiana Jones referencing the new RAID tools in OpenBSD 3.8.
Releases
The following table summarizes the version history of the OpenBSD operating system. {{{2}}}
| Version | Release date | Supported until | Significant changes |
|---|---|---|---|
| 1.1 | 18 October 1995 | ||
| 1.2 | 1 July 1996 |
| |
| 2.0 | 1 October 1996 | ||
| 2.1 | 1 June 1997 | Replacement of the older sh with pdksh.[148] | |
| 2.2 | 1 December 1997 | Addition of the afterboot(8) man page.[149]
| |
| 2.3 | 19 May 1998 | Introduced the haloed daemon, or aureola beastie, in head-only form created by Erick Green.[150] | |
| 2.4 | 1 December 1998 | Featured the complete haloed daemon, with trident and a finished body.[151] | |
| 2.5 | 19 May 1999 | Introduced the Cop daemon image done by Ty Semaka.[152] | |
| 2.6 | 1 December 1999 | Based on the original SSH suite and developed further by the OpenBSD team, 2.6 saw the first release of OpenSSH, which is now available standard on most Unix-like operating systems and is the most widely used SSH suite.[153] | |
| 2.7 | 15 June 2000 | Support for SSH2 added to OpenSSH.[154] | |
| 2.8 | 1 December 2000 | isakmpd(8)[155]
| |
| 2.9 | 1 June 2001 |
Filesystem performance increases from softupdates and dirpref code.[156] | |
| 3.0 | 1 December 2001 |
E-Railed (OpenBSD Mix),[157] a techno track performed by the release mascot Puff Daddy, the famed rapper and political icon.
| |
| 3.1 | 19 May 2002 | Systemagic,[158] where Puffy, the Kitten Slayer, battles evil script kitties. Inspired by the works of Rammstein and a parody of Buffy the Vampire Slayer.
| |
| 3.2 | 1 November 2002 | Goldflipper,[160] a tale in which James Pond, agent 077, super spy and suave lady's man, deals with the dangers of a hostile internet. Styled after the orchestral introductory ballads of James Bond films. | |
| 3.3 | 1 May 2003 |
Puff the Barbarian,[161] born in a tiny bowl; Puff was a slave, now he hacks through the C, searching for the Hammer. It is an 80s rock-style song and parody of Conan the Barbarian dealing with open documentation.
| |
| 3.4 | 1 November 2003 |
The Legend of Puffy Hood where Sir Puffy of Ramsay,[162] a freedom fighter who, with Little Bob of Beckley, took from the rich and gave to all. Tells of the POSSE project's cancellation. An unusual blend of both hip-hop and medieval-style music, a parody of the tale of Robin Hood intended to express OpenBSD's attitude to free speech.
| |
| 3.5 | 1 May 2004 |
CARP License and Redundancy must be free,[166] where a fish seeking to license his free redundancy protocol, CARP, finds trouble with the red tape. A parody of the Fish Licence skit and Eric the Half-a-Bee Song by Monty Python, with an anti-software patents message.
| |
| 3.6 | 1 November 2004 |
Pond-erosa Puff (live) was the tale of Pond-erosa Puff,[173] a no-guff freedom fighter from the wild west, set to hang a lickin' on no-good bureaucratic nerds who encumber software with needless words and restrictions. The song was styled after the works of Johnny Cash, a parody of the Spaghetti Western and Clint Eastwood and inspired by liberal license enforcement.
| |
| 3.7 | 19 May 2005 | The Wizard of OS,[176] where Puffathy, a little Alberta girl, must work with Taiwan to save the day by getting unencumbered wireless. This release was styled after the works of Pink Floyd and a parody of The Wizard of Oz; this dealt with wireless hacking.[177] | |
| 3.8 | 1 November 2005 | 1 November 2006 | |
| 3.9 | 1 May 2006 | 1 May 2007 |
Attack of the Binary BLOB,[179] which chronicles the developer's fight against binary blobs and vendor lock-in,[180] a parody of the 1958 film The Blob and the pop-rock music of the era. |
| 4.0 | 1 November 2006 | 1 November 2007 | Humppa Negala,[181] a Hava Nagilah parody with a portion of Entrance of the Gladiators and Humppa music fused together, with no story behind it, simply a homage to one of the OpenBSD developers' favorite genres of music.[182] |
| 4.1 | 1 May 2007 | 1 May 2008 | Puffy Baba and the 40 Vendors,[184] a parody of the Arabic fable Ali Baba and the Forty Thieves, part of the book of One Thousand and One Nights, in which Linux developers are mocked over their allowance of non-disclosure agreements when developing software while at the same time implying hardware vendors are criminals for not releasing documentation required to make reliable device drivers.[185]
|
| 4.2 | 1 November 2007 | 1 November 2008 | 100001 1010101,[188] the Linux kernel developers gets a knock for violating the ISC-style license of OpenBSD's open hardware abstraction layer for Atheros wireless cards.
|
| 4.3 | 1 May 2008 | 1 May 2009 | Home to Hypocrisy[190][191] |
| 4.4 | 1 November 2008 | 18 October 2009 |
Trial of the BSD Knights,[192] summarizes the history of BSD including the USL v. BSDi lawsuit. The song was styled after the works of Star Wars.
|
| 4.5 | 1 May 2009 | 19 May 2010 | Games. It was styled after the works of Tron.[195]
|
| 4.6 | 18 October 2009 | 1 November 2010 | Planet of the Users.[198] In the style of Planet of the Apes, Puffy travels in time to find a dumbed-down dystopia, where "one very rich man runs the earth with one multinational". Open-source software has since been replaced by one-button computers, one-channel televisions, and closed-source software which, after you purchase it, becomes obsolete before you have a chance to use it. People subsist on soylent green. The theme song is performed in the reggae rock style of The Police.
