Software:Trusted Platform Module
| Status | Published |
|---|---|
| Year started | 2009 |
| Latest version | ISO/IEC 11889:2015 2015 |
| Organization | Trusted Computing Group, ISO/IEC JTC 1 |
| Domain | Secure cryptoprocessor |
| Abbreviation | TPM |
| Website | ISO/IEC 11889-1:2015, ISO/IEC 11889-2:2015, ISO/IEC 11889-3:2015, ISO/IEC 11889-4:2015 |
Trusted Platform Module (TPM) is an international standard for a secure cryptoprocessor, a dedicated microcontroller designed to secure hardware through integrated cryptographic keys. The term can also refer to a chip conforming to the standard ISO/IEC 11889.
One of Windows 11's operating system requirements is TPM 2.0 implementation. Microsoft has stated that this is to help increase security against firmware attacks.[1]
History
Trusted Platform Module (TPM) was conceived by a computer industry consortium called Trusted Computing Group (TCG). It evolved into TPM Main Specification Version 1.2 which was standardized by International Organization for Standardization (ISO) and International Electrotechnical Commission (IEC) in 2009 as ISO/IEC 11889:2009.[2] TPM Main Specification Version 1.2 was finalized on 3 March 2011 completing its revision.[3][4]
On 9 April 2014 the Trusted Computing Group announced a major upgrade to their specification entitled TPM Library Specification 2.0.[5] The group continues work on the standard incorporating errata, algorithmic additions and new commands, with its most recent edition published as 2.0 in November 2019.[6] This version became ISO/IEC 11889:2015.
When a new revision is released it is divided into multiple parts by the Trusted Computing Group. Each part consists of a document that makes up the whole of the new TPM specification.
- Part 1 Architecture (renamed from Design Principles)
- Part 2 Structures of the TPM
- Part 3 Commands
- Part 4 Supporting Routines (added in TPM 2.0)
Overview
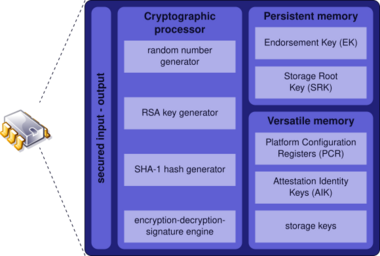
The Trusted Platform Module (TPM) provides:
- A hardware random number generator[7][8]
- Facilities for the secure generation of cryptographic keys for limited uses.
- Remote attestation: Creates a nearly unforgeable hash key summary of the hardware and software configuration. One could use the hash to verify that the hardware and software have not been changed. The software in charge of hashing the setup determines the extent of the summary.
- Binding: Data is encrypted using the TPM bind key, a unique RSA key descended from a storage key. Computers that incorporate a TPM can create cryptographic keys and encrypt them so that they can only be decrypted by the TPM. This process, often called wrapping or binding a key, can help protect the key from disclosure. Each TPM has a master wrapping key, called the storage root key, which is stored within the TPM itself. User-level RSA key containers are stored with the Windows user profile for a particular user and can be used to encrypt and decrypt information for applications that run under that specific user identity.[9][10]
- Sealed storage: Specifies the TPM state[11] for the data to be decrypted (unsealed).[12]
- Other Trusted Computing functions for the data to be decrypted (unsealed).[13]
Computer programs can use a TPM for the authentication of hardware devices, since each TPM chip has a unique and secret Endorsement Key (EK) burned in as it is produced. Security embedded in hardware provides more protection than a software-only solution.[14] Its use is restricted in some countries.[15]
Uses
Platform integrity
The primary scope of TPM is to ensure the integrity of a platform. In this context, "integrity" means "behaves as intended", and a "platform" is any computer device regardless of its operating system. This is to ensure that the boot process starts from a trusted combination of hardware and software, and continues until the operating system has fully booted and applications are running.
When TPM is used, the firmware and the operating system are responsible for ensuring integrity.
For example, the Unified Extensible Firmware Interface (UEFI) can use TPM to form a root of trust: The TPM contains several Platform Configuration Registers (PCRs) that allow secure storage and reporting of security-relevant metrics. These metrics can be used to detect changes to previous configurations and decide how to proceed. Examples of such use can be found in Linux Unified Key Setup (LUKS),[16] BitLocker and PrivateCore vCage memory encryption. (See below.)
Another example of platform integrity via TPM is in the use of Microsoft Office 365 licensing and Outlook Exchange.[17]
Another example of TPM use for platform integrity is the Trusted Execution Technology (TXT), which creates a chain of trust. It could remotely attest that a computer is using the specified hardware and software.[18]
Disk encryption
Full disk encryption utilities, such as dm-crypt, can use this technology to protect the keys used to encrypt the computer's storage devices and provide integrity authentication for a trusted boot pathway that includes firmware and boot sector.[19]
Other uses and concerns
Any application can use a TPM chip for:
- Digital rights management (DRM)
- Windows Defender
- Windows Domain logon[20]
- Protection and enforcement of software licenses
- Prevention of cheating in online games[21]
Other uses exist, some of which give rise to privacy concerns. The "physical presence" feature of TPM addresses some of these concerns by requiring BIOS/UEFI-level confirmation for operations such as activating, deactivating, clearing or changing ownership of TPM by someone who is physically present at the console of the machine.[22][23]
By organizations
The United States Department of Defense (DoD) specifies that "new computer assets (e.g., server, desktop, laptop, thin client, tablet, smartphone, personal digital assistant, mobile phone) procured to support DoD will include a TPM version 1.2 or higher where required by Defense Information Systems Agency (DISA) Security Technical Implementation Guides (STIGs) and where such technology is available." The DoD anticipates that TPM is to be used for device identification, authentication, encryption, and device integrity verification.[24]
TPM implementations
| Developer(s) | Microsoft |
|---|---|
| Repository | github |
| Written in | C, C++ |
| Type | TPM implementation |
| License | BSD License |
| Website | trustedcomputinggroup |
Laptops and Notebooks
In 2006 new laptops began being sold with a built-in TPM chip. In the future, this concept could be co-located on an existing motherboard chip in computers, or any other device where the TPM facilities could be employed, such as a cellphone. On a PC, either the Low Pin Count (LPC) bus or the Serial Peripheral Interface (SPI) bus is used to connect to the TPM chip.
