Software:VeraCrypt
 | |
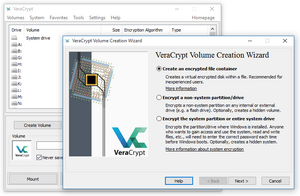 VeraCrypt 1.17 on Windows 10 | |
| Developer(s) | Mounir Idrassi[1] via IDRIX (based in Paris, France)[2] and AM Crypto (based in Kobe, Japan)[3] |
|---|---|
| Initial release | June 22, 2013 |
| Stable release | 1.26.7 (October 31, 2023[4]) [±] |
| Written in | C, C++, Assembly |
| Operating system |
|
| Platform | IA-32, x86-64, AArch64 and armhf |
| Available in | 43 languages[5] |
| Type | Disk encryption software |
| License | Multi-licensed as Apache License 2.0 and TrueCrypt License 3.0[6] |
VeraCrypt is a free and open-source utility for on-the-fly encryption (OTFE).[7] The software can create a virtual encrypted disk that works just like a regular disk, but within a file. It can also encrypt a partition[8] or (in Microsoft Windows) the entire storage device with pre-boot authentication.[9]
VeraCrypt is a fork of the discontinued TrueCrypt project.[10] It was initially released on 22 June 2013. Many security improvements have been implemented and concerns within the TrueCrypt code audits have been addressed. VeraCrypt includes optimizations to the original cryptographic hash functions and ciphers, which boost performance on modern central processing units.
Encryption scheme
VeraCrypt employs AES, Serpent, Twofish, Camellia, and Kuznyechik as ciphers. Version 1.19 stopped using the Magma cipher in response to a security audit.[11] For additional security, ten different combinations of cascaded algorithms are available:[12]
- AES–Twofish
- AES–Twofish–Serpent
- Camellia–Kuznyechik
- Camellia–Serpent
- Kuznyechik–AES
- Kuznyechik–Serpent–Camellia
- Kuznyechik–Twofish
- Serpent–AES
- Serpent–Twofish–AES
- Twofish–Serpent
The cryptographic hash functions available for use in VeraCrypt are BLAKE2s-256, SHA-256, SHA-512, Streebog and Whirlpool.[13] VeraCrypt used to have support for RIPEMD-160, but it has since been removed in version 1.26.[14]
VeraCrypt's block cipher mode of operation is XTS.[15] It generates the header key and the secondary header key (XTS mode) using PBKDF2 with a 512-bit salt. By default, they go through 200,000 or 500,000 iterations, depending on the underlying hash function used and whether it is system or non-system encryption.[16] The user can customize it to lower these numbers to as low as 2,048 and 16,000, respectively.[16]
Security improvements
- The VeraCrypt development team considered the TrueCrypt storage format too vulnerable to a National Security Agency (NSA) attack, so it created a new format incompatible with that of TrueCrypt. VeraCrypt versions prior to 1.26.5 are capable of opening and converting volumes in the TrueCrypt format.[17][18] Since ver. 1.26.5 TrueCrypt compatibility is dropped.[19]
- An independent security audit of TrueCrypt released 29 September 2015 found TrueCrypt includes two vulnerabilities in the Windows installation driver allowing an attacker arbitrary code execution and privilege escalation via DLL hijacking.[20] This was fixed in VeraCrypt in January 2016.[21]
- While TrueCrypt uses 1,000 iterations of the PBKDF2-RIPEMD-160 algorithm for system partitions, VeraCrypt uses either 200,000 iterations (SHA-256, BLAKE2s-256, Streebog) or 500,000 iterations (SHA-512, Whirlpool) by default (which is customizable by user to be as low as 2,048 and 16,000 respectively).[16] For standard containers and non-system partitions, VeraCrypt uses 500,000 iterations by default regardless of the hashing algorithm chosen (which is customizable by user to be as low as 16,000).[16] While these default settings make VeraCrypt slower at opening encrypted partitions, it also makes password-guessing attacks slower.[22]
- Additionally, since version 1.12, a new feature called "Personal Iterations Multiplier" (PIM) provides a parameter whose value is used to control the number of iterations used by the header key derivation function, thereby making brute-force attacks potentially even more difficult. VeraCrypt out of the box uses a reasonable PIM value to improve security,[23] but users can provide a higher value to enhance security. The primary downside of this feature is that it makes the process of opening encrypted archives even slower.[23][24][25][26]
- A vulnerability in the bootloader was fixed on Windows and various optimizations were made as well. The developers added support for SHA-256 to the system boot encryption option and also fixed a ShellExecute security issue. Linux and macOS users benefit from support for hard drives with sector sizes larger than 512. Linux also received support for the NTFS formatting of volumes.