|
| 4.7 | 19 May 2010 | 1 May 2011 | I'm Still Here [199] |
| 4.8 | 1 November 2010 | 1 November 2011 | El Puffiachi.[200][201]
|
| 4.9 | 1 May 2011 | 1 May 2012 | The Answer.[202]
|
| 5.0 | 1 November 2011 | 1 November 2012 | What Me Worry?.[203] |
| 5.1 | 1 May 2012 | 1 May 2014 | Bug Busters. The song was styled after the works of Ghostbusters.[204] |
| 5.2 | 1 November 2012 | 1 November 2013 | Aquarela do Linux.[205]
|
| 5.3 | 1 May 2013 | 1 May 2014 | Blade Swimmer. The song was styled after the works of Roy Lee, a parody of Blade Runner.[206]
|
| 5.4 | 1 November 2013 | 1 November 2014 | Our favorite hacks, a parody of My Favorite Things.[207] |
| 5.5 | 1 May 2014 | 1 May 2015 | Wrap in Time.[208]
|
| 5.6 | 1 November 2014 | 18 October 2015 | Ride of the Valkyries.[209]
|
| 5.7 | 1 May 2015 | 29 March 2016 | Source Fish.[210]
|
| 5.8 | 18 October 2015 | 1 September 2016 | 20 years ago today, Fanza, So much better, A Year in the Life.[211] (20th anniversary release[212])
|
| 5.9 | 29 March 2016 | 11 April 2017 | Doctor W^X, Systemagic (Anniversary Edition).[213]
|
| 6.0 | 1 September 2016 | 9 October 2017 | Another Smash of the Stack, Black Hat, Money, Comfortably Dumb (the misc song), Mother, Goodbye and Wish you were Secure, Release songs parodies of Pink Floyd's The Wall, Comfortably Numb and Wish You Were Here.[214] |
| 6.1 | 11 April 2017 | 15 April 2018 | Winter of 95, a parody of Summer of '69.[217]
|
| 6.2 | 9 October 2017 | 18 October 2018 | A three-line diff[218]
|
| 6.3 | 2 April 2018 | 3 May 2019 |
|
| 6.4 | 18 October 2018 | 17 October 2019 |
|
| 6.5 | 24 April 2019 | 19 May 2020 |
|
| 6.6 | 17 October 2019 | 18 October 2020 |
|
| 6.7 | 19 May 2020 | 1 May 2021 |
|
| 6.8 | 18 October 2020 | 14 October 2021 |
|
| 6.9 | 1 May 2021 | 21 April 2022[note 5] |
|
| 7.0 | 14 October 2021 | 20 October 2022[note 5] | |
| 7.1 | 21 April 2022 | 10 April 2023[note 5] | |
| 7.2 | 20 October 2022 | 16 October 2023[note 5] |
|
| 7.3 | 10 April 2023 | 5 April 2024[note 5] |
|
| 7.4 | 16 October 2023 | 8 October 2024[note 5] |
|
| 7.5 | 5 April 2024 | 28 April 2025[note 5] |
|
| 7.6 | 8 October 2024 | 22 October 2025[note 5] |
|
| 7.7 | 28 April 2025 | May 2026[note 5] |
|
| 7.8 | 22 October 2025 | Oct 2026[note 5] |
|
See also
- Comparison of BSD operating systems
- Comparison of open-source operating systems
- KAME project, responsible for OpenBSD's IPv6 support
- OpenBSD Journal
- OpenBSD security features
- Unix security
Notes
- ↑ 1.0 1.1 Multiple selections were permitted as users may use multiple BSD variants side by side.
- ↑ Later renamed to Cybercop Scanner after SNI was purchased by Network Associates.
- ↑ As of OpenBSD 6.3[update], either Clang 5.0.1, GCC 4.2.1 or GCC 3.3.6 is shipped, depending on the platform.[84][43]
- ↑ Compare release history of NetBSD, which OpenBSD branched from
- ↑ 5.00 5.01 5.02 5.03 5.04 5.05 5.06 5.07 5.08 5.09 OpenBSD is released roughly every 6 months targeting May and November and only the latest two releases receive security and reliability fixes for the base system.[223]
References
- ↑ "Package Management". OpenBSD Frequently Asked Questions. https://www.openbsd.org/faq/faq15.html#PkgMgmt.
- ↑ "OpenBSD Platforms". OpenBSD. https://www.openbsd.org/plat.html.
- ↑ 3.0 3.1 3.2 "Copyright Policy". OpenBSD. http://www.openbsd.org/policy.html.
- ↑ 4.0 4.1 de Raadt, Theo (29 March 2009). "Archive of the mail conversation leading to Theo de Raadt's departure". http://www.theos.com/deraadt/coremail.html.
- ↑ OpenBSD Project (19 May 2020). "OpenBSD". https://www.openbsd.org/.
- ↑ "Murus App, Apple PF for macOS from OpenBSD". https://murusfirewall.com/murus/.
- ↑ "Android's C Library Has 173 Files of Unchanged OpenBSD Code". http://undeadly.org/cgi?action=article&sid=20140506132000.
- ↑ "LLVM Release License". http://releases.llvm.org/7.0.0/LICENSE.TXT.
- ↑ "OpenSSH for Windows". https://twitter.com/nocentino/status/996843655112613888.
- ↑ Grimes, Roger A. (29 December 2006). "New year's resolution No. 1: Get OpenBSD". InfoWorld. http://www.infoworld.com/article/2659465/security/new-year-s-resolution-no--1--get-openbsd.html.