The Trusted Computing Group (TCG) has certified TPM chips manufactured by Infineon Technologies, Nuvoton, and STMicroelectronics,[25] having assigned TPM vendor IDs to Advanced Micro Devices, Atmel, Broadcom, IBM, Infineon, Intel, Lenovo, National Semiconductor, Nationz Technologies, Nuvoton, Qualcomm, Rockchip, Standard Microsystems Corporation, STMicroelectronics, Samsung, Sinosun, Texas Instruments, and Winbond.[26]
TPM 2.0 implementations
There are five different types of TPM 2.0 implementations (listed in order from most to least secure):[27][28]
- Discrete TPMs are dedicated chips that implement TPM functionality in their own tamper resistant semiconductor package. They are the most secure, certified to FIPS-140 with level 3 physical security[29] resistance to attack versus routines implemented in software, and their packages are required to implement some tamper resistance. For example, the TPM for the brake controller in a car is protected from hacking by sophisticated methods.[30]
- Integrated TPMs are part of another chip. While they use hardware that resists software bugs, they are not required to implement tamper resistance. Intel has integrated TPMs in some of its chipsets.
- Firmware TPMs (fTPMs) are firmware-based (e.g. UEFI) solutions that run in a CPU's trusted execution environment. Intel, AMD and Qualcomm have implemented firmware TPMs.
- Hypervisor TPMs (vTPMs) are virtual TPMs provided by and rely on hypervisors, in an isolated execution environment that is hidden from the software running inside virtual machines to secure their code from the software in the virtual machines. They can provide a security level comparable to a firmware TPM. Google Cloud Platform has implemented vTPM.[31]
- Software TPMs are software emulators of TPMs that run with no more protection than a regular program gets within an operating system. They depend entirely on the environment that they run in, so they provide no more security than what can be provided by the normal execution environment. They are useful for development purposes.
Open source implementations
The official TCG reference implementation of the TPM 2.0 Specification has been developed by Microsoft. It is licensed under BSD License and the source code is available on GitHub.[32]
In 2018 Intel open-sourced its Trusted Platform Module 2.0 (TPM2) software stack with support for Linux and Microsoft Windows.[33] The source code is hosted on GitHub and licensed under BSD License.[34][35]
Infineon funded the development of an open source TPM middleware that complies with the Software Stack (TSS) Enhanced System API (ESAPI) specification of the TCG.[36] It was developed by Fraunhofer Institute for Secure Information Technology (SIT).[37]
IBM's Software TPM 2.0 is an implementation of the TCG TPM 2.0 specification. It is based on the TPM specification Parts 3 and 4 and source code donated by Microsoft. It contains additional files to complete the implementation. The source code is hosted on SourceForge[38] and GitHub[39] and licensed under BSD License.
In 2022, AMD announced that under certain circumstances their fTPM implementation causes performance problems. A fix is available in form of a BIOS-Update.[40][41]
TPM 1.2 versus TPM 2.0
While TPM 2.0 addresses many of the same use cases and has similar features, the details are different. TPM 2.0 is not backward compatible with TPM 1.2.[42][43][44]
| Specification | TPM 1.2 | TPM 2.0 |
|---|---|---|
| Architecture | The one-size-fits-all specification consists of three parts.[4] | A complete specification consists of a platform-specific specification which references a common four-part TPM 2.0 library.[45][6] Platform-specific specifications define what parts of the library are mandatory, optional, or banned for that platform; and detail other requirements for that platform.[45] Platform-specific specifications include PC Client,[46] mobile,[47] and Automotive-Thin.[48] |
| Algorithms | SHA-1 and RSA are required.[49] AES is optional.[49] Triple DES was once an optional algorithm in earlier versions of TPM 1.2,[50] but has been banned in TPM 1.2 version 94.[51] The MGF1 hash-based mask generation function that is defined in PKCS#1 is required.[49] | The PC Client Platform TPM Profile (PTP) Specification requires SHA-1 and SHA-256 for hashes; RSA, ECC using the Barreto–Naehrig 256-bit curve and the NIST P-256 curve for public-key cryptography and asymmetric digital signature generation and verification; HMAC for symmetric digital signature generation and verification; 128-bit AES for symmetric-key algorithm; and the MGF1 hash-based mask generation function that is defined in PKCS#1 are required by the TCG PC Client Platform TPM Profile (PTP) Specification.[52] Many other algorithms are also defined but are optional.[53] Note that Triple DES was readded into TPM 2.0, but with restrictions some values in any 64-bit block.[54] |
| Crypto Primitives | A random number generator, a public-key cryptographic algorithm, a cryptographic hash function, a mask generation function, digital signature generation and verification, and Direct Anonymous Attestation are required.[49] Symmetric-key algorithms and exclusive or are optional.[49] Key generation is also required.[55] | A random number generator, public-key cryptographic algorithms, cryptographic hash functions, symmetric-key algorithms, digital signature generation and verification, mask generation functions, exclusive or, and ECC-based Direct Anonymous Attestation using the Barreto–Naehrig 256-bit curve are required by the TCG PC Client Platform TPM Profile (PTP) Specification.[52] The TPM 2.0 common library specification also requires key generation and key derivation functions.[56] |
| Hierarchy | One (storage) | Three (platform, storage and endorsement) |
| Root keys | One (SRK RSA-2048) | Multiple keys and algorithms per hierarchy |
| Authorization | HMAC, PCR, locality, physical presence | Password, HMAC, and policy (which covers HMAC, PCR, locality, and physical presence). |
| NVRAM | Unstructured data | Unstructured data, counter, bitmap, extend, PIN pass and fail |
The TPM 2.0 policy authorization includes the 1.2 HMAC, locality, physical presence, and PCR. It adds authorization based on an asymmetric digital signature, indirection to another authorization secret, counters and time limits, NVRAM values, a particular command or command parameters, and physical presence. It permits the ANDing and ORing of these authorization primitives to construct complex authorization policies.[57]
Reception
The Trusted Computing Group (TCG) has faced resistance to the deployment of this technology in some areas, where some authors see possible uses not specifically related to Trusted Computing, which may raise privacy concerns. The concerns include the abuse of remote validation of software decides what software is allowed to run) and possible ways to follow actions taken by the user being recorded in a database, in a manner that is completely undetectable to the user.[58]
The TrueCrypt disk encryption utility, as well as its derivative VeraCrypt, do not support TPM. The original TrueCrypt developers were of the opinion that the exclusive purpose of the TPM is "to protect against attacks that require the attacker to have administrator privileges, or physical access to the computer". The attacker who has physical or administrative access to a computer can circumvent TPM, e.g., by installing a hardware keystroke logger, by resetting TPM, or by capturing memory contents and retrieving TPM-issued keys. The condemning text goes so far as to claim that TPM is entirely redundant.[59] The VeraCrypt publisher has reproduced the original allegation with no changes other than replacing "TrueCrypt" with "VeraCrypt".[60] The author is right that, after achieving either unrestricted physical access or administrative privileges, it is only a matter of time before other security measures in place are bypassed.[61][62] However, stopping an attacker in possession of administrative privileges has never been one of the goals of TPM (see § Uses for details), and TPM can stop some physical tampering.[16][18][21][22][23]