- Unicode passwords are supported on all operating systems since version 1.17 (except for system encryption on Windows).[17]
- VeraCrypt added the capability to boot system partitions using UEFI in version 1.18a.[17]
- Option to enable/disable support for the TRIM command for both system and non-system drives was added in version 1.22.[17]
- Erasing the system encryption keys from RAM during shutdown/reboot helps mitigate some cold boot attacks, added in version 1.24.[17]
- RAM encryption for keys and passwords on 64-bit systems was added in version 1.24.[17]
VeraCrypt audit
QuarksLab conducted an audit of version 1.18 on behalf of the Open Source Technology Improvement Fund (OSTIF), which took 32 man-days. The auditor published the results on 17 October 2016.[17][27][28] On the same day, IDRIX released version 1.19, which resolved major vulnerabilities identified in the audit.[29]
Fraunhofer Institute for Secure Information Technology (SIT) conducted another audit in 2020, following a request by Germany's Federal Office for Information Security (BSI), and published the results in October 2020.[30][31]
Security precautions
There are several kinds of attacks to which all software-based disk encryption is vulnerable. As with TrueCrypt, the VeraCrypt documentation instructs users to follow various security precautions to mitigate these attacks,[32][33] several of which are detailed below.
Encryption keys stored in memory

VeraCrypt stores its keys in random-access memory (RAM); on some personal computers dynamic random-access memory (DRAM) will maintain its contents for several seconds after power is cut, or longer if the temperature is lowered. Even if there is some degradation in the memory contents, various algorithms may be able to recover the keys. This method, known as a cold boot attack, which would apply in particular to a notebook computer obtained while in power-on, suspended, or screen-locked mode, was successfully used to attack a file system protected by TrueCrypt versions 4.3a and 5.0a in 2008.[34] With version 1.24, VeraCrypt added the option of encrypting the in-RAM keys and passwords on x86-64 editions of Microsoft Windows, with a CPU overhead of less than 10%, and the option of erasing all encryption keys from memory when a new device is connected.[17]
Tampered hardware
VeraCrypt documentation states that VeraCrypt is unable to secure data on a computer if an attacker physically accessed it and VeraCrypt is then used on the compromised computer by the user again. This does not affect the common case of a stolen, lost, or confiscated computer.[35] The attacker having physical access to a computer can, for example, install a hardware or a software keylogger, a bus-mastering device capturing memory or install any other malicious hardware or software, allowing the attacker to capture unencrypted data (including encryption keys and passwords) or to decrypt encrypted data using captured passwords or encryption keys. Therefore, physical security is a basic premise of a secure system.[36]
Some kinds of malware are designed to log keystrokes, including typed passwords, that may then be sent to the attacker over the Internet or saved to an unencrypted local drive from which the attacker might be able to read it later, when they gain physical access to the computer.[37]
Trusted Platform Module
VeraCrypt does not take advantage of Trusted Platform Module (TPM). VeraCrypt FAQ repeats the negative opinion of the original TrueCrypt developers verbatim.[38] The TrueCrypt developers were of the opinion that the exclusive purpose of the TPM is "to protect against attacks that require the attacker to have administrator privileges, or physical access to the computer". The attacker who has physical or administrative access to a computer can circumvent TPM, e.g., by installing a hardware keystroke logger, by resetting TPM, or by capturing memory contents and retrieving TPM-issued keys. The condemning text goes so far as to claim that TPM is entirely redundant.[39]
It is true that after achieving either unrestricted physical access or administrative privileges, it is only a matter of time before other security measures in place are bypassed.[40][41] However, stopping an attacker in possession of administrative privileges has never been one of the goals of TPM. (See Trusted Platform Module § Uses for details.) TPM might, however, reduce the success rate of the cold boot attack described above.[42][43][44][45][46] TPM is also known to be susceptible to SPI attacks.[47]
Plausible deniability
As with its predecessor TrueCrypt, VeraCrypt supports plausible deniability[48] by allowing a single "hidden volume" to be created within another volume.[49] The Windows versions of VeraCrypt can create and run a hidden encrypted operating system whose existence may be denied.[50] The VeraCrypt documentation lists ways in which the hidden volume deniability features may be compromised (e.g., by third-party software which may leak information through temporary files or via thumbnails) and possible ways to avoid this.[32]
Performance
VeraCrypt supports parallelized[51]: 63 encryption for multi-core systems. On Microsoft Windows, pipelined read and write operations (a form of asynchronous processing)[51]: 63 to reduce the performance hit of encryption and decryption. On processors supporting the AES-NI instruction set, VeraCrypt supports hardware-accelerated AES to further improve performance.[51]: 64 On 64-bit CPUs VeraCrypt uses optimized assembly implementation of Twofish, Serpent, and Camellia.[17]
License and source model
VeraCrypt was forked from the since-discontinued TrueCrypt project in 2013,[10] and originally contained mostly TrueCrypt code released under the TrueCrypt License 3.0. In the years since, more and more of VeraCrypt's code has been rewritten and released under the permissive Apache License 2.0.