- ↑ Glass, Adam (23 December 1994). "Theo De Raadt". netbsd-users (Mailing list). Archived from the original on 14 October 2017. Retrieved 10 January 2006.
- ↑ De Raadt, Theo (18 October 1996). "The OpenBSD 2.0 release". openbsd-announce (Mailing list). Archived from the original on 4 February 2017. Retrieved 15 May 2016.
- ↑ "Announcing – The OpenBSD Foundation". OpenBSD Journal. 26 July 2007. http://undeadly.org/cgi?action=article&sid=20070726015128.
- ↑ "'CVS: cvs.openbsd.org: src' - MARC". https://marc.info/?l=openbsd-cvs&m=172443408727088&w=2.
- ↑ 15.0 15.1 BSD Usage Survey (Report). The BSD Certification Group. 31 October 2005. p. 9. http://www.bsdcertification.org/downloads/pr-20051031-usage-survey-en-en.pdf. Retrieved 16 September 2012.
- ↑ "OpenBSD PF - Building a Router". https://www.openbsd.org/faq/pf/example1.html.
- ↑ "Building an OpenBSD wireless access point". https://ctors.net/2013/12/30/openbsd_wireless_access_point.
- ↑ 18.0 18.1 McIntire, Tim (8 August 2006). "Take a closer look at OpenBSD". Developerworks. IBM. http://www.ibm.com/developerworks/aix/library/au-openbsd.html.
- ↑ "AccessEnforcer Model AE800". Calyptix Security. http://www.calyptix.com/products/models/ae800/.
- ↑ "High Resistance Firewall genugate". GeNUA. https://www.genua.de/en/products/high-resistance-firewall-genugate.html.
- ↑ "RTMX O/S IEEE Real Time POSIX Operating Systems". RTMX. http://www.rtmx.com/. "RTMX O/S is a product extension to OpenBSD Unix-like operating system with emphasis on embedded, dedicated applications."
- ↑ ".vantronix secure system". Compumatica secure networks. http://www.vantronix.com/. "The Next Generation Firewall is not a standalone device, it is a Router for operation in security critical environments with high requirements for availability, comprehensive support as well as reliable and trusted systems powered by OpenBSD."
- ↑ Dohnert, Roberto J. (21 January 2004), "Review of Windows Services for UNIX 3.5", OSNews (David Adams), http://www.osnews.com/story/5751
- ↑ Reiter, Brian (26 January 2010). "WONTFIX: select(2) in SUA 5.2 ignores timeout". brianreiter.org. https://brianreiter.org/2010/01/26/wontfix-select2-in-sua-5-2-ignores-timeout/.
- ↑ "Microsoft Acquires Softway Systems To Strengthen Future Customer Interoperability Solutions", Microsoft News Center (Microsoft), 17 September 1999, http://www.microsoft.com/en-us/news/press/1999/sept99/softwaypr.aspx, retrieved 19 June 2012
- ↑ "Milltech Consulting Inc.". 2019. https://www.milltech.com/about.
- ↑ "Core Force", Core Labs, http://corelabs.coresecurity.com/index.php?module=Wiki&action=view&type=project&name=Core_Force, retrieved 13 December 2011, "CORE FORCE provides inbound and outbound stateful packet filtering for TCP/IP protocols using a Windows port of OpenBSD's PF firewall, granular file system and registry access control and programs' integrity validation."
- ↑ "Chapter 31. Firewalls". https://docs.freebsd.org/en/books/handbook/firewalls/.
- ↑ "pf.c". https://opensource.apple.com/source/xnu/xnu-1456.1.26/bsd/net/pf.c.auto.html.
- ↑ 30.0 30.1 "About Xenocara". Xenocara. https://xenocara.org/.
- ↑ Tzanidakis, Manolis (21 April 2006). "Using OpenBSD on the desktop". Linux.com. http://archive09.linux.com/articles/52930.
- ↑ 32.0 32.1 Lucas, Michael W. (April 2013). Absolute OpenBSD: Unix for the Practical Paranoid (2nd ed.). San Francisco, California: No Starch Press. ISBN 978-1-59327-476-4. https://www.nostarch.com/obenbsd2e. Retrieved 28 May 2016.
- ↑ "OpenPorts.se Statistics". OpenPorts.se. http://openports.se/statistics.php.
- ↑ 34.0 34.1 "OpenBSD 6.0". OpenBSD. https://www.openbsd.org/59.html.
- ↑ "The X Windows System". OpenBSD Frequently Asked Questions. http://www.openbsd.org/faq/faq11.html. "OpenBSD ships with the cwm(1), fvwm(1) and twm(1) window managers, [...]"
- ↑ "OpenBSD 6.8". https://www.openbsd.org/68.html.
- ↑ "WireGuard imported into OpenBSD". https://undeadly.org/cgi?action=article;sid=20200622052207.
- ↑ Varghese, Sam (8 October 2004). "Staying on the cutting edge". The Age. http://www.theage.com.au/articles/2004/10/07/1097089476287.html.
- ↑ Laird, Cameron; Staplin, George Peter (17 July 2003). "The Essence of OpenBSD". ONLamp. http://www.onlamp.com/pub/a/bsd/2003/07/17/openbsd_core_team.html.
- ↑ De Raadt, Theo (19 December 2005). "2.3 release announcement". openbsd-misc (Mailing list).
Without [SNI's] support at the right time, this release probably would not have happened.
- ↑ Wayner, Peter (13 July 2000). "18.3 Flames, Fights, and the Birth of OpenBSD". Free For All: How Linux and the Free Software Movement Undercut the High Tech Titans (1st ed.). HarperBusiness. ISBN 978-0-06-662050-3. http://www.jus.uio.no/sisu/free_for_all.peter_wayner/index.html. Retrieved 13 December 2011.