In 2015 Richard Stallman suggested to replace the term "Trusted computing" with the term "Treacherous computing" due to the danger that the computer can be made to systematically disobey its owner if the cryptographical keys are kept secret from them. He also considers that TPMs available for PCs in 2015 are not currently[timeframe?] dangerous and that there is no reason not to include one in a computer or support it in software due to failed attempts from the industry to use that technology for DRM, but that the TPM2 released in 2022 is precisely the "treacherous computing" threat he had warned of.[63]
Attacks
In 2010 Christopher Tarnovsky presented an attack against TPMs at Black Hat Briefings, where he claimed to be able to extract secrets from a single TPM. He was able to do this after 6 months of work by inserting a probe and spying on an internal bus for the Infineon SLE 66 CL PC.[64][65]
In 2015 as part of the Snowden revelations, it was revealed that in 2010 a US CIA team claimed at an internal conference to have carried out a differential power analysis attack against TPMs that was able to extract secrets.[66][67]
In 2018, a design flaw in the TPM 2.0 specification for the static root of trust for measurement (SRTM) was reported (CVE-2018-6622). It allows an adversary to reset and forge platform configuration registers which are designed to securely hold measurements of software that are used for bootstrapping a computer.[68] Fixing it requires hardware-specific firmware patches.[68] An attacker abuses power interrupts and TPM state restores to trick TPM into thinking that it is running on non-tampered components.[69]
Main Trusted Boot (tboot) distributions before November 2017 are affected by a dynamic root of trust for measurement (DRTM) attack CVE-2017-16837, which affects computers running on Intel's Trusted eXecution Technology (TXT) for the boot-up routine.[69]
In case of physical access, computers with TPM are vulnerable to cold boot attacks as long as the system is on or can be booted without a passphrase from shutdown or hibernation, which is the default setup for Windows computers with BitLocker full disk encryption.[70]
In 2021, the Dolos Group showed an attack on a discrete TPM, where the TPM chip itself had some tamper resistance, but the other endpoints of its communication bus did not. They read a full-disk-encryption key as it was transmitted across the motherboard, and used it to decrypt the laptop's SSD.[71]
2017 weak key generation controversy
In October 2017, it was reported that a code library developed by Infineon, which had been in widespread use in its TPMs, contained a vulnerability, known as ROCA, which generated weak RSA key pairs that allowed private keys to be inferred from public keys. As a result, all systems depending upon the privacy of such weak keys are vulnerable to compromise, such as identity theft or spoofing.[72]
Cryptosystems that store encryption keys directly in the TPM without blinding could be at particular risk to these types of attacks, as passwords and other factors would be meaningless if the attacks can extract encryption secrets.[73]
Infineon has released firmware updates for its TPMs to manufacturers who have used them.[74]
Availability
Currently, a TPM is provided by nearly all PC and notebook manufacturers in their products.
TPM
The TPM is implemented by several vendors:
- Infineon provides both TPM chips and TPM software, which are delivered as OEM versions with new computers as well as separately by Infineon for products with TPM technology which comply with TCG standards. For example, Infineon licensed TPM management software to Broadcom Corp. in 2004.[75]
- Microchip (formerly Atmel) manufactures TPM devices that it claims to be compliant to the Trusted Platform Module specification version 1.2 revision 116 and offered with several interfaces (LPC, SPI, and I2C), modes (FIPS 140-2 certified and standard mode), temperature grades (commercial and industrial), and packages (TSSOP and QFN).[76][77] Their TPMs support PCs and embedded devices.[76] They also provides TPM development kits to support integration of its TPM devices into various embedded designs.[78]
- Nuvoton Technology Corporation provides TPM devices for PC applications. Nuvoton also provides TPM devices for embedded systems and Internet of Things (IoT) applications via I2C and SPI host interfaces. Nuvoton's TPM complies with Common Criteria (CC) with assurance level EAL 4 augmented with ALC_FLR.1, AVA_VAN.4 and ALC_DVS.2, FIPS 140-2 level 2 with Physical Security and EMI/EMC level 3 and Trusted Computing Group Compliance requirements, all supported within a single device. TPMs produced by Winbond are now part of Nuvoton.[79]
- STMicroelectronics has provided TPMs for PC platforms and embedded systems since 2005. The product offering [80] includes discrete devices with several interfaces supporting Serial Peripheral Interface (SPI) and I²C and different qualification grades (consumer, industrial and automotive). The TPM products are Common Criteria (CC) certified EAL4+ augmented with ALC_FLR.1 and AVA_VAN.5, FIPS 140-2 level 2 certified with physical security level 3 and also Trusted Computing Group (TCG) certified.
There are also hybrid types; for example, TPM can be integrated into an Ethernet controller, thus eliminating the need for a separate motherboard component.[81][82]
Field upgrade
Field upgrade is the TCG term for updating the TPM firmware. The update can be between TPM 1.2 and TPM 2.0, or between firmware versions. Some vendors limit the number of transitions between 1.2 and 2.0, and some restrict rollback to previous versions.[citation needed] Platform OEMs such as HP[83] supply an upgrade tool.
Since July 28, 2016, all new Microsoft device models, lines, or series (or updating the hardware configuration of an existing model, line, or series with a major update, such as CPU, graphic cards) implement, and enable by default TPM 2.0.
While TPM 1.2 parts are discrete silicon components, which are typically soldered on the motherboard, TPM 2.0 is available as a discrete (dTPM) silicon component in a single semiconductor package, an integrated component incorporated in one or more semiconductor packages - alongside other logic units in the same package(s), and as a firmware (fTPM) based component running in a trusted execution environment (TEE) on a general purpose System-on-a-chip (SoC).[84]
Virtual TPM
- Google Compute Engine offers virtualized TPMs (vTPMs) as part of Google Cloud's Shielded VMs product.[85]
- The libtpms library provides software emulation of a Trusted Platform Module (TPM 1.2 and TPM 2.0). It targets the integration of TPM functionality into hypervisors, primarily into Qemu.[86]
Operating systems
- Windows 11 requires TPM 2.0 support as a minimum system requirement.[87][88] On many systems TPM is disabled by default which requires changing settings in the computer's UEFI to enable it.[89]
- The Trusted Platform Module 2.0 (TPM 2.0) has been supported by the Linux kernel since version 3.20.[90][91][92]
- Windows Vista and later have native support for TPM 1.2.