The TrueCrypt license is generally considered to be source-available but not free and open source. The Apache license is universally considered to be free and open source. The mixed VeraCrypt license is widely but not universally considered to be free and open source.
On 28 May 2014 TrueCrypt ceased development under unusual circumstances,[52][53][54] and there exists no way to contact the former developers.
VeraCrypt is considered to be free and open source by:
- PC World[55]
- Techspot[56]
- DuckDuckGo's Open Source Technology Improvement Fund[57][58]
- SourceForge[59]
- Open Tech Fund[60]
- Fosshub[61]
- opensource.com[62]
- fossmint[63]
- The current VeraCrypt development team[64]
VeraCrypt is not considered free and open source by:
- Debian[65] Debian considers all software that does not meet the guidelines of its DFSG to be non-free.
The original TrueCrypt license (but not necessarily the current combined VeraCrypt license) is not considered free and open source by:
- The Free Software Foundation[66][67]
- At least one member of the Open Source Initiative (OSI). The director[68] expressed concern about an older version of the TrueCrypt license, but the OSI has not published a determination regarding either TrueCrypt or VeraCrypt.
Legal cases
In United States v Burns (2001) 1 S.C.R. 283, 2001 SCC 7, the defendant had three hard drives, the first being a system partition that was later found to contain caches of deleted child pornography and manuals for how to use VeraCrypt, with the second drive being encrypted, and the third drive having miscellaneous music files. Even though the defendant admitted to having child pornography on his second hard drive, he refused to give the password to the authorities. Despite searching for clues of previously used passwords on the first drive, and inquiries to the FBI about any weaknesses to the VeraCrypt software that could be used to access the drive partition, and brute-forcing the partition with the alphanumeric character set as potential passwords, the partition could not be accessed. Due to the defendant confessing to having child pornography on the encrypted drive, the prosecution applied to force the defendant to give away the password under the foregone conclusion doctrine in the All Writs Act.[69]
In a search of a California defendant's apartment for accessing child pornography, a VeraCrypt drive of over 900 gigabytes capacity was found as an external hard drive. The FBI was called to assist local law enforcement, but the FBI claimed to not have found a weakness in the VeraCrypt software. The FBI also denied having a backdoor within the VeraCrypt software. It was later found that another suspect had educated the defendant into using encryption to hide his photos and videos of child pornography. Because the defendant had admitted to having child pornography on the drive as a backup and chat logs relating to the other suspect educating the defendant on how to use VeraCrypt, the "foregone conclusion doctrine"[70] was used again.[71]
See also
References
- ↑ "Mounir Idrassi (idrassi)". https://github.com/idrassi.
- ↑ "Contact Us – IDRIX". https://www.idrix.fr/Root/mos/Contact_Us/Itemid,3/.
- ↑ "AM Crypto – Mounir IDRASSI – Cybersecurity & Cryptography Expert". https://amcrypto.jp/.
- ↑ "Release Notes". July 2, 2023. https://www.veracrypt.fr/en/Release%20Notes.html.
- ↑ "VeraCrypt Files – Source Code". VeraCrypt. English (default) + 42 languages listed in "Translations" folder inside VeraCrypt_1.26.24_Source.zip archive. https://sourceforge.net/projects/veracrypt/files/VeraCrypt%201.26.24/Source%20Code/.
- ↑ "root/License.txt". TrueCrypt Foundation. 17 Oct 2016. https://www.veracrypt.fr/code/VeraCrypt/tree/License.txt.