- ↑ Miller, Todd C.; De Raadt, Theo (6 June 1999). "strlcpy and strlcat - Consistent, Safe, String Copy and Concatenation". USENIX Annual Technical Conference. Monterey, California. http://www.usenix.org/events/usenix99/millert.html. Retrieved 13 December 2011.
- ↑ 43.0 43.1 43.2 "gcc-local – local modifications to gcc". OpenBSD manual pages. http://man.openbsd.org/OpenBSD-6.0/man1/gcc-local.1.
- ↑ De Raadt, Theo; Hallqvist, Niklas; Grabowski, Artur; Keromytis, Angelos D.; Provos, Niels (6 June 1999). "Cryptography in OpenBSD: An Overview". USENIX Annual Technical Conference. Monterey, California. https://www.usenix.org/legacy/publications/library/proceedings/usenix99/deraadt.html. Retrieved 27 May 2016.
- ↑ "Pledge() - A New Mitigation Mechanism". https://www.openbsd.org/papers/hackfest2015-pledge/mgp00002.html.
- ↑ Provos, Niels (9 August 2003). "Privilege Separated OpenSSH". http://www.citi.umich.edu/u/provos/ssh/privsep.html.
- ↑ "Innovations". https://www.openbsd.org/innovations.html. "Privilege separation: [...] The concept is now used in many OpenBSD programs, for example [...] etc."
- ↑ "Project History and Credits". OpenSSH. http://www.openssh.com/history.html.
- ↑ "SSH usage profiling". OpenSSH. http://www.openssh.com/usage/.
- ↑ Biancuzzi, Federico (18 March 2004). "An Interview with OpenBSD's Marc Espie". ONLamp. http://www.onlamp.com/pub/a/bsd/2004/03/18/marc_espie.html.
- ↑ "OpenSSH Remote Challenge Vulnerability". 26 June 2002. http://www.iss.net/threats/advise123.html.
- ↑ "A partial list of affected operating systems". http://xforce.iss.net/xforce/xfdb/9169.
- ↑ "OpenBSD's IPv6 mbufs remote kernel buffer overflow.". 13 March 2007. http://www.coresecurity.com/content/open-bsd-advisorie.
- ↑ Brindle, Joshua (30 March 2008), "Secure doesn't mean anything", Security Blog, http://securityblog.org/brindle/2008/03/30/secure-doesnt-mean-anything/, retrieved 13 December 2011
- ↑ "Security". OpenBSD. http://www.openbsd.org/security.html. "Secure by Default."
- ↑ Wheeler, David A. (3 March 2003). "2.4. Is Open Source Good for Security?". Secure Programming for Linux and Unix HOWTO. http://www.dwheeler.com/secure-programs/Secure-Programs-HOWTO/open-source-security.html. Retrieved 13 December 2011.
- ↑ De Raadt, Theo (14 December 2010). "Allegations regarding OpenBSD IPSEC". openbsd-tech (Mailing list). Archived from the original on 25 December 2020. Retrieved 28 May 2016.
- ↑ Holwerda, Thom (14 December 2010). "FBI Added Secret Backdoors to OpenBSD IPSEC". OSNews. http://www.osnews.com/story/24136/_FBI_Added_Secret_Backdoors_to_OpenBSD_IPSEC_.
- ↑ Ryan, Paul (23 December 2010). "OpenBSD code audit uncovers bugs, but no evidence of backdoor". Ars Technica. https://arstechnica.com/open-source/news/2010/12/openbsd-code-audit-uncovers-bugs-but-no-evidence-of-backdoor.ars.
- ↑ Schwartz, Mathew J. (22 December 2010). "OpenBSD Founder Believes FBI Built IPsec Backdoor". InformationWeek: DARKreading. http://www.darkreading.com/vulnerabilities-and-threats/openbsd-founder-believes-fbi-built-ipsec-backdoor/d/d-id/1095055.
- ↑ Van Sprundel, Ilja (December 2017). "Are all BSDs created equally? — A survey of BSD kernel vulnerabilities". https://media.ccc.de/v/34c3-8968-are_all_bsds_created_equally.
- ↑ Van Sprundel, Ilja (July 2017). "Are all BSDs created equally? — A survey of BSD kernel vulnerabilities". https://media.defcon.org/DEF%20CON%2025/DEF%20CON%2025%20presentations/DEF%20CON%2025%20-%20Ilja-van-Sprundel-BSD-Kern-Vulns.pdf.
- ↑ "Lecture: A systematic evaluation of OpenBSD's mitigations". December 2019. https://fahrplan.events.ccc.de/congress/2019/Fahrplan/events/10519.html.
- ↑ "Is OpenBSD secure?". 29 December 2019. https://isopenbsdsecu.re/.
- ↑ "src/usr.sbin/httpd/". https://cvsweb.openbsd.org/cgi-bin/cvsweb/src/usr.sbin/httpd/.
- ↑ "web/obhttpd: OpenBSD http server". https://www.freshports.org/www/obhttpd/.
- ↑ "Game of Trees (Got)". https://gameoftrees.org.
- ↑ "LibreSSL". https://www.libressl.org/.
- ↑ 69.0 69.1 "OpenBGPD". http://www.openbgpd.org/.
- ↑ "OpenIKED". https://www.openiked.org.
- ↑ "OpenNTPD". http://www.openntpd.org/.
- ↑ "OpenSMTPD". https://www.opensmtpd.org.
- ↑ "OpenSSH". https://www.openssh.com/.
- ↑ "rpki-client". https://rpki-client.org.
- ↑ "Contents of /stable/10/crypto/openssh/README". https://svnweb.freebsd.org/base/stable/10/crypto/openssh/README?view=markup. "This is the port of OpenBSD's excellent OpenSSH to Linux and other Unices."