- Windows 8 and later have native support for TPM 2.0. Windows 7 can install official patch to add TPM 2.0 support.[93]
Platforms
- Google includes TPMs in Chromebooks as part of their security model.[94]
- Oracle ships TPMs in their X- and T-Series Systems such as T3 or T4 series of servers.[95] Support is included in Solaris 11.[96]
- In 2006, with the introduction of first Macintosh models with Intel processors, Apple started to ship Macs with TPM. Apple never provided an official driver, but there was a port under GPL available.[97] Apple has not shipped a computer with TPM since 2006.[98]
- In 2011, Taiwanese manufacturer MSI launched its Windpad 110W tablet featuring an AMD CPU and Infineon Security Platform TPM, which ships with controlling software version 3.7. The chip is disabled by default but can be enabled with the included, pre-installed software.[99]
Virtualization
- VMware ESXi hypervisor has supported TPM since 4.x, and from 5.0 it is enabled by default.[100][101]
- Xen hypervisor has support of virtualized TPMs. Each guest gets its own unique, emulated, software TPM.[102]
- KVM, combined with QEMU, has support for virtualized TPMs. As of 2012[update], it supports passing through the physical TPM chip to a single dedicated guest. QEMU 2.11 released in December 2017 also provides emulated TPMs to guests.[103]
- VirtualBox has support for virtual TPM 1.2 and 2.0 devices starting with version 7.0 released in October 2022.[104]
Software
- Microsoft operating systems Windows Vista and later use the chip in conjunction with the included disk encryption component named BitLocker. Microsoft had announced that from January 1, 2015, all computers will have to be equipped with a TPM 2.0 module in order to pass Windows 8.1 hardware certification.[105] However, in a December 2014 review of the Windows Certification Program this was instead made an optional requirement. However, TPM 2.0 is required for connected standby systems.[106] Virtual machines running on Hyper-V can have their own virtual TPM module starting with Windows 10 1511 and Windows Server 2016.[107] Microsoft Windows includes two TPM related commands: tpmtool, a utility that can be used to retrieve information about the TPM, and tpmvscmgr, a command-line tool that allows creating and deleting TPM virtual smart cards on a computer.[108][109]
Endorsement keys
TPM endorsement keys (EKs) are asymmetric key pairs unique to each TPM. They use the RSA and ECC algorithms. The TPM manufacturer usually provisions endorsement key certificates in TPM non-volatile memory. The certificates assert that the TPM is authentic. Starting with TPM 2.0, the certificates are in X.509 DER format.
These manufacturers typically provide their certificate authority root (and sometimes intermediate) certificates on their web sites.
- AMD[110][111][112][113]
- Infineon[114]
- Intel[115][116]
- NationZ [117][118][119][120]
- Nuvoton[121][122][123][124][125]
- ST Micro[126][127][128][129][130][131][132][133][134][135]
TPM software libraries
To utilize a TPM, the user needs a software library that communicates with the TPM and provides a friendlier API than the raw TPM communication. Currently, there are several such open-source TPM 2.0 libraries. Some of them also support TPM 1.2, but mostly TPM 1.2 chips are now deprecated and modern development is focused on TPM 2.0.
Typically, a TPM library provides an API with one-to-one mappings to TPM commands. The TCG specification calls this layer the System API(SAPI). This way the user has more control over the TPM operations, however the complexity is high. To hide some of the complexity most libraries also offer simpler ways to invoke complex TPM operations. The TCG specification call these two layers Enhanced System API(ESAPI) and Feature API(FAPI).
There is currently only one stack that follows the TCG specification. All the other available open-source TPM libraries use their own form of richer API.
| TPM Libraries | API | TPM 2.0 | TPM 1.2 | Attestation server or example | Microsoft Windows |
Linux | Bare metal |
|---|---|---|---|---|---|---|---|
| tpm2-tss[136] | SAPI, ESAPI and FAPI from the TCG specification |
Yes | No | No, but there is a separate project* | Yes | Yes | Maybe** |
| ibmtss[137][138] | 1:1 mapping to TPM commands + rich API (mild layer on top) |
Yes | Partial | Yes, "IBM ACS"[139][140] | Yes | Yes | No |
| go-tpm[141] | 1:1 mapping to TPM commands + rich API (mild layer on top) |
Yes | Partial | Yes, "Go-attestation"[142] | Yes | Yes | No |
| wolfTPM[143] | 1:1 mapping to TPM commands + rich API (wrappers) |
Yes | No | Yes, examples are inside the library | Yes | Yes | Yes |
| TSS.MSR[144] | 1:1 mapping to TPM commands + rich API (wrappers) |
Yes | No | Yes, examples are inside the library | Yes | Yes*** | No |
(*) There is a separate project called "CHARRA" by Fraunhofer[145] that uses the tpm2-tss library for Remote Attestation. The other stacks have accompanying attestation servers or directly include examples for attestation. IBM offer their open-source Remote Attestation Server called "IBM ACS" on SourceForge and Google have "Go-Attestation" available on GitHub, while "wolfTPM" offers time and local attestation examples directly in its open-source code, also on GitHub.
(**) There is an application note[146] about an example project for the AURIX 32-bit SoC using the tpm2-tss library.
(***) Requires additional libraries (dotnet) to run on Linux.
These TPM libraries are sometimes also called TPM stacks, because they provide the interface for the developer or user to interact with the TPM. As seen from the table, the TPM stacks abstract the operating system and transport layer, so the user could migrate one application between platforms. For example, by using TPM stack API the user would interact the same way with a TPM, regardless if the physical chip is connected over SPI, I2C or LPC interface to the Host system.
See also
- AMD Platform Security Processor
- ARM TrustZone
- Crypto-shredding
- Hardware security
- Hardware security module
- Hengzhi chip
- Intel Management Engine
- Microsoft Pluton
- Next-Generation Secure Computing Base
- Secure Enclave
- Threat model
References
- ↑ Warren, Tom (2021-06-25). "Why Windows 11 is forcing everyone to use TPM chips" (in en). The Verge. https://www.theverge.com/2021/6/25/22550376/microsoft-windows-11-tpm-chips-requirement-security.
- ↑ "ISO/IEC 11889-1:2009 – Information technology – Trusted Platform Module – Part 1: Overview". International Organization for Standardization. May 2009. http://www.iso.org/iso/catalogue_detail.htm?csnumber=50970.
- ↑ "TPM 1.2 Main Specification" (in en-US). https://trustedcomputinggroup.org/resource/tpm-main-specification/.
- ↑ 4.0 4.1 "Trusted Platform Module (TPM) Specifications". Trusted Computing Group. March 1, 2011. https://www.trustedcomputinggroup.org/tpm-main-specification/.
- ↑ "Trusted Computing Group Releases TPM 2.0 Specification for Improved Platform and Device Security" (in en-US). Trusted Computing Group. 2014-04-01. https://trustedcomputinggroup.org/trusted-computing-group-releases-tpm-2-0-specification-improved-platform-device-security/.
