Software:GNU Privacy Guard
 | |||||||
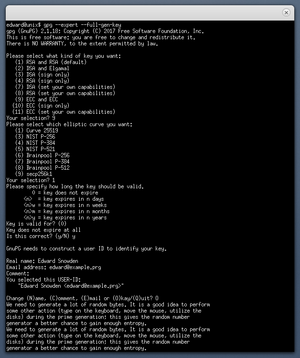 Key pair generation process in Unix terminal emulator | |||||||
| Original author(s) | Werner Koch | ||||||
|---|---|---|---|---|---|---|---|
| Developer(s) | GNU Project | ||||||
| Initial release | 7 September 1999 | ||||||
| Stable release(s) [±] | |||||||
| |||||||
| Repository | dev | ||||||
| Written in | C | ||||||
| Operating system | Microsoft Windows, macOS, RISC OS, Android, Linux | ||||||
| Type | OpenPGP | ||||||
| License | 2007: GPL-3.0-or-later[lower-alpha 1] 1997: GPL-2.0-or-later[lower-alpha 2] | ||||||
| Website | gnupg | ||||||
GNU Privacy Guard (GnuPG or GPG) is a free-software replacement for Symantec's cryptographic software suite PGP. The software is compliant with the now obsoleted[4] RFC 4880, the IETF standards-track specification of OpenPGP. Modern versions of PGP are interoperable with GnuPG and other OpenPGP v4-compliant systems.[5]
November 2023 saw two drafts aiming to update the 2007 OpenPGP v4 specification (RFC4880), ultimately resulting in the RFC 9580 standard in July 2024. The proposal from the GnuPG developers, which is called LibrePGP, was not taken up by the OpenPGP Working Group and future versions of GnuPG will not support the current version of OpenPGP.[6]
GnuPG is part of the GNU Project and received major funding from the German government in 1999.[7]
Overview
GnuPG is a hybrid-encryption software program because it uses a combination of conventional symmetric-key cryptography for speed, and public-key cryptography for ease of secure key exchange, typically by using the recipient's public key to encrypt a session key which is used only once. This mode of operation is part of the OpenPGP standard and has been part of PGP from its first version.
The GnuPG 1.x series uses an integrated cryptographic library, while the GnuPG 2.x series replaces this with Libgcrypt.
GnuPG encrypts messages using asymmetric key pairs individually generated by GnuPG users. The resulting public keys may be exchanged with other users in a variety of ways, such as Internet key servers. They must always be exchanged carefully to prevent identity spoofing by corrupting public key ↔ "owner" identity correspondences. It is also possible to add a cryptographic digital signature to a message, so the message integrity and sender can be verified, if a particular correspondence relied upon has not been corrupted.
GnuPG also supports symmetric encryption algorithms. By default, GnuPG uses the AES symmetrical algorithm since version 2.1,[8] CAST5 was used in earlier versions. GnuPG does not use patented or otherwise restricted software or algorithms. Instead, GnuPG uses a variety of other, non-patented algorithms.[9] For a long time, it did not support the IDEA encryption algorithm used in PGP. It was in fact possible to use IDEA in GnuPG by downloading a plugin for it, however, this might require a license for some uses in countries in which IDEA was patented. Starting with versions 1.4.13 and 2.0.20, GnuPG supports IDEA because the last patent of IDEA expired in 2012. Support of IDEA is intended "to get rid of all the questions from folks either trying to decrypt old data or migrating keys from PGP to GnuPG",[10] and hence is not recommended for regular use.
More recent releases of GnuPG 2.x ("modern" and the now deprecated "stable" series) expose most cryptographic functions and algorithms Libgcrypt (its cryptography library) provides, including support for elliptic-curve cryptography (ECDH, ECDSA and EdDSA)[11] in the "modern" series (i.e. since GnuPG 2.1).