- ↑ "src/crypto/external/bsd/openssh/dist/README – view – 1.4". http://cvsweb.netbsd.org/bsdweb.cgi/src/crypto/external/bsd/openssh/dist/README?rev=1.4&content-type=text/x-cvsweb-markup&only_with_tag=MAIN.
- ↑ "dragonfly.git/blob – crypto/openssh/README". https://gitweb.dragonflybsd.org/dragonfly.git/blob/HEAD:/crypto/openssh/README. "This is the port of OpenBSD's excellent OpenSSH to Linux and other Unices."
- ↑ "Arch Linux – openssh 7.2p2-1 (x86_64)". Arch Linux. https://www.archlinux.org/packages/core/x86_64/openssh/.
- ↑ "openssh". OpenSUSE. https://software.opensuse.org/package/openssh.
- ↑ "Debian – Details of package openssh-client in jessie". Debian. https://packages.debian.org/jessie/openssh-client.
- ↑ De Raadt, Theo (18 June 2013). "An Internet Exchange for Calgary". http://www.yycix.ca/talks/cuug-2013-06-18/an-internet-exchange-for-Calgary.pdf.
- ↑ "3hg | isotop - index". https://www.3hg.fr/Isos/isotop/.
- ↑ pavroo (17 May 2021). "Isotop". https://archiveos.org/isotop/.
- ↑ 84.0 84.1 "clang-local – OpenBSD-specific behavior of LLVM/clang". OpenBSD manual pages. http://man.openbsd.org/OpenBSD-6.2/man1/clang-local.1.
- ↑ 85.0 85.1 85.2 85.3 85.4 Andrews, Jeremy (2 May 2006). "Interview: Theo de Raadt". KernelTrap. http://kerneltrap.org/node/6550.
- ↑ "OpenBSD's flavors". OpenBSD Frequently Asked Questions. https://www.openbsd.org/faq/faq5.html#Flavors.
- ↑ "Applying patches in OpenBSD". OpenBSD Frequently Asked Questions. https://www.openbsd.org/faq/faq10.html#Patches.
- ↑ "Migrating to OpenBSD". OpenBSD Frequently Asked Questions. http://www.openbsd.org/faq/faq1.html#OtherUnixes.
- ↑ "Hackathons". OpenBSD. https://www.openbsd.org/hackathons.html.
- ↑ "Interview: Theo de Raadt of OpenBSD". NewsForge. 28 March 2006. https://www.linux.com/news/interview-theo-de-raadt-openbsd/.
- ↑ 91.0 91.1 91.2 "Release Songs". OpenBSD. http://www.openbsd.org/lyrics.html.
- ↑ Chisnall, David (20 January 2006). "BSD: The Other Free UNIX Family". InformIT. http://www.informit.com/articles/article.aspx?p=439601&seqNum=3.
- ↑ Smith, Jesse (18 November 2013). "OpenBSD 5.4: Puffy on the Desktop". http://distrowatch.com/weekly.php?issue=20131118#feature.
- ↑ 94.0 94.1 Cranor, Chuck D.; De Raadt, Theo (6 June 1999). "Opening the Source Repository with Anonymous CVS". USENIX Annual Technical Conference. Monterey, California. https://www.usenix.org/legacy/event/usenix99/cranor_f.html. Retrieved 13 December 2011.
- ↑ Cranor, Chuck D.. "Chuck Cranor's Home Page". http://chuck.cranor.org/. "I also hosted and helped create the first Anonymous CVS server on the Internet (the original anoncvs.openbsd.org [...]"
- ↑ "OpenCVS released soon.". https://www.gnu.org/distros/common-distros.html.
- ↑ "OpenCVS is to be released soon.". https://www.gnu.org/distros/common-distros.html.
- ↑ "CVSINTRO(7)". https://man.openbsd.org/cvsintro.
- ↑ Fresh, Andrew. "Why OpenBSD Developers Use CVS". https://cvs.afresh1.com/~andrew/o/why-cvs.html.
- ↑ "Project Goals". http://www.openbsd.org/goals.html. "Integrate good code from any source with acceptable licenses. [...], NDAs are never acceptable."
- ↑ De Raadt, Theo; Hallqvist, Niklas; Grabowski, Artur; Keromytis, Angelos D.; Provos, Niels (6 June 1999). "Cryptography in OpenBSD: An Overview". USENIX Annual Technical Conference. Monterey, California. https://www.usenix.org/legacy/publications/library/proceedings/usenix99/deraadt.html. Retrieved 1 February 2014.
- ↑ 102.0 102.1 De Raadt, Theo (5 December 2006). "Presentation at OpenCON". http://www.openbsd.org/papers/opencon06-docs/index.html.
- ↑ "TI literature number SLLC139 TUSB3410 Bootcode Source Listing". https://github.com/openbsd/src/blob/master/sys/dev/microcode/tusb3410/tusb3410-license.
- ↑ "Permission from Realtek to include wireless firmwares". https://github.com/openbsd/src/blob/master/sys/dev/microcode/rsu/rsu-license.
- ↑ "Permission from Realtek to include wireless firmwares". https://github.com/openbsd/src/blob/master/sys/dev/microcode/urtwn/urtwn-license.
- ↑ "Permission from Realtek to include wireless firmwares". https://github.com/openbsd/src/blob/master/sys/dev/microcode/rtwn/rtwn-license.
- ↑ "more details in license files". https://github.com/openbsd/src/blob/master/sys/dev/microcode/atmel/atu-license.
- ↑ "more details in license files". https://github.com/openbsd/src/blob/master/sys/dev/microcode/cirruslogic/cs4280-license.