- ↑ 6.0 6.1 "TPM Library Specification 2.0". Trusted Computing Group. https://www.trustedcomputinggroup.org/tpm-library-specification/.
- ↑ Alin Suciu; Tudor Carean (2010). "Benchmarking the True Random Number Generator of TPM Chips". arXiv:1008.2223 [cs.CR].
- ↑ TPM Main Specification Level 2, Part 1 Design Principles (Version 1.2, Revision 116 ed.), https://trustedcomputinggroup.org/wp-content/uploads/TPM-Main-Part-1-Design-Principles_v1.2_rev116_01032011.pdf, retrieved 12 September 2017
- ↑ "Understanding Machine-Level and User-Level RSA Key Containers". October 22, 2014. https://docs.microsoft.com/en-us/previous-versions/aspnet/f5cs0acs(v=vs.100).
- ↑ "tspi_data_bind(3) – Encrypts data blob" (Posix manual page). Trusted Computing Group. http://linux.die.net/man/3/tspi_data_bind.
- ↑ Trusted Platform Module Library Specification, Family "2.0", Part 1 – Architecture, Section 12, TPM Operational States (Level 00, Revision 01.59 ed.), Trusted Computing Group, https://trustedcomputinggroup.org/wp-content/uploads/TCG_TPM2_r1p59_Part1_Architecture_pub.pdf, retrieved January 17, 2021
- ↑ TPM Main Specification Level 2, Part 3 – Commands (Version 1.2, Revision 116 ed.), Trusted Computing Group, http://www.trustedcomputinggroup.org/files/static_page_files/72C33D71-1A4B-B294-D02C7DF86630BE7C/TPM%20Main-Part%203%20Commands_v1.2_rev116_01032011.pdf, retrieved June 22, 2011
- ↑ Microsoft Article on TPM, July 25, 2008, https://docs.microsoft.com/en-us/previous-versions/windows/it-pro/windows-vista/cc749022(v=ws.10)?redirectedfrom=MSDN, retrieved April 1, 2021
- ↑ "TPM – Trusted Platform Module". IBM. http://www-01.ibm.com/support/docview.wss?uid=pos1R1003970&aid=1.
- ↑ "Windows 11 TPM 2.0 requirement has a special exception" (in en-US). 2021-06-28. https://www.slashgear.com/windows-11-tpm-2-0-requirement-has-a-special-exception-27680130/.
- ↑ 16.0 16.1 "LUKS support for storing keys in TPM NVRAM". 2013. https://github.com/shpedoikal/tpm-luks.
- ↑ "Microsoft Office Outlook Exchange Error 80090016 After a System Board Replacement". https://www.dell.com/support/kbdoc/en-uk/000137758/microsoft-office-outlook-exchange-error-80090016-after-a-system-board-replacement.
- ↑ 18.0 18.1 Greene, James (2012). "Intel Trusted Execution Technology". Intel. http://www.intel.com/content/dam/www/public/us/en/documents/white-papers/trusted-execution-technology-security-paper.pdf.
- ↑ "TPM Encryption". https://www.techsectora.com/2021/02/tpm-header-what-is-it-and-why-is-it-used.html?m=1.
- ↑ "Get Started with Virtual Smart Cards: Walkthrough Guide". https://docs.microsoft.com/en-us/windows/security/identity-protection/virtual-smart-cards/virtual-smart-card-get-started#step-3-enroll-for-the-certificate-on-the-tpm-virtual-smart-card.
- ↑ 21.0 21.1 Autonomic and Trusted Computing: 4th International Conference. ATC. 2007. ISBN 9783540735465.
- ↑ 22.0 22.1 Pearson, Siani; Balacheff, Boris (2002). Trusted computing platforms: TCPA technology in context. Prentice Hall. ISBN 9780130092205.
- ↑ 23.0 23.1 "SetPhysicalPresenceRequest Method of the Win32_Tpm Class". Microsoft. http://msdn.microsoft.com/en-us/library/aa376478(VS.85).aspx.
- ↑ Instruction 8500.01. US Department of Defense. 14 March 2014. p. 43.
- ↑ "TPM Certified Products List". Trusted Computing Group. https://www.trustedcomputinggroup.org/membership/certification/tpm-certified-products/.
- ↑ "TCG Vendor ID Registry". 23 September 2015. https://www.trustedcomputinggroup.org/wp-content/uploads/Vendor_ID_Registry_0-8_clean.pdf.
- ↑ Lich, Brian; Browers, Nick; Hall, Justin; McIlhargey, Bill; Farag, Hany (27 October 2017). "TPM Recommendations". Microsoft. https://docs.microsoft.com/en-us/windows/device-security/tpm/tpm-recommendations.
- ↑ "Trusted Platform Module 2.0: A Brief Introduction". Trusted Computing Group. October 13, 2016. https://www.trustedcomputinggroup.org/wp-content/uploads/TPM-2.0-A-Brief-Introduction.pdf.
- ↑ "TPM Certified Products". https://trustedcomputinggroup.org/membership/certification/tpm-certified-products.
- ↑ "Trusted Platform Module (TPM) - 2.0: A BRIEF INTRODUCTION". https://trustedcomputinggroup.org/wp-content/uploads/TPM-2.0-A-Brief-Introduction.pdf.
- ↑ GCE Shielded VM - Virtual Trusted Platform Module (vTPM)
- ↑ "GitHub - microsoft/ms-tpm-20-ref: Reference implementation of the TCG Trusted Platform Module 2.0 specification.". GitHub. https://github.com/Microsoft/ms-tpm-20-ref.
- ↑ "Intel Open-Sources New TPM2 Software Stack - Phoronix". https://www.phoronix.com/scan.php?page=news_item&px=Intel-New-Open-Source-TPM2.
- ↑ "Linux TPM2 & TSS2 Software". https://github.com/tpm2-software.
- ↑ "The TPM2 Software Stack: Introducing a Major Open Source Release Intel Software". https://software.intel.com/en-us/blogs/2018/08/29/tpm2-software-stack-open-source.
- ↑ "Open source TPM 2.0 software stack eases security adoption". August 17, 2018. https://www.eenewsembedded.com/news/open-source-tpm-20-software-stack-eases-security-adoption.
- ↑ "Infineon Enables Open Source Software Stack for TPM 2.0". August 17, 2018. https://www.bisinfotech.com/infineon-enables-open-source-software-stack-for-tpm-2-0/.
- ↑ "IBM's Software TPM 2.0 download | SourceForge.net". https://sourceforge.net/projects/ibmswtpm2/.
