Sponge function
In cryptography, a sponge function or sponge construction is any of a class of algorithms with finite internal state that take an input bit stream of any length and produce an output bit stream of any desired length. Sponge functions have both theoretical and practical uses. They can be used to model or implement many cryptographic primitives, including cryptographic hashes, message authentication codes, mask generation functions, stream ciphers, pseudo-random number generators, and authenticated encryption.[1]
Construction
A sponge function is built from three components:[2]
- a state memory, S, containing b bits,
- a function
- a padding function P
S is divided into two sections: one of size r (the bitrate) and the remaining part of size c (the capacity). These sections are denoted R and C respectively.
f produces a pseudorandom permutation of the states from S.
P appends enough bits to the input string so that the length of the padded input is a whole multiple of the bitrate, r. This means the input is segmented into blocks of r bits.
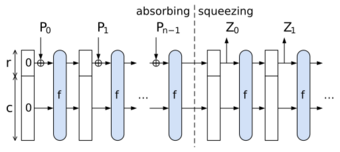
Operation
The sponge function "absorbs" (in the sponge metaphor) all blocks of a padded input string as follows:
- S is initialized to zero
- for each r-bit block B of P(string)
- R is replaced with R XOR B (using bitwise XOR)
- S is replaced by f(S)
The sponge function output is now ready to be produced ("squeezed out") as follows:
- repeat until output is full
- output the R portion of S
- S is replaced by f(S)
If less than r bits remain to be output, then R will be truncated (only part of R will be output).
Another metaphor describes the state memory as an "entropy pool", with input "poured into" the pool, and the transformation function referred to as "stirring the entropy pool".[3]
Note that input bits are never XORed into the C portion of the state memory, nor are any bits of C ever output directly. The extent to which C is altered by the input depends entirely on the transformation function f. In hash applications, resistance to collision or preimage attacks depends on C, and its size (the "capacity" c) is typically twice the desired resistance level.
Duplex construction
It is also possible to absorb and squeeze in an alternating fashion.[1] This operation is called the duplex construction or duplexing. It can be the basis of a single pass authenticated encryption system. This have also been used as an efficient variant of the Fiat-Shamir transformation for some protocols.[4]
- The state S is initialized to zero
- for each r-bit block B of the input
- R is XORed with B
- S is replaced by f(S)
- R is now an output block of size r bits.
Overwrite mode
It is possible to omit the XOR operations during absorption, while still maintaining the chosen security level.[1] In this mode, in the absorbing phase, the next block of the input overwrites the R part of the state. This allows keeping a smaller state between the steps. Since the R part will be overwritten anyway, it can be discarded in advance, only the C part must be kept.
Applications
Sponge functions have both theoretical and practical uses. In theoretical cryptanalysis, a random sponge function is a sponge construction where f is a random permutation or transformation, as appropriate. Random sponge functions capture more of the practical limitations of cryptographic primitives than does the widely used random oracle model, in particular the finite internal state.[5]
The sponge construction can also be used to build practical cryptographic primitives. For example, the Keccak cryptographic sponge with a 1600-bit state has been selected by NIST as the winner in the SHA-3 competition. The strength of Keccak derives from the intricate, multi-round permutation f that its authors developed.[6] The RC4-redesign called Spritz refers to the sponge-construct to define the algorithm.
For other examples, a sponge function can be used to build authenticated encryption with associated data (AEAD),[3] as well as password hashing schemes.[7]
References
- ↑ 1.0 1.1 1.2 Bertoni, Guido; Daemen, Joan; Peeters, Michaël; van Assche, Giles. "Duplexing the Sponge: Single-Pass Authenticated Encryption and Other Applications". https://keccak.team/files/SpongeDuplex.pdf.
- ↑ Bertoni, Guido; Daemen, Joan; Peeters, Michaël; van Assche, Giles. "The sponge and duplex constructions". https://keccak.team/sponge_duplex.html.
- ↑ 3.0 3.1 Rivest, Ron; Schuldt, Jacob (2014-10-27). "Spritz – a spongy RC4-like stream cipher and hash function". https://people.csail.mit.edu/rivest/pubs/RS14.pdf. Retrieved 2014-12-29.
- ↑ Chiesa, Alessandro; Orrù, Michele (2025), A Fiat-Shamir Transformation From Duplex Sponges, 2025/536, https://eprint.iacr.org/2025/536, retrieved 2025-04-09
- ↑ Bertoni, Guido; Daemen, Joan; Peeters, Michaël; van Assche, Giles. "On the Indifferentiability of the Sponge Construction". https://keccak.team/files/SpongeIndifferentiability.pdf.
- ↑ Boutin, Chad (2 October 2012). "NIST Selects Winner of Secure Hash Algorithm (SHA-3) Competition". NIST. https://www.nist.gov/itl/csd/sha-100212.cfm. Retrieved 4 October 2012.
- ↑ van Beirendonck, M.; Trudeau, L.; Giard, P.; Balatsoukas-Stimming, A. (2019-05-29). "A Lyra2 FPGA Core for Lyra2REv2-Based Cryptocurrencies". IEEE International Symposium on Circuits and Systems (ISCAS). Sapporo, Japan: IEEE. pp. 1–5. doi:10.1109/ISCAS.2019.8702498.
External links
 |