- ↑ "typo. OK deraadt@". https://github.com/openbsd/src/blob/master/sys/dev/microcode/cirruslogic/cs4280-license.
- ↑ "Explaining Why We Don't Endorse Other Systems". 10 December 2023. https://www.gnu.org/distros/common-distros.html.
- ↑ Matzan, Jem (15 June 2005). "BSD cognoscenti on Linux". NewsForge. Linux.com. https://www.linux.com/news/bsd-cognoscenti-linux.
- ↑ Gasperson, Tina (6 June 2001). "OpenBSD and ipfilter still fighting over license disagreement". Linux.com. http://www.linux.com/feature/12774.
- ↑ "src/usr.sbin/mrinfo/mrinfo.c – view – 1.7". cvsweb.openbsd.org. 31 July 2001. http://cvsweb.openbsd.org/cgi-bin/cvsweb/src/usr.sbin/mrinfo/mrinfo.c?rev=1.7&content-type=text/x-cvsweb-markup. "New license from Xerox! This code is now FREE! Took a while and a lot of mails, but it is worth it."
- ↑ "src/usr.sbin/map-mbone/mapper.c – view – 1.5". cvsweb.openbsd.org. 31 July 2001. http://cvsweb.openbsd.org/cgi-bin/cvsweb/src/usr.sbin/map-mbone/mapper.c?rev=1.5&content-type=text/x-cvsweb-markup. "New license from Xerox! This code is now FREE! Took a while and a lot of mails, but it is worth it."
- ↑ De Raadt, Theo (24 August 2001). "Re: Why were all DJB's ports removed? No more qmail?". openbsd-misc (Mailing list). Archived from the original on 19 April 2016.
- ↑ Bernstein, Daniel J. (27 August 2001). "Re: Why were all DJB's ports removed? No more qmail?". openbsd-misc (Mailing list). Archived from the original on 4 February 2012.
- ↑ Espie, Marc (28 August 2001). "Re: Why were all DJB's ports removed? No more qmail?". openbsd-misc (Mailing list). Archived from the original on 19 April 2016.
- ↑ Hartmeier, Daniel (10 June 2002). "Design and Performance of the OpenBSD Stateful Packet Filter (pf)". USENIX Annual Technical Conference. Monterey, California. https://www.usenix.org/legacy/event/usenix02/tech/freenix/hartmeier.html. Retrieved 13 December 2011.
- ↑ The OpenBSD PF Packet Filter Book: PF for NetBSD, FreeBSD, DragonFly and OpenBSD. Reed Media Services. 2006. ISBN 0-9790342-0-5. http://www.reedmedia.net/books/pf-book/. Retrieved 19 May 2016.
- ↑ "New BSD licensed CVS replacement for OpenBSD". 6 December 2004. https://slashdot.org/story/52396.
- ↑ "pkg-config(1)". https://man.openbsd.org/pkg-config.1.
- ↑ "OpenBSD Project in Financial Danger". Slashdot. 21 March 2006. http://slashdot.org/story/06/03/21/1555243/openbsd-project-in-financial-danger.
- ↑ "Mozilla Foundation Donates $10K to OpenSSH". Slashdot. 4 April 2006. http://slashdot.org/story/06/04/04/1820228/mozilla-foundation-donates-10k-to-openssh.
- ↑ "GoDaddy.com Donates $10K to Open Source Development Project". The Hosting News. 19 April 2006. http://www.thehostingnews.com/article2217.html.
- ↑ Beck, Bob (14 January 2014). "Request for Funding our Electricity". openbsd-misc (Mailing list). Archived from the original on 12 November 2020. Retrieved 17 May 2016.
- ↑ 126.0 126.1 Bright, Peter (20 January 2014). "OpenBSD rescued from unpowered oblivion by $20K bitcoin donation". Ars Technica. https://arstechnica.com/information-technology/2014/01/openbsd-rescued-from-unpowered-oblivion-by-20k-bitcoin-donation/.
- ↑ "The OpenBSD Foundation 2014 Fundraising Campaign". OpenBSD Foundation. http://www.openbsdfoundation.org/campaign2014.html.
- ↑ "Announcing - The OpenBSD Foundation". OpenBSD Journal. 26 July 2007. http://undeadly.org/cgi?action=article&sid=20070726015128.
- ↑ Brodkin, Jon (22 April 2014). "OpenSSL code beyond repair, claims creator of "LibreSSL" fork". https://arstechnica.com/information-technology/2014/04/openssl-code-beyond-repair-claims-creator-of-libressl-fork/.
- ↑ McAllister, Neil (8 July 2015). "Microsoft rains cash on OpenBSD Foundation, becomes top 2015 donor". https://www.theregister.co.uk/2015/07/08/microsoft_donates_to_openbsd_foundation/.
- ↑ "Contributors". OpenBSD Foundation. http://www.openbsdfoundation.org/contributors.html.
- ↑ Vaughan-Nichols, Steven J.. "Microsoft becomes OpenBSD's first gold contributor". https://www.zdnet.com/article/microsoft-becomes-openbsds-first-gold-contributor/.
- ↑ Mackie, Kurt (12 November 2018). "Microsoft Now Supports OpenSSH in Windows Server 2019". https://redmondmag.com/articles/2018/12/11/microsoft-now-supports-openssh-in-windows-server-2019.aspx.
- ↑ "Donate to the OpenBSD Foundation". https://www.openbsdfoundation.org/contributors.html.
- ↑ "OpenBSD Donors". http://www.openbsdfoundation.org/contributors.html.
- ↑ "Smartisan Makes Another Iridium Donation to the OpenBSD Foundation". http://undeadly.org/cgi?action=article&sid=20170817195416.