Algorithms
As of 2.3 or 2.2 versions, GnuPG supports the following algorithms:
- Public key
- RSA, ElGamal, DSA, ECDH (cv25519, cv448,[lower-alpha 3] nistp256, nistp384, nistp521, brainpoolP256r1, brainpoolP384r1, brainpoolP512r1, secp256k1), ECDSA (nistp256, nistp384, nistp521, brainpoolP256r1, brainpoolP384r1, brainpoolP512r1, secp256k1), EdDSA (ed25519, ed448[lower-alpha 3])
- Cipher
- 3DES, IDEA (for backward compatibility), CAST5, Blowfish, Twofish, AES-128, AES-192, AES-256, Camellia-128, -192 and -256
- Hash
- MD5, SHA-1, RIPEMD-160, SHA-256, SHA-384, SHA-512, SHA-224
- Compression
- Uncompressed, ZIP, ZLIB, BZIP2
History
GnuPG was initially developed by Werner Koch.[12][13] The first production version, version 1.0.0, was released on September 7, 1999, almost two years after the first GnuPG release (version 0.0.0).[14][12] The German Federal Ministry of Economics and Technology funded the documentation and the port to Microsoft Windows in 2000.[13]
GnuPG is a system compliant to the OpenPGP standard, thus the history of OpenPGP is of importance; it was designed to interoperate with PGP, an email encryption program initially designed and developed by Phil Zimmermann.[15][16]
On February 7, 2014, a GnuPG crowdfunding effort closed, raising €36,732 for a new website and infrastructure improvements.[17]
Branches
Since the release of a stable GnuPG 2.3, starting with version 2.3.3 in October 2021, three stable branches of GnuPG are actively maintained:[18]
- A "stable branch", which currently is (as of 2026) the 2.5 branch.[19]
- An "old stable branch", which currently is (as of 2026) the 2.4 branch.
- The old "legacy branch" (formerly called "classic branch"), which is and will stay the 1.4 branch.
Before GnuPG 2.3, two stable branches of GnuPG were actively maintained:
- "Modern" (2.2), with numerous new features, such as elliptic curve cryptography, compared to the former "stable" (2.0) branch, which it replaced with the release of GnuPG 2.2.0 on August 28, 2017.[20] It was initially released on November 6, 2014.[11]
- "Classic" (1.4), the very old, but still maintained stand-alone version, most suitable for outdated or embedded platforms. Initially released on December 16, 2004.[21]
Different GnuPG 2.x versions (e.g. from the 2.2 and 2.0 branches) cannot be installed at the same time. However, it is possible to install a "classic" GnuPG version (i.e. from the 1.4 branch) along with any GnuPG 2.x version.[11]
Before the release of GnuPG 2.2 ("modern"), the now deprecated "stable" branch (2.0) was recommended for general use, initially released on November 13, 2006.[22] This branch reached its end-of-life on December 31, 2017;[23] Its last version is 2.0.31, released on December 29, 2017.[24]
Before the release of GnuPG 2.0, all stable releases originated from a single branch; i.e., before November 13, 2006, no multiple release branches were maintained in parallel. These former, sequentially succeeding (up to 1.4) release branches were:
- 1.2 branch, initially released on September 22, 2002,[25] with 1.2.6 as the last version, released on October 26, 2004.[26]
- 1.0 branch, initially released on September 7, 1999,[14] with 1.0.7 as the last version, released on April 30, 2002.[27]
(Note that before the release of GnuPG 2.3.0, branches with an odd minor release number (e.g. 2.1, 1.9, 1.3) were development branches leading to a stable release branch with a "+ 0.1" higher version number (e.g. 2.2, 2.0, 1.4); hence branches 2.2 and 2.1 both belong to the "modern" series, 2.0 and 1.9 both to the "stable" series, while the branches 1.4 and 1.3 both belong to the "classic" series.
With the release of GnuPG 2.3.0, this nomenclature was altered to be composed of a "stable" and "LTS" branch from the "modern" series, plus 1.4 as the last maintained "classic" branch. Also note that even or odd minor release numbers do not indicate a stable or development release branch, anymore.)