- ↑ "IBM SW TPM 2.0". https://github.com/kgoldman/ibmswtpm2/.
- ↑ "Intermittent System Stutter Experienced with fTPM Enabled on Windows 10 and 11". AMD. 2022-03-08. https://www.amd.com/en/support/kb/faq/pa-410.
- ↑ "AMD Issues Fix and Workaround for Ryzen's fTPM Stuttering Issues" (in en). 2022-03-07. https://www.tomshardware.com/news/amd-issues-fix-and-workaround-for-ftpm-stuttering-issues.
- ↑ "Part 1: Architecture", Trusted Platform Module Library, Trusted Computing Group, October 30, 2014, https://www.trustedcomputinggroup.org/wp-content/uploads/TPM-Rev-2.0-Part-1-Architecture-01.16.pdf, retrieved October 27, 2016
- ↑ "TPM 1.2 vs. 2.0 Features | Dell US". https://www.dell.com/support/article/en-us/sln312590/tpm-1-2-vs-2-0-features?lang=en.
- ↑ "TPM 1.2, 2.0 and FTPM (Firmware-based TPM) Information". http://aps2.toshiba-tro.de/kb0/TSB8B03XO0000R01.htm.
- ↑ 45.0 45.1 Arthur, Will; Challener, David; Goldman, Kenneth (2015). A Practical Guide to TPM 2.0: Using the New Trusted Platform Module in the New Age of Security. New York City: Apress Media, LLC. p. 69. doi:10.1007/978-1-4302-6584-9. ISBN 978-1430265832.
- ↑ "PC Client Protection Profile for TPM 2.0 – Trusted Computing Group". https://www.trustedcomputinggroup.org/pc-client-protection-profile-tpm-2-0/.
- ↑ "TPM 2.0 Mobile Reference Architecture Specification – Trusted Computing Group". trustedcomputinggroup.org. https://www.trustedcomputinggroup.org/tpm-2-0-mobile-reference-architecture-specification/.
- ↑ "TCG TPM 2.0 Library Profile for Automotive-Thin". 1 March 2015. https://trustedcomputinggroup.org/tcg-tpm-2-0-library-profile-automotive-thin/.
- ↑ 49.0 49.1 49.2 49.3 49.4 "Archived copy". http://trustedcomputinggroup.org/wp-content/uploads/TPM-Main-Part-2-TPM-Structures_v1.2_rev116_01032011.pdf.
- ↑ "Archived copy". http://trustedcomputinggroup.org/wp-content/uploads/mainP2Struct_rev85.pdf.
- ↑ "Archived copy". http://trustedcomputinggroup.org/wp-content/uploads/TPM-main-1.2-Rev94-part-2.pdf.
- ↑ 52.0 52.1 "Archived copy". https://www.trustedcomputinggroup.org/wp-content/uploads/PC-Client-Specific-Platform-TPM-Profile-for-TPM-2-0-v43-150126.pdf.
- ↑ "Archived copy". https://www.trustedcomputinggroup.org/wp-content/uploads/TCG_Algorithm_Registry_Rev_1.22.pdf.
- ↑ "Archived copy". https://trustedcomputinggroup.org/wp-content/uploads/TCG-_Algorithm_Registry_Rev_1.27_FinalPublication.pdf.
- ↑ "Archived copy". http://trustedcomputinggroup.org/wp-content/uploads/TPM-Main-Part-1-Design-Principles_v1.2_rev116_01032011.pdf.
- ↑ "Archived copy". https://www.trustedcomputinggroup.org/wp-content/uploads/TPM-Rev-2.0-Part-1-Architecture-01.16.pdf.
- ↑ Trusted Platform Module Library; Part 3: Commands, Trusted Computing Group, March 13, 2014, http://www.trustedcomputinggroup.org/files/static_page_files/C213752B-1A4B-B294-D053D90DF2AB69C5/TPM%20Rev%202.0%20Part%203%20-%20Commands%2001.07-2014-03-13-code.pdf, retrieved September 2, 2014
- ↑ Stallman, Richard Matthew. "Project GNU". Free Software Foundation. https://www.gnu.org/philosophy/can-you-trust.html.
- ↑ "TrueCrypt User Guide". TrueCrypt Foundation. 7 February 2012. p. 129. https://www.grc.com/misc/truecrypt/TrueCrypt%20User%20Guide.pdf.
- ↑ "FAQ". IDRIX. 2 July 2017. https://www.veracrypt.fr/en/FAQ.html.
- ↑ Culp, Scott (2000). "Ten Immutable Laws Of Security (Version 2.0)". Microsoft. https://technet.microsoft.com/en-us/library/hh278941.aspx.
- ↑ Johansson, Jesper M. (October 2008). "Security Watch Revisiting the 10 Immutable Laws of Security, Part 1". Microsoft. https://technet.microsoft.com/en-us/library/2008.10.securitywatch.aspx.
- ↑ "Can You Trust Your Computer? - GNU Project - Free Software Foundation". https://www.gnu.org/philosophy/can-you-trust.en.html.
- ↑ "Black Hat: Researcher claims hack of processor used to secure Xbox 360, other products". January 30, 2012. https://www.networkworld.com/news/2010/020210-black-hat-processor-security.html.
- ↑ Szczys, Mike (February 9, 2010). "TPM crytography cracked". https://hackaday.com/2010/02/09/tpm-crytography-cracked/.
- ↑ Scahill, Jeremy ScahillJosh BegleyJeremy; Begley, Josh (March 10, 2015). "The CIA Campaign to Steal Apple's Secrets". The Intercept. https://theintercept.com/2015/03/10/ispy-cia-campaign-steal-apples-secrets/.
- ↑ "TPM Vulnerabilities to Power Analysis and An Exposed Exploit to Bitlocker – The Intercept" (in en-US). The Intercept. https://theintercept.com/document/2015/03/10/tpm-vulnerabilities-power-analysis-exposed-exploit-bitlocker/.
- ↑ 68.0 68.1 Seunghun, Han; Wook, Shin; Jun-Hyeok, Park; HyoungChun, Kim (August 15–17, 2018). "A Bad Dream: Subverting Trusted Platform Module While You Are Sleeping". 27th USENIX Security Symposium. Baltimore, MD, USA: USENIX Association. ISBN 9781939133045. https://www.usenix.org/system/files/conference/usenixsecurity18/sec18-han.pdf.
- ↑ 69.0 69.1 Cimpanu, Catalin (August 29, 2018). "Researchers Detail Two New Attacks on TPM Chips". Bleeping Computer. https://www.bleepingcomputer.com/news/security/researchers-detail-two-new-attacks-on-tpm-chips/.