- ↑ "Anonymous CVS". OpenBSD. http://www.openbsd.org/anoncvs.html.
- ↑ "Mirrors". OpenBSD. http://www.openbsd.org/ftp.html.
- ↑ "Orders". OpenBSD. http://www.openbsd.org/orders.html.
- ↑ 140.0 140.1 "Packages and Ports". OpenBSD Frequently Asked Questions. http://www.openbsd.org/faq/faq15.html.
- ↑ "OpenBSD". http://www.mckusick.com/beastie/shirts/openbsd.html.
- ↑ De Raadt, Theo (19 May 1999). "OpenBSD 2.5 Release Announcement". openbsd-announce (Mailing list). Archived from the original on 2 February 2014.
OpenBSD 2.5 introduces the new Cop daemon image done by cartoonist Ty Semeka.
- ↑ "OpenBSD 2.7". OpenBSD. http://www.openbsd.org/27.html.
- ↑ Matzan, Jem (1 November 2006). "OpenBSD 4.0 review". Software in Review. http://www.softwareinreview.com/bsd/openbsd_4.0_review.html. "Each OpenBSD release has a graphical theme and a song that goes with it. The theme reflects a major concern that the OpenBSD programmers are addressing or bringing to light."
- ↑ "Undeadly". http://undeadly.org/cgi?action=article&sid=20061019013207.
- ↑ "Changes". http://www.openbsd.org/plus.html.
- ↑ "OpenBSD 2.0". http://wolfram.schneider.org/bsd/ftp/releases/OpenBSD-2.0.
- ↑ "Release Notes". https://www.openbsd.org/21.html.
- ↑ "Release Notes". https://www.openbsd.org/22.html.
- ↑ "Release Notes". https://www.openbsd.org/23.html.
- ↑ "Release Notes". https://www.openbsd.org/24.html.
- ↑ "Release Notes". https://www.openbsd.org/25.html.
- ↑ "Release Notes". https://www.openbsd.org/26.html.
- ↑ "Release Notes". https://www.openbsd.org/27.html.
- ↑ "OpenBSD 2.8 Changelog". https://www.openbsd.org/plus28.html.
- ↑ "Release Notes". https://www.openbsd.org/29.html.
- ↑ "Release Notes". https://www.openbsd.org/30.html.
- ↑ "Release Notes". https://www.openbsd.org/31.html.
- ↑ "Errata". https://www.openbsd.org/errata31.html#sshderrata31.
- ↑ "Release Notes". https://www.openbsd.org/32.html.
- ↑ "Release Notes". https://www.openbsd.org/33.html.
- ↑ "Release Notes". https://www.openbsd.org/34.html.
- ↑ "p0f". http://www.stearns.org/p0f/p0f.
- ↑ 164.0 164.1 164.2 "OpenBSD Innovations". The OpenBSD project. https://www.openbsd.org/innovations.html.
- ↑ 165.0 165.1 165.2 Constantine A. Murenin; Raouf Boutaba (17 March 2009). "OpenBSD Hardware Sensors Framework.". AsiaBSDCon 2009 Proceedings, 12–15 March 2009. Tokyo University of Science, Tokyo, Japan (published 14 March 2009). http://www.openbsd.org/papers/asiabsdcon2009-sensors-paper.pdf. Retrieved 4 March 2019. Alt URL
- ↑ "Release Notes". https://www.openbsd.org/35.html.
- ↑ Biancuzzi, Federico (15 April 2004). "OpenBSD PF Developer Interview". O'Reilly Media. http://www.onlamp.com/lpt/a/4767.
- ↑ Federico Biancuzzi (6 May 2004). "OpenBSD PF Developer Interview, Part 2". O'Reilly Media. http://www.onlamp.com/lpt/a/4839.
- ↑ "bc(1)". https://man.openbsd.org/bc.1.
- ↑ "dc(1)". https://man.openbsd.org/OpenBSD-5.9/man1/dc.1.
- ↑ "nm(1)". https://man.openbsd.org/nm.1.
- ↑ "size(1)". https://man.openbsd.org/size.1.
- ↑ "Release Notes". https://www.openbsd.org/36.html.
- ↑ "Release Notes". https://www.openntpd.org/goals.html.
- ↑ 175.0 175.1 Federico Biancuzzi (28 October 2004). "OpenBSD 3.6 Live". O'Reilly Media. http://www.onlamp.com/lpt/a/5302.
- ↑ "Release Notes". https://www.openbsd.org/37.html.
- ↑ Federico Biancuzzi (19 May 2005). "OpenBSD 3.7: The Wizard of OS". O'Reilly Media. http://www.onlamp.com/pub/a/bsd/2005/05/19/openbsd_3_7.html.
- ↑ Federico Biancuzzi (20 October 2005). "OpenBSD 3.8: Hackers of the Lost RAID". O'Reilly Media. http://www.onlamp.com/lpt/a/6270.
- ↑ "Release Notes". https://www.openbsd.org/39.html.
- ↑ 180.0 180.1 Federico Biancuzzi (27 April 2006). "OpenBSD 3.9: Blob-Busters Interviewed". O'Reilly Media. http://www.onlamp.com/lpt/a/6557.
- ↑ "Release Notes". https://www.openbsd.org/40.html.
- ↑ Federico Biancuzzi (26 October 2006). "OpenBSD 4.0: Pufferix's Adventures". O'Reilly Media. http://www.oreillynet.com/lpt/a/6769.
- ↑ "Errata". https://www.openbsd.org/errata40.html#m_dup1errata40.
- ↑ "Release Notes". https://www.openbsd.org/41.html.
- ↑ Federico Biancuzzi (3 May 2007). "OpenBSD 4.1: Puffy Strikes Again". O'Reilly Media. http://www.onlamp.com/lpt/a/7008.