Platforms

Although the basic GnuPG program has a command-line interface, there exists various front-ends that provide it with a graphical user interface. For example, GnuPG encryption support has been integrated into KMail and Evolution, the graphical email clients found in KDE and GNOME, the most popular Linux desktops. There are also graphical GnuPG front-ends, for example Seahorse for GNOME and KGPG and Kleopatra for KDE.
GPGTools provides a number of front-ends for OS integration of encryption and key management as well as GnuPG installations via Installer packages[28] for macOS. GPG Suite[28] installs all related OpenPGP applications (GPG Keychain), plugins (GPG Mail) and dependencies (MacGPG), along with GPG Services (integration into macOS Services menu) to use GnuPG based encryption.
Instant messaging applications such as Psi and Fire can automatically secure messages when GnuPG is installed and configured. Web-based software such as Horde also makes use of it. The cross-platform extension Enigmail provides GnuPG support for Mozilla Thunderbird and SeaMonkey. Similarly, Enigform provides GnuPG support for Mozilla Firefox. FireGPG was discontinued June 7, 2010.[29]
In 2005, g10 Code GmbH and Intevation GmbH released Gpg4win, a software suite that includes GnuPG for Windows, GNU Privacy Assistant, and GnuPG plug-ins for Windows Explorer and Outlook. These tools are wrapped in a standard Windows installer, making it easier for GnuPG to be installed and used on Windows systems.[30]
Vulnerabilities
The OpenPGP standard specifies several methods of digitally signing messages. In 2003, due to an error in a change to GnuPG intended to make one of those methods more efficient, a security vulnerability was introduced.[31] It affected only one method of digitally signing messages, only for some releases of GnuPG (1.0.2 through 1.2.3), and there were fewer than 1000 such keys listed on the key servers.[32] Most people did not use this method, and were in any case discouraged from doing so, so the damage caused (if any, since none has been publicly reported) would appear to have been minimal. Support for this method has been removed from GnuPG versions released after this discovery (1.2.4 and later).
Two further vulnerabilities were discovered in early 2006; the first being that scripted uses of GnuPG for signature verification may result in false positives,[33] the second that non-MIME messages were vulnerable to the injection of data which while not covered by the digital signature, would be reported as being part of the signed message.[34] In both cases updated versions of GnuPG were made available at the time of the announcement.
In June 2017, a vulnerability (CVE-2017-7526) was discovered within Libgcrypt by Bernstein, Breitner and others: a library used by GnuPG, which enabled a full key recovery for RSA-1024 and about more than 1/8 of RSA-2048 keys. This side-channel attack exploits the fact that Libgcrypt used a sliding windows method for exponentiation which leads to the leakage of exponent bits and to full key recovery.[35][36] Again, an updated version of GnuPG was made available at the time of the announcement.
Around June 2018, the SigSpoof attacks were announced. These allowed an attacker to convincingly spoof digital signatures.[37][38]
In January 2021, Libgcrypt 1.9.0 was released, which was found to contain a severe bug that was simple to exploit. A fix was released 10 days later in Libgcrypt 1.9.1.[39]
In December 2025, at Chaos Communication Congress, Lexi Groves (aka 49016) and Liam Wachter presented a series of vulnerabilities in GnuPG, ranging from remote code execution to unauthorized subkey addition. The team reported those bugs to the GnuPG issue tracker, with some of them getting fixed and others still remaining unresolved.[40][41]
Divergence from OpenPGP standard
In November 2023, the LibrePGP standard was released. This was in response to changes made to the OpenPGP standard that were perceived by the GnuPG team to be unfounded. The GnuPG project no longer aims to comply with the OpenPGP standard, instead opting to comply with their own LibrePGP standard, which is meant to be based on the OpenPGP standard as it existed in September 2021.[42][43]
See also
- Acoustic cryptanalysis
- Key signing party
- Off-the-Record Messaging – also known as OTR
- OpenPGP card – a smartcard with many GnuPG functions
- Package manager
- Retroshare – a friend-to-friend network based on PGP authentication
- Web of trust
Notes
References
- ↑ "Noteworthy changes in version 2.3.2". 2021-08-24. https://dev.gnupg.org/source/gnupg/browse/master/NEWS;gnupg-2.3.2.