- ↑ Melissa Michael (8 October 2018). "Episode 14 Reinventing the Cold Boot Attack: Modern Laptop Version" (Podcast). F-Secure Blog. Archived from the original on 28 September 2019. Retrieved 28 September 2019.
- ↑ "Trusted platform module security defeated in 30 minutes, no soldering required". August 3, 2021. https://arstechnica.com/gadgets/2021/08/how-to-go-from-stolen-pc-to-network-intrusion-in-30-minutes/.
- ↑ Goodin, Dan (October 16, 2017). "Millions of high-security crypto keys crippled by newly discovered flaw". Ars Technica. https://arstechnica.com/information-technology/2017/10/crypto-failure-cripples-millions-of-high-security-keys-750k-estonian-ids/.
- ↑ "Can the NSA Break Microsoft's BitLocker? – Schneier on Security". https://www.schneier.com/blog/archives/2015/03/can_the_nsa_bre_1.html.
- ↑ ""TPM Update - Infineon Technologies"". https://www.infineon.com/cms/en/product/promopages/tpm-update/.
- ↑ "Trusted Platform Module (TPM) im LAN-Adapter". Heise Online. March 12, 2005. https://www.heise.de/newsticker/meldung/Trusted-Platform-Module-TPM-im-LAN-Adapter-143777.html.
- ↑ 76.0 76.1 "Home – Microchip Technology". http://www.atmel.com/products/security-ics/embedded/.
- ↑ "AN_8965 TPM Part Number Selection Guide – Application Notes – Microchip Technology Inc.". http://www.atmel.com/Images/Atmel-8965-TPM-Part-No-Selection-Guide-ApplicationNote.pdf.
- ↑ "Home – Microchip Technology". http://www.atmel.com/products/security-ics/embedded/?tab=tools.
- ↑ "Nuvoton TPM". https://www.nuvoton.com/products/cloud-computing/security/trusted-platform-module-tpm.
- ↑ "STSAFE-TPM". https://www.st.com/content/ccc/resource/sales_and_marketing/promotional_material/flyer/group0/62/f7/89/67/99/9a/40/45/STSAFE_TPM_Flyer/files/STSAFE-TPM-Flyer.pdf/jcr:content/translations/en.STSAFE-TPM-Flyer.pdf.
- ↑ "Replacing Vulnerable Software with Secure Hardware: The Trusted Platform Module (TPM) and How to Use It in the Enterprise". Trusted computing group. 2008. https://www.trustedcomputinggroup.org/files/temp/4B551C9F-1D09-3519-AD45C1F0B5D61714/TPM%20Overview.pdf.
- ↑ "NetXtreme Gigabit Ethernet Controller with Integrated TPM1.2 for Desktops". Broadcom. May 6, 2009. http://www.broadcom.com/products/Ethernet-Controllers-and-Adapters/Enterprise-Client-Controllers/BCM5752.
- ↑ "HP TPM Configuration Utility". https://support.hp.com/us-en/product/hp-prodesk-490-g3-microtower-pc/7633358/document/c05381064.
- ↑ "TPM vs PTT: What are the main differences between these technologies?". August 9, 2021. https://www.thewindowsclub.com/tpm-vs-ptt-differences.
- ↑ "Shielded VMs". Google Cloud. https://cloud.google.com/shielded-vm.
- ↑ "libtpms Virtual TPM". October 27, 2021. https://github.com/stefanberger/libtpms.
- ↑ Microsoft. "Windows 11 Specs and System Requirements | Microsoft" (in en-us). https://www.microsoft.com/en-us/windows/windows-11-specifications.
- ↑ Chabaud, Florent (November 15–16, 2022). "Setting Hardware Root-of-Trust from Edge to Cloud, and How to Use it". in le Guernic, Gurvan. Rennes, France: C&ESAR 2022. pp. 115–130. https://ceur-ws.org/Vol-3329/paper-07.pdf. Location: Université de Rennes 1, Campus de Beaulieu, IRISA/Inria Rennes, 263 avenue du Général Leclerc, 35042 RENNES cedex.
- ↑ "Windows 11 update: TPM 2.0 and PC Health Check confusion" (in en-US). 2021-06-24. https://www.slashgear.com/windows-11-tpm-2-0-update-system-requirement-confusion-24679866/.
- ↑ "TPM 2.0 Support Sent In For The Linux 3.20 Kernel - Phoronix". https://www.phoronix.com/scan.php?page=news_item&px=Linux-3.20-TPM-2.0-Security.
- ↑ "TPM 2.0 Support Continues Maturing In Linux 4.4 - Phoronix". https://www.phoronix.com/scan.php?page=news_item&px=TPM-2.0-Security-Linux-4.4.
- ↑ "With Linux 4.4, TPM 2.0 Gets Into Shape For Distributions - Phoronix". https://www.phoronix.com/scan.php?page=news_item&px=Linux-4.4-TPM-2.0.
- ↑ "Update to add support for TPM 2.0 in Windows 7 and Windows Server 2008 R2 - Microsoft Support". https://support.microsoft.com/en-us/topic/update-to-add-support-for-tpm-2-0-in-windows-7-and-windows-server-2008-r2-8ef7d943-995e-ee23-0c54-06600e368e1c.
- ↑ "Chromebook security: browsing more securely". Chrome Blog. https://chrome.googleblog.com/2011/07/chromebook-security-browsing-more.html.
- ↑ "Oracle Solaris and Oracle SPARC T4 Servers— Engineered Together for Enterprise Cloud Deployments". Oracle. http://www.oracle.com/us/products/servers-storage/solaris/solaris-and-sparc-t4-497273.pdf.
- ↑ "tpmadm". Oracle. http://docs.oracle.com/cd/E23824_01/html/821-1462/tpmadm-1m.html.
- ↑ Singh, Amit, "Trusted Computing for Mac OS X", OS X book, http://www.osxbook.com/book/bonus/chapter10/tpm/, retrieved August 2, 2011.
- ↑ "Your Laptop Data Is Not Safe. So Fix It". PC World. January 20, 2009. http://www.pcworld.com/article/157966/laptop_security.html.
- ↑ "TPM. Complete protection for peace of mind". Winpad 110W. MSI. http://www.msi.com/product/windpad/WindPad-110W.html.
- ↑ Security and the Virtualization Layer, VMware, http://pubs.vmware.com/vsphere-50/index.jsp?topic=%2Fcom.vmware.vsphere.security.doc_50%2FGUID-E9B71B85-FBA3-447C-8A60-DEE2AE1A405A.html, retrieved May 21, 2013.
- ↑ Enabling Intel TXT on Dell PowerEdge Servers with VMware ESXi, Dell, http://en.community.dell.com/techcenter/b/techcenter/archive/2012/06/13/enabling-intel-txt-on-dell-poweredge-servers-with-vmware-esxi.aspx, retrieved May 21, 2013.