- ↑ Constantine A. Murenin (30 December 2006). "New two-level sensor API". in Marco Peereboom. http://undeadly.org/cgi?action=article&sid=20061230235005.
- ↑ Constantine A. Murenin (17 April 2007). "Generalised Interfacing with Microprocessor System Hardware Monitors". Proceedings of 2007 IEEE International Conference on Networking, Sensing and Control, 15–17 April 2007.. London, United Kingdom: IEEE. pp. 901–906. doi:10.1109/ICNSC.2007.372901. IEEE ICNSC 2007, pp. 901–906.. ISBN 978-1-4244-1076-7. http://sensors.cnst.su/IEEE_ICNSC_2007.
- ↑ "Release Notes". https://www.openbsd.org/42.html.
- ↑ Federico Biancuzzi (1 November 2007). "Puffy's Marathon: What's New in OpenBSD 4.2". O'Reilly Media. http://onlamp.com/lpt/a/7155.
- ↑ "Release Notes". https://www.openbsd.org/43.html.
- ↑ Federico Biancuzzi (29 April 2008). "Puffy and the Cryptonauts: What's New in OpenBSD 4.3". O'Reilly Media. http://www.onlamp.com/lpt/a/7290.
- ↑ "Release Notes". https://www.openbsd.org/44.html.
- ↑ Kurt Miller (2008). "OpenBSD's Position Independent Executable (PIE) Implementation". https://www.openbsd.org/papers/nycbsdcon08-pie/.
- ↑ 194.0 194.1 Federico Biancuzzi (3 November 2008). "Source Wars - Return of the Puffy: What's New in OpenBSD 4.4". O'Reilly Media. http://broadcast.oreilly.com/2008/11/source-wars---return-of-the-pu.html.
- ↑ "Release Notes". https://www.openbsd.org/45.html.
- ↑ Federico Biancuzzi (15 June 2009). "PuffyTron recommends OpenBSD 4.5". O'Reilly Media. http://broadcast.oreilly.com/2009/06/openbsd-45.html.
- ↑ 197.0 197.1 Constantine A. Murenin (21 May 2010). "6.2. Evolution of drivers; Chart VII. Number of drivers using the sensors framework from OpenBSD 3.4 to 4.6.". OpenBSD Hardware Sensors — Environmental Monitoring and Fan Control (MMath thesis). University of Waterloo: UWSpace. hdl:10012/5234. Document ID: ab71498b6b1a60ff817b29d56997a418.
- ↑ "Release Notes". https://www.openbsd.org/46.html.
- ↑ "Release Notes". https://www.openbsd.org/47.html.
- ↑ "Release Notes". https://www.openbsd.org/48.html.
- ↑ "MARC". http://marc.info/?l=openbsd-misc&m=128397592926217&w=2.
- ↑ "Release Notes". https://www.openbsd.org/49.html.
- ↑ "Release Notes". https://www.openbsd.org/50.html.
- ↑ "Release Notes". https://www.openbsd.org/51.html.
- ↑ "Release Notes". https://www.openbsd.org/52.html.
- ↑ "Release Notes". https://www.openbsd.org/53.html.
- ↑ "Release Notes". https://www.openbsd.org/54.html.
- ↑ "Release Notes". https://www.openbsd.org/55.html.
- ↑ "Release Notes". https://www.openbsd.org/56.html.
- ↑ "Release Notes". https://www.openbsd.org/57.html.
- ↑ "Release Notes". https://www.openbsd.org/58.html.
- ↑ "MARC". http://marc.info/?l=openbsd-announce&m=144515087006176.
- ↑ "Release Notes". https://www.openbsd.org/59.html.
- ↑ OpenBSD 6.0. ISBN 978-0-9881561-8-0. https://www.openbsd.org/60.html. Retrieved 24 July 2016.
- ↑ "OpenBSD vax". https://www.openbsd.org/vax.html.
- ↑ "OpenBSD sparc". https://www.openbsd.org/sparc.html.
- ↑ "OpenBSD 6.1". https://www.openbsd.org/61.html.
- ↑ "OpenBSD 6.2". https://www.openbsd.org/62.html.
- ↑ "unveil(2)". https://man.openbsd.org/unveil.
- ↑ "OpenBSD 6.6". https://www.openbsd.org/66.html.
- ↑ "OpenBSD 6.7". https://www.openbsd.org/67.html.
- ↑ "OpenBSD 6.8". https://www.openbsd.org/68.html.
- ↑ "OpenBSD FAQ". https://www.openbsd.org/faq/faq5.html#Flavors.
- ↑ "OpenBSD 6.9". https://www.openbsd.org/69.html.
- ↑ 225.0 225.1 "OpenBSD 7.0". https://www.openbsd.org/70.html.
- ↑ "OpenBSD 7.1". https://www.openbsd.org/71.html.
- ↑ "OpenBSD loongson". http://www.openbsd.org/loongson.html.
- ↑ "OpenBSD 7.2". https://www.openbsd.org/72.html.
- ↑ "OpenBSD 7.3". https://www.openbsd.org/73.html.
- ↑ "OpenBSD 7.4". https://www.openbsd.org/74.html.
- ↑ "OpenBSD 7.5". https://www.openbsd.org/75.html.
- ↑ "OpenBSD 7.6". https://www.openbsd.org/76.html.
- ↑ "OpenBSD 7.7". https://www.openbsd.org/77.html.
- ↑ "OpenBSD 7.8". https://www.openbsd.org/78.html.
External links
- The OpenBSD Foundation
- on GitHub
- OpenBSD at DistroWatch
- OpenBSD manual pages
- OpenBSD source code search
 |