- ↑ "Noteworthy changes in version 2.2.30". 2021-08-26. https://dev.gnupg.org/source/gnupg/browse/master/NEWS;gnupg-2.2.30.
- ↑ "Noteworthy changes in version 1.4.23". 2018-06-11. https://dev.gnupg.org/source/gnupg/browse/master/NEWS;gnupg-1.4.23.
- ↑ Wouters, Paul; Huigens, Daniel; Winter, Justus; Yutaka, Niibe (July 2024). "RFC 9580 OpenPGP". IETF. https://www.rfc-editor.org/rfc/rfc9580.html.
- ↑ "GnuPG Frequently Asked Questions". The GNU Privacy Guard. https://www.gnupg.org/faq/gnupg-faq.html#compatible.
- ↑ Edge, Jake (December 6, 2023). "A schism in the OpenPGP world". Linux Weekly News. https://lwn.net/Articles/953797/.
- ↑ "Bundesregierung fördert Open Source" (in de). Heise Online. 1999-11-15. http://www.heise.de/newsticker/meldung/Bundesregierung-foerdert-Open-Source-24110.html.
- ↑ "[Announce] The maybe final Beta for GnuPG 2.1". https://lists.gnupg.org/pipermail/gnupg-announce/2014q4/000357.html.
- ↑ "GnuPG Features". https://www.gnupg.org/features.en.html.
- ↑ Koch, Werner (2012-12-21). "GnuPG 1.4.13 released" (Mailing list). gnupg-users. Archived from the original on 2013-02-12. Retrieved 2013-05-19.
- ↑ 11.0 11.1 11.2 Koch, Werner (2014-11-06). "[Announce] GnuPG 2.1.0 "modern" released". gnupg.org. http://lists.gnupg.org/pipermail/gnupg-announce/2014q4/000358.html.
- ↑ 12.0 12.1 Angwin, Julia (5 February 2015). "The World's Email Encryption Software Relies on One Guy, Who is Going Broke". ProPublica. https://www.propublica.org/article/the-worlds-email-encryption-software-relies-on-one-guy-who-is-going-broke.
- ↑ 13.0 13.1 Wayner, Peter (19 November 1999). "Germany Awards Grant for Encryption". The New York Times. http://partners.nytimes.com/library/tech/99/11/cyber/articles/19encrypt.html.
- ↑ 14.0 14.1 "Release Notes". GnuPG. https://gnupg.org/download/release_notes.html#sec-2-41.
- ↑ "Gnu Privacy Guard". OpenPGP.org. http://www.openpgp.org/members/gnupg.shtml.
- ↑ "Where to Get PGP". Philzimmermann.com. https://philzimmermann.com/EN/findpgp/.
- ↑ "GnuPG: New web site and infrastructure". goteo.org. http://goteo.org/project/gnupg-new-website-and-infrastructure/home.
- ↑ "GnuPG 2.3.3 released". https://lists.gnupg.org/pipermail/gnupg-announce/2021q4/000466.html.
- ↑ "The GNU Privacy Guard". https://gnupg.org/.
- ↑ Koch, Werner (2017-08-28). "[Announce] GnuPG 2.2.0 released". gnupg-announce (Mailing list). Archived from the original on 2017-08-29. Retrieved 2017-09-21.
- ↑ Koch, Werner (2004-12-16). "[Announce] GnuPG stable 1.4 released". gnupg.org. http://lists.gnupg.org/pipermail/gnupg-announce/2004q4/000186.html.
- ↑ Koch, Werner (2006-11-13). "[Announce] GnuPG 2.0 released". gnupg.org. http://lists.gnupg.org/pipermail/gnupg-announce/2006q4/000239.html.