- ↑ "XEN Virtual Trusted Platform Module (vTPM)". http://wiki.xenproject.org/wiki/Virtual_Trusted_Platform_Module_%28vTPM%29.
- ↑ "QEMU 2.11 Changelog". December 12, 2017. https://wiki.qemu.org/ChangeLog/2.11#TPM.
- ↑ "Changelog for VirtualBox 7.0". October 10, 2022. https://www.virtualbox.org/wiki/Changelog-7.0.
- ↑ "Windows Hardware Certification Requirements". Microsoft. http://msdn.microsoft.com/en-us/library/windows/hardware/hh748188.aspx.
- ↑ "Windows Hardware Certification Requirements for Client and Server Systems". Microsoft. https://msdn.microsoft.com/en-us/library/windows/hardware/jj128256.
- ↑ "What's new in Hyper-V on Windows Server 2016". Microsoft. https://technet.microsoft.com/en-us/windows-server-docs/compute/hyper-v/what-s-new-in-hyper-v-on-windows.
- ↑ tpmtool | Microsoft Docs
- ↑ tpmvscmgr | Microsoft Docs
- ↑ AMD EK RSA Root Certificate, https://ftpm.amd.com/pki/aia/264D39A23CEB5D5B49D610044EEBD121
- ↑ AMD EK ECC Root Certificate, https://ftpm.amd.com/pki/aia/23452201D41C5AB064032BD23F158FEF
- ↑ AMD EK Ryzen 6000 RSA Intermediate Certificate, https://ftpm.amd.com/pki/aia/51ADE34A2F8253525E2321AD63F7B197
- ↑ AMD EK Ryzen 6000 ECC Intermediate Certificate, https://ftpm.amd.com/pki/aia/D30EE6F7557055BA66AD1A1DD1157D2C
- ↑ Infineon Root Certificate, https://www.infineon.com/cms/en/product/promopages/optiga_tpm_certificates/
- ↑ Intel EK Root Certificate, https://upgrades.intel.com/content/CRL/ekcert/EKRootPublicKey.cer
- ↑ Intel EK Intermediate Certificate, https://upgrades.intel.com/content/CRL/ekcert/SPTHEPIDPROD_EK_Platform_Public_Key.cer
- ↑ NationZ EK Root Certificate, https://pki.nationz.com.cn/EkRootCA/EkRootCA.crt
- ↑ NationZ EK Intermediate Certificate, https://pki.nationz.com.cn/EkMfrCA001/EkMfrCA001.crt
- ↑ NationZ EK Intermediate Certificate, https://pki.nationz.com.cn/EkMfrCA002/EkMfrCA002.crt
- ↑ NationZ EK Intermediate Certificate, https://pki.nationz.com.cn/EkMfrCA003/EkMfrCA003.crt
- ↑ Nuvoton EK Root Certificate 1110, https://www.nuvoton.com/security/NTC-TPM-EK-Cert/Nuvoton%20TPM%20Root%20CA%201110.cer
- ↑ Nuvoton EK Root Certificate 1111, https://www.nuvoton.com/security/NTC-TPM-EK-Cert/Nuvoton%20TPM%20Root%20CA%201111.cer
- ↑ Nuvoton EK Root Certificate 2110, https://www.nuvoton.com/security/NTC-TPM-EK-Cert/Nuvoton%20TPM%20Root%20CA%202110.cer
- ↑ Nuvoton EK Root Certificate 2111, https://www.nuvoton.com/security/NTC-TPM-EK-Cert/Nuvoton%20TPM%20Root%20CA%202111.cer
- ↑ Nuvoton EK Root Certificate 2112, https://www.nuvoton.com/security/NTC-TPM-EK-Cert/Nuvoton%20TPM%20Root%20CA%202112.cer
- ↑ ST Micro EK GlobalSign Certificate, https://secure.globalsign.com/cacert/gstpmroot.crt
- ↑ ST Micro EK Root Certificate, https://secure.globalsign.com/cacert/stmtpmekroot.crt
- ↑ ST Micro EK Intermediate Certificate, https://secure.globalsign.com/cacert/stmtpmekint01.crt
- ↑ ST Micro EK Intermediate Certificate, https://secure.globalsign.com/cacert/stmtpmekint02.crt
- ↑ ST Micro EK Intermediate Certificate, https://secure.globalsign.com/cacert/stmtpmekint03.crt
- ↑ ST Micro EK Intermediate Certificate, https://secure.globalsign.com/cacert/stmtpmekint04.crt
- ↑ ST Micro EK Intermediate Certificate, https://secure.globalsign.com/cacert/stmtpmekint05.crt
- ↑ ST Micro EK GlobalSign ECC Certificate, https://secure.globalsign.com/cacert/tpmeccroot.crt
- ↑ ST Micro EK ECC Root Certificate, https://secure.globalsign.com/stmtpmeccroot01.crt
- ↑ ST Micro EK ECC Intermediate Certificate, https://secure.globalsign.com/stmtpmeccint01.crt
- ↑ tpm2-software/tpm2-tss, Linux TPM2 & TSS2 Software, 2020-11-18, https://github.com/tpm2-software/tpm2-tss, retrieved 2020-11-20
- ↑ "IBM TSS for TPM 2.0". https://sourceforge.net/projects/ibmtpm20tss.
- ↑ "IBM TSS for TPM 2.0". https://github.com/kgoldman/ibmtss.
- ↑ "IBM TPM Attestation Client Server". https://sourceforge.net/projects/ibmtpm20acs.
- ↑ "IBM TPM Attestation Client Server". https://github.com/kgoldman/acs.
- ↑ google/go-tpm, 2020-11-18, https://github.com/google/go-tpm, retrieved 2020-11-20
- ↑ google/go-attestation, 2020-11-19, https://github.com/google/go-attestation, retrieved 2020-11-20
- ↑ wolfSSL/wolfTPM, wolfSSL, 2020-11-18, https://github.com/wolfSSL/wolfTPM, retrieved 2020-11-20
- ↑ TSS.MSR, https://github.com/Microsoft/TSS.MSR, retrieved June 17, 2021
- ↑ Fraunhofer-SIT/charra, Fraunhofer Institute for Secure Information Technology, 2020-08-26, https://github.com/Fraunhofer-SIT/charra, retrieved 2020-11-20
- ↑ AG, Infineon Technologies. "OPTIGA™ TPM SLI 9670 A-TPM board - Infineon Technologies". https://www.infineon.com/cms/de/product/evaluation-boards/optiga-tpm-sli9670-a-tpm/.
 |