- ↑ "VeraCrypt Official Site"
- ↑ "VeraCrypt Volume". VeraCrypt Official Website. https://veracrypt.fr/en/VeraCrypt%20Volume.html.
- ↑ "Operating Systems Supported for System Encryption". VeraCrypt Official Website. https://veracrypt.fr/en/Supported%20Systems%20for%20System%20Encryption.html.
- ↑ 10.0 10.1 Rubens, Paul (October 13, 2014). "VeraCrypt a Worthy TrueCrypt Alternative". eSecurity Planet. Quinstreet Enterprise. https://www.esecurityplanet.com/open-source-security/veracrypt-a-worthy-truecrypt-alternative.html.
- ↑ Pauli, Darren (October 18, 2016). "Audit sees VeraCrypt kill critical password recovery, cipher flaws". https://www.theregister.co.uk/2016/10/18/veracrypt_audit/.
- ↑ "Encryption Algorithms". VeraCrypt Documentation. IDRIX. https://www.veracrypt.fr/en/Encryption%20Algorithms.html.
- ↑ "Hash Algorithms". VeraCrypt Documentation. IDRIX. https://www.veracrypt.fr/en/Hash%20Algorithms.html.
- ↑ "Changelog". IDRIX. https://sourceforge.net/projects/veracrypt/files/VeraCrypt%20Nightly%20Builds/.
- ↑ "Modes of Operation". VeraCrypt Documentation. IDRIX. https://www.veracrypt.fr/en/Modes%20of%20Operation.html.
- ↑ 16.0 16.1 16.2 16.3 "Header Key Derivation, Salt, and Iteration Count". VeraCrypt Documentation. IDRIX. https://www.veracrypt.fr/en/Header%20Key%20Derivation.html.
- ↑ 17.0 17.1 17.2 17.3 17.4 17.5 17.6 17.7 17.8 "VeraCrypt Release Notes"
- ↑ Castle, Alex (March 2015). "Where Are We At With TrueCrypt?". Maximum PC: 59.
- ↑ "VeraCrypt - Free Open source disk encryption with strong security for the Paranoid". https://www.veracrypt.fr/en/Release%20Notes.html.
- ↑ Constantin, Lucian (September 29, 2015). "Newly found TrueCrypt flaw allows full system compromise". https://www.pcworld.com/article/2987439/newly-found-truecrypt-flaw-allows-full-system-compromise.html.
- ↑ CVE-2016-1281: TrueCrypt and VeraCrypt Windows installers allow arbitrary code execution with elevation of privilege
- ↑ Rubens, Paul (June 30, 2016). "VeraCrypt a worthy TrueCrypt Alternative". https://www.esecurityplanet.com/open-source-security/veracrypt-a-worthy-truecrypt-alternative.html.
- ↑ 23.0 23.1 "PIM". https://www.veracrypt.fr/en/Personal%20Iterations%20Multiplier%20(PIM).html.
- ↑ Khandelwal, Swati (11 August 2015). "Encryption Software VeraCrypt 1.12 Adds New PIM Feature To Boost Password Security". https://thehackernews.com/2015/08/veracrypt-encryption-software.html#.
- ↑ Brinkmann, Martin (7 August 2015). "TrueCrypt alternative VeraCrypt 1.12 ships with interesting PIM feature". https://www.ghacks.net/2015/08/07/truecrypt-alternative-veracrypt-1-12-ships-with-interesting-pim-feature/.
- ↑ "Transcript of Episode #582". https://www.grc.com/sn/sn-582.htm.
- ↑ "The VeraCrypt Audit Results". OSTIF. October 17, 2016. https://ostif.org/the-veracrypt-audit-results/.
- ↑ QuarksLab (October 17, 2016). VeraCrypt 1.18 Security Assessment (Report). OSTIF. https://blog.quarkslab.com/resources/2016-10-17-audit-veracrypt/16-08-215-REP-VeraCrypt-sec-assessment.pdf. Retrieved October 18, 2016.
- ↑ Bédrune, Jean-Baptiste; Videau, Marion (October 17, 2016). "Security Assessment of VeraCrypt: fixes and evolutions from TrueCrypt". QuarksLab. http://blog.quarkslab.com/security-assessment-of-veracrypt-fixes-and-evolutions-from-truecrypt.html.