- ↑ Koch, Werner (2017-01-23). "[Announce] GnuPG 2.1.18 released" (in en). gnupg.org. https://lists.gnupg.org/pipermail/gnupg-announce/2017q1/000401.html.
- ↑ "GnuPG 2.0.31". 2017-12-29. https://dev.gnupg.org/rGe6dae418c260592c0860519481b5eb92d14329db.
- ↑ Koch, Werner (2002-09-06). "[Announce]GnuPG 1.2 released". gnupg.org. http://lists.gnupg.org/pipermail/gnupg-announce/2002q3/000136.html.
- ↑ Koch, Werner (2004-08-26). "[Announce] GnuPG 1.2.6 released". gnupg.org. http://lists.gnupg.org/pipermail/gnupg-announce/2004q3/000176.html.
- ↑ Koch, Werner (2002-04-30). "[Announce] GnuPG 1.0.7 released". gnupg.org. http://lists.gnupg.org/pipermail/gnupg-announce/2002q2/000135.html.
- ↑ 28.0 28.1 "GPG Suite". GPGTools. https://gpgtools.org/.
- ↑ "FireGPG's developers blog". 7 June 2010. http://blog.getfiregpg.org/2010/06/07/firegpg-discontinued/.
- ↑ "Gpg4win – About Gpg4win". https://www.gpg4win.org/about.html.
- ↑ Nguyen, Phong Q.. "Can We Trust Cryptographic Software? Cryptographic Flaws in GNU Privacy Guard v1.2.3.". EUROCRYPT 2004: 555–570. https://www.di.ens.fr/~pnguyen/pub_Ng04.htm.
- ↑ Koch, Werner (November 27, 2003). "GnuPG's ElGamal signing keys compromised". http://lists.gnupg.org/pipermail/gnupg-announce/2003q4/000160.html.
- ↑ Koch, Werner (February 15, 2006). "False positive signature verification in GnuPG". http://lists.gnupg.org/pipermail/gnupg-announce/2006q1/000211.html.
- ↑ Koch, Werner (March 9, 2006). "GnuPG does not detect injection of unsigned data". http://lists.gnupg.org/pipermail/gnupg-announce/2006q1/000218.html.
- ↑ Edge, Jake (5 July 2017). "Breaking Libgcrypt RSA via a side channel". https://lwn.net/Articles/727179/.
- ↑ "Sliding right into disaster: Left-to-right sliding windows leak". https://eprint.iacr.org/2017/627.pdf.
- ↑ "Decades-old PGP bug allowed hackers to spoof just about anyone's signature". 14 June 2018. https://arstechnica.com/information-technology/2018/06/decades-old-pgp-bug-allowed-hackers-to-spoof-just-about-anyones-signature/.
- ↑ "Pass gets a fail: Simple Password Store suffers GnuPG spoofing bug". https://www.theregister.co.uk/2018/06/19/gnupg_popped_again_in_pass/.
- ↑ "Severe bug in Libgcrypt – used by GPG and others – is a whole heap of trouble, prompts patch scramble". https://www.theregister.com/2021/01/29/severe_libgcrypt_bug/.
- ↑ "gpg.fail". https://gpg.fail/.
- ↑ Groves, Lexi; Wachter, Liam (2025-12-27). To sign or not to sign: Practical vulnerabilities in GPG & friends (Video). Retrieved 2025-12-28 – via media.ccc.de.
- ↑ Heinecke, Andre (2025-01-17). "My thoughts on SequoiaPGP and LibrePGP". https://www.gnupg.org/blog/20250117-aheinecke-on-sequoia.html.
- ↑ "LibrePGP". https://librepgp.org/.
External links
- Official website
- A Short History of the GNU Privacy Guard, written by Werner Koch, published on GnuPG's 10th birthday
- GnuPG - ArchWiki, which includes practical information on how to use the software. Assumes the user is running Arch Linux, but the information is generally applicable on all systems.
 |