- ↑ "VeraCrypt / Forums / General Discussion: Germany BSI Security Evaluation of VeraCrypt". https://sourceforge.net/p/veracrypt/discussion/general/thread/1a04e8bf82/?limit=25#ed5f.
- ↑ "Security Evaluation of VeraCrypt". Federal Office for Information Security (BSI). 2020-11-30. https://www.bsi.bund.de/SharedDocs/Downloads/EN/BSI/Publications/Studies/Veracrypt/Veracrypt.html. Retrieved 2022-07-27.
- ↑ 32.0 32.1 "Security Requirements and Precautions Pertaining to Hidden Volumes". VeraCrypt Documentation. IDRIX. https://www.veracrypt.fr/en/Security%20Requirements%20for%20Hidden%20Volumes.html.
- ↑ "Security Requirements and Precautions". VeraCrypt Documentation. IDRIX. https://veracrypt.fr/en/Security%20Requirements%20and%20Precautions.html.
- ↑ Halderman, J. Alex; Schoen, Seth D.; Heninger, Nadia; Clarkson, William; Paul, William; Calandrino, Joseph A.; Feldman, Ariel J.; Appelbaum, Jacob et al. (July 2008). "Lest We Remember: Cold Boot Attacks on Encryption Keys". 17th USENIX Security Symposium. https://www.usenix.org/legacy/event/sec08/tech/full_papers/halderman/halderman.pdf.
- ↑ "Physical Security". VeraCrypt Documentation. IDRIX. 2015-01-04. https://veracrypt.fr/en/Physical%20Security.html.
- ↑ Schneier, Bruce (October 23, 2009). ""Evil Maid" Attacks on Encrypted Hard Drives". https://www.schneier.com/blog/archives/2009/10/evil_maid_attac.html.
- ↑ "Malware". VeraCrypt Documentation. IDRIX. 2015-01-04. https://veracrypt.fr/en/Malware.html.
- ↑ "FAQ". IDRIX. 2 July 2017. https://www.veracrypt.fr/en/FAQ.html.
- ↑ "TrueCrypt User Guide". TrueCrypt Foundation. 7 February 2012. p. 129. https://www.grc.com/misc/truecrypt/TrueCrypt%20User%20Guide.pdf.
- ↑ Culp, Scott (2000). "Ten Immutable Laws Of Security (Version 2.0)". Microsoft. https://technet.microsoft.com/en-us/library/hh278941.aspx.
- ↑ Johansson, Jesper M. (October 2008). "Security Watch Revisiting the 10 Immutable Laws of Security, Part 1". Microsoft. https://technet.microsoft.com/en-us/library/2008.10.securitywatch.aspx.
- ↑ "LUKS support for storing keys in TPM NVRAM". 2013. https://github.com/shpedoikal/tpm-luks.
- ↑ Greene, James (2012). "Intel Trusted Execution Technology". Intel. http://www.intel.com/content/dam/www/public/us/en/documents/white-papers/trusted-execution-technology-security-paper.pdf.
- ↑ (Google Books) Autonomic and Trusted Computing: 4th International Conference. ATC. 2007. ISBN 9783540735465. https://books.google.com/books?id=cUhpq98Zb8AC&pg=PA124. Retrieved May 31, 2014.
- ↑ Pearson, Siani; Balacheff, Boris (2002). Trusted computing platforms: TCPA technology in context. Prentice Hall. ISBN 978-0-13-009220-5. https://books.google.com/books?id=EWk2pLY7atgC. Retrieved July 21, 2016.
- ↑ "SetPhysicalPresenceRequest Method of the Win32_Tpm Class". Microsoft. http://msdn.microsoft.com/en-us/library/aa376478(VS.85).aspx.
- ↑ "TPM Sniffing Attacks Against Non-Bitlocker Targets". 2022. https://www.secura.com/blog/tpm-sniffing-attacks-against-non-bitlocker-targets.
- ↑ "Plausible Deniability". VeraCrypt Documentation. IDRIX. https://www.veracrypt.fr/en/Plausible%20Deniability.html.
- ↑ "Hidden Volume". VeraCrypt Documentation. IDRIX. https://www.veracrypt.fr/en/Hidden%20Volume.html.
- ↑ 51.0 51.1 51.2 "VeraCrypt User Guide". IDRIX. 2015-01-04. https://veracrypt.fr/en/Parallelization.html.
- ↑ Buchanan, Bill (May 30, 2014). "Encryption software TrueCrypt closes doors in odd circumstances". https://www.theguardian.com/technology/2014/may/30/encryption-software-truecrypt-closes-doors.
- ↑ Ratliff, Evan (March 30, 2016). "The Strange Origins of TrueCrypt, ISIS's Favored Encryption Tool". The New Yorker. https://www.newyorker.com/news/news-desk/the-strange-origins-of-truecrypt-isiss-favored-encryption-tool. Retrieved April 9, 2022.
- ↑ Buchanan, Bill (Nov 5, 2018). "The Fall of TrueCrypt and Rise of VeraCrypt". Medium. https://medium.com/asecuritysite-when-bob-met-alice/the-fall-of-truecrypt-and-rise-of-veracrypt-44f910ed5162.
- ↑ Constantin, Lucian (October 18, 2016). "Critical flaws found in open-source encryption software VeraCrypt". PC World. https://www.pcworld.com/article/410730/critical-flaws-found-in-open-source-encryption-software-veracrypt.html.
- ↑ Long, Heinrich (August 3, 2020). "How to Encrypt Files, Folders and Drives on Windows". Techspot. https://www.techspot.com/guides/2069-how-to-encrypt-windows/.
- ↑ Hall, Christine (May 4, 2016). "DuckDuckGo Gives $225,000 to Open Source Projects". FOSS Force. https://fossforce.com/2016/05/duckduckgo-gives-open-source-projects/.
- ↑ "A Special Thank You to DuckDuckGo for Supporting OSTIF and VeraCrypt". Open Source Technology Fund. May 3, 2016. https://ostif.org/a-special-thank-you-to-duckduckgo-for-supporting-ostif-and-veracrypt/.
- ↑ "Need strong security? VeraCrypt is an open source disk encryption software that gives extra security against brute-force attacks". SourceForge. February 8, 2020. https://sourceforge.net/projects/veracrypt/.
- ↑ McDevitt, Dan (July 18, 2018). "Privacy and anonymity-enhancing operating system Tails continued the implementation of open-source disk encryption software VeraCrypt into the GNOME user interface". Open Technology Fund. https://www.opentech.fund/news/june-2018-monthly-report/.
- ↑ "VeraCrypt is a free, open source disk encryption program". FOSSHub. Jan 17, 2021. https://www.fosshub.com/VeraCrypt.html.
- ↑ Kenlon, Seth (April 12, 2021). "VeraCrypt offers open source file-encryption with cross-platform capabilities". https://opensource.com/article/21/4/open-source-encryption.
- ↑ Afolabi, Jesse (March 5, 2021). "Veracrypt – An Open Source Cross-Platform Disk Encryption Tool". FOSSMINT. https://www.fossmint.com/veracrypt-open-source-disk-encryption-software/.
- ↑ "VeraCrypt: Source Code". https://veracrypt.io/en/Source%20Code.html.
- ↑ "Debian Bug report logs - #814352: ITP: veracrypt -- Cross-platform on-the-fly encryption". 10 February 2016. https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=814352.
- ↑ "Nonfree Software Licenses". Free Software Foundation Licensing and Compliance Lab. January 12, 2022. https://www.gnu.org/licenses/license-list.en.html#Truecrypt-3.0.
- ↑ "Various Licenses and Comments about Them". https://www.gnu.org/licenses/license-list.html.
- ↑ Phipps, Simon (2013-11-15), "TrueCrypt or false? Would-be open source project must clean up its act", InfoWorld, http://www.infoworld.com/d/open-source-software/truecrypt-or-false-would-be-open-source-project-must-clean-its-act-230862, retrieved 2014-05-20
- ↑ US v. Burns, May 10, 2019, https://scholar.google.com/scholar_case?case=16135496452212358302&q=veracrypt&hl=en&as_sdt=2006, retrieved 2023-08-22
- ↑ No. 20-937: Brief of Amici Curiae Office of the Public Defender of the State Of New Jersey and National Association For Public Defense in Support of the Petitioner (2021)
- ↑ In the Matter of the Search of a Residence in Aptos, California 95003, 2018-03-20, https://scholar.google.com/scholar_case?case=10773460282541696547&q=veracrypt&hl=en&as_sdt=2006, retrieved 2023-08-22
External links
- No URL found. Please specify a URL here or add one to Wikidata.
- VeraCrypt 1.18 Security Assessment
 |
